Group-IB, a global threat hunting and adversary-centric cyber intelligence company, has presented its new report “Ransomware Uncovered 2020-2021”. The research dives deep into the global ransomware outbreak in 2020 and analyzes major players’ TTPs (tactics, techniques, and procedures). By the end of 2020, the ransomware market, fuelled by the pandemic turbulence, had turned into the biggest cybercrime money artery. Based on the analysis of more than 500 attacks observed during Group-IB’s own incident response engagements and cyber threat intelligence activity, Group-IB estimates that the number of ransomware attacks grew by more than 150% in 2020, with many restless players having joined the Big Game Hunting last year. In 2020, ransomware attacks on average caused 18 days of downtime for the affected companies, while the average ransom amount increased almost twofold. Ransomware operations turned into robust competitive business structures going after large enterprises, with Maze, Conti, and Egregor gangs having been at the forefront last year. North America, Europe, Latin America, and the Asia-Pacific became the most commonly attacked regions respectively.
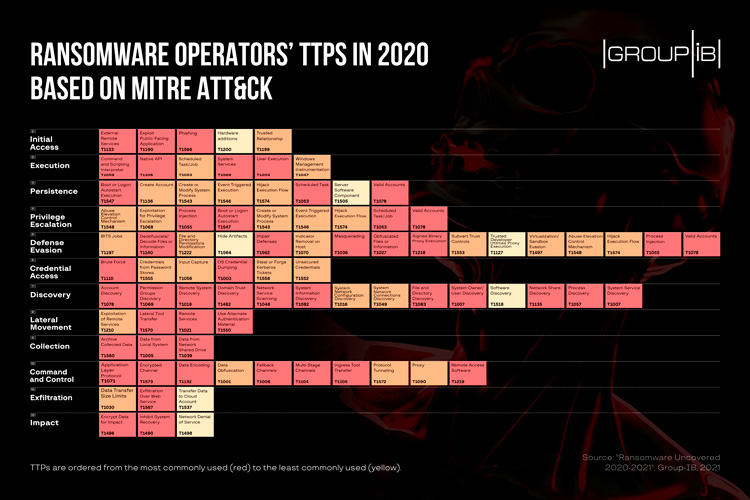
To keep the cybersecurity professionals up to date with how ransomware gangs operate and help the defense teams thwart their attacks, Group-IB’s DFIR team has for the first time mapped the most commonly used TTPs in 2020 in accordance with MITRE ATT&CK®. If you are a cybersecurity executive, make sure your technical team receives the copy of this report for comprehensive threat hunting and detection tips.
The gold rush of 2020
COVID-19 made many organizations, distracted with mitigating the fallout from the pandemic, vulnerable to cyber threats. Ransomware turned out to be the one that capitalized on the crisis most. The attacks not only grew in numbers (more than 150%) but also in scale and sophistication the average ransom demand increased by more than twofold and amounted to $170,000 in 2020. The norm seems to be shifting toward the millions. Group-IB DFIR team found out that Maze, DoppelPaymer, and RagnarLocker were the greediest groups, with their ransom demands averaging between $1 million and $2 million.
On a technical level, public-facing RDP servers were the most common target for many ransomware gangs last year. Against the backdrop of the pandemic that caused many people to work from home, the number of such servers grew exponentially. In 52% of all attacks, analyzed by Group-IB DFIR team, publicly accessible RDP servers were used to gain initial access, followed by phishing (29%), and exploitation of public-facing applications (17%).
Big Game Hunting targeted ransomware attacks against wealthy enterprises continued to be one of the defining trends in 2020. In hope to secure the biggest ransom possible, the adversaries were going after large companies. Big businesses cannot afford downtime, averaging 18 days in 2020. The operators were less concerned about the industry and more focused on scale. It’s no surprise that most of the ransomware attacks, that Group-IB analyzed, occurred in North America and Europe, where most of the Fortune 500 firms are located, followed by Latin America and the Asia-Pacific respectively.
A chance of easy money prompted many gangs to join the Big Game Hunting. State-sponsored threat actors who were seen carrying out financially motivated attacks were not long in coming. Groups such as Lazarus and APT27 started to use ransomware during their operations.
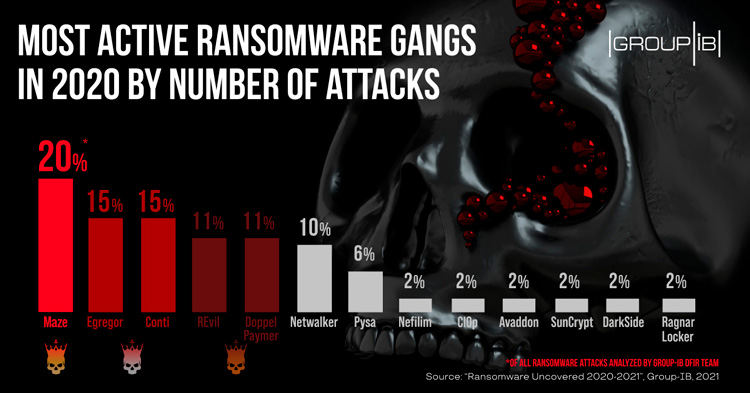
Conti, Egregor, and DarkSide all joined the ransomware gold rush in 2020. Many of them were so prolific that they made it to the top of the most active gangs in their debut year. The top 5 most active ransomware families, according to Group-IB, were Maze, Conti, Egregor, DoppelPaymer, and REvil. Not all of them lasted for long for various reasons.
The growing threat of ransomware has put it in the spotlight of law enforcement. Some gangs operating under the Ransomware-as-a-Service (RaaS) model, such as Egregor and Netwalker, were impacted by the police efforts. Another notorious RaaS collective, Maze, called it quits at the end of 2020. Despite these events, the ransomware business continues prospering, with Ransomware-as-a-Service model being of the driving forces behind this phenomenal growth.
Very organized crime
Ransomware-as-a-Service involves the developers selling/leasing malware to the program affiliates for further network compromise and ransomware deployment. The profits are shared between the operators and program affiliates. This business model with everyone focusing on what they do best can generate millions as the earnings are only limited to the number of affiliates the operators can attract. Group-IB DFIR team observed that 64% of all ransomware attacks it analyzed in 2020 came from operators using the RaaS model.
The prevalence of affiliate programs in the underground was the underlying trend of 2020. Group-IB Threat Intelligence & Attribution system recorded the emergence of 15 new public ransomware affiliate programs last year.
Mortal Combo: most common TTPs
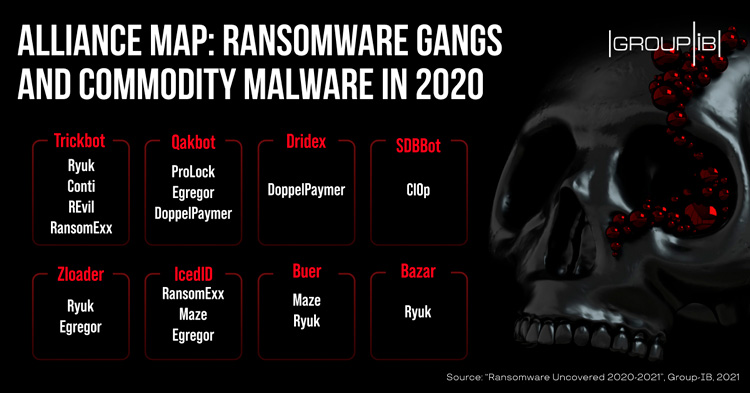
With the rise of ransomware in 2020, cybercrime actors who use commodity malware such as Trickbot, Qakbot, and Dridex helped many ransomware operators to obtain initial access to target networks more and more often. Last year, a lot of botnet operators partnered with ransomware gangs:
It’s important to detect malware like Trickbot at the early stages to prevent the data from being encrypted before the attackers move laterally. Most of these commodity malware families are capable to perform their activities silently and can hide from traditional sandboxing solution without raising the flag. Advanced Managed XDR platform allow to detect such threats by performing behavior analysis of emails, files, and links. It is crucial to extract and fully detonate discovered payloads in a safe isolated environment, harvesting indicators of compromise that help in subsequent threat hunting activities.
PowerShell was the most frequently abused interpreter for launching the initial payload. Its popularity among the attackers is explained by the fact that the interpreter is part of every Windows-based system, hence it’s easier to disguise malicious activity. Another theme of 2020, however, was the active exploitation of Linux with some threat actors adding corresponding versions to their arsenal.
In the credential access stage, threat actors often used brute force with NLBrute and Hydra being the most popular tools, based on Group-IB’s IR engagements. To obtain valid privileges, ransomware operators in 2020 often used credential dumping retrieving all the passwords from the machine. The attackers’ favorite tools here were ProcDump, Mimikatz, and LaZagne.
Based on Group-IB’s DFIR team observations, in 2020, ransomware operators spent 13 days on average in the compromised network before encrypting data for impact. Before deploying ransomware, operators did their best to find and remove any available backups, so that it would be impossible for the victim to recover encrypted files. Another factor, which allowed the gangs to ensure a higher success rate, was the exfiltration of critical data to use it as a leverage to increase the chances of the ransom being paid the trend set by the infamous Maze collective.
The pandemic has catapulted ransomware into the threat landscape of every organization and has made it the face of cybercrime in 2020. From what used to be a rare practice and an end-user concern, ransomware has evolved last year into an organized multi-billion industry with competition within, market leaders, strategic alliances, and various business models. This successful venture is only going to get bigger from here. Due to their profitability, the number of RaaS programs will keep growing, more cybercriminals will focus on gaining access to networks for resale purposes. Data exfiltration effectiveness can make it another big niche, with some actors abandoning the use of ransomware at all. Growing ransom demands will be accompanied by increasingly advanced techniques. Given that most attacks are human-operated it is paramount for organizations to understand how attackers operate, what tools they use in order to be able to counter ransomware operators’ attacks and hunt for them proactively. It is everyone’s concern now.

Senior digital forensics analyst at Group-IB
The full technical analysis of the adversaries’ TTPs mapped to and organized in accordance with MITRE ATT&CK® as well as threat hunting and detection tips put together by Group-IB Digital Forensics and Incident Response (DFIR) team, is available in the new report “Ransomware Uncovered 2020-2021“.