Group-IB, an international company that specializes in preventing cyberattacks, has uncovered a malicious code designed to steal customers’ payment data on seven online stores in the UK and the US. The injected code has been identified as a new JavaScript Sniffer (JS Sniffer), dubbed by Group-IB as GMO. Group-IB Threat Intelligence team first discovered the GMO JS Sniffer on the website of the international sporting goods company FILA UK, which could have led to the theft of payment details of at least 5,600 customers for the past 4 months.
Nothing to be sniffed at
Most recent breaches similar to this include British Airways and Ticketmaster which were first analyzed by RiskIQ research team, where cybercriminals managed to compromise personal information of thousands of travelers and concert goers with a few of lines of code. British Airways and Ticketmaster websites were infected with JS Sniffers, a type of malicious code injected into a victim’s website designed to steal a consumer’s personal data including payment card details, names, credentials etc. FILA UK website (fila.co[.]uk) became cybercriminals’ new major target on the UK market . GMO JS Sniffer has also been discovered on 6 other websites of US-based companies. This type of attack is especially dangerous given that it can be applied to almost any e-commerce site around the world. Group-IB made multiple attempts to alert FILA, which was known to be impacted by GMO. Six other websites affected by this JS Sniffer were notified upon discovery as well. Group-IB team has also reached out to local authorities in the UK and the US to conduct outreach.
Group-IB’s Threat Intelligence team first discovered GMO on the FILA UK website. The malicious code was detected in early March 2019. In the course of further research it was revealed that GMO JS Sniffer has presumably been collecting customer payment data since November 2018. According to Alexa.com, the number of fila.co[.]uk unique monthly visitors is estimated at around 140k per month. According to IRP, UK market research firm, a minimum conversion into purchase for fashion and clothing ecommerce is equal to 1%. Using very conservative estimates, payment and personal details of at least 5,600 customers could have been stolen by cybercriminals — everyone who has purchased items on fila.co.uk since November 2018 has potentially had their details compromised. Typically, after customer data is stolen, it is usually resold on underground cardshops. Another scheme of cashing out involves the use of compromised cards to buy valuable goods, e.g. electronics, for onward sale.
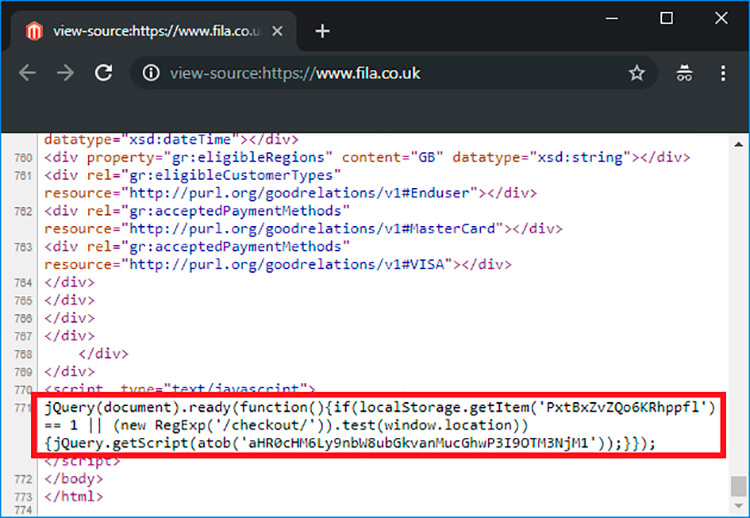
One-line card stealing code downloads a JavaScript Sniffer once a customer lands on a checkout page, which intercepts credit card data and sends it to local storage. After, the payment cards’ details are sent to the JS Sniffer’s gate which is located on the same server as a JS Sniffer script itself. Cybercriminals might have injected a malicious code by either exploiting a vulnerability of Magento CMS (content management system), used by FILA.co.uk, or simply by compromising the credentials of the website administrator using special spyware or cracking password with brute force methods. We dubbed this JS Sniffer family GMO because the malware uses gmo[.]li host.

Group-IB CTO and Head of Threat Intelligence
Fig. 1 The screenshot shows a one-line code (line # 771) that downloads a JS Sniffer designed to steal customers’ data once a user lands on a checkout page.
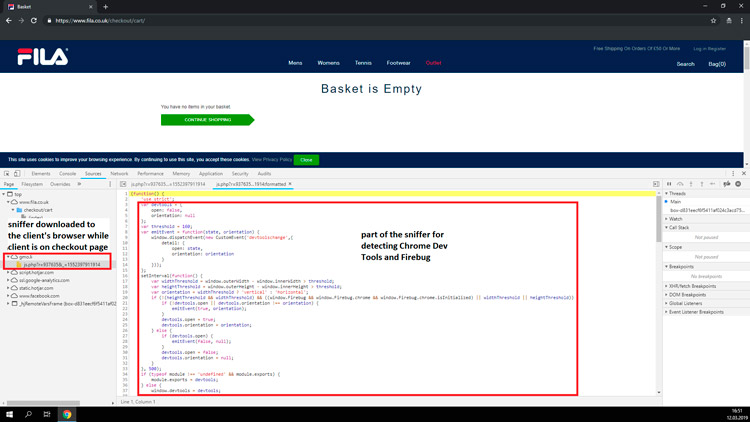
Fig. 2 The screenshot shows part of the JS Sniffer that detects Chrome Dev Tools and Firebug & the Sniffer downloaded to user’s browser once a user lands on a checkout page
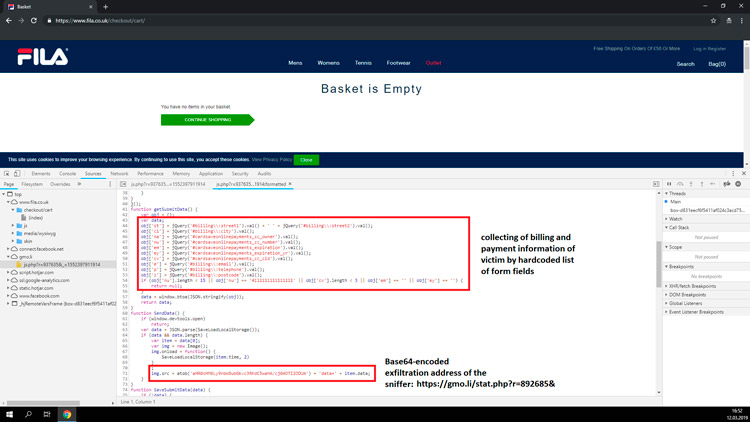
Fig. 3 The screenshot shows part of the JS Sniffer with functions for collecting victim’s billing and payment information and sending extracted information to cybercriminals via image request
Fig. 4 The screenshot shows part of the JS Sniffer that calls functions for collecting and sending victim’s payment information to cybercriminals
Later Group-IB’s specialists found other websites infected with GMO JS Sniffer. The list included six ecommerce stores with a total of around 350,000 monthly unique visitors (according to Alexa.com rankings): http://jungleeny[.]com (Home design store), https://forshaw[.]com/ (Pest Management Products Store), https://www.absolutenewyork[.]com/ (Cosmetics Store), https://www.cajungrocer[.]com/ (Online Grocery Store), https://www.getrxd[.]com/ (Training Equipment Store), https://www.sharbor[.]com/ (Video Editing Apparel store).
E pluribus unum?
GMO is a family of JS Sniffers that targets Magento-based online stores. GMO can detect Firebug and Google Developer Tools, which allows the sniffer to remain undetected. Group-IB’s Threat Intelligence team discovered that GMO has been active since May 2018. The domain name used for the sniffer’s codes storage and as a gate for stolen data collection was registered on May 7, 2018. The newly discovered GMO JS Sniffer is one of the 15 families of sniffers described by Group-IB in its new report that the company is prepping to release soon. Group-IB Threat Intelligence customers will be the first to receive the report. Nine out of these fifteen JS Sniffers’ families were not previously researched.
JS Sniffers is a type of malware that remains poorly researched. Despite its simplicity, it is capable of causing massive financial and reputational damage to huge international corporations and therefore should not be underestimated. Recent data breaches at British Airways and Ticketmaster proved this point. And not only small online stores get affected, but also payment systems and banks whose clients’ suffer from payment data leaks. The umbrella term «Magecart» given to these attacks by RiskIQ analysts should be much broader than that. There are many more groups using distinct families of JS Sniffers capable of targeting online stores. Since in some cases it is difficult to determine how many people use the sniffer, Group-IB experts call them families, not groups. Every family of JS Sniffers has unique characteristics and requires a detailed analysis. Group-IB Threat Intelligence team continuously analyses new types of JS Sniffers: multipurpose and specific, designed to target particular content management systems. Considering, the size of the market and the mounting threat JS Sniffers pose Group-IB decided to analyze several sniffers’ families enriching the knowledge about this malware significantly adding to the prior attempts to research JS Sniffers.

Group-IB CTO and Head of Threat Intelligence