What happens when the people who are meant to stop scams spreading on social media are being impersonated by the scammers themselves? Facebook has over 2.9 billion monthly active users, and accounts on this social network are an attractive target for cybercriminals looking to steal personal information. Group-IB Digital Risk Protection (DRP) experts have discovered a new and still ongoing phishing scheme aimed at Facebook users that sees threat actors attempt to steal account credentials and take over profiles. Throughout February and March 2023, Group-IB researchers identified more than 3,200 scam profiles that were either compromised or created by the cybercriminals who launched this campaign. The scam is conducted in more than 20 languages, although Group-IB experts found that the vast majority of the profiles impersonating Meta posted in English. Upon discovery of these phishing profiles, Group-IB’s Computer Emergency Response Team (CERT-GIB) shared information on the compromised and created accounts with Facebook in line with Group-IB’s responsible disclosure protocol.
With this phishing campaign, the scammers’ ultimate aim is to gain access to the Facebook accounts of public figures, celebrities, businesses, sports teams, as well as individual profiles, to steal sensitive information, and potentially use the same compromised credentials to gain access to other accounts held by the individual. The latter is possible given the all-too-common occurrence that a person uses the same combination of username and password for multiple services, and this poses serious risks for their accounts on financial services platforms.
The scammers are able to harvest Facebook account credentials by tricking the victims, who believe they are verifying their account with Meta’s technical team to prevent it from being blocked, into entering their data voluntarily on a phishing website or by sending their browser cookies (session hijacking attack). During their investigation, Group-IB experts noted that the scammers behind this scheme used various social engineering tactics to fool the victims into handing over their account credentials. Most notably, the scammers impersonate Meta, Facebook’s parent company, in their public posts and on any of their more than 220 phishing sites. They appropriate Meta and Facebook’s official logos on their social media profiles and phishing web pages to make them appear legitimate and trustworthy in the eyes of users. These fake profiles have nothing to do with Facebook, and they are frequently taken down quickly by the social network.
Key Findings
- Analysts at Group-IB uncovered more than 3,200 fake Facebook profiles/pages impersonating the Meta and Facebook technical support teams posting in 23 languages.
- Group-IB found over 1,200 fake profiles in March 2023 alone.
- The scam profiles are either created from scratch or they are already-compromised accounts that the scammers leverage in new phishing attempts.
- Group-IB researchers discovered more than 220 phishing sites mimicking official Meta and Facebook webpages. These webpages are created on cheap or free all-in-one web platforms and are used in both typical phishing and session hijacking attacks, the latter of which is less frequently seen in the wild.
- The core aim of the scammers is account takeover, completed once an individual enters their username/email and password on a phishing site or sends their browser cookies to the scammers, who can use this data in a session hijacking attack.
- The cybercriminals behind this campaign seek to take over the Facebook accounts of prominent individuals, celebrities, businesses, and sports teams in the hopes of increasing their reach.
- The scammers lure potential victims in with attention-grabbing posts that contain a signature indicating the post was “written” by Meta/Facebook support staff. They tag dozens of other pages in their posts, which also feature links to the phishing websites.
- Potential victims will see the scam posts either in their newsfeed, their notifications, or if they search for the name of an individual or company whose account has been tagged.
Aiming for the stars
After obtaining a user’s login credentials, the scammers can leverage this compromised account to harvest the credentials of other users. Group-IB experts observed that in some instances, the scammers would repurpose a compromised account into a phishing profile. In this scenario, the account is given a new name, containing a combination of keywords such as “account”, “retrieval” or “recovery”, and the scammers begin posting, signing off their publications with “Meta Business Services” or another similar body. This approach can be particularly effective as victims can be duped into thinking that the page is being managed by Meta employees. These pages publish a large amount of posts, making it highly likely that subscribers to the taken-over page will see the publications in their newsfeed. Another option for the attackers, which Group-IB experts have seen in other scam campaigns, is to hold the compromised account in exchange for a ransom. In the context of this campaign, the attackers could threaten to delete the account or post undesirable content unless a ransom is paid.
In this campaign, the scammers have set their sights on a broad range of individuals and business enterprises. Public figures such as politicians, celebrities, musicians, and influencers are among the primary targets, along with sports teams and public organizations. The real danger in this phishing campaign lies in its potential reach. The number of victims can increase exponentially because the followers of a particular page – those who subscribed before the account was taken over by the scammers – are converted into potential victims following account takeover. As a result, the aim of this blog is to raise awareness of the potential risks and economic losses that can be associated with phishing attacks, and to urge individuals and organizations to take action, by ensuring that their passwords are strong and unique and by enabling two-factor authentication to protect against schemes such as this one.
Furthermore, this blog serves as another example of the need for internet users to remain vigilant while browsing social media. Recently, Group-IB Digital Risk Protection experts outlined how scammers used 2,400 fake profiles on Facebook to impersonate some of the biggest companies in the Middle East and North Africa, advertising fake jobs to Arabic-speaking users with the aim of stealing their account credentials. Now, scammers have turned to impersonating Meta itself.
This phishing scheme was discovered by Group-IB analysts who leveraged the company’s proprietary Digital Risk Protection platform. This sector-leading, multi-purpose solution gives brands 360 degree protection against intellectual property violations and scams involving their name and likeness. All findings were detected with Digital Risk Protection’s AI-infused logo analysis and text recognition features, and the machine-learning algorithms contained in this technology allow this solution to automatically detect and extract keywords relevant to this scheme. Group-IB Digital Risk Protection gives brands all the tools necessary to take actions to mitigate these violations, and we will continue to monitor this and other scam campaigns that seek to appropriate the name and likeness of prominent brands, and raise awareness of any new techniques, tactics, and procedures leveraged by the scammers.
Quantity and quality
Group-IB Digital Risk Protection experts began tracking this phishing campaign in February 2023, and over the course of two months, discovered more than 3,200 accounts impersonating Meta technical support linked to this campaign. Of this total, more than 1,200 profiles started posting in March 2023, and 982 in February 2023.
In their attempts to quantify the number of profiles utilized in this phishing campaign, analysts noted that many of the pages were created or compromised and then swiftly deleted or restricted by Facebook due to the content they produced. Group-IB experts found traces of the campaign dating back to December 2020, suggesting that the scam scheme has been active for upwards of two years.
Group-IB experts found posts related to this campaign in a total of 23 languages. The vast majority (more than 90%) of the fake Meta technical support profiles published content in English, although this does not mean that the phishing campaign exclusively targets individuals for whom English is their native language. For example, posts in English regularly tagged celebrities and public figures in non-English speaking countries. The other most common languages used in this campaign were Mongolian (2.5% of scam profiles), Arabic (2.3%), Italian (0.8%), and Khmer (0.6%).
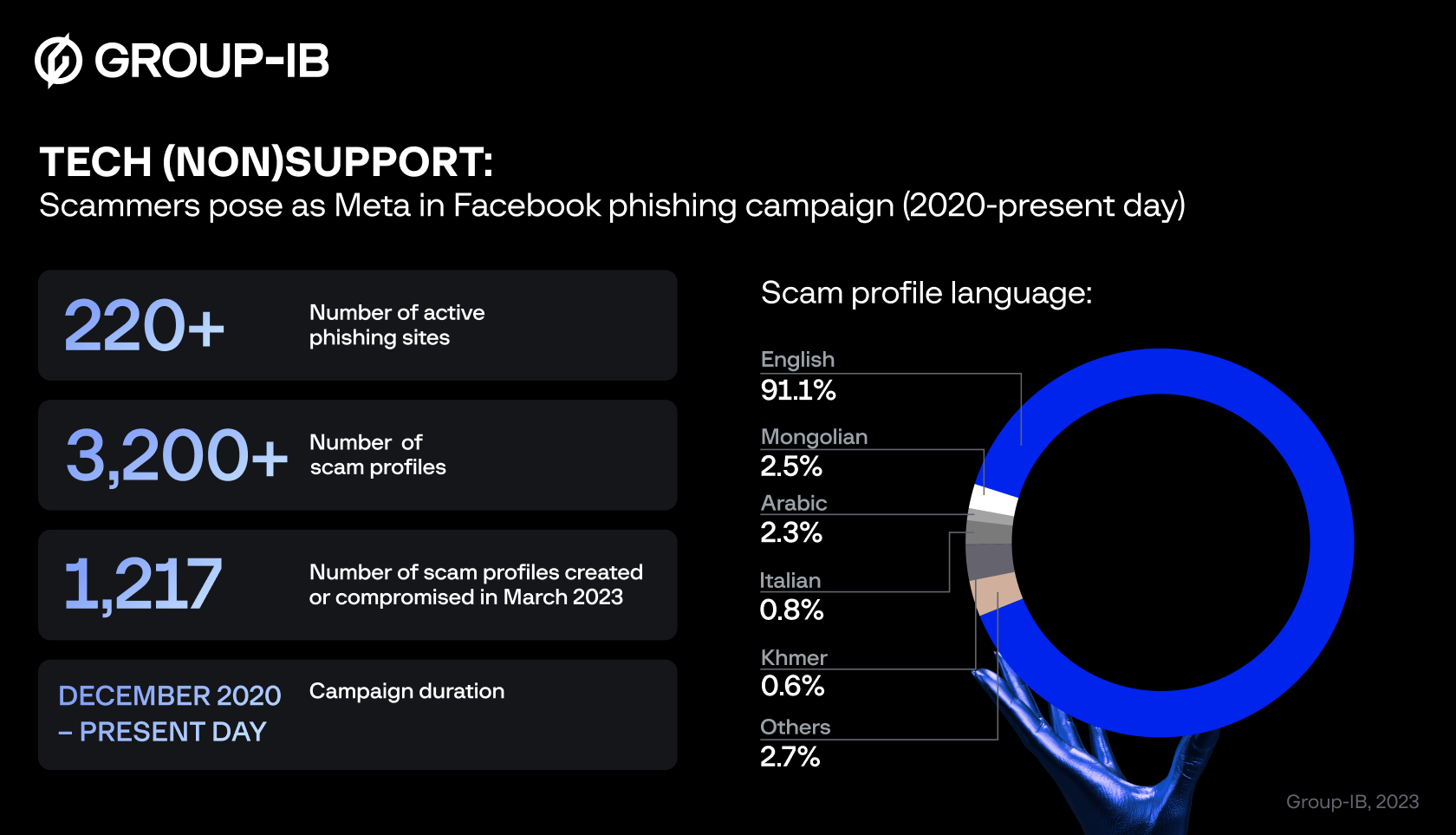
Figure 1: Statistical overview of fake Meta tech support scam.
Some of the profiles analyzed by Group-IB had only four posts on them, others had hundreds. However, each of the posts published tagged anywhere from 10 to 50 users, the majority of them public figures, celebrities, companies and organizations. This indicates that the scammers are targeting profiles that have a large following to increase potential reach in the event of account takeover, but it could also mean that individuals who search for information about a particular celebrity on Facebook could view these scam posts and potentially interact with them. Furthermore, it extends the potential financial gain that the cybercriminals behind this campaign can achieve, as the scammers can demand money from victims to retrieve their compromised account.
In addition, Group-IB researchers discovered more than 220 active phishing websites used by the scammers during this campaign. These web pages are used to trick the user into entering their Facebook login credential and password, оr session cookies. The cybercriminals used cheap or free web platforms to create their websites. These provide a low barrier of entry for bad actors looking to launch their own scheme, and is an increasingly common tactic seen in the vast majority of scam enterprises analyzed by Group-IB Digital Risk Protection experts. Additionally, these solutions obfuscate attribution attempts, as the pages created with these services do not have unique IP addresses or domains, and information about the creators of these pages is not available to the public.
The phishing run sheet
Let’s start with the profiles themselves. As outlined above, the scammers either use newly created profiles or repurpose accounts they have already compromised. They give these profiles names such as “Restriction Account Business Information”, and “Page Standard-Community Recovery” to lure users in and give the impression the posts are by Meta’s technical support team. By doing this, the scammers hope to trick greater numbers of users into clicking the links to the phishing websites contained in their posts. Additionally, the use of non-standard characters in some examples seen by Group-IB, such as “Account |nformat|on System”, is one way that the scammers try to avoid detection by Facebook’s anti-phishing algorithms.
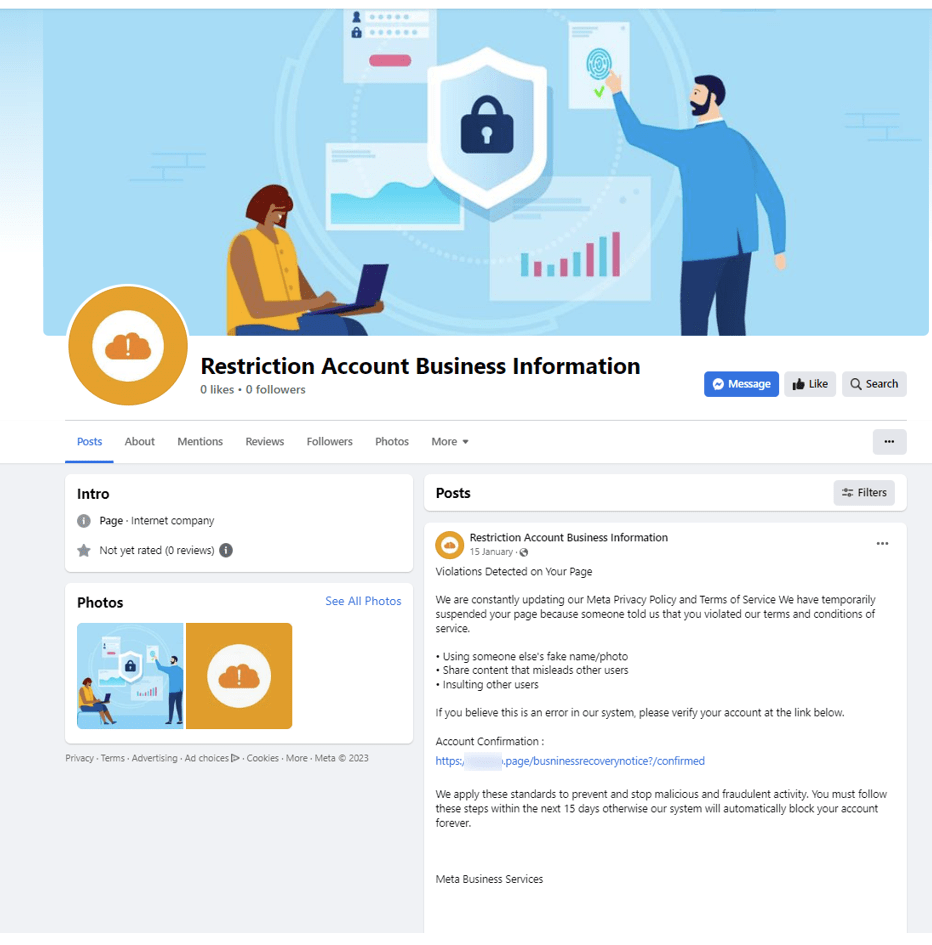
Figure 2: Screenshot of created page used by scammers during this phishing campaign.
The scammers begin to publish on the pages of accounts they have created or taken over. Some pages published a handful of posts a day, others posted hundreds. The posts slightly differ in their word choice, but they are all purportedly written by Meta or Facebook’s technical support team and inform of an alleged breach of Facebook violations committed on the page. In each post, the scammers tag roughly 50 other profiles belonging to other celebrities, public figures, or organizations. In addition, they contain a call to action urging “violators” to click on a link to verify their account. This link redirects users to a phishing website created by the scammers.
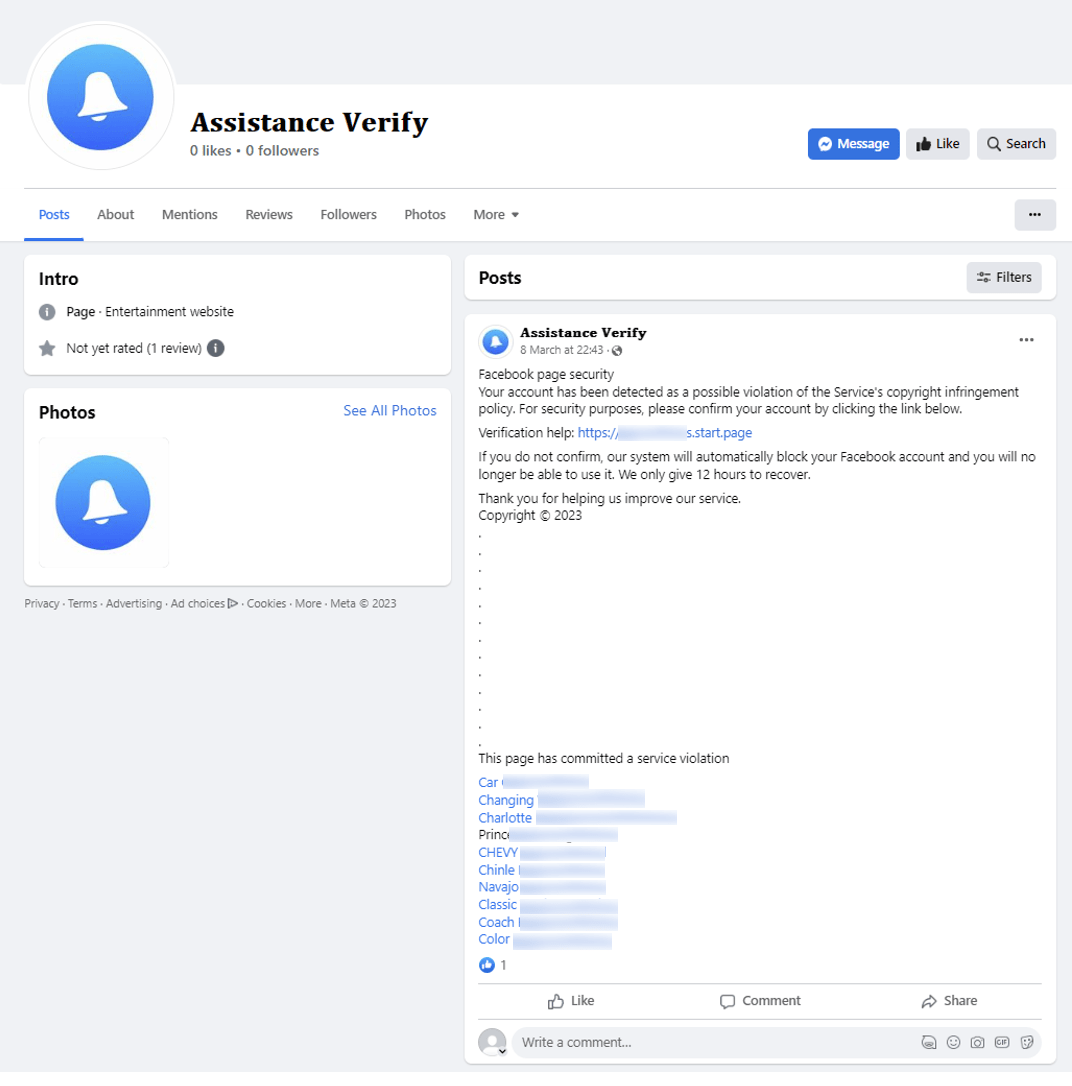
Figure 3: An example of a Facebook post tagging multiple users that contains a link to a phishing site.
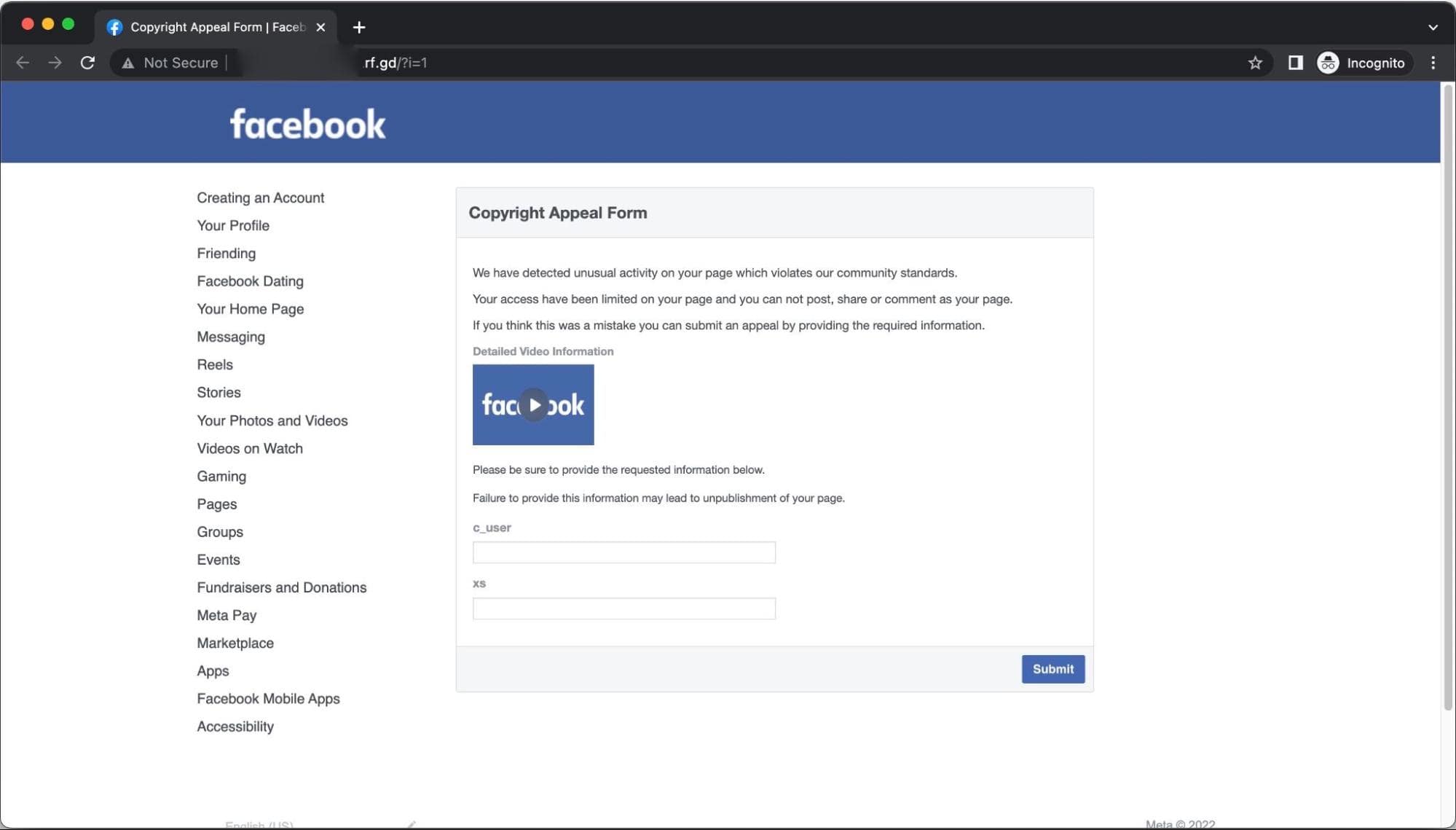
The victim, fooled by the false impression of authority created by the scammers, clicks on the phishing link in a post they believe to be written by Meta’s technical support team. Immediately after clicking on the link in the post, the victim is then redirected to a fake web page that contains the branding either of Facebook or Meta. The phishing web page contains text falsely informing the victim that their Facebook profile will be disabled after it was found to be engaged in suspicious activity, i.e. copyright infringement. At this stage, the scammers appear to give the victims the option to appeal the forthcoming suspension by clicking on the “Continue” button, but all this does is help the scammers get closer to their eventual goal of account takeover.
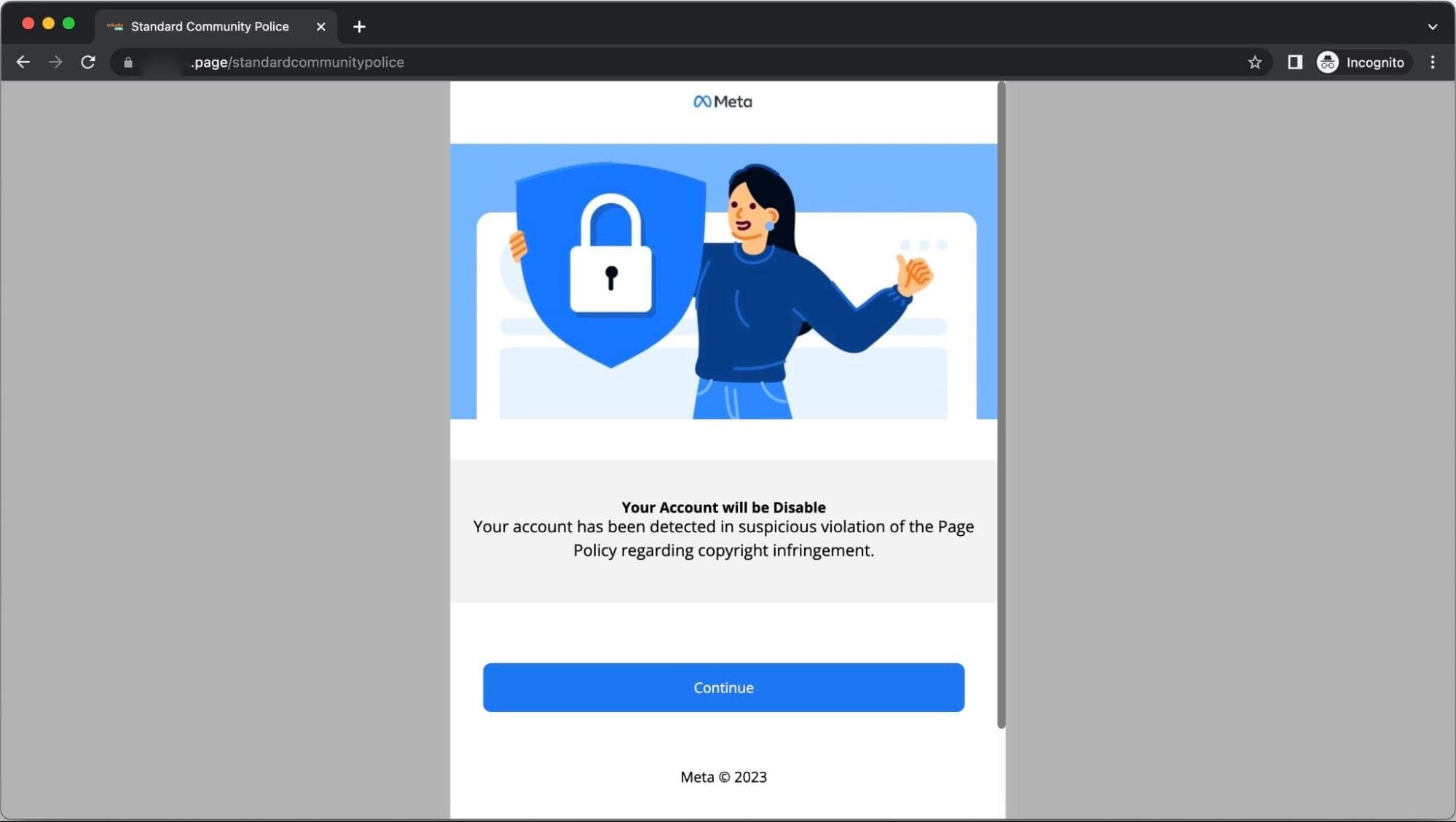
Figure 4: Phishing page containing Meta’s branding and likeness, which purports to inform the victim that they have violated Facebook’s copyright policy.
After clicking on the “Continue” button, victims will be redirected to one of two types of pages. The first type is a phishing web page that contains Meta or Facebook’s name and likeness. This webpage features a message warning the user that their Facebook account will be locked. Users are prompted to verify their account, by entering their login credential and password in the data entry form, to prevent it from being blocked.

Figure 5: Phishing page where victims are asked to enter their account credentials.
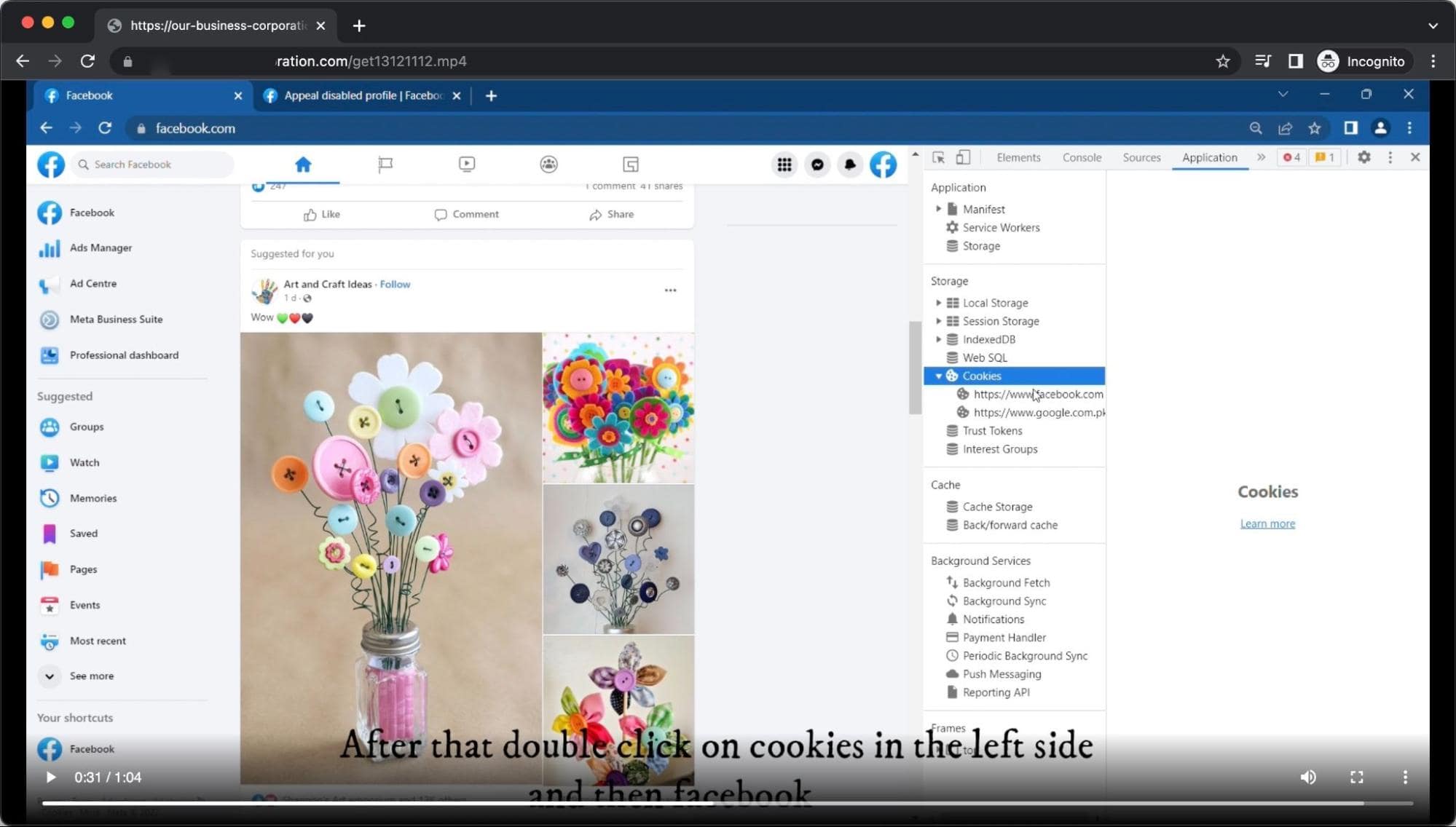
The second type of phishing site instructs the user to share their c-user and xs cookie data with the scammers in order to appeal against the fake copyright violation and retrieve their account. The page also features a video that instructs the user how to access their cookie data and enter it on the page.
The cookies that attackers claim to require from the user to process the so-called copyright appeal contain information pertaining to:
- Facebook User ID
- Session number
- Session secret
- Secure flag
By providing their cookie details to the scammers, users open themselves up to a session hijacking attack that can result in account takeover. Session hijacking, also known as cookie hijacking, is a type of web attack that sees an attacker take over a user’s session on a website or web application without the user’s knowledge or consent. Each session that is created when a user visits a website or web application is assigned a unique ID. This ID is stored as a cookie in the user’s web browser, and is used to authenticate subsequent requests to the server.
Once the attacker has the session ID, they can impersonate the user and make requests to the server as if they were the user. This also gives them access to sensitive data and the right to modify it, and also execute unauthorized transactions. This can result in financial loss, identity theft, or data breach. In this particular scam campaign, the scammers can use the accounts compromised via session hijacking to make a wave of phishing posts on the user’s profile, flooding the feed of the user’s friends, contacts, or if the account belongs to a public figure, thousands or millions of followers.
Conclusion
The world continues to be gripped by a scam epidemic, and social media is playing an ever-increasing role in the growing proliferation of scams. Social networks offer would-be threat actors a low-cost way of launching a scam campaign, and the growing number of free or cheap all-in-one hosting solutions make it easier than ever for a scammer to create a phishing website. In previous campaigns, Group-IB experts have documented how scammers turned their hand to impersonating some of the world’s largest companies, whether they be logistics firms or manpower agencies. These scams are frequently spread on Facebook, but this latest scheme underlines how scammers can leverage the branding and likeness of Meta, Facebook’s parent company, to outwit unsuspecting users. Credential theft can have a significant impact, both for an individual and potentially their employer, in the case that the login credential and password is the same for other accounts.
Amid the continued growth in scam profiles, pages, and campaigns, companies looking to protect their brand cannot rely solely on the manual discovery of violations. This is where Group-IB’s Digital Risk Protection comes into play. This market-leading solution can continuously and automatically monitor millions of online resources, including images, redirect chains, traffic sources, and HTML files, and send violations for takedown in order to keep your brand safe.
Recommendations for users
Strong digital hygiene practices and user vigilance both go a long way to preventing phishing attacks. We encourage users to be extra careful when accessing social networking sites, as scammers can use these platforms to spread their malicious content. Taking an extra handful of seconds to double check the URL or page name could make all the difference.
- Enable two-factor authentication (2FA) for social networks accounts to provide an extra layer of security that can prevent such kinds of attacks
- Use official links that are published by the respective entity
- Double check that you enter URLs correctly, to reduce exposure to fake sites created with domain names containing spelling errors (a process known as typosquatting)
- Ensure that web pages requesting sensitive information use a secure connection.
- Be cautious of subdomain phishing (ex: mybank.xyz.com)
Direct hit on phishing and scams
Try Digital Risk Protection to disarm scammers and protect your brand