Group-IB, one of the global leaders in cybersecurity headquartered in Singapore, has discovered an unprecedented phishing attack in Vietnam. The campaign impersonates 27 popular Vietnam’s financial institutions and remains active at the time of writing. The cybercriminals seek to reap highly detailed personal information from the clients of those institutions to the extent of robbing their bank accounts. The fraudsters use techniques that allow them to bypass OTP verification. Group-IB’s Computer Emergency Response Team (CERT-GIB) has identified 240 interconnected domains that are a part of the phishing campaign’s infrastructure. Upon detection of this activity, CERT-GIB immediately notified Vietnam’s national computer emergency response team VNCERT.
All 240 domains have been blocked following CERT-GIB and local authorities’ efforts. Yet, new domains regularly appear. Group-IB continues to cooperate with domain registrars and other authorities to take down new domains as they are identified, stemming the potential for further financial loss from users and mitigating the damage to the reputation of the financial institutions involved.
Old but Gold
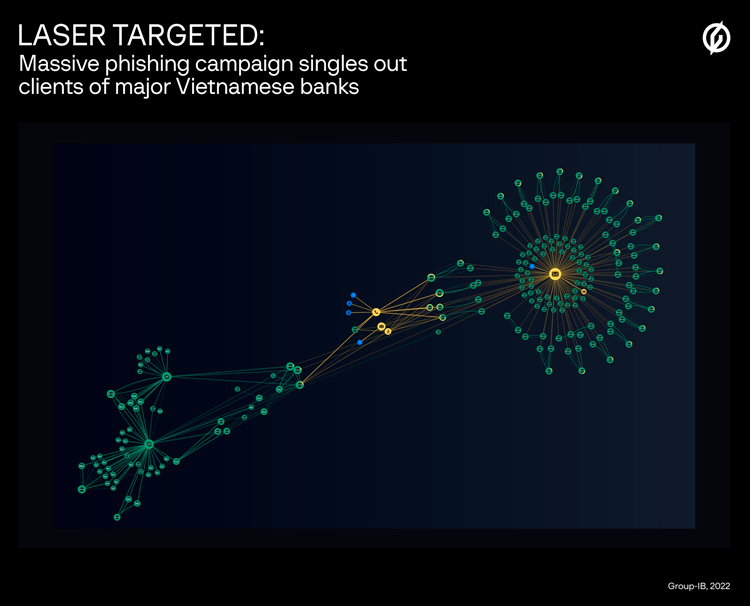
The campaign described initially launched in May 2019, which is when the first domain was registered. The latest phishing domain was activated on June 1, 2022. In all, thanks to Group-IB’s Graph Network Analysis tool, CERT-GIB was able to identify 240 interconnected domains:
Phishers’ infrastructure. Source: Group-IB Threat Intelligence system
Although those domains are now inactive, new domains are regularly added. CERT-GIB notes that this is by design: the domains are intended to only be active for short periods of time, which complicates detection and takedown. For this reason too, the actual number of domains could be significantly higher.
CERT-GIB was able to retrieve the number of visitors to 44 out of 240 websites identified, where web counters were installed. Just since the beginning of 2021, at least 7,800 potential victims visited these 44 phishing resources. The overall number of visitors and affected users is unknown but is believed to be significantly higher, taking into account the scale, duration of the fraudulent operations and the degree of sophistication in the methods used by the cybercriminals. The campaign is directed at major financial institutions of Vietnam with every phishing website, it uses an OTP hijacking scheme, and their communications tactics are highly customized and targeted.
Swiss Army Knife Phishing
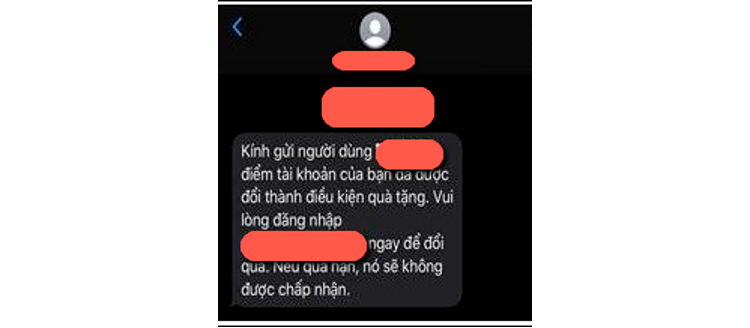
The phishing scheme leverages rogue SMS, Telegram and WhatsApp messages, and even comments on Facebook pages of legitimate Vietnamese financial service companies to lure victims to their phishing pages. The fraudulent messages are disguised to look like official communications coming from real banks, marketplaces or ecommerce companies. One of the scammers’ SMS, retrieved by CERT-GIB informed the victim that they have been awarded a gift and needed to login to their banking portal to claim it. The message said that the offer was set to expire soon, by which cybercriminals create a sense of urgency. One of the tactics used by the operators of the campaign is the usage of shortened URLs where an average user would be unable to differentiate the legitimacy of the URL.
SMS sent by the fraudsters
Upon clicking on such links, the victims are forwarded to a fake web page featuring the logos of 27 highly reputed banks and financial institutes either as a single page or as a drop-down option whereby victims can pick their registered bank.
Once the victim chooses its bank from the list, they are redirected to another phishing page disguised as a legitimate banking portal. Should the victim input their username and password, they are taken to the next fake web page where a One Time Password (OTP) is requested. At this point, the fraudsters use the already stolen credentials to login into the victim’s real account. After the victim receives an OTP from their bank (as requested by fraudsters), submitting it via the fake authentication page, this gives the cybercriminals full access to the victim’s bank account. With this data they can also initiate unauthorized illicit transactions.
Then, once the victim “logs in” to the fake account, they are presented with a message that says that “the transaction is still processing”.
This duplicitous methodology enables the cybercriminals to steal funds from victims’ accounts and to harvest a vast amount of personal data (such as name, address, national identity card details, phone number, DOB, and occupation) which is actively traded in the cybercriminal underground community or purchased by other threat actors for further targeted follow-up attacks on the victims.
Group-IB has observed offers to sell Vietnamese citizens’ information harvested as a result of phishing campaigns on underground markets. While it is unknown whether the information is authentic and is sourced directly from this phishing campaign or not, CERT-GIB’s analysts have seen first-hand instances of offers to sell data about holders of bank accounts in Vietnam.
Buyer beware
To date, the campaign appears restricted to Vietnam. CERT-GIB continues to monitor the infrastructure for new domains and phishing tactics. In the meantime, users should note that communications from their financial institutions that seek to create a sense of urgency or intimidation are red flags. It’s important to pay attention to the domain name of the URL in the browser and be wary of websites that appear to malfunction or create long chains of redirection. Users should avoid purchasing from unauthorized resellers or click on links that offer discounts. They are likely fraudulent, and it is critically important to confirm the credibility of the source. Ascertain if it is your financial institution’s official website, look for reviews, and call customer support if you are suspicious. Enabling two-factor authentication wherever possible and changing passwords from time to time are also good habits.
Cybercriminals exploit the lack of decent monitoring and blocking efforts to create fake sites. Companies impersonated by scammers should implement regular monitoring to observe fake sites that misuse their legitimate brand names. Map and attribute newly registered domains, which help to reveal patterns to improve the quality and scope of detection. Use an automated machine-learning based Digital Risk Protection system that is fueled by regular updates to improve its knowledge base about cybercriminals’ infrastructure, tactics, tools.