A member of TipTop, a hacking group known for attacking customers of major Russian banks for several years, was arrested and convicted in Russia. The group, dubbed TipTop by Group-IB, used malware to steal money from payment cards. Their member’s arrest was the result of a joint operation by Russian cyber police units.
The group distributed their malware by disguising it as popular mobile apps. Downloading such an app prompted the download of the actual Trojan, which gave the hackers access to the mobile banking services the victims used.
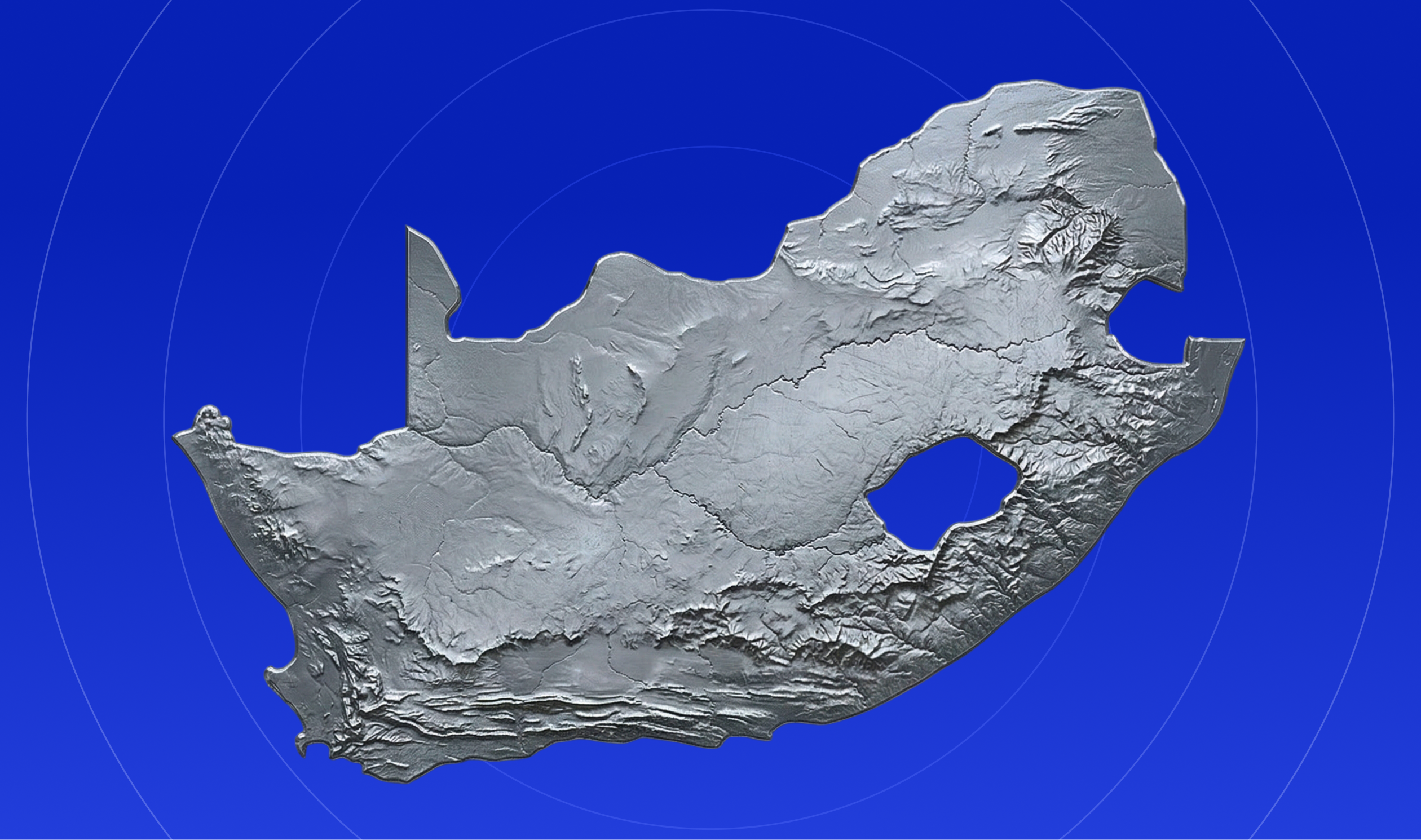
The group was dubbed TipTop and its main targets were customers of major Russian banks that used Android smartphones. The hackers delivered malware to victims’ devices via fake mobile apps disguised as banking apps, messengers, Adobe’s graphic design application, fake Google Play store app. The hackers placed links to the fake apps either on websites they designed themselves or on legitimate web resources they compromised. To increase the number of potential victims, the cybercriminals promoted these websites in search engines by purchasing ads for the keyword ‘mobile bank.

Head of Investigation Department, Group-IB
Once the user tried to download one of the malicious apps, the Hqwar Android banking Trojan (also known as Agent.BID) was installed on their device. The group tried other tools and money withdrawal schemes too, which made it difficult to attribute a particular attack to them. In 2015, the hackers used the Hqwar (Agent.BID) mobile Android Trojan to infect customers of Russian banks. In 2016, they started using the Honli Trojan, and in February 2016 an upgraded version of it, which antiviruses detected as Asacub.g. In the same year, the group tried infecting smartphones with Cron, a Trojan developed by their predecessors, which gave its name to that group. At the time, TipTop used the CatsElite (MarsElite) Trojan. In April 2017, they returned to Hqware (Agent.BID) but also used Lokibot and an upgraded version of the old Marcher (Rahunok) Trojan. All mobile Trojans used by the hackers could intercept and read SMS messages, record phone calls and send USSD requests, but their main goal was to steal payment card details either using phishing windows that copied legitimate application windows or employing web fakes designed to trick users into entering their credentials for online banking accounts. The groups’ C&Cs used to infect the devices and control botnets were located in Germany, USA and Ukraine at different times.
During the investigation, the police established that a previously convicted 31-year-old resident of the city of Krasnoyarsk, who transferred money from users’ accounts to the accounts and cards of cybercriminals, was responsible for stealing money from the residents of one of the regions in Russia (over $1,000).
The man was arrested and his home was searched. During the search, the police found and seized computers, hard drives, flash drives, phones, and SIM cards. According to the investigation, the detainee’s role in the TipTop group was to transfer money from users’ accounts to the accounts and cards of the cybercriminals.
The police opened a criminal case for an offence committed under article 273 of the Russian Criminal Code «Creation, use and dissemination of harmful computer programs». The accused was later convicted and received a two-year suspended sentence.
After the fall of the CRON gang in late 2016, TipTop, to which the detainee belonged, became one of the largest and most dangerous ones. With the use of Android Trojans, the cybercriminals have managed to infect over 800,000 smartphones. The damage from their activities is currently being established, but certain estimations suggest that the cybercriminal group could have stolen between USD 1,500 and 10,500 on a daily basis. Group-IB first detected the group’s activities in 2015. The group’s victims in a number of regions across Russia have been identified.

Head of Investigation Department, Group-IB