Group-IB’s Computer Emergency Response Team (CERT-GIB) analyzed hundreds of coronavirus-related phishing emails between February 13 and April 1, 2020. Spyware turned out to be the most common malware class hiding in fraudulent COVID-19 emails, with AgentTesla topping the list of phishers’ favorite strains. Group-IB researchers also discovered that coronavirus had split hacker underground into those who capitalize on the pandemic and those who strongly oppose exploiting the crisis. Group-IB urges users to stay vigilant and pay close attention to any emails about coronavirus, especially now that most employees are working from home.
Spyware: the most likely COVID-19 payload
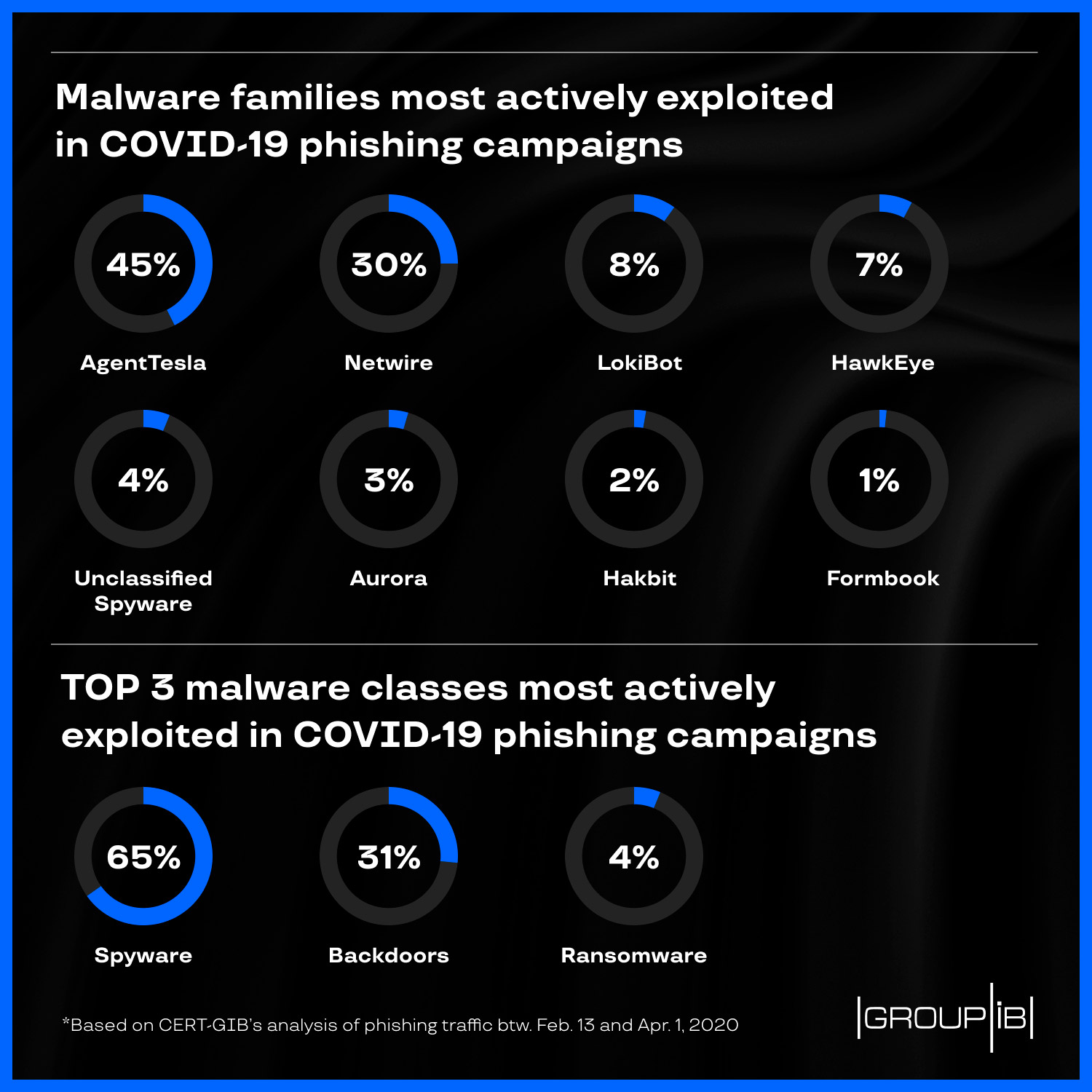
CERT-GIB’s report is based on analyses of coronavirus-related phishing traffic by the Threat Detection System (TDS) Polygon as part of operations to prevent threats spread online. Most COVID-19-related phishing emails analyzed had different spyware strains embedded as attachments. AgentTesla (45%), NetWire (30%), and LokiBot (8%) were the most actively exploited malware families. With some minor differences, all these malware samples are designed to collect personal and financial data. They can retrieve user credentials from browsers, mail clients and file transfer protocol (FTP) clients, capture screenshots, and secretly track user behavior and send it to cybercriminals’ C&Cs.
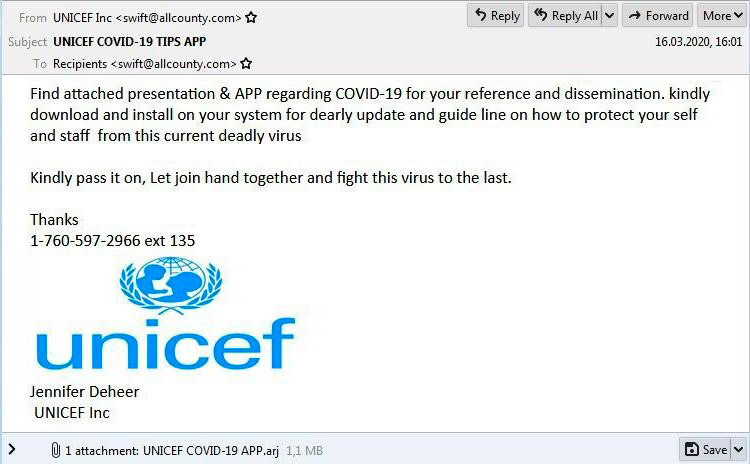
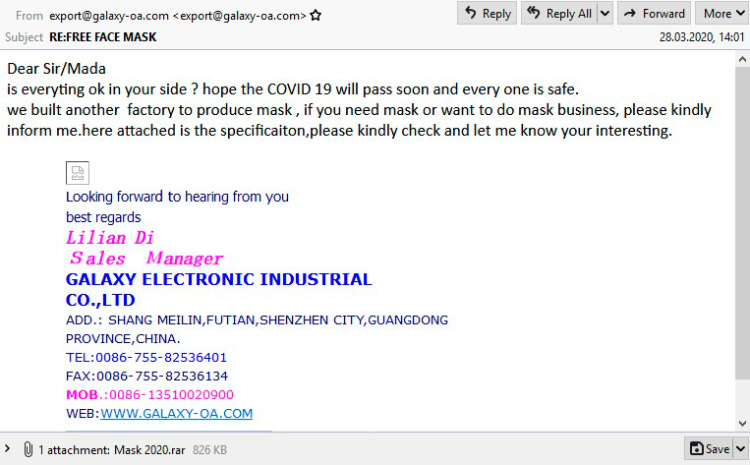
Most of the emails detected were in English. Those behind such COVID-related campaigns target government organizations and private companies. The emails were masked as advisories, purchase orders, face masks offers, and alerts or safety recommendations from the World Health Organization, UNICEF, and other international agencies and private companies such as Maersk, Pekos Valves, and CISCO. These companies are in no way involved in the scams, of course.
Fig. 1. Example of a malicious email disguised as “UNICEF COVID-19 TIPS APP” with spyware in the attachment. Source: CERT-GIB
Fig. 2. Example of a phishing email disguised as an offer of free masks. Source: CERT-GIB
Cybercriminals have used the following file extensions to deliver malware samples: .gz, .ace, .arj, and .rar, three of which are archive formats. It’s worth noting that .rar also became the second commonly used format to deliver archived malware in H1 2019 and accounted for 25% of all archived malicious files detected by Group-IB’s CERT in the first half of 2019. To trick antivirus software, threat actors include the passwords for accessing the content in the email subject line, in the archive name, or in subsequent correspondence with the victim. Unless behavioral analytics is employed, such malware is likely to remain undetected.
Hacker underground split over coronavirus
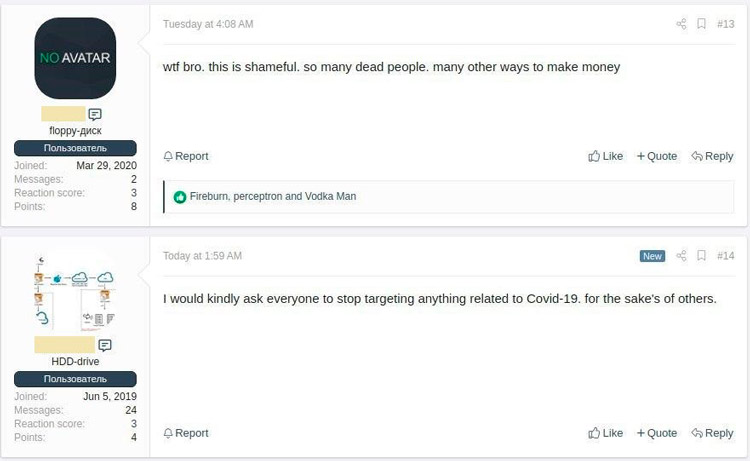
Phishing emails exploiting coronavirus panic accounted for about 5% of all malicious emails detected and analyzed by CERT-GIB over the review period. This relatively small percentage can partly be explained by the fact that not all cybercriminals are capitalizing on coronavirus fears. According to media reports, some ransomware gangs have stated that they will not target medical organizations during the outbreak. Group-IB’s Threat Intelligence team has also detected a number of underground forum posts by users who urge others to stop exploiting COVID-19 for malicious purposes.
Fig. 3. Posts on a hacker forum in which users urge others to stop exploiting COVID-19. Source: Group-IB Threat Intelligence
The coronavirus crisis has affected many economies and the underground hacking economy is no exception. Group-IB Threat Intelligence has tracked down more than 500 posts on underground forums in which users offered coronavirus discounts and promotional codes on DDoS, spamming, and other services to stimulate demand, affected by the pandemic.
Fig. 4. Post on a hacker forum from a user providing a 20% discount and promocode on spamming and domain registration services. Source: Group-IB Threat Intelligence
Fig. 5. Post on a hacker forum from a user announcing discounts on DDoS services due to the crisis caused by COVID-19. Source: Group-IB Threat Intelligence
Remote work increases the likelihood of cyberattacks
People should remain particularly vigilant now that most people are working from home due to the pandemic. We predict an increase in the number of cyberattacks on unprotected home networks used by employees who have switched to remote work as the virus spreads offline. Corporate security teams should reassess their approach to securing corporate digital space by strengthening their perimeter, which now includes employees’ home devices. A single employee who opens a malicious file from an undetected phishing email could jeopardize the whole company’s operations.

Head of Group-IB’s Computer Emergency Response Team (CERT-GIB)
All remote employees’ email accounts as well as the VPNs used to access corporate networks should be protected with two-factor authentication at least. Moreover, implementing network protection solutions is needed to analyze incoming and outgoing emails. Network segmentation and access right differentiation are both required. It is also recommended that even remote user activity be covered by the organization’s perimeter security tools.