The hacker group ATMZOW and its JavaScript-sniffer became known in 2020, thanks to the Malwarebytes researchers, when the group installed a JS sniffer on a website that was collecting donations for victims of the Australia bushfires.
However, based on a specific obfuscation technique used by the group, we can track its activities back to 2015 as “Magento Guruincsite malware”. Moreover, one of the first domain names, used by the group, was created in 2016.
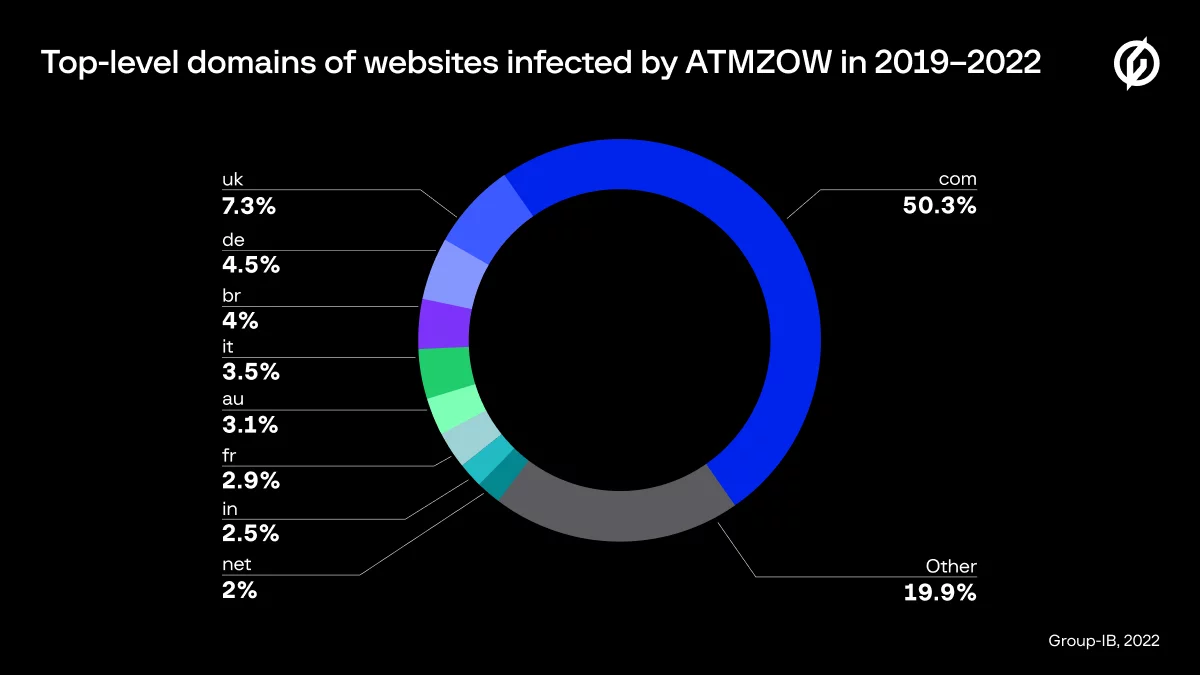
According to Group-IB Threat Intelligence data, ATMZOW has successfully infected at least 483 websites belonging to the domain zones of Italy, Germany, France, UK, Australia, India, Brazil etc. since the beginning of 2019.
Group-IB specialists collected information about ATMZOW’s recent activity and found ties with a phishing campaign targeting clients of a US bank based on the same JS obfuscation technique and a connection between the domain names used for the JS sniffer and the phishing domains on account of the same email address used. Further analysis showed that the same phishing kit was used during the activity of Prometheus TDS, when an unknown adversary used phishing pages as a final redirect when distributing Hancitor malware. With moderate confidence, we can conclude that both the ATMZOW JS sniffer campaign and related phishing attacks could have been conducted by the Hancitor group.
ATMZOW: recent activity
In May 2022 Group-IB specialists discovered that ATMZOW started using Google Tag Manager (GTM) to deliver malicious payloads. Google Tag Manager is a tag management system that allows website owners to quickly and easily update various code snippets known as tags on websites and mobile apps.
The hackers created a Google Tag Manager link with ID GTM-WNV8QFR and started using legitimate GTM code to inject JS sniffers. Injection starts with a common GTM snippet.

Figure 1: Google Tag Manager snippet with the attacker’s ID
This GTM script contains a specific tag (“vtp_html“) with the next stage injector.

Figure 2: Google Tag Manager script with the attacker’s injector
Executing the script loaded by Google Tag Manager appends the injector to the DOM of the infected website.

Figure 3: The attacker’s injector
The injector checks if the current user’s address in the address bar contains a “checkout” substring. If it does, the injector loads the final payload from https://designestylelab[.]com/css/. The script loaded from https://designestylelab[.]com/css/ is a sample of the ATMZOW JS sniffer, but it contains an additional layer of obfuscation.

Figure 4: ATMZOW sample with additional obfuscation
If we remove the junk symbols from the long string in this sample, we obtain a Base64-encoded string. After decoding, we obtain an ATMZOW sample with its common obfuscation.

Figure 5: ATMZOW sample
After decrypting the strings used in this sample, we obtain a clean script of the ATMZOW JS sniffer.

Figure 6: Use of a fake payment form in a sample of the ATMZOW JS sniffer

Figure 7: Exfiltration address https://gvenlayer[.]com/track/ in a sample of the ATMZOW JS sniffer
Phishing campaign
In January 2022 Group-IB specialists detected several phishing pages targeting clients of a US-based bank. The pages used IDN domain names. A noteworthy fact about the pages is that they have a JavaScript script, which was presumably obfuscated by the same tool as used by ATMZOW for the group’s samples of JS sniffers.

Figure 8: Screenshot of a JS script from the page https://xn--keyvigatrs-key-7oc4531jsva[.]com/ktt/cmd/logon
- xn--kys-nvigatorky-zp8g5mna[.]com
- xn--kynavigatos-ky-pwc6541jna[.]com
- navlgator-kcy[.]com
- xn--kyavigator-ky-jjc7914ima[.]com
- xn--ky-vigatorkey-kjc9383i4ka[.]com
- xn--key-vigatrs-key-wuc9688j1wa[.]com
- xn--keyvigatrs-key-7oc4531jsva[.]com
Connection between the JS-sniffer and the phishing campaign
When we detected the same obfuscation technique on a phishing website for the first time, we hypothesized that the method was not unique to ATMZOW, but that other hackers could be using the same obfuscator. However, further analysis of the group’s recent activity showed additional evidence that attacks involving the JS sniffer and the phishing campaign were conducted by the same group.
When ATMZOW started using Google Tag Manager as the initial stage of their infections, they used a website with the domain name designestylelab[.]com as the storage location for their payloads. With a patented technology named Group-IB Graph, we discovered that this domain was created using the email address [email protected]. The same email address was used to create two more IDN domains for phishing pages targeting clients of the same bank as the pages with the ATMZOW-like obfuscation, which we first detected in January 2022:
- kẹy-ņạvigatorkey.com (xn--ky-vigatorkey-kjc9383i4ka[.]com)
- key-ņạvigatọrskey.com (xn--key-vigatrskey-8oc4531jsva[.]com)

Figure 9: Graph shows a connection between JS sniffer storage and phishing domains
In addition, one of these domains created with the email address [email protected] (xn--ky-vigatorkey-kjc9383i4ka[.]com) was tagged as a phishing page with ATMZOW-like obfuscated JS script. It was detected on January 27, 2022.
Based on the same JS obfuscation technique and the connection between the domain names used for the JS sniffer and the phishing domains (the same email address), we can conclude with a high degree of reliability that both campaigns were conducted by the same threat group.
Connection between the phishing campaign and Hancitor malware
While analyzing Prometheus TDS, Group-IB Threat Intelligence specialists detected several cases when phishing pages targeting clients of the same bank were used as a final redirect after downloading the malicious payload distributed by Prometheus TDS. In all cases, the malicious payload was Microsoft Office documents with a macro that dropped Hancitor malware.
For example, a common method of distribution via Prometheus TDS was the use of Google Docs with a link to the compromised website with Prometheus.Backdoor installed. In this case, the Prometheus.Backdoor link was hXXp://www.swingsidebilbao[.]com/wp-content/plugins/contact-form-7/includes/block-editor/carl.php. If a user clicked on the link, they would receive a malicious Office document “0210_4367220121562.doc” (SHA1: be3effcb9069ac6d66256c8246fde33e55980403) and then would be redirected to the phishing website hXXps://xn--keynvigatorkey-yp8g[.]com/ktt/cmd/logon0210_4367220121562.doc. If the user opened the malicious document and enabled macros then, the document would drop the Hancitor DLL (SHA1: 17693bca881ec9bc9851fcb022a664704c048b9d).
As we can see, in this case the hackers used IDN domains again to spoof a real banking website. Moreover, if we compare unique URLs generated while analyzing phishing pages from both campaigns, it is clear that both phishing pages were created using the same kit, with slight modifications.
| Unique URLs of phishing page with ATMZOW obfuscation | Unique URLs from Hancitor-related phishing page |
|---|---|
| https://xn--keyvigatrs-key-7oc4531jsva[.]com/ktt/cmd/logon/ | https://xn--keynvigatorkey-yp8g[.]com/ktt/cmd/logon0210_4367220121562.doc |
| https://xn--keyvigatrs-key-7oc4531jsva[.]com/ktt/cmd/logon | https://xn--keynvigatorkey-yp8g[.]com/ktt/cmd/logon |
| https://xn--keyvigatrs-key-7oc4531jsva[.]com/a3dcb4d229de6fde0db5686dee47145d_wait.gif | https://xn--keynvigatorkey-yp8g[.]com/wait.gif |
| https://xn--keyvigatrs-key-7oc4531jsva[.]com/a3dcb4d229de6fde0db5686dee47145d_security.php | https://xn--keynvigatorkey-yp8g[.]com/security.php |
Based on the information we collected, we can therefore conclude with a high degree of reliability that both clusters of phishing pages are part of a long-running phishing campaign conducted by one cybercriminal group.
IoCs
Phishing websites with ATMZOW-like obfuscation
- xn--kys-nvigatorky-zp8g5mna.com
- xn--kynavigatos-ky-pwc6541jna.com
- navlgator-kcy.com
- xn--kyavigator-ky-jjc7914ima.com
- xn--ky-vigatorkey-kjc9383i4ka.com
- xn--key-vigatrs-key-wuc9688j1wa.com
- xn--keyvigatrs-key-7oc4531jsva.com
Phishing websites detected in the Hancitor campaign with Prometheus TDS
- xn--avigatorkey-56b.com
- xn--nvigators-key-if2g.com
- xn--keynvigatorkey-yp8g.com
- xn--xprss53-s8ad.com
ATMZOW GTM ID
- GTM-WNV8QFR
ATMZOW JS sniffer storage
- designestylelab.com
ATMZOW JS sniffer gates
- gvenlayer.com
- metahtmlhead.com
- winsiott.com
- congolo.pro
- vamberlo.com
- nmdatast.com
- seclib.org

































