Four hours and eighteen minutes. That is how long it took the hacker group LockBit to penetrate the victim’s infrastructure and launch the ransomware. As is unfortunately often the case, the ransomware was delivered to the company’s network directly through a forgotten remote access tool (RDP).
When responding to cybersecurity incidents, Group-IB specialists often come across attacks conducted through forgotten and unknown digital assets such as RDP servers and legacy landing pages. The fact that infrastructure becomes forgotten can be ascribed to the human factor (e.g., a company employee gives remote access to a vendor’s specialist and forgets to revoke it afterwards), but unknown assets are more difficult to categorize.
Imagine the following situation. In 2016, a marketing specialist makes an urgent request to the IT department to create a landing page with the domain name “promotionforthisproduct2016.com” in order to promote a product. The domain was created and soon thereafter the promotion ended. A year goes by and the IT specialist leaves the company. Two years later, the marketing specialist follows suit. In 2020, the company hires a new Chief Security Officer who is not told anything about the domain or the potentially vulnerable infrastructure that hosts it.

Attack against a bank using LockBit ransomware
All around the world, Group-IB teams help customers with incident response, evidence collection, and mitigation of damage caused by a cyber incident. In a situation like the one above, the key task is to stop the malware as soon as possible, ideally at the earliest stages of the kill chain. Unfortunately, the ideal scenario is not always feasible. Sometimes the victim company’s specialists do not know what to do if an attack has been detected during its active phase, while in other cases they cannot keep up with how fast an attack spreads.
As people say, the Internet remembers everything — and not just the photos of Beyoncé or Barbra Streisand’s house, but any external IT assets that companies create. Assets can also be seen by threat actors, who can use vulnerabilities and weaknesses to carry out attacks.
How do threat actors find out that infrastructure is unprotected or has vulnerabilities?
Hackers can find unprotected or insufficiently protected assets simply by monitoring the Internet and using open source scanning tools, but this approach requires some basic tech skills. There is an even simpler way: using dedicated dark web resources that sell access rights. Some criminals specialize in identifying vulnerable servers, and instead of exploiting the weaknesses in the infrastructures themselves, they sell the information to other hackers.
The image below shows MagBo, an in-demand marketplace that currently sells access to more than 170,000 hacked servers.
Between H2 2020 and H1 2021, the total value of the market for access to corporate networks amounted to $7 million, with 16% growth year-on-year. Group-IB analysts reported a 204% increase in the number of unauthorized access offers and a 205% increase in the number of sellers.
The market for access to corporate networks grew extremely quickly as companies had to urgently switch their employees to remote work due to the Covid-19 pandemic, thereby creating a huge influx of new assets that businesses did not have time to properly secure. Though they surely intended to manage and protect these assets after the fact, things don’t always go according to plan.
The website MagBo is only one of many examples of resources that sell access to private servers. Many such resources specialize in selling access to servers with open ports 3389 (for RDP) and 443 (for HTTPS), and not only ports 25 and 80 as can be seen in the screenshot.
When it comes to vulnerabilities, a threat actor’s task is fairly simple: to detect any outdated software installed on the victim’s assets. In more recent versions of their software, manufacturers patch vulnerabilities that could be exploited by hackers. As such, to keep up their security posture, users only need to update the software installed on their systems from time to time. Yet in our experience, many customers fail to do it in a timely manner.
One of Group-IB’s primary objectives is to prevent potential attacks on our clients. Towards this goal, we have released an EASM solution called Group-IB Attack Surface Management (ASM).
Attack Surface Management is a part of Unified Risk Platform, a single platform comprising products and services for managing cyber risks related to targeted attacks, data leaks, fraud, phishing, and brand abuse.
Group-IB Attack Surface Management indexes the entire IPv4 space, thereby identifying every Internet-facing asset and logging important data points about each one — what software and services are running, which ports are open, and so on. Using other publicly available information (such as registrar data, DNS records, Whois data, SSL certificates, and more), the solution identifies digital links between Internet-facing assets. By simply entering the primary domain of a business, Group-IB Attack Surface Management maps out the organization’s entire external attack surface, with an eye towards discovering shadow IT and other hidden risks.
The solution helps visualize the entire external attack surface from an attacker’s point of view, assess any risks and vulnerabilities, and address weaknesses proactively.
What is Group-IB Attack Surface Management?
Attack Surface Management is a cloud-based SaaS solution rooted in Group-IB Threat Intelligence. ASM monitors and manages the external attack surface and is fully agentless. The solution detects all known and unknown Internet-facing assets related to your organization and creates an up-to-date inventory.
Group-IB monitors the Internet 24/7 and detects IPs, domains, SSL/TLS certificates, cloud and local storage systems, and any software running on the detected hosts. All detected assets are categorized and checked for vulnerabilities. In order to better understand any problem areas, the solution offers eight categories, each with a rating on a scale from 0 to 10, where 0 means “many issues” and 10 means “no issues”.
Advantages of Threat Intelligence
One of the main competitive advantages of Group-IB Attack Surface Management is the ability to promptly obtain up-to-date vulnerability data collected by Group-IB Threat Intelligence. The solution also detects corporate system compromise by continuously scanning hacker groups, botnets, dark web mentions, leaks of login and password pairs, WebShell infestations, JS sniffers, malware hosts, etc. ASM even detects “invisible” attacks using unique IoCs, threat attribution and prioritization, and faster response based on data about the attacker’s behavior, tools, and tactics.
All this data helps you to recognize when your company becomes a target for threat actors and therefore makes it possible to preemptively block attacks against your employees and customers. For user convenience, all detected digital assets are visualized using the network infrastructure graph, another next-gen product developed by Group-IB engineers.
You have identified a problem area. What should you do next?
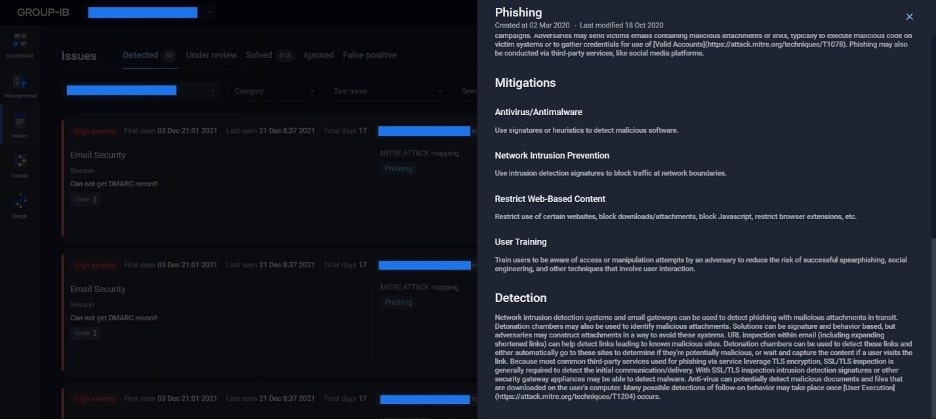
To make things easier for you and your clients, we have created a dedicated section called “Issues” where you can filter detected problems and obtain detailed information about what hacker groups use these vulnerabilities, how these vulnerabilities are exploited (indicating TTP according to the MITRE ATT&CK® matrix) and — most importantly — the recommendations we provide to solve these issues.
We therefore not only inform the client that, for example, they do not have the DMARC set up on a specific domain, but also provide a detailed action plan to solve the issue, including informing employees why it is crucial to thoroughly check the sender of every email:
In this section, users can also manually prioritize issues and mark them as solved or as false positives.
The Assets section has six asset category tabs to help customers troubleshoot issues.
- Domains & subdomains
Large enterprises have thousands of domains and subdomains to manage and protect. In some cases, domains are deprecated and should be taken offline. The “Domains” tab helps customers identify outdated and unnecessary domains so that they can be decommissioned. Additionally, this tab shows risks on existing domains that may require remediation. - IP addresses
Just as with domains and subdomains, IP addresses are a major component of a business’s attack surface, and there may be thousands – or even tens of thousands – of IP addresses to manage. This tab gives an up-to-date inventory of all of the IP addresses that are connected to the customer’s primary domain, providing visibility on the entire digital estate as well as potential risks and security issues. - IP subnets
IP subnets can give threat actors important information about a business’s network architecture – how many subnets the digital estate is broken into, the maximum number of hosts that each subnet can support, and potentially the purpose and scope of each subnet, based on the types of external assets they contain. This tab gives a quick view of all the subnets within the customer’s IT infrastructure. - SSL certificates
If SSL certificates are not properly managed, they may expire and cause expensive unplanned downtime for websites and applications. The “SSL Certificates” tab shows issues such as certificates that are approaching (or past) the expiration date, self-signed certificates, outdated TLS protocols, and other potential security risks.
The Attack Surface Management Assets section also includes two useful tabs that can help customers strengthen security:
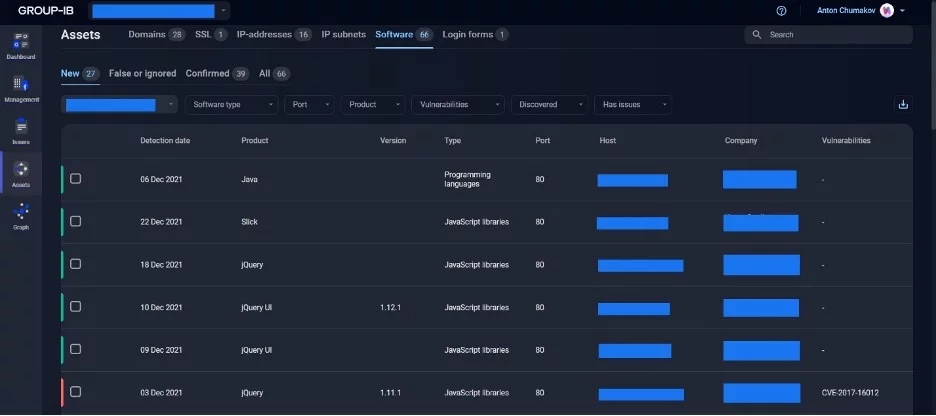
- Software & Services
In this section, customers can review all software that was automatically discovered on hosts and filter it by vulnerability, product, and product version.As shown on the picture below, the interface is very simple, and even a user without any knowledge of information security will easily understand how to react to various vulnerabilities:
For example, a host has jQuery v. 1.11.1 installed with an unpatched vulnerability CVE-2017-16012 (this vulnerability is more than four years old, but this one’s on the customer), while another host has jQuery v. 1.12.1 where this vulnerability has been fixed. The most logical step would be to simply update jQuery. - Login forms
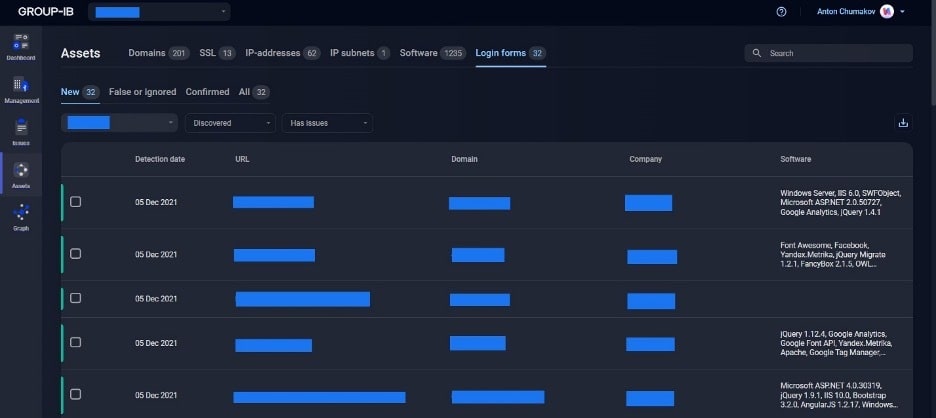
Remote access services are an essential tool for connecting to remote servers, databases, cloud instances, and more. However, if these remote login forms are left exposed to the public Internet– and not properly hardened with strong credentials and multi-factor authentication– they may give threat actors an easy path to breach the corporate network.This section shows Internet-facing login forms and services, like VPN gateways, RDP and SSH ports, etc., which are installed on these hosts:
We don’t mean to suggest that each of these login forms is insecure. Many are likely hardened in accordance with the company’s internal security policies. However, most customers cannot guarantee that each employee will follow the company’s policy, and threat actors only need one vulnerable server to gain a foothold in the network.
For instance, let’s imagine that a company’s administrator created a new domain name back in 2018 at the request of the marketing team for a short-term promotion. Suppose further that the administrator set up the login/password pair as “admin/admin” so that marketing specialists would not get bogged down with complicated passwords. Brute-forcing this domain will be a piece of cake for even moderately skilled hackers. Obtaining access to one of the company’s assets will enable threat actors to proceed with the attack.
Due to the functionalities described above, Attack Surface Management helps carry out a thorough assessment of the company’s security posture and provides valuable data to all information security specialists, system administrators, and MSSP providers. Attack Surface Management uses threat intelligence insights that will also benefit the company’s senior management who are not as savvy in information security and IT as technical specialists.
The simple and user-friendly dashboard with a risk-scoring function helps assess the objective state of security in real time. Meanwhile, problem-solving recommendations ensure that the company’s security stance is promptly improved.
Discover the external attack surface with Attack Surface Management
Improve your security posture and manage your risks!