Group-IB, an international company that specializes in preventing cyberattacks, which has recently opened Global HQ in Singapore, has discovered a new wave of massive fraudulent campaigns involving the use of dozens of well-known brands including Alitalia, Carrefour, Conad, etc. Italian and Spanish-speaking customers have become the primary targets of the group of scammers, dubbed Lotsy by Group-IB. The «Lotsy» scheme involves the illegal use of famous brands and quizzes to deceive people into visiting toxic third-party websites. Group-IB’s Brand Protection team has detected a total of 114 related fake web-resources involved in the scheme.
This case started with an alert from Alitalia. The Lotsy fraudsters attempted to abuse the brand of the international airline company, which protected its customers with the help of Group-IB’s Brand Protection experts, who quickly blocked the fake resources illegally using Alitalia brand. The links to fake Alitalia websites were provided to Group-IB by DeepCyber. After researching and blocking these resources, Group-IB’s team discovered several other fake websites illegally using famous international brands, including Conad (Italian retail store), Target (International retail stores), Carrefour (international chain of hypermarkets) and many others. These websites are aimed at taking users to several suspicious third party resources. The brands have nothing to do with the fraudulent scheme, of course.
How does this scheme work?
Lotsy leverages the so-called freebie strategy, and are likely to be behind the fraudulent scheme Group-IB described in 2017, offering users free gifts such as first class tickets, coupons, free cosmetics and even cash in order to trick them into visiting fake websites, which are actively promoted via messengers and social media by real people who fell victim to the fraudulent scheme. Most of these websites as well as the social media posts and WhatsApp messages are in Italian or Spanish.
First, you see a link shared by one of your friends in a Facebook post or via a WhatsApp message promising, for example, a free ticket giveaway. Next, once you click on the link, you end up on a fake website, which looks very similar to the legitimate sites of the companies mentioned above: the fraudsters use URLs that mimic the legitimate websites and copy the branding of well-known companies to avoid suspicion. To get the «reward» you are prompted to answer a few simple questions. This is a hypnosis technique: you are expected to give positive responses to simple questions, which helps the fraudsters to establish trust. When you answer all the questions the website prompts you to like the page and share the post with a number of Facebook friends or WhatsApp contacts to get the reward. At this point, you also see a number of fake Facebook comments on the website praising the companies for the gifts the commentators supposedly received. When you hit the share button and unknowingly involve your friends in the fraudulent scheme by sharing the link with them, instead of the promised reward, you are redirected to third-party fraudulent resources that offer you to visit a hookup website, install an extension for your browser and subscribe for paid services. In the worst-case scenario, you may end up on a malicious website. The type of website you are redirected to depends on the user’s country, device, or language settings.
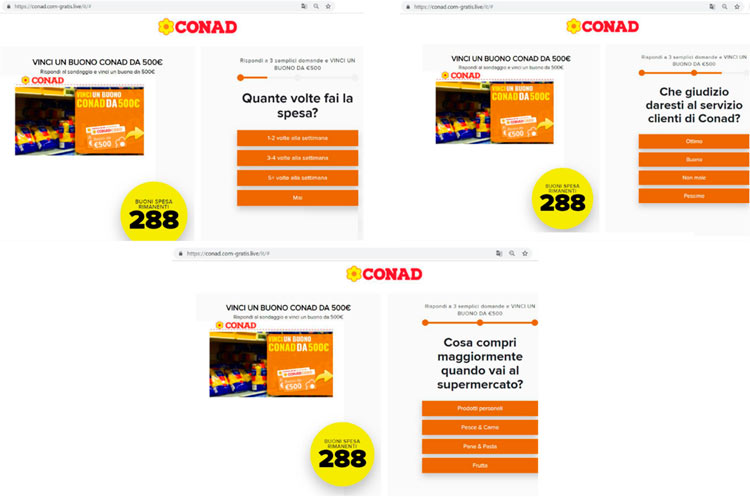
Fig. 1 Fake page (https://conad.corn-gratis[.]live/it/#) disguised as a legitimate Conad website. And the following questions are asked: “How often do you go to the supermarket?”, “How would you rate Conad’s customer service?”, “What do you buy when you go to the supermarket?”
Fig. 2 When you answer the questions you are asked to share the website with 20 of your contacts in WhatsApp to get the reward
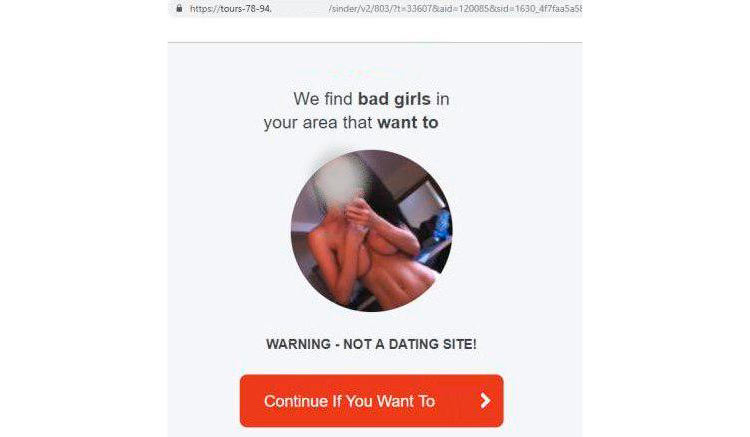
Fig. 3 Once you hit the share button you can be redirected to a hookup website or other third-party resources
Group-IB Threat Intelligence system has identified at least 114 domains used in this scheme, 28 of which were active at the time of preparing this news story. Other domains may be activated at any time. Group-IB experts have discovered that all the fraudulent resources are related, based on their registration date, similarities in their domain names (use of «corn», «voucher», «regalo» words in most of the domains), domain extensions (.win, .top, .money, .gratis etc.) and the content almost all of them use nearly identical templates for short surveys. Most of the websites were registered between late 2018 and early 2019.
We believe that a single group is likely behind this fraudulent scheme, dubbed Lotsy by Group-IB experts, because of the instruments they use: fake quizzes and lotteries. Since the start of their operations in summer 2017, the design and general appearance of their fake websites remain very similar. For the past 2 years of Lotsy’s activity, more than 100 brands were affected.

Head of Group-IB’s Brand Protection team in Singapore
Lotsy is trying to be very cautious: to avoid detection they never use brand names in second-level domains. Some of the domains discovered by Group-IB’s Brand Protection team have been used for redirects only and do not have any accessible content. The fraudsters also hide their identities by using different hosting providers.
Why is this dangerous?
In the cybersecurity framework, a fake fraudulent website is a threat to customers and brands.
This is a typical scam aimed at tricking users into visiting third-party websites ranging from the resources, that entice a victim to sign up for expensive paid subscriptions and install unwanted programs, to malicious websites. For companies the consequences of this kind of fraud can be both reputational damage and financial harm. Unhappy customers act fast: even after one negative experience many users are likely to stop buying from a brand whose name has been involved in a scam. This is why companies need to detect and quickly block resources that illegally use their brands online. People tend to have more trust in links that are shared by their friends, as in this case. And fake websites that use such schemes for promotion reach wider audiences faster than legitimate resources that use traditional methods to drive traffic.

Head of Group-IB’s Brand Protection team in Singapore
How not to fall victim?
For users:
- Do not click on suspicious URLs, even if they are coming from your friends.
- Always check what the official website looks like. Pay attention to the domain name and the web interface of the resource.
- Always avoid suspicious resources that request your personal and payment data.
For brands:
- Purchase all similar domain names so that cyber criminals could not use your trademark in a fake website’s domain name. For example, if your address is internet-shop.com, cybercriminals can register the following domain names: internet.shop.com or internet shop.com and deceive people using your brand name.
- Monitor references to your brand in the domain names and phishing websites databases regularly. Companies that provide brand protection and anti-fraud services have access to these databases.
- Discover and quickly eliminate the networks of fraudulent websites that use your brand.