Group-IB, one of the global leaders in cybersecurity, has released new research on the state-sponsored hacker group APT41. The Group-IB Threat Intelligence team estimates that in 2021 the threat actors gained access to at least 13 organizations worldwide. While analyzing the group’s malicious campaigns, Group-IB experts uncovered interesting adversary techniques and artifacts left by the hackers that point to their origin. The report also reveals details of their “working days“.
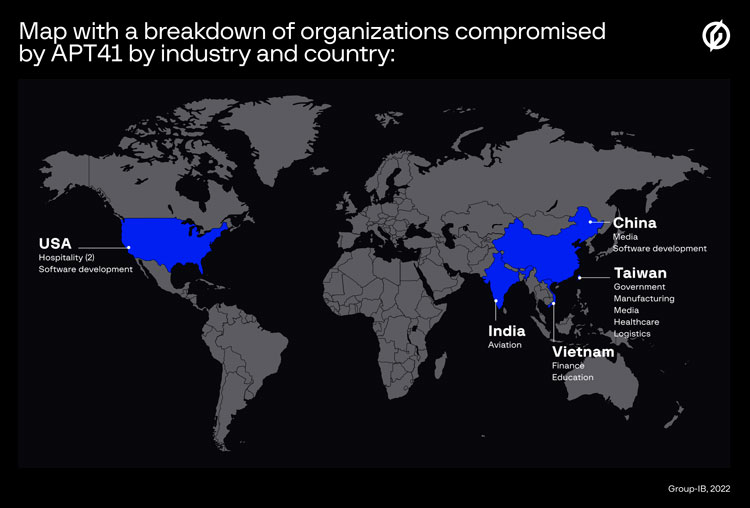
The state-sponsored hacker group APT41 (aka ARIUM, Winnti, LEAD, WICKED SPIDER, WICKED PANDA, Blackfly, Suckfly, Winnti Umbrella, Double Dragon), whose goals are cyber espionage and financial gain, has been active since at least 2007. Group-IB Threat Intelligence analysts identified four APT41 malware campaigns carried out in 2021 that were geographically spread across the United States, Taiwan, India, Vietnam, and China. The targeted industries included the public sector, manufacturing, healthcare, logistics, hospitality, education, as well as the media and aviation. According to Group-IB, there were 13 confirmed victims of APT41 in 2021, but the actual number could be much higher.
Our analysis shows that 2021 was an intense year for APT41. Research into the discovered tools and indicators of compromise revealed malicious activity and made it possible to notify businesses and government organizations about emerging or committed APT41 attacks. As a result, they could take the necessary steps to protect themselves or hunt for traces of compromise across their networks. In 2021, we sent over 80 early warnings related to APT41 in total.

Analyst within the APT Research Team at Group-IB
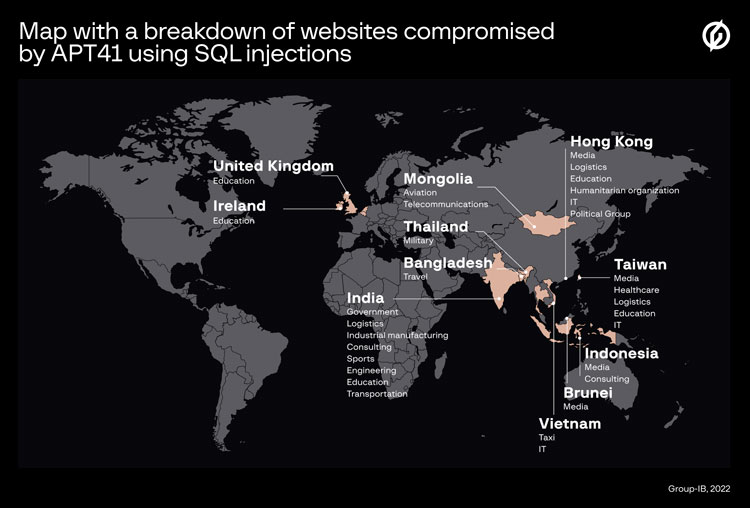
In the investigated campaigns, the group used the following reconnaissance tools: Acunetix, Nmap, SQLmap, OneForAll, subdomain3, subDomainsBrute, and Sublist3r. APT41 members usually use phishing, exploit various vulnerabilities (including Proxylogon), and conduct watering hole or supply-chain attacks to initially compromise their victims. However, in the recent campaigns examined by Group-IB, the attackers performed SQL injections on websites using the publicly available tool SQLmap as the initial attack vector. In some organizations, the group gained access to the command shell of the targeted server, while in others they accessed databases with information about existing accounts, lists of employees, and plaintext and hashed passwords. The SQL injections enabled the threat actors to infiltrate victim networks in half of the cases: 43 out of 86 websites turned out to be vulnerable.
Cobalt Strike: old but gold
Group-IB established that the group used a unique method of dividing a payload (a custom Cobalt Strike Beacon) in order to download malicious code to target devices and execute it. Once the payload was compiled, it was encoded in Base64 and then divided into chunks of 775 characters and added to a text file using a certain command. In one of the observed cases, in order to write the entire payload to a file, the threat actors needed to repeat this action 154 times. The same atypical method of dividing the payload was observed in the network belonging to another organization, where the threat actors divided the code into chunks of 1,024 characters. To write the payload fully, in this case they needed 128 iterations.
Group-IB researchers emphasize that the group usually used certain servers exclusively to host the Cobalt Strike framework, while they exploited others only for active scanning through Acunetix. The Group-IB TI team identified servers that were used for both, however. “Despite the servers being protected with the cloud service CloudFlare, which hides the real server addresses, the Group-IB Threat Intelligence system detected APT41 server backends, which helped monitor the group’s malicious infrastructure and quickly block their servers,“ a Group-IB specialist said.
A noteworthy finding by Group-IB related to Cobalt Strike is the use of listeners with custom SSL certificates. Listeners are used for accepting connections from the payload in order to maintain communication between bots and the C&C server. In the cases examined, APT41 used unique SSL certificates that mimicked ”Microsoft“, “Facebook” and ”CloudFlare”. According to Group-IB, servers with such certificates first emerged in early 2020. By the end of 2021, their number reached 106. The Group-IB team identified more than 100 Cobalt Strike servers that are used only by APT41. Most are no longer active. All information about adversary infrastructure and indicators of compromise are automatically sent to Group-IB Managed XDR (part of the Unified Risk Platform), which helps detect threats and identify attacks at an early stage.
Working on a schedule
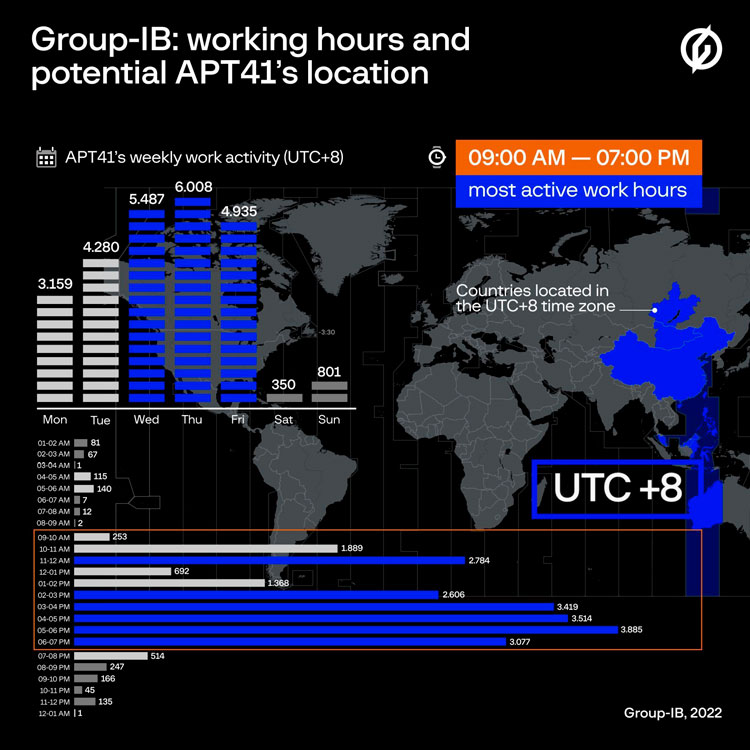
Research into APT41 malware campaigns from 2021 helped Group-IB Threat Intelligence analysts align all the group’s timestamps to UTC+8. As a result, they have come to the following conclusions. The group starts working at 9 AM and its activity stops around 7 PM. There are several countries in the attacker’s time zone, including China, Malaysia, Singapore, parts of Russia, and Australia.
Regarding threat actor attribution, the report provides a list of mostly Chinese IP addresses used to communicate with Cobalt Strike servers. The experts also noted the use of Chinese characters on the devices from which the attacks were conducted. Interestingly, the researchers noticed a specific Pinyin format being used to name directories. Pinyin is a romanization system that represents the sounds of the Chinese language using the Latin alphabet.