Get 24/7 incident response assistance from our global team
- APAC: +65 3159 4398
- EU & NA: +31 20 890 55 59
- MEA: +971 4 540 6400
- LATAM: +56 2 275 473 79
Get 24/7 incident response assistance from our global team
Please review the following rules before submitting your application:
1. Our main objective is to foster a community of like-minded individuals dedicated to combatting cybercrime and who have never engaged in Blackhat activities.
2. All applications must include research or a research draft. You can find content criteria in the blog. Please provide a link to your research or research draft using the form below.
Gain a comprehensive view of your Security Operations Center across people,
processes, and technology. Identify capability gaps, validate effectiveness, and
build a clear roadmap to higher maturity and resilience.

Self-assessments rarely show your true security posture. Without detection engineering, integrated threat
intelligence, and objective benchmarking, SOC teams struggle to prioritize resources, justify investments, and
plan their next stage of evolution.
of SOCs operate below their own target maturity level
of MITRE ATT&CK® techniques are covered by half of all SOCs
of SOCs have defined performance metrics to track improvement
Group-IB’s intelligence-powered SOC Assessment goes beyond standard maturity checks. Our methodology
combines the SOC-CMM and MITRE ATT&CK® SOC Assessment frameworks with extensive experience in threat
hunting, digital forensics, and incident response. Your SOC will be evaluated in every security domain — from
strategy and governance to day-to-day operations.
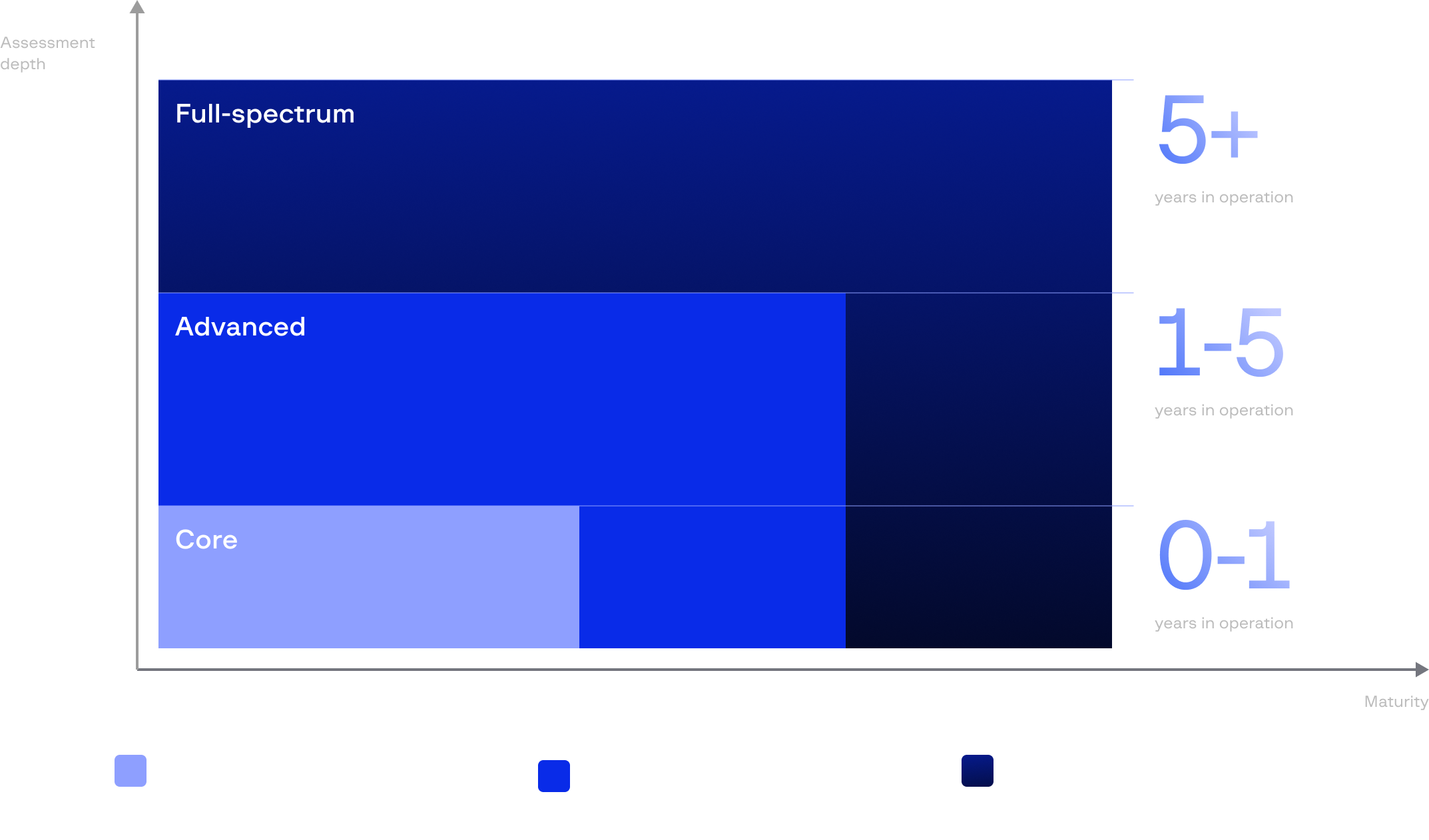


























































































Our compass will point you to the right assessment path
Make the most of our SOC Assessment as part of the Group-IB Services Retainer
and enjoy ongoing improvements, validation, and access to expert teams without
new contracts or extra costs.


A SOC assessment is a structured evaluation of your Security Operations Center’s maturity, capability, and beyond. It measures how effectively your people, processes, and technologies detect, investigate, and respond to threats.
Yes. It can be delivered on-site, remotely, or in a hybrid format depending on your region and scope. The process is designed to collect all the necessary information securely and without disrupting operations.
Group-IB uses the SOC-CMM model for maturity and capability scoring, MITRE ATT&CK® for detection mapping, and additional internal digital forensic and incident response and Threat Intelligence benchmarks to ensure accuracy and context.
Yes. We provide pre-audit support and readiness workshops for organizations preparing to achieve Defined, Validated, or Risk-Driven certification levels.
No. The process relies on interviews, documentation reviews, and read-only data collection. All work is performed without affecting active monitoring or detection.
It usually takes 4–6 weeks for the Core level of SOC assessments, depending on SOC size, scope, and maturity. Timelines can be adjusted for complex or multi-entity environments.
You will receive maturity and capability scores, a gap analysis for each domain, detection coverage mapping, and a 1- or 3-year roadmap with prioritized recommendations.
A SOC assessment measures maturity and provides practical guidance for improvement. An audit focuses on compliance with specific standards or regulations. Assessments are broader, more operational, and result in actionable change.
SOC managers, CISOs, MSSPs, national and industry SOCs, CERTs, and companies aiming to benchmark or strengthen their cyber defense operations.
The recommended timeframe is once a year. Regular assessments help track progress, optimize investments, and align SOC operations with evolving threats and business priorities.
Yes, for the Advanced level of SOC assessments. Group-IB reviews detection rules and use cases to identify coverage gaps and help align detections with relevant adversary TTPs.
It reveals underused tools, overlapping technologies, and skill gaps, allowing your organization to optimize resources and focus spending where it delivers the most protection.
You will receive a detailed roadmap with actionable next steps. Group-IB can also support implementation through SOC Development, Threat Intelligence Program Development, or training courses such as Building the Ultimate SOC.