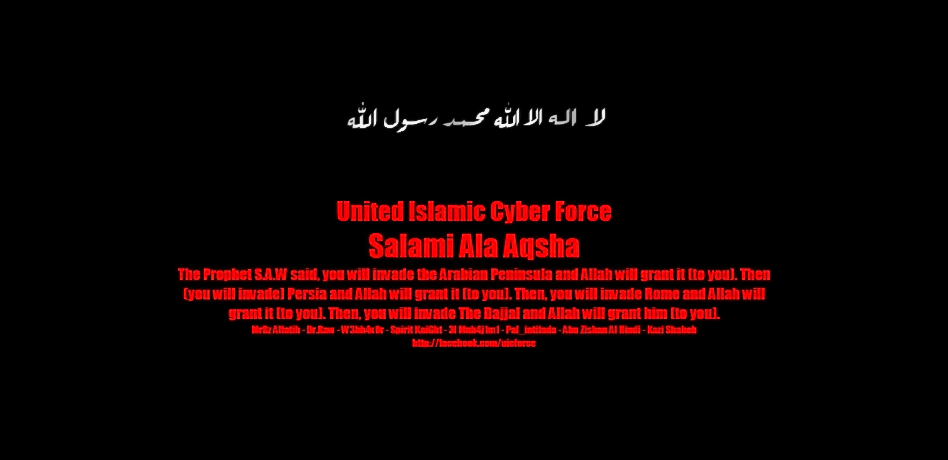
For several hours the site of the Bloc Québécois, a federal political party in Canada, was not available. Visitors encountered a black screen with threatening red letters: “United Islamic Cyber Force, Salami Ala Aqsha.”
An active pro-Islamic hacker group – United Islamic Cyber Force (UICF) – was behind this website defacement in March 2015. The attack was their response to criticism by Canadian politicians of a Muslim woman who appeared in a hijab in the House of Commons.
The UICF became first known in January 2014. There have been no less than 40 members of the group from Indonesia, Pakistan, Morocco, Algeria and Kosovo at different times. All members of the group openly support Islamic radical movements.
Group-IB has identified the identities of some of the UICF hacktivists, and today we are ready to discuss both the group itself and its members. In the overwhelming majority of cases, hacktivists are very young people with a low level of technical training, victims of propaganda or under the influence of others.
Its Record
In the three years of its existence, members of the United Islamic Cyber Force group participated in numerous operations.
Here are some of the best known campaigns:
A joint attack on French Internet resources in January 2015 organized by pro-Muslim radical hackers from the United Islamic Cyber Force, Fallaga Team, AnonGhost and Cyber Caliphate after the terrorist attack on the Parisian editorial offices of Charlie Hebdo.
“Hackintifada” directed against Israeli websites and online resources. The first attack occurred on April 7, 2013, when there were disruptions in the website of the Ministry of Foreign Affairs and the Ministry of Education, then the attacks became a tradition and occurred every year on April 7.
An attack on the state resources of India initiated by the famous group Anonymous. The reason for it was the blocking of a number of video hosting and file-sharing resources in the country and a crackdown on piracy.
An operation meant to draw attention to the war between Israel and Palestine and its Palestinians victims.
An attack in response to the Israeli prohibition on visiting the Al-Aqsa mosque in Jerusalem. The reason for this ban was the assassination attempt on October 29, 2014, against Israeli politician Yehuda Glick, who favored giving Jews, Muslims and Christians the opportunity to pray together on the Temple Mount. The shooter was killed during the attempt to apprehend him and the incident caused riots.
Analyzing the joint attacks and operations of the UICF, we came to the conclusion that the group and its members are connected with more than 60 hacker groups around the world, most of which are pro-Islamic.
The majority of the attacks committed by the UICF are Deface (substitution or blocking of the main page of the site) or DDoS (denial of service). During a Deface attack on a hacked site, the official content was replaced with pro-Islamic radical slogans, as was the case with the Bloc Québécois. Some of the slogans were connected with ISIS.
In addition to the slogans, those pages indicate the name of the operations, the aliases of the hackers who conducted the attacks and sometimes even their contact information. This is a kind of “note” from the hacktivists officially taking responsibility for the action, and a tip-off for journalists and potential followers.
Since the main goal of hacktivists is to attract attention to their actions, information about these attacks is actively disseminated on social networks. To do this, almost every one of them has a lot of profiles on Facebook, Twitter, Google+ and specialized hacking forums.
- LiByA SqL RoOt
- Nivenzal Attacker
- Zishan Rider
- Pal_Intifada
- 3l Muh4j1m1
- Physicaal AL, Kosova?
- MrBz Alfatih
- r00t-Pwn
- Thex@b1_Ma
- Root Max
- Xknight / xKnight Al Maroc
- Spirit KniGht
- W3bh4x0r
- AnoaGhost aka Shiro’Tenshi
- Syuhada1337
- KidSZonk
- soul_hiTz 98
- Senyum 420
- Alpha-Kill3r
- AlboCyber AL
- Backdoorcoder AL
- 51N1CH1
- Dr.Raw
- CyberHack Al
- Haxor-Gaza
- DK.r00t
- irhaby_newbie
- Gunz_Berry
- Ivan Al Hasyim
- L1ttle M0nster
- J1h4d_attacker
- Atique
- Kazi Shaheb
- 4prili666h05T
- Lakhdar DZ
- Yunus
- LogOut Ma
- CReZZ DoT ID
- infern0
- Ali Lord Hacker
- Cemongwaw
- the black monster
- matrix
- RBG hack
- Anas Colere
Children of cyber-division
Using our Threat Intelligence system and Open Source Intelligence methodology, we decided to identify the identities of several members of the United Islamic Cyber Force team from around the world and show who they really are.
AnoaGhost
Location: Indonesia
Participates in UICF, Indonesian Intelegent Security, Secret Code Army and !nsp3ct0r Team.
This is likely the hacktivist who uses the alias AnoaGhost. Photo from his Facebook profile.
By analyzing the Deface attacks conducted by AnoaGhost, we discovered his email address [email protected] — the hacktivist left it on one of the websites he compromised.
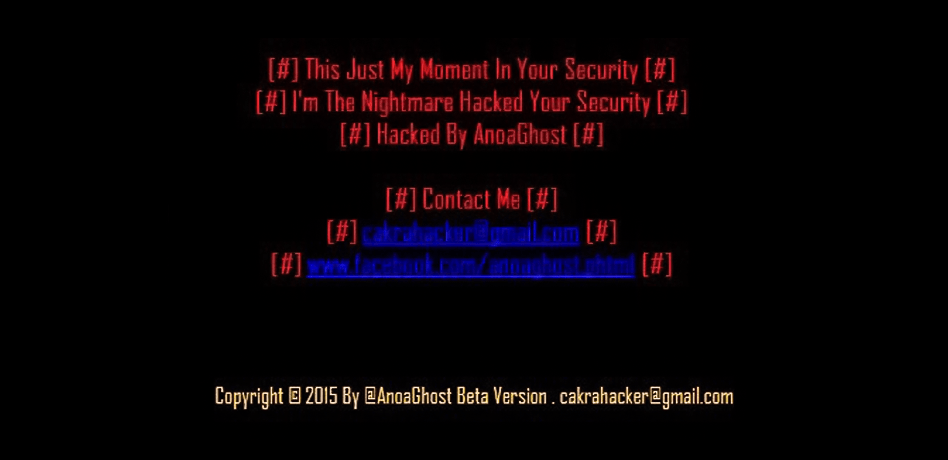
Portion of a Deface page set up by the hacker with his contact information
With the alias used in the email address – cakrahacker, an inactive blog was found on the Blogspot platform http://cakrahacker.blogspot.com.
Mention of this blog was found in a Facebook profile in an entry from August 6, 2011, by a user named Chakra B. In this profile, we found messages left by friends of the user, who called him “cakra,” which partially coincides with the username in the email address [email protected].
There were also found the birthday greetings left by his friends in the profile on March 10. Based on the information from that profile, the probable name of the hacktivist is Chakra Bernaty, and his place of residence is Bandung, Indonesia. Apparently, he is studying computer science at the Universitas Islam Negeri Sunan Gunung Djati Bandung.
A photo from the Facebook profile of a purported hacktivist, in which his real name is easily seen
Two other pages were found on Facebook with the name AnoaGhost, used by the attacker in Deface attacks, one of which contains references to another nickname used by the attacker: ShiroTenshi.
https://www.facebook[.]com/AnoaGhost.gov/
https://www.facebook[.]com/anoaghost.moe/
Based on the nickname found on one of the pages on Facebook, we found the attacker’s website shiro-tenshi.ml, registered in the Netherlands through the organization Freenom, was discovered. We also found additional accounts belonging to the attacker:
https://pastebin[.]com/u/anoaghost
https://twitter[.]com/shirotenshii
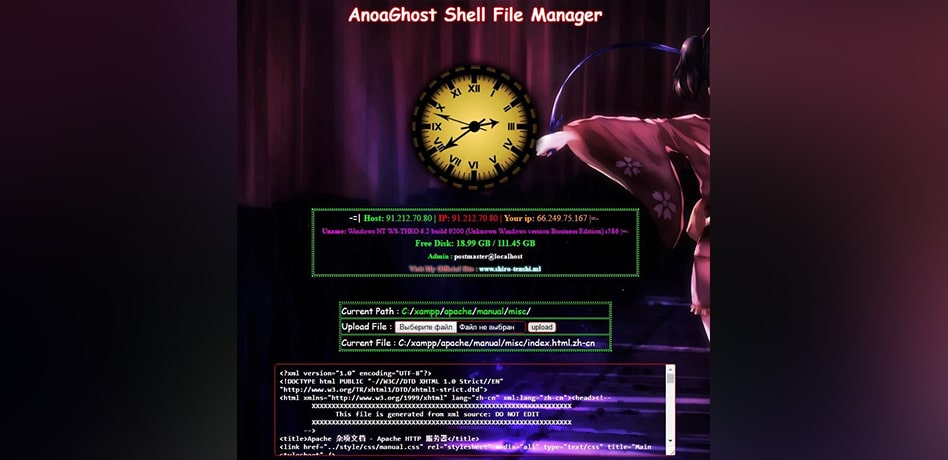
Screenshot of the interface software of the hacker AnoaGhost
There is another interesting detail. The hacker used AnoaGhost Shell File Manager v3.0 software, which also mentions the attacker’s website shiro-tenshi.ml in its text.
Gunz_Berry
Location: Indonesia
Participates in groups such as AnonCoders, Falllaga Team, Indonesian Code Party and Khilafah Cyber Army.

This is likely the attacker with the alias Gunz_Berry. Photo from his Facebook profile
We discovered the email address [email protected] used as contact information in a Deface attack.
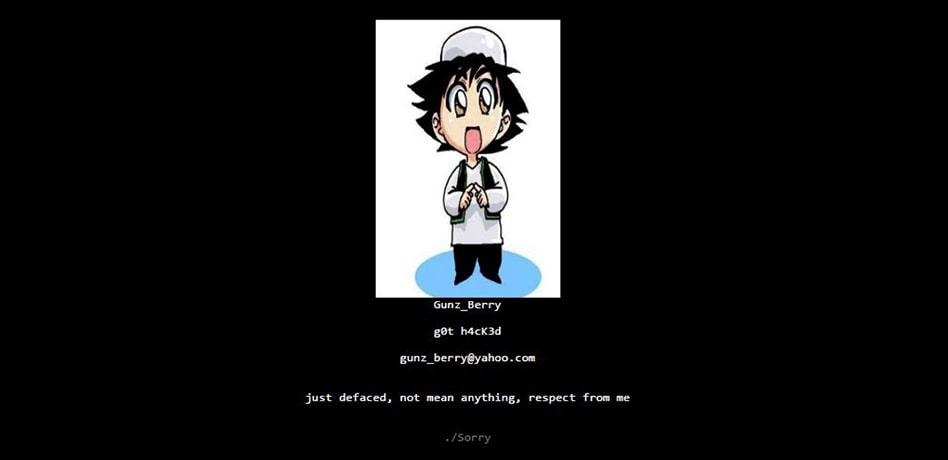
Part of a Deface page on a hacked website containing contact information of the attacker
This is the e-mail address he used to register on 000webhost[.]com with the name Guntur.
In addition to the email address, the attacker often left in the text of Deface pages a link to the Facebook profile as contact information: https://www.facebook[.]com/newbieyangtakbisaapaapa. The name Guntur, shown in the profile, corresponds to the name of the user on 000webhost.com. There are also posts with links to mirror sites of hacked sites in this user’s name.
Based on this information, we determined the real name of the attacker. It is Guntur R. He lives in Indonesia.
Based on the alias of the hacktivist, another profile was found on Facebook. However, now it is inactive: https://www.facebook[.]com/gunz.berry.9.
The attacker also owns the domain name gunz-berry[.]com, which is registered in Indonesia.
We determined that Gunz_Berry uses in his attacks the software gunz_berry xh3LL Backd00r 1.0, a modification of the GaLers xh3LL Backd00r software distributed on underground Indonesian hackers’ forums. Its author is a hacker with the alias Mr. DellatioNx196. This software is used in Deface attacks and serves to simplify the loading of pages and files onto the server where the hacked website is located.
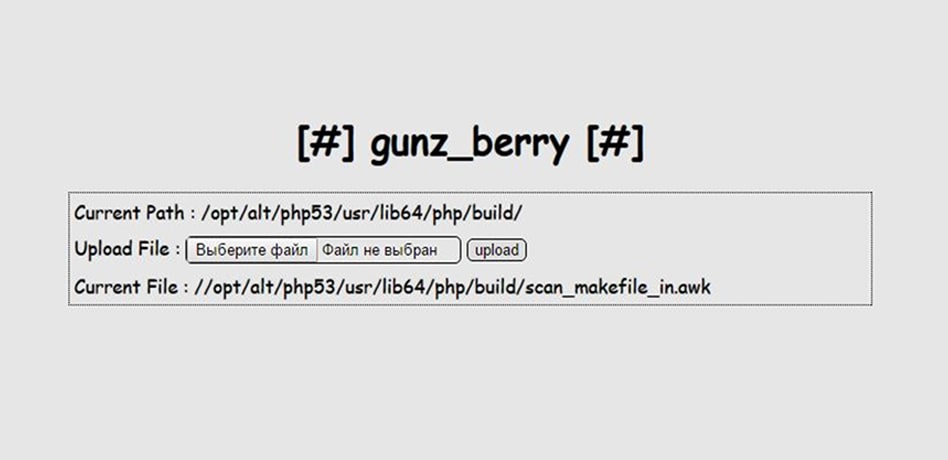
Screenshot of the interface software of the hacker alias gunz_berry
When recovering the password of the Facebook account (https://facebook[.]com/gunz.berry.9) the following information was received: g*********i@y****.c*.id. Presumably, it is the Yahoo! Indonesia mail service in the domain yahoo.co.id, which confirms his presence in Indonesia.
W3bh4x0r
Location: Nigeria
Participated in the activities of groups such as Nigeria Cyber Force, United Nigeria Cyber Force, Extreme Crew, Naija S3curity Kill3rs, Nigerian Gray Hat Hackers and Cyb3r Command0s.

Presumed appearance of the hacktivist with the alias W3bh4x0r. Photo from his Facebook profile.
On some Deface pages left by the activist on hacked sites, the email address a*********[email protected], was found, presumably belonging to the attacker.
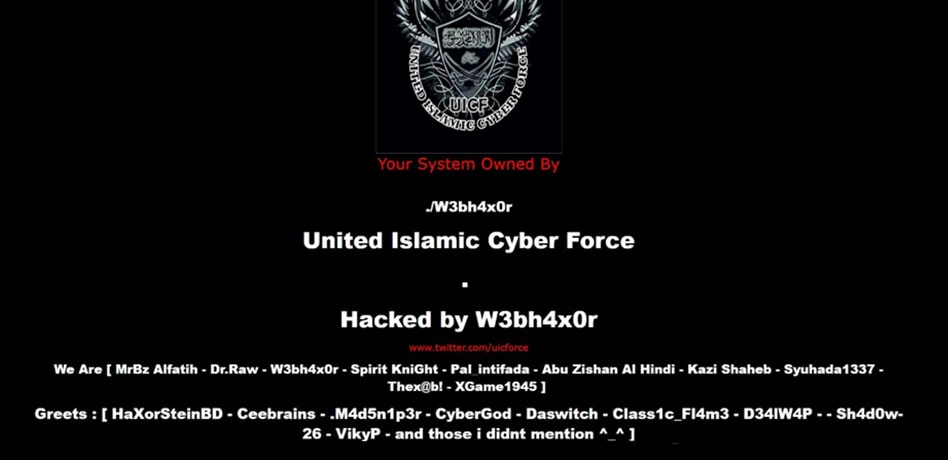
Part of the Deface page of the hacker of a website on the behalf of the UICF
The attacker also left a link to the Facebook account: https://www.facebook[.]com/web.haxor as contact information on Deface pages.
When attempting to recover the password for this Facebook account, it was determined that it was registered to the email address o***********[email protected] and phone number + ********** ** 36. The mobile phone number coincides with the numbers of the number to which the email address a****************[email protected] is attached, which confirms the connection between them.
The hacktivist’s name and photos of him were found on this page. The user name on the account – Habiblahi Adeleke Busari – coincides with the user name of a Gmail account with the email address a****************[email protected]. While attempting to recover the password for this Facebook account, the following data were uncovered.
Thus, we can conclude that the possible real name of the attacker is Habiblahi Adeleke B. Place of residence: Nigeria.
Also, an account was found on the streaming service SoundCloud. A bog was found http://nigeriacyberforce[.]blogspot[.]ru/ related to the group United Nigeria Cyber Force. In this blog, an article titled “wordpress 0day exploit Revslider” was published by a user with the alias “adeleke busari.”
We also found an account on Google+ https://plus[.]google[.]com/105478645066963208223/posts and the website http://www.mp3loaded[.]com[.]ng/, which belongs to the hacktivist.
Through the email address a****************ri@gmail[.]comads were found on the Nigerian nairaland.com forum from a user with the nickname Lekzy001, which coincides with the nickname listed on the Facebook page https://www.facebook[.]com/web.haxor.
Also in those ads were the WhatsApp number 07052547605 and website http://ictwebsitesolutions[.]com, where the contact telephone is +234**********6 (+234 is the country code of Nigeria) and Instagram https://www.instagram[.]com/lekzyone/, and https://www.facebook.com/web.haxor was indicated as its Facebook page.
The telephone number found +234************6 recovers the password for e-mail address adelekebusari@gmail[.]com and his Facebook account.
Lakhdar DZ
Location: Algeria
Lakhdar DZ is a member of the group United Islamic Cyber Force and has taken part in actions of the group Arab Warriors Team.
Presumed appearance of the hacktivist with the alias Lakhdar DZ.
On Deface pages that the activist left on hacked sites, we found the e-mail address Lakhdar46Dz@gmail[.]com, presumably belonging to the attacker. Also, as contact information, he left a link to a profile on Facebook that is currently inactive https://www.facebook[.]com/lakhdar46dz.

Portion of the Deface page left by the attacker on a hacked site,
indicating contact information
Accounts on social media were obtained by a search of the alias used by the hacktivist:
- https://www.facebook[.]com/lakhdar.22dz
- https://www.instagram[.]com/Lakhdar***/
- https://www.facebook[.]com/Lakhdar-DZ-14437794092594
The Facebook profile contained the following information: Skype account lakhdar.222 and Twitter account https://twitter[.]com/LakhdarX33, as well as real photos of the attacker.
Based on data from social media, the following information was obtained: the presumed name of the attacker is Lakhar B., 21.
Place of residence: Sidi Bel Abbes, Algeria
These data were obtained mainly from the profile on Facebook https://www.facebook[.]com/lakhdar.22dz.
Several websites are associated with this hacktivist. Two domain names are registered at email address lakhdar46dz@gmail[.]com:
- news-ar.com
- geek-ar.com
In Twitter, Facebook and Skype accounts, the following websites of this attacker were found, with domain names are registered with false data:
- http://lakhdar-dz[.]info
- http://lakhdar-dz[.]net
While recovering the Facebook account (https://www.facebook[.]com/lakhdar.22dz) the following information was received: l********z@a**.com (presumably AOL mail service).
While recovering the password to the Twitter account (https://twitter[.]com/lakhdarX33) the following information was obtained: la*********@l***.** (presumably, mail service from Mail.Ru in the list.ru domain).
Zishan Rider
Location: India
Zishan Rider has taken part in the actions of such groups as Anonymous Afghanistan, Anonymous Laayoune, Anti-Sec Cyber Crew and IndianCyb3rDevils, as well as the FreePalestine movement.

Presumed appearance of the hacker with the alias Zishan Rider
Based on the alias Zishan Rider, used by the attacker, the following profiles were found on social networks:
- Twitter https://twitter[.]com/zishanrider
- Facebook https://www.facebook[.]com/profile.php?id=100002707467602
- Ask.fm https://ask[.]fm/ZishanRider
Also, on the Deface pages the attacker left on the hacked sites, two e-mail addresses were found to contact the attacker: zishanrider@cyberdude[.]com and zishanrider@mail[.]com.
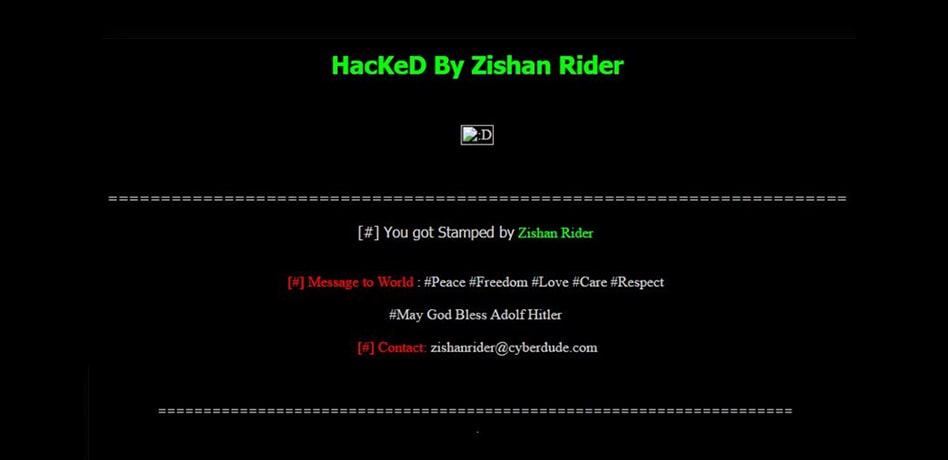
Portion of the Deface page left by the attacker on a hacked site, with his contact email address
In the Twitter account found from the alias used by the attacker, a blog was found that he maintained on his zishanrider[.]com domain, which was registered to the email address zishanrider@yahoo[.]com, name Zishan Rider, address Delhi 110001 India, as well as the cellular telephone number +91.97******100 (+91 is the country code for India).
Based on the data obtained, we established his real name as Zishan S. The residence of the activist is Delhi, India. His birthday is June 27.
While recovering the password in the Yahoo! Mail service for the account mentioned previously, a mask of the backup Gmail account was obtained: z**********[email protected].
While recovering the password of the attacker’s Twitter account, the following mask of an e-mail address of the hacktivist was obtained: zi************@gmail.com.
In his attacks, he regularly makes reference to radical Islam, advocating its dissemination. He also uses photos depicting Adolf Hitler on his Deface pages.
Hidden threat
From their profiles, none of the hacktivists from the United Islamic Cyber Force looks like professional cybercriminals who attack banks, government institutions or strategic infrastructure facilities. They are yesterday’s schoolchildren and students, with a limited life experience, easily amenable to someone else’s influence. Their goal is not to steal money, but publicity – coverage of their actions by the world media.
How to avoid becoming a victim of hacktivists
- Penetration testing and web resource audit
We recommend comprehensive security assessments of IT infrastructure. Areas of interest should include web resource security (86% of web resources contain at least one critical vulnerability); corporate network infrastructure: public Wi-Fi with access to corporate segments, cloud where employee available information is stored; unprotected backup copies. - Threat Intelligence
There is no such thing as 100% protection against cyber attacks but you definitely can reduce the risk and improve your protection level. A great route for this is to understand the actual threats you are facing, by using Cyber Intelligence, a system designed to collect, monitor and analyze criminal groups, their tactics and tools. - Protection against DDoS attacks
When a DDoS attack targets corporate website and causes significant response time delays, users may lose their time, trust in your company and sometimes also money. We recommend using the services of strong providers — their innovative filtration network enables medium-sized or large organizations to proactively, reliably and inexpensively protect their websites against sophisticated DDoS attacks. - WAF (WEB Application Firewall)
Any advanced application code may contain errors. Hackers use them to gain unauthorized access to company and user data. It is essential not only to promptly detect and block application attacks, but also to ensure that software vulnerabilities cannot be exploited. Next gen WAF effectively addresses all these challenges.


































