Group-IB, a Singapore-based cybersecurity company that specializes in preventing cyberattacks, announces that there has been a number of incidents in which Telegram chats were illegally accessed on iOS and Android devices, with the customers of various Russian mobile operators having been affected. In all the cases, the victim’s only authentication factor was SMS. The risk it poses is that malefactors can potentially gain access to other messaging apps, social networking sites, email accounts, and mobile banking apps and services where SMS is the only authentication method used.
In late 2019, several Russian entrepreneurs who had faced the problem of unauthorized access to their Telegram chats reached out to Group-IB’s Cyber Investigation Department. The incidents occurred on iOS and Android devices regardless of what mobile operator the victim used.
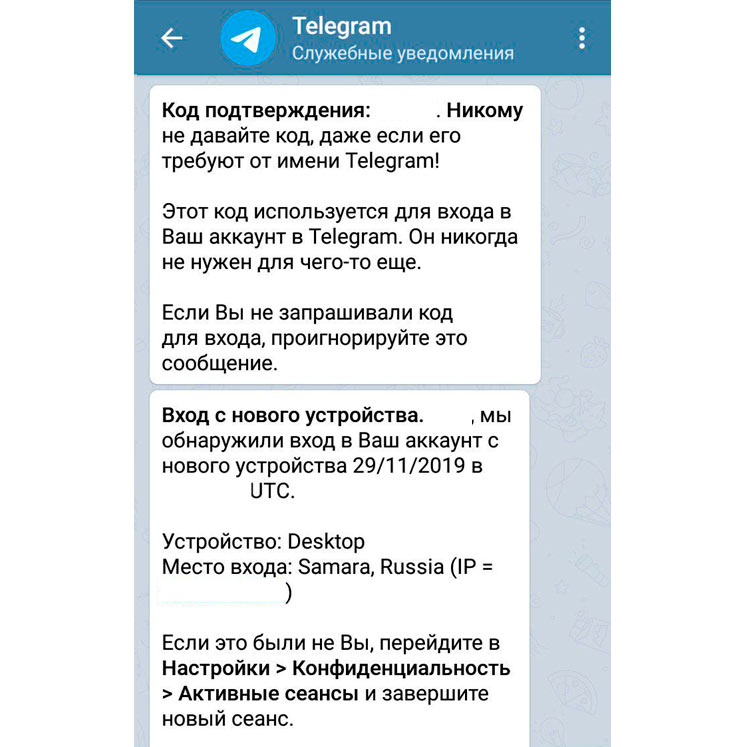
The attack started when users received a message from Telegram’s service channel (the messenger’s official channel with a blue verified badge) with a login code that the user did not request. Users then received an SMS with an activation code, which was almost immediately followed by a “new device login” notification on the same Telegram channel. In all the cases Group-IB is aware of, the attackers logged in to victims’ accounts via the mobile Internet (they have likely used one-time use SIM cards), and in most cases the attackers’ IP addresses were located in the city of Samara, Russia.
How to protect yourself
Group-IB experts emphasize that Telegram has built-in security mechanisms enabling effective protection against the attackers, but not everyone uses them.
Apart from the required SMS messages, one more authentication factor – an additional password – should be enabled in Telegram. It is important that everyone does this. You then need to check other applications and services that use SMS for authentication as the first or second factor for password recovery for email accounts, other messengers, and mobile banking applications and services.

Deputy Head of the Digital Forensics Lab at Group-IB
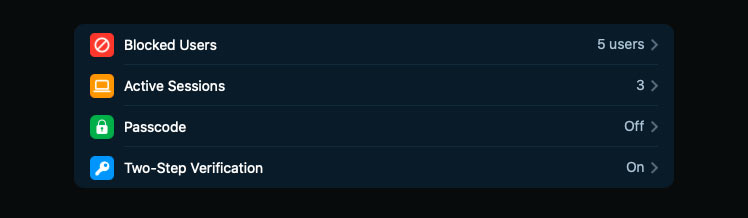
Group-IB experts warn that such attacks can only be successful if the Password or Two-step verification options are turned off in Telegram’s settings on a smartphone. To enable protection on iOS and Android devices, go to Telegram’s Settings > Privacy and Security > Two-Step Verification > Set Additional Password. More detailed information about how to enable this option is available on the messenger’s official website.
Group-IB experts add that it is not recommended to add a recovery email address to restore this password, because email account recovery is usually performed via SMS too. WhatsApp users can increase the security level of their accounts in a similar way.
How the attackers gain access to Telegram
Group-IB digital forensic experts examined the electronic devices of all victims and established that they had not been infected with any spyware or banking Trojans, their accounts had not been hacked, nor their SIM cards had been copied. Forensic examination showed that the attackers gained access to the victims’ messengers using SMS codes received when the account is being logged in from a new device.
The scheme is as follows: when the messenger is being activated on a new device, Telegram sends a code through the service channel to all user devices with active sessions, followed by SMS (upon request). Knowing this, the attackers initiate a request to make Telegram send an SMS with an activation code, gain access to this SMS message, and use the received code for successful authentication in the messenger.
This technique allows malefactors to gain access to all the victim’s chats, except for the secret ones, as well as to the history of their chats, including shared files and photos. If a legitimate user detects unauthorized access, they can stop it by terminating all other active sessions except for their own. Thanks to Telegram’s built-in security mechanism, a malefactor who has just got access, cannot terminate the user’s “older” active sessions for at least 24 hours. Therefore, it’s important to detect a new illegitimate session and terminate it on time, before malefactors kick a user out of their account. Group-IB experts have notified the Telegram team of the ongoing analysis of the incidents.
Access for $4,000
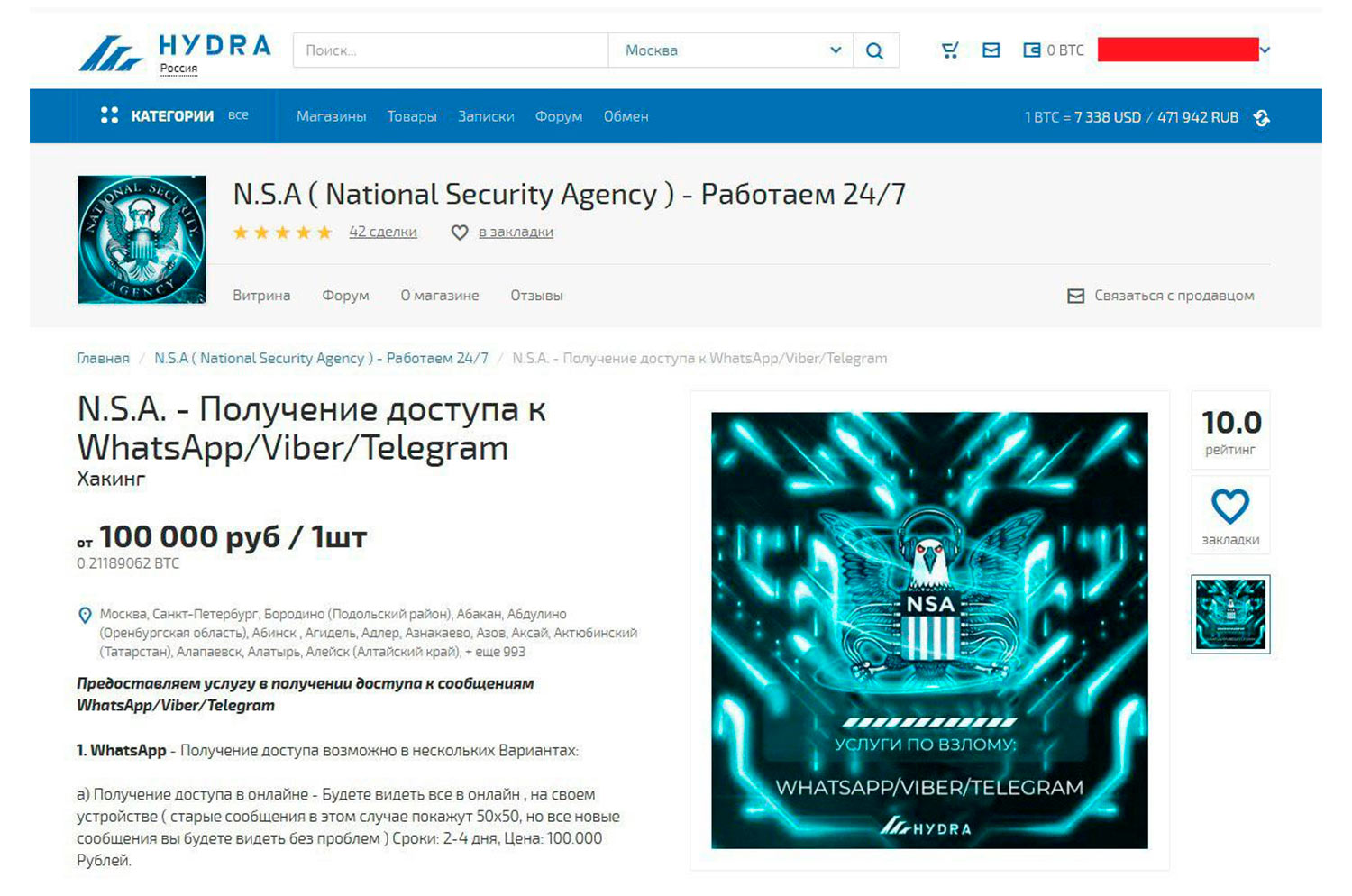
The examination of the incidents is continuing, with the technique used by the attackers to bypass SMS authentication factor yet to be determined. Security researchers have earlier described cases when text messages were intercepted by exploiting SS7 and Diameter protocols, used in telecom networks. In theory, such attacks can also be carried out by gaining illegal access to the special equipment for SMS interception or using insider information obtained from the employees of mobile operators. Group-IB researchers discovered recent posts on underground forums with offers to hack various instant messengers, including Telegram.
The ads published on Hydra underground forum, in particular, offered to buy access to WhatsApp, Viber or Telegram messengers. To get access to one’s WhatsApp or Viber account, two options were offered – an “online” one, which would allegedly show all the new messages on the device of the “service” buyer in real time, and an “advanced” one, which would reportedly grant access to the chat history with all the media files, including deleted ones. The price for the access to a WhatsApp account ranges between $1,550 and $5,450, while the access to a Viber account can be purchased for $1,550-3,900. For “stealing” a Telegram account, only one option – giving the full access to the account – was offered at $3,900 price.
According to various security experts’ reports, social media, mobile banking and instant messengers can be hacked by exploiting SS7, but these were single cases of targeted or test attacks. The new campaign that already includes more than 10 cases shows that the attackers want to commoditize this attack scheme. In order to prevent such attacks, users must increase their level of cyber awareness: at least use multi-factor authentication wherever possible and add a mandatory additional factor to SMS, which is available on Telegram.

Head of Investigation Department, Group-IB