Group-IB, a Singapore-based cybersecurity company, has discovered a new multi-stage fraud scheme called Rabbit Hole. Just like Alice follows the White Rabbit in Lewis Carroll’s novel, fraudsters lead their victims from one resource to another, stealing personal information, payment data, and money along the way. Group-IB Digital Risk Protection has discovered the traces of White Rabbit all over the world, including in Singapore, where close to a hundred fraudulent resources were detected. The scheme exploits the names of local celebrities, the brands that people trust as well as hot topics, such as COVID-19, to lure victims.
Various social engineering scams have been on the rise in the past few years. According to Singapore police, more people were tricked into divulging to scammers their one-time passwords (OTPs) for online transactions, resulting in 1,101 victims losing around $15.3 million in total last year. It was more than a fourfold increase from 2018 when 244 victims were cheated of about $456,000 in total. Together with vishing (a form of phone fraud), the new fraud scheme, which Group-IB’s Brand Protection team named Rabbit Hole, has been gaining popularity among online fraudsters worldwide since 2019. Some of the scheme’s elements, such as fake online surveys that Group-IB named Lotsy, emerged about two years ago. The scam grew in scale and sophistication and has now become a multi-stage scheme that is well-shielded from traditional detection methods.
In may the Singapore Police Force reported an increase in phishing scam cases reported during the COVID-19. According to the report, victims receive COVID-themed e-mails or text messages purportedly sent from a company they know or trust such as banks, government agencies, trade unions like NTUC, or companies such as SingPost or Netflix. Group-IB Brand Protection team has discovered that they are a part of the complex scheme called the Rabbit Hole.
Following the White Rabbit
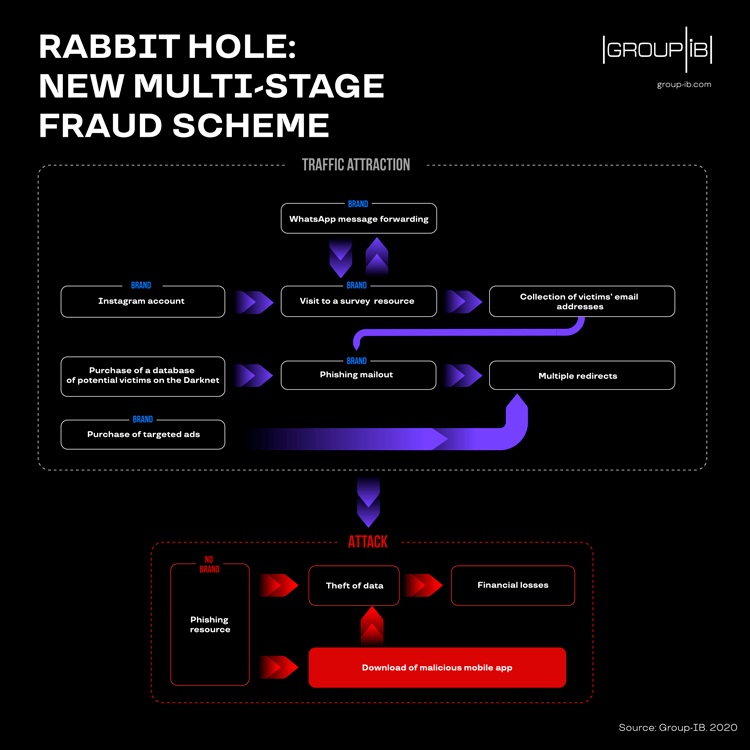
Group-IB’s Brand Protection team has divided the scheme into two main parts: the White Rabbit (the stage during which fraudsters attract traffic via social media, SMS or doorway pages) and Rabbit Hole, which involves the actual attack, theft of money, personal information or interception of payment data. For traditional automated detection systems, different stages of the Rabbit Hole scheme look like separate independent violations, which makes it impossible to eradicate this type of fraud completely.
Fig. 1. Rabbit Hole Fraud Scheme
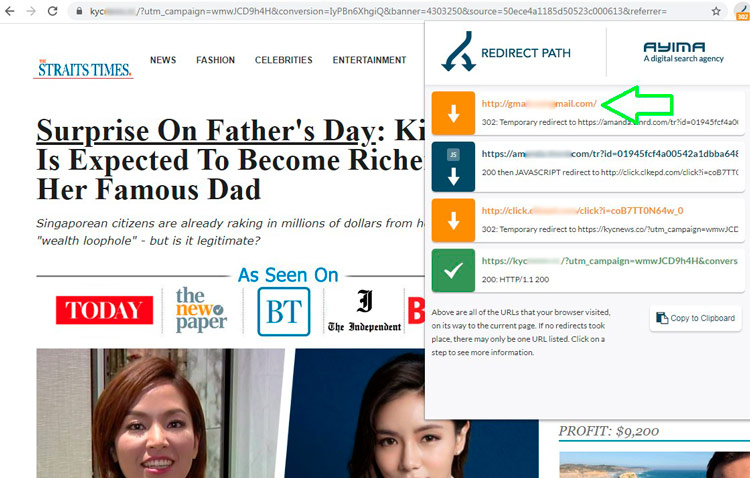
During the first stage, fraudsters exploit big names in fake ads as bait. They either pose as local celebrities, entrepreneurs, politicians, or use big companies’ brands as a lure and announce giveaways, special offers, or surveys with big prizes and expensive gifts (e.g. gift cards, smartphones, headphones, tickets). The fake ads are massively promoted via social media, targeted SMS, forced redirects, doorway pages — specially created web pages that attract users who, for example, made a typo while trying to access gmail — is another way to end up in the Rabbit Hole. Earlier in 2019, Group-IB reported on bitcoin scams in Singapore, which happened to be nothing but one of the White Rabbit’s stages.
Fig. 2. Fake Straits Times Website featuring a Bitcoin scam, redirect from a doorway page
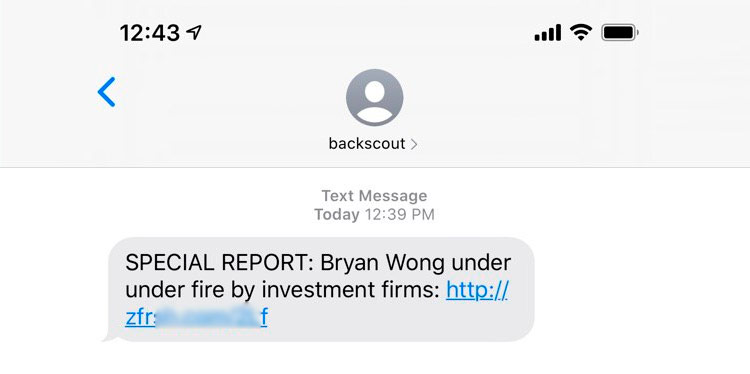
Group-IB’s Brand Protection team identified a number of instances, where local celebrities’ brands were abused as part of the Rabbit Hole scheme. They include Bryan Wong, Prime Minister Lee Hsien Loong, Ho Ching, Adam Khoo, JJ Lin, Henry Golding, Kim Lim, Peter Lim, Zhang Yong, and others. In other countries, fraudsters exploit the names of Elon Musk, Francesco Totti, Galen Weston, Andrew Forrest, Mel Gibson, Tom Gleeson, Gordon Ramsay, Lena Meyer-Landrut and many others. Widely recognized brands, such as Straits Times, M1, Lazada, Singtel, SingPost, 7-Eleven, Dettol, and McDonald’s are known to have been used by fraudsters to deceive Singaporeans as well. These companies and people are in no way involved in the scams, of course.
Fig. 3. SMS message prompting users to visit fake Straits Times page
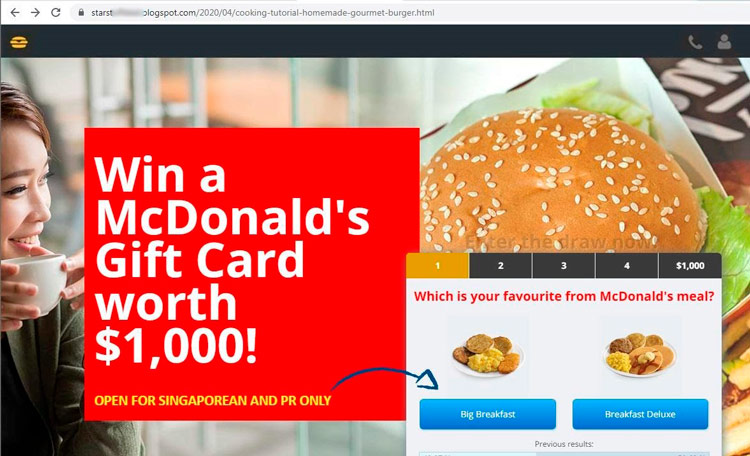
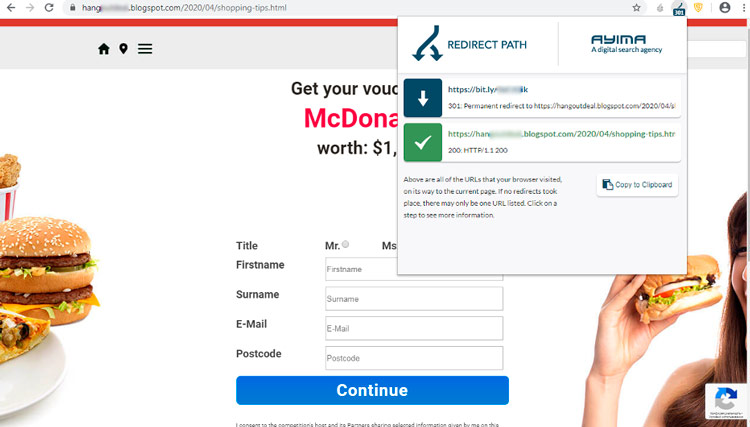
It is noteworthy that once the user takes a bait, in this case, a fake social media ad with a logo of famous brand (McDonald’s in this case), and follows the link, they end up in an almost endless chain of redirects. The information about the user location, IP address, device model, and user agent are gathered while the victim is thrown from one website to another and in the end a personalized link to a survey is generated. This allows the fraudsters to tailor content to a particular victim and makes it more complicated to track down the scheme’s initial stage. According to Group-IB’s estimates, such resources can have up to 5,000 visitors daily.
Fig. 4. Facebook ad launched from a fake account exploiting McDonald’s brand
Once the user follows the link to the survey, they are asked to answer a number of simple questions and sometimes share their good luck with their friends via messengers or social media. This way, fraudsters ensure viral distribution of the scheme and boost traffic to their resources. Group-IB Brand Protection team discovered close to 100 fraudulent resources tailored for Singaporeans.
Fig. 5. Fake website disguised as McDonald’s survey
At the same time, the victim is asked to enter their phone or email address, which can later be used for phishing mailouts or malware infection. Once these preparatory steps have been completed, fraudsters move on to the next stage: the bottomless Rabbit Hole.
Fig. 6. Fake website harvesting user personal data disguised as McDonald’s website
Down the bottomless hole
All victims who take the bait during the first stage receive emails or personal messages in which they are invited to take part in a new survey or quiz, with “considerable monetary rewards”.
This bitcoin scam targets regular users, celebrities and media outlets at the same time. While online users should always stay vigilant and follow basic cyber hygiene, brand owners should remember: unhappy customers and fans act fast. Even after one negative experience, many customers are likely to lose trust and abandon a brand. Brand owners, be it a media outlet or a celebrity, should constantly monitor any potential abuse online using the systems that allow to automatically detect and promptly eliminate any references to their brands in the domain names, website interface, phishing website databases, social media and elsewhere.
If these were cold emails or messages without first building up the user’s expectations, they would be sent straight to spam. In this case, however, the user is actually waiting for a ‘miracle’ — they have completed the survey, shared the post, and shared their contact details. The user already trusts this invitation and essentially ‘jumps into the hole’, following the rabbit.

Head of Anti-piracy & Brand Protection team in Singapore
The key part of the scheme is that users are asked to transfer a certain sum as a “fee” or “tax” or make a test payment at the end of the survey. Victims receive no reward, of course, but instead lose their money, personal data, or both.
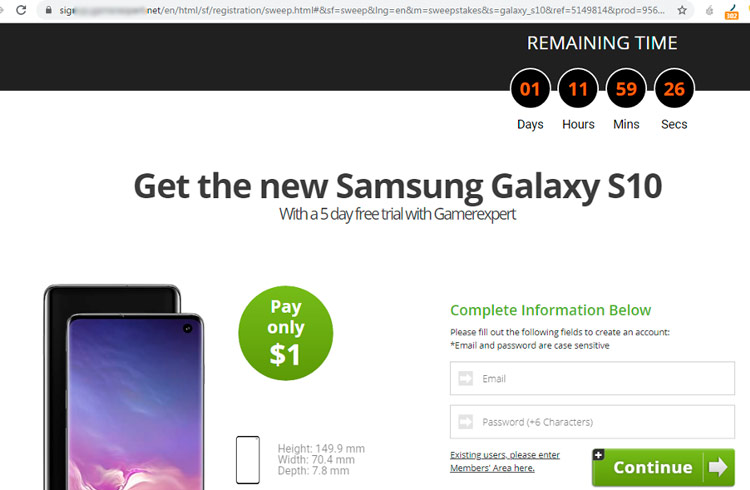
Fig. 7. Fake website asking a user to pay a fee to get the reward
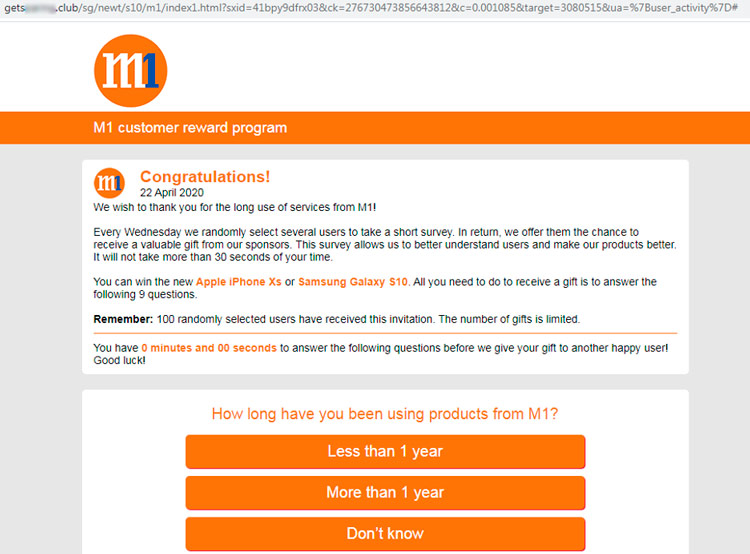
For instance, as part of fake surveys purporting to be from M1, users were tricked into entering their personal data, email addresses on the fraudulent website. The real M1 has nothing to do with the fake survey, of course. The aim was to steal personal information, payment data or money (you pay $1 now, and in a month or so, you will be charged $80 more). The link to the survey worked only once and only for a specific user, which made the resource extremely difficult to detect and neutralize.
Fig. 8. Fake website disguised as M1 survey
We’ve been tracking down various types of fraud all over the world for several years now and see how fraudulent schemes evolve and fraudsters became smarter. While classic phishing often mentions brands and involves fraud schemes with theft of money or accounts through a single resource (which is easy to track and block), the Rabbit Hole involves personalization and is divided into at least two parts and several resources in order to generate as much traffic as possible by using hot topics like COVID-19, celebrity names and brands. This makes it more difficult to search for and block resources through which money is stolen. Not all companies are prepared to monitor teaser contextual ads on social media, while domain name registrars, when contacting them directly with takedown requests, have no technical capabilities to go through the entire scheme from White Rabbit to Rabbit Hole.
Simply blocking fake pages and accounts is like trying to kill the Hydra: with every resource blocked, new resources appear. Effective monitoring and blockage can only be achieved with the automated machine-learning powered Brand Protection system fueled by regularly updated knowledge base about cybercriminals’ infrastructure, tactics and, tools. By understanding how the scheme works, we see how the user travels through websites and block both parts of the scheme. This is the only effective way to fight this type of fraud.

CEO and founder at Group-IB
The danger of the Rabbit scheme lies in the fact that private individuals are not the only ones who suffer. Major brands and celebrities whose names are abused by fraudsters suffer reputational damage. According to market researchers, nearly 64% of users who have faced brand abuse online will never return to that brand — their trust in it has been undermined.
It’s no longer effective to just look for fake accounts and websites masking as legitimate brands. These websites are promoted using contextual ads, banners, social media ads, and other means. Monitoring should include user behavior simulation. Complete visibility of the scheme from stage one to the point where users’ money is stolen is essential — otherwise, scammers can quickly rebuild the blocked parts and continue their fraudulent operations. What we recommend to online users is to always remain vigilant. A couple of simple rules: If you spot a long redirect chain, it’s a red flag. Always double-check the domain name, website registration date when entering personal information or payment data.