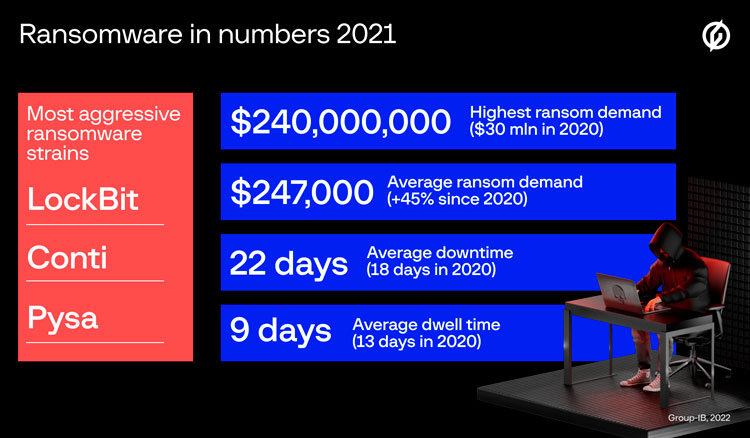
Group-IB, one of the global cybersecurity leaders, unveils its second annual guide to the evolution of threat number one “Ransomware Uncovered 2021/2022″. The findings of the second edition of the report indicate that the ransomware empire kept its winning streak going with the average ransom demand growing by 45% to reach $247,000 in 2021. Ransomware gangs have also become way greedier since 2020. A record-breaking ransom of $240 million ($30 mln in 2020) was demanded by Hive from MediaMarkt. Hive and another 2021 newcomer to the Big Game Hunting, Grief, quickly made its way to the top 10 gangs by the number of victims posted on dedicated leak sites (DLS).
Ransomware assembly line
The new report takes stock of the most up-to-date tactics, techniques, and procedures (TTPs) of ransomware threat actors observed across all geographic locations by Group-IB Digital Forensics and Incident Response (DFIR) team. In addition to the analysis of more than 700 attacks investigated as part of Group-IB’s own incident response engagements and cyber threat intelligence activity in 2021, the report also examines ransomware DLS.
Human-operated ransomware attacks have maintained the global cyber threat landscape lead by solid margins over the last three years. The rise of initial access brokers described in Group-IB’s Hi-Tech Crime Trends report and the expansion of Ransomware-as-a-Service programs (RaaS) have become the two main driving forces behind continuous growth of ransomware operations. RaaS made it possible for low-skilled cybercriminals to join the game to ultimately bring the victim numbers up.
Based on the analysis of more than 700 attacks in 2021, Group-IB DFIR experts estimated that the ransom demand averaged $247,000 in 2021, 45% more than in 2020. Ransomware evolved with more sophistication which is clearly visible from the victim’s downtime, which increased from 18 days in 2020 to 22 days in 2021.
RaaS programs started offering their affiliates not only ransomware builds, but also custom tools for data exfiltration to simplify and streamline operations. As such, the double extortion technique became even more widespread sensitive victim data was exfiltrated as a leverage to get the ransom paid in 63% of cases analyzed by Group-IB DFIR team. Between the Q1’2021 and Q1’2022, ransomware gangs posted data belonging to more than 3,500 victims on DLS. Most companies whose data was posted on DLS by ransomware operators in 2021 were based in the United States (1,655), Canada (176), and the UK (168), while most organizations affected belonged to the manufacturing (322), real estate (305) and professional service (256) industries.
Lockbit, Conti, and Pysa turned out to be the most aggressive gangs with 670, 640, and 186 victims uploaded on DLS respectively. The two of the newcomers to the Big Game Hunting in 2021, Hive and Grief (a rebrand of the DoppelPaymer), quickly made its way to the big league of top 10 gangs, accounted for by the number of victims posted on DLS.
Bots are not what they seem
Exploitation of public-facing RDP servers once again became the most common way to gain an initial foothold in the target network in 2021 47% of all the attacks investigated by Group-IB DFIR experts started with compromising an external remote service.
Spear phishing emails carrying commodity malware on board remained second (26%). Commodity malware deployed at the initial stage has become increasingly popular among ransomware actors. However, in 2021 the attribution of ransomware attacks became increasingly complicated since many bots such as Emotet, Qakbot, and IcedID were being used by various threat actors, unlike in 2020, when certain commodity malware families had strong affiliation with specific ransomware gangs. For instance, Group-IB DFIR team observed that IcedID was used to gain initial access by various ransomware affiliates, including Egregor, REvil, Conti, XingLocker, RansomExx.
In general, many ransomware affiliates relied on living-off-the-land techniques and legitimate tools during the attack lifecycle. Commodity malware was often used to start post-exploitation activities via loading frameworks such as Cobalt Strike (observed in 57% of the attacks).
However, some ransomware gangs were seen trying very unconventional approaches: REvil affiliates leveraged zero-day vulnerabilities to attack Kaseya’s clients. BazarLoader, used in Ryuk operations, was distributed via vishing (voice phishing). Phishing emails contained information about “paid subscriptions”, which could allegedly be canceled by phone. During the call, the threat actors lured the victim to a fake website and gave instructions to download and open a weaponized document, which downloaded and ran BazarLoader.
Given multiple rebrands forced by the law enforcement actions as well as the merge of TTPs due to the constant migration of affiliates from one Ransomware-as-a-Service (RaaS) program to another it is becoming increasingly challenging for security professionals to keep track of the ever-evolving tactics and tools of ransomware threat actors. To help corporate cybersecurity navigate through and prepare for ransomware incidents we outlined the main trends and TTPs changes and turned them into actionable insights mapped to and organized according to the MITRE ATT&CK® matrix.

Head of Group-IB DFIR team
The second 2021/2022 edition of the “Ransomware Uncovered” report features a MITRE ATT&CK® matrix which contains information about TTPs most frequently employed during human-operated ransomware attacks to help corporate cybersecurity teams brace for ransomware incidents. The new report is available for download via Group-IB’s website.