Introduction
Every day, billions of people rely on postal and courier services to deliver everything from handwritten letters to high value online orders. These services form the backbone of the global marketplace, especially in the age of e-commerce.
According to the 2024 Universal Postal Union’s State of the Postal Sector report , postal services now serve a population of 7.3 billion people, and without them, a country’s GDP could drop by a median of 7%.
And according to Statista, about 161 billion parcels were shipped worldwide in 2022 alone. Some of the top countries driving this volume include:
- China, which handled roughly 110 billion parcels in 2022, by far the largest share of global parcel traffic.
- United States, which shipped about 21 billion parcels in the same year.
- Japan, with around 9 billion parcels in 2022.
Figure 1. Statista number of parcels shipped worldwide in 2022.
This huge reliance on courier services has basically made them a modern day essential service, and with that, come the scams.
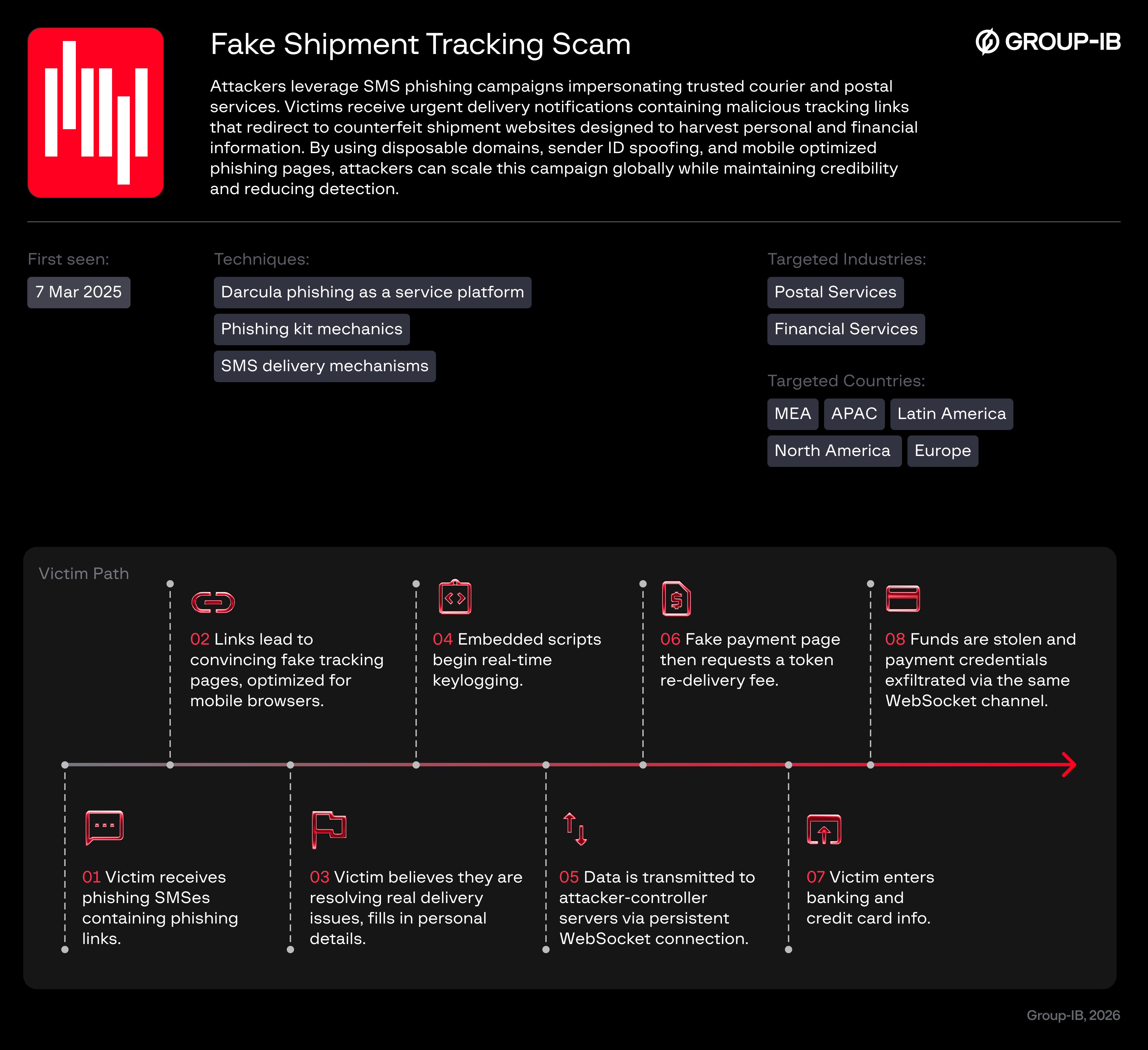
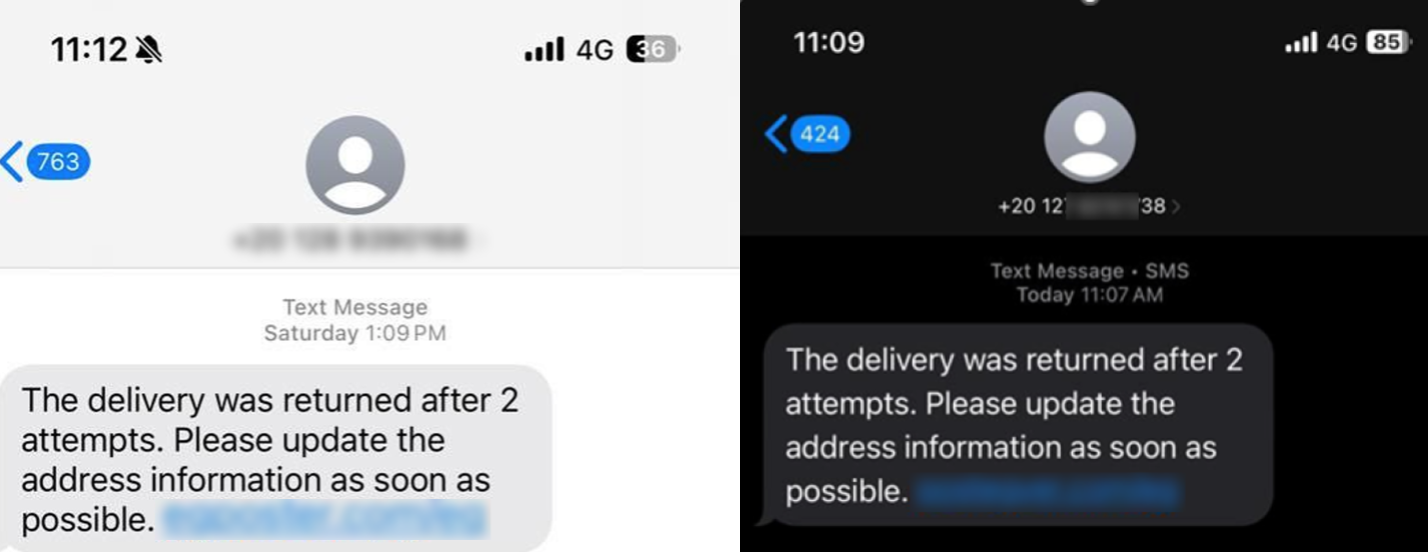
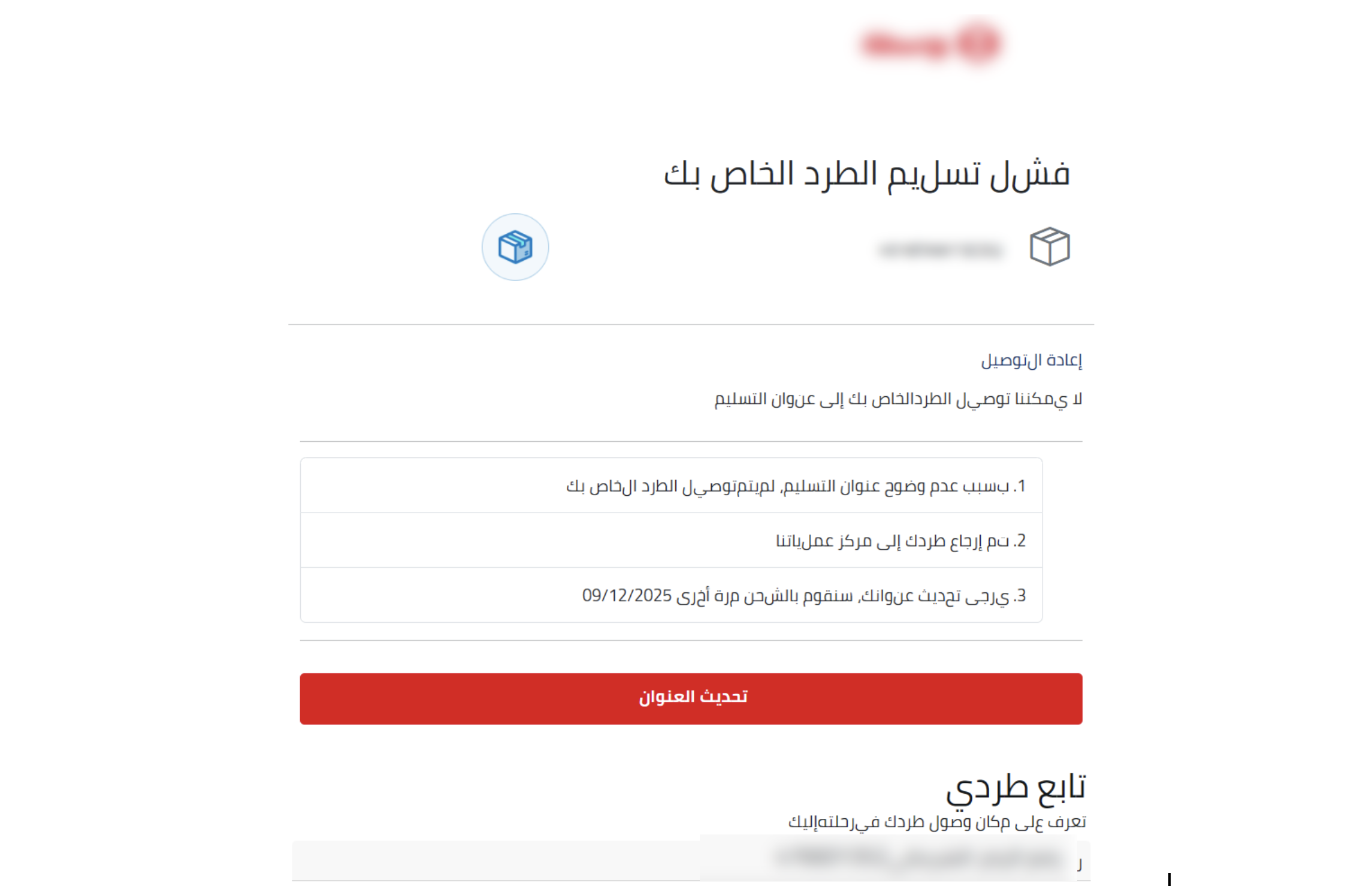
One of the most common and fastest spreading schemes is the “fake shipment tracking” scam. It usually begins with an anonymous text message claiming that “delivery has failed” due to various reasons and the victim’s package has been “returned after a number of delivery attempts”. The phishing messages will urge victims to “update their address information as soon as possible”, and make due payments such as “handling fees”, “taxes”, or “tariffs” before the package can be rerouted and released back to the victim. These messages look urgent, official, and time-sensitive, which is exactly what the scammers want.
Behind the link is no delivery update at all, only a phishing page designed to steal personal information, payment details, or even access to bank accounts.
Key Discoveries
- The fake shipment tracking scam leverages global reliance on e-commerce and postal services, exploiting delivery anxiety at scale.
- SMS delivery relies on anonymous local-looking numbers and Sender ID spoofing, allowing malicious messages to merge into legitimate message threads.
- Infrastructure analysis identified recurring IP addresses, domain registrars, and hosting overlaps indicating coordinated operations.
- HTML analysis revealed embedded scripts, WebSocket connections, real-time keylogging, UUID session tracking, and direct credential exfiltration.
- Stolen data includes personal information, banking credentials, card numbers, CVV codes, and OTPs transmitted via persistent WebSocket channels.
- The campaign expanded beyond postal themes to include online shops, transportation apps, bill payments, fines, subscriptions, and telecom services.
Who may find this blog interesting:
- Cybersecurity analysts and corporate security teams
- Threat intelligence specialists
- Cyber investigators
- Computer Emergency Response Teams (CERT)
- Law enforcement investigators
- Cyber police forces
Group-IB Threat Intelligence Portal
Group-IB customers can access our Threat Intelligence portal for more information about the phishing activity detailed in this blog and Darcula Pushing Kit, which is presumed to be potentially involved in this campaign and associated with PhaaS activity.
Scam Scheme
Who Is Affected By This Scheme?
The following graph shows the activity of this scheme from the beginning of 2024 when it was first tracked for this research. 2025 saw an explosive growth of fake shipment tracking scams with the spikes likely coinciding with the holiday seasons.
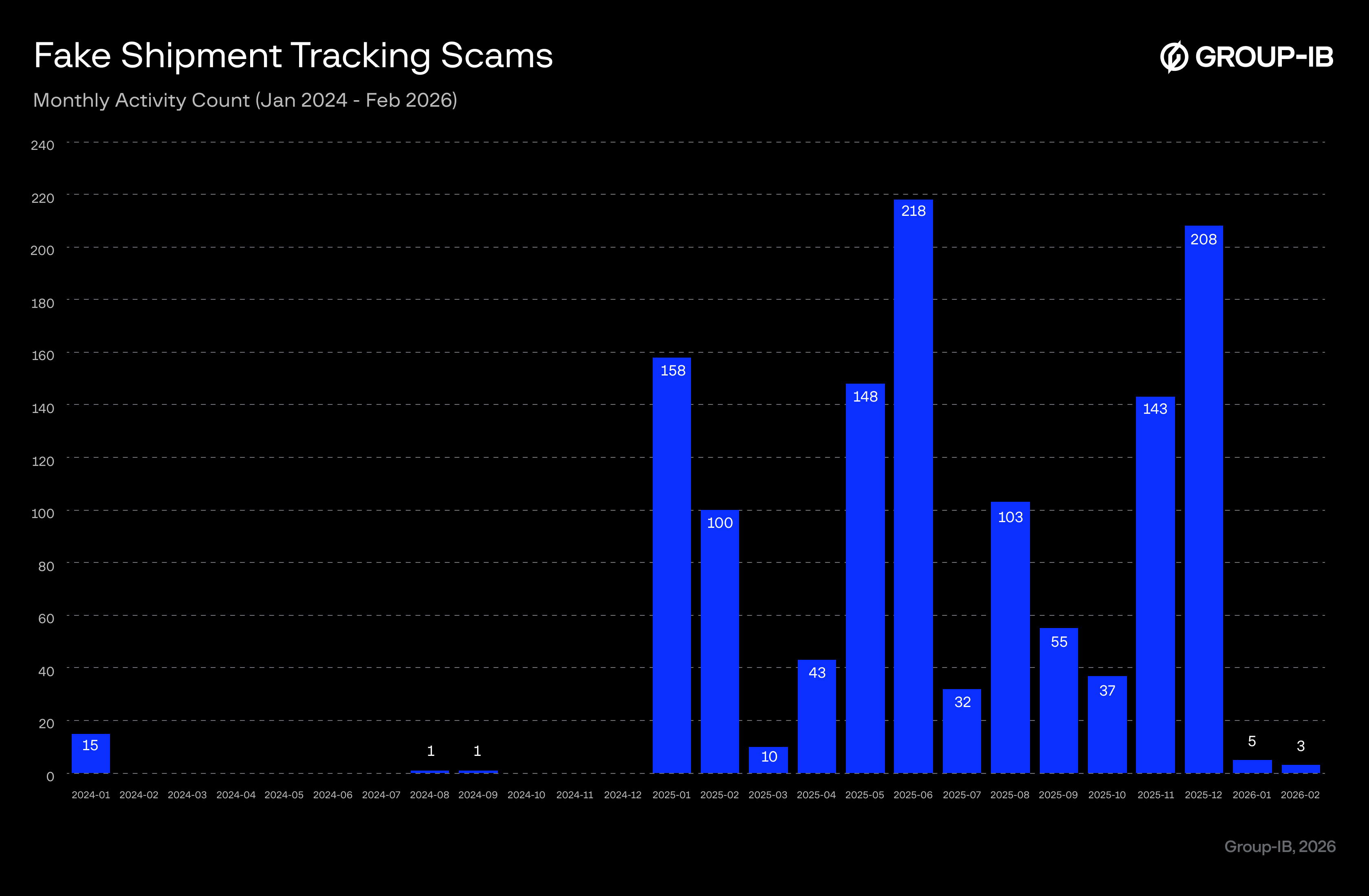
Figure 2. Fake shipment tracking scams grew substantially in 2025.
Targeted Industries
The fake shipment tracking scam primarily exploits the widespread reliance on parcel delivery services, making it one of the most prevalent phishing schemes observed by Group-IB researchers. As online shopping and logistics services are deeply embedded in everyday activities, a broad segment of the population is exposed to this threat. However, analysis indicates that certain sectors are disproportionately targeted, with postal and delivery services representing the most frequently abused category, followed by financial services, telecommunications, mobility services, and e-commerce platforms in the MEA region.
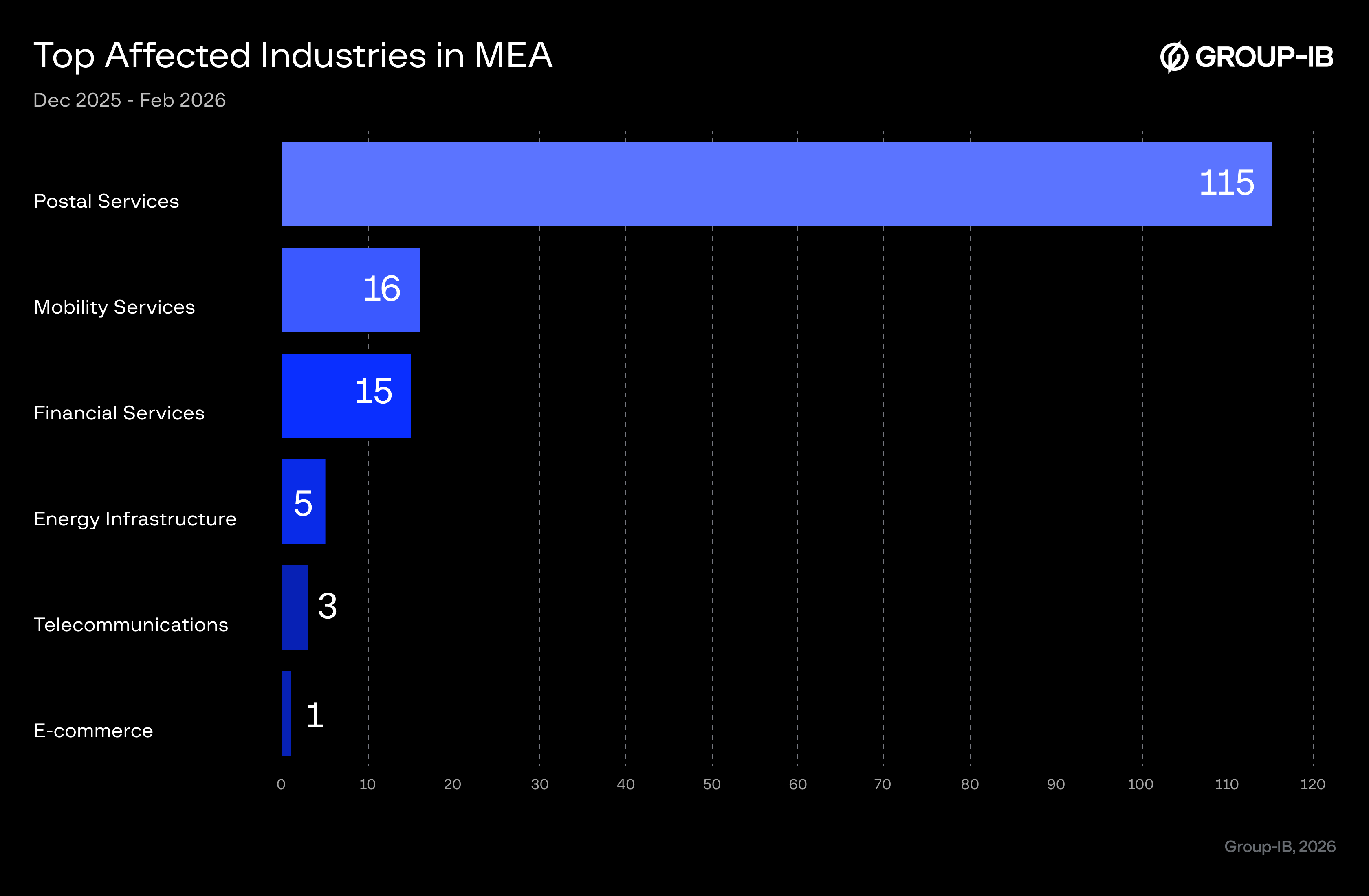
Figure 3. Most affected industries in MEA.
Targeted Countries
This scheme is prevalent and targets multiple countries around the world. The following statistics shows activity in the MEA region observed just in the last two months between 1 December 2025 and 1 February 2026 within the course of this research.
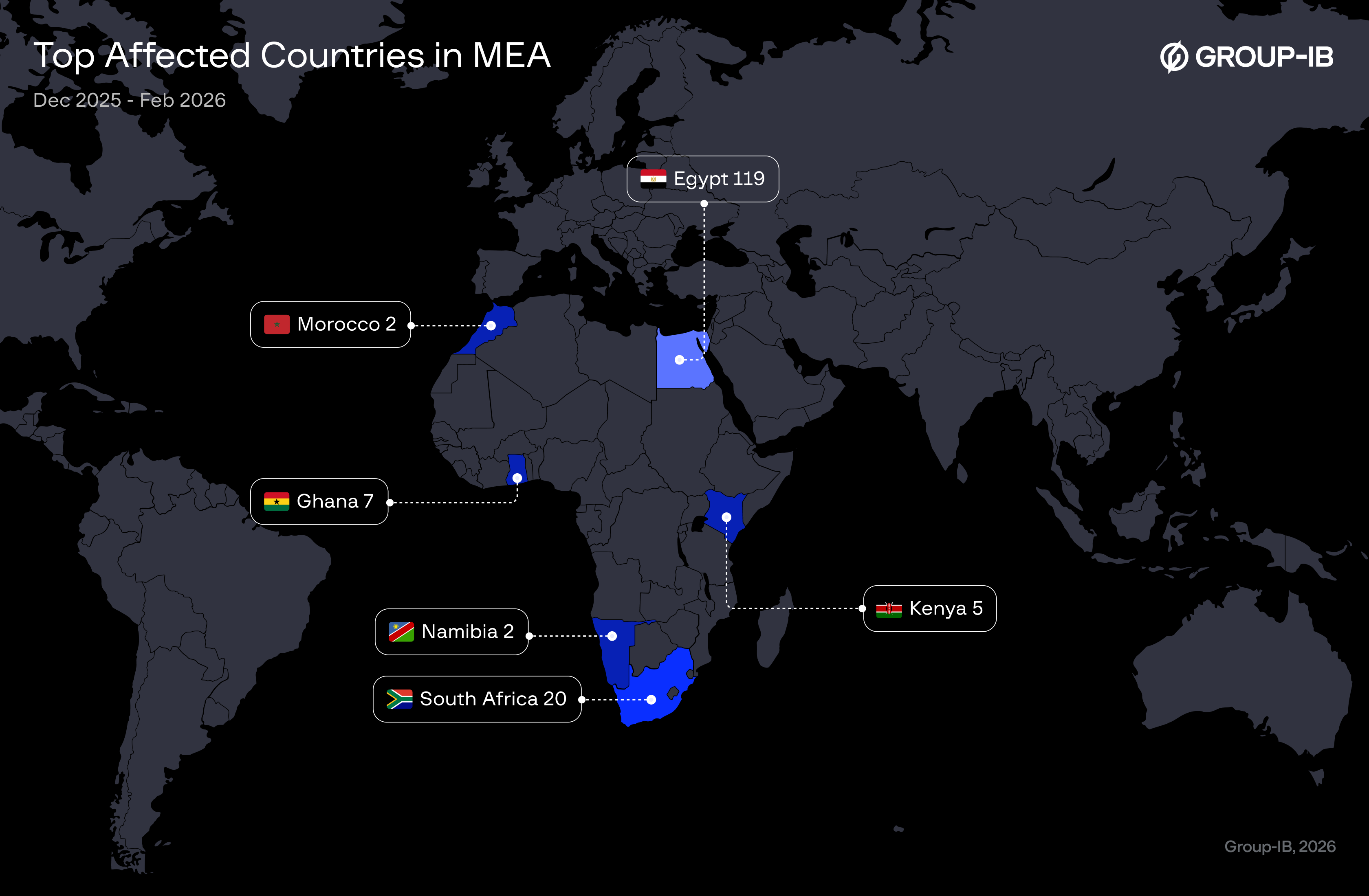
Figure 4. Top affected countries in MEA
How Does This Phishing Scheme Work?
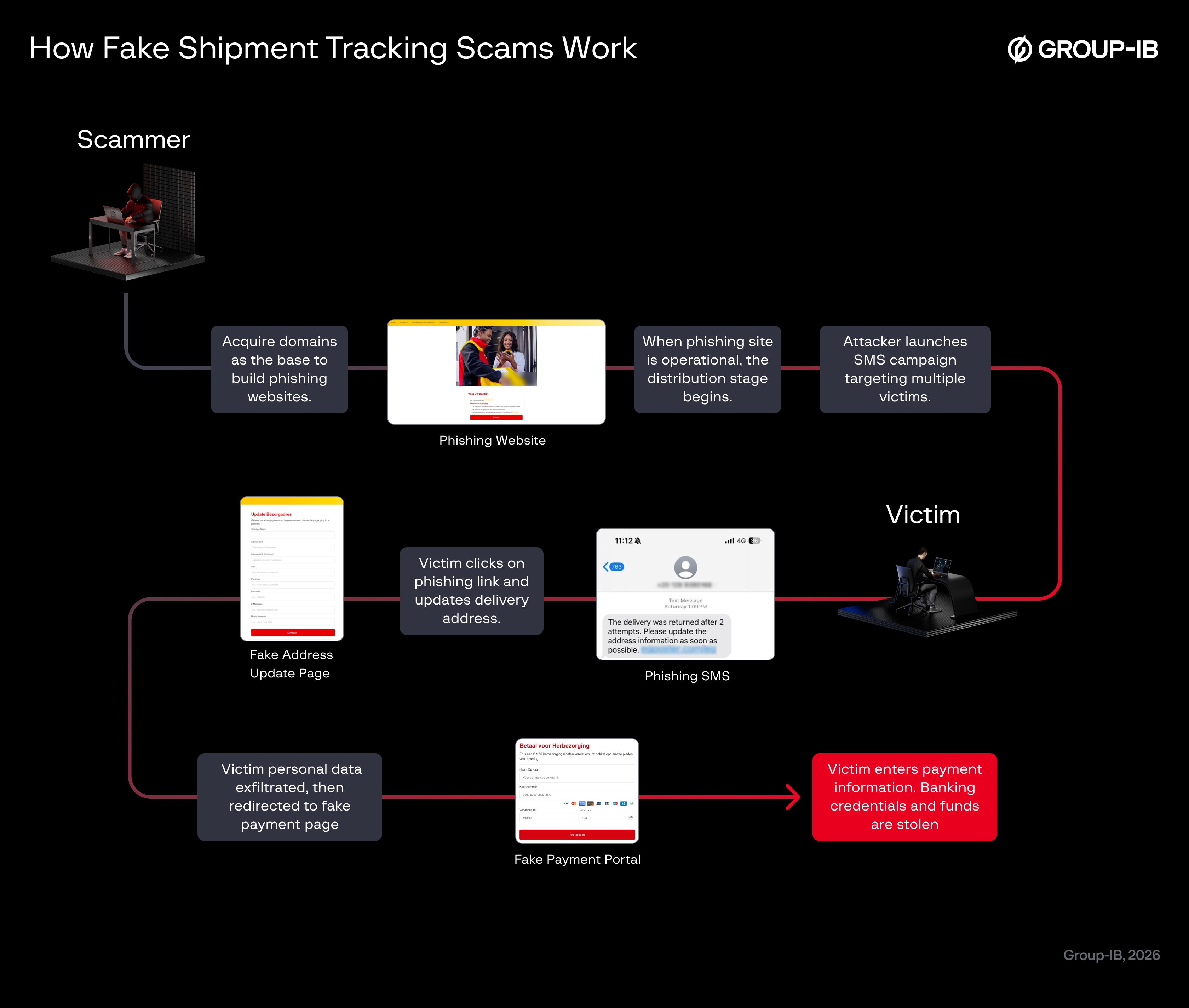
Figure 5. How fake shipment tracking scams work.
How Does the Attacker Deliver Messages?
Once the phishing domain and fake website are ready, attackers are observed to use two different methods for delivery, though both are sent through SMS (Short Message Service):
- Anonymous Number
If the attacker is targeting Egypt, they may send messages from numbers formatted like local Egyptian mobile prefixes such as 02010, 02011, or 02012. This increases the message’s credibility and makes victims more likely to believe it is coming from a legitimate local courier service.
Figure 6. SMS sent though anonymous, but region-specific phone numbers.
- Sender ID Spoofing
Attackers take advantage of how mobile phones group messages by Sender ID. By using online or illegal SMS gateways that allow sender name spoofing, the attacker can send messages that appear to come from the same official sender your phone already trusts. As a result, the fraudulent SMS merges into the legitimate message thread, making it look identical to genuine communications from the real postal or courier service.
Figure 7. Phishing message sent through Sender ID spoofing merges with legitimate SMSs.
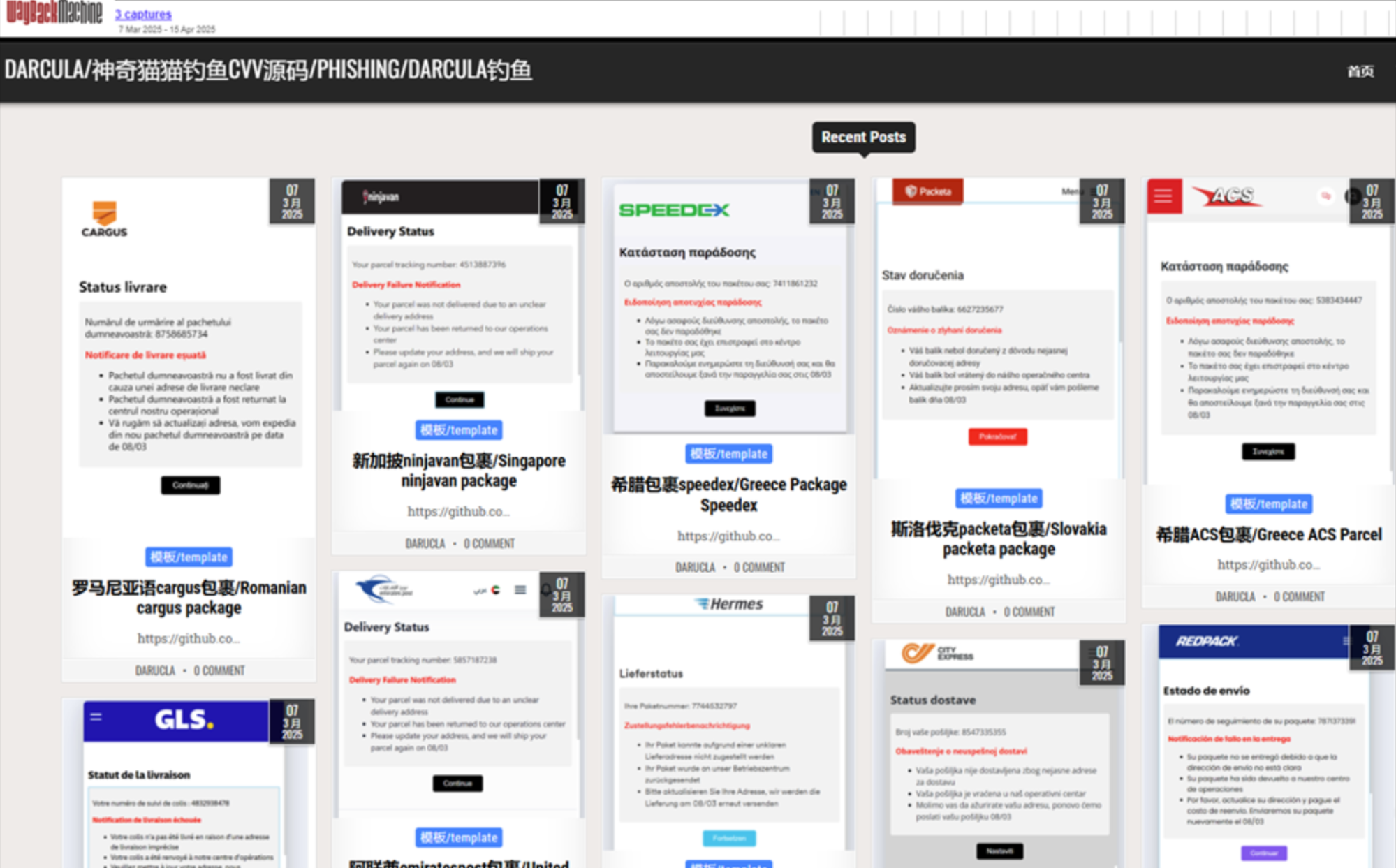
Who is Darcula?
While no single threat actor has been definitively linked to the operation of these fake shipment tracking schemes, Group-IB researchers observed that many of the phishing sites analyzed for this blog share infrastructure and characteristics commonly associated with the PhaaS (Phishing-as-a-Service) provider known as Darcula, which is presumed to be potentially involved in this campaign and associated with PhaaS activity.
Darcula Phishkit is a Chinese-language PhaaS platform that has been widely used in phishing attacks against organizations (government, airlines) and services (postal, financial) in over 100 countries. Darcula phishkit offers cybercriminals more than 20,000 counterfeit domains (to spoof brands) and over 200 phishing templates.
They commercialize phishing-as-a-service through Telegram, emerging in 2023 as a groundbreaking criminal platform that put sophisticated, ready-to-deploy phishing kits directly in the hands of cybercriminals.However, following its exposure from a screenshot by Mnemonic, Darcula removed their public contact information, accounts, domains, and platform and continued their activities privately underground
Figure 8. Original screenshot of Darcula PhaaS services by Mnemonic.
Commonly Abused Top-Level Domains in Scam Campaigns
Many phishing and fake shipment tracking scams rely on cheap, disposable, and lightly regulated domains to operate quickly and anonymously. Extensions such as [.]xyz,[.]help, [.]sbs, [.]shop, [.]click, [.]love, [.]top, and [.]cc are heavily targeted by scammers because they are low cost and easy to register in bulk. Even trusted extensions like .com are abused through look alike variations designed to mimic real brands. Understanding how these top-level domains (TLDs) are misused helps users recognize suspicious links before falling victim to fraudulent delivery notifications or phishing pages.
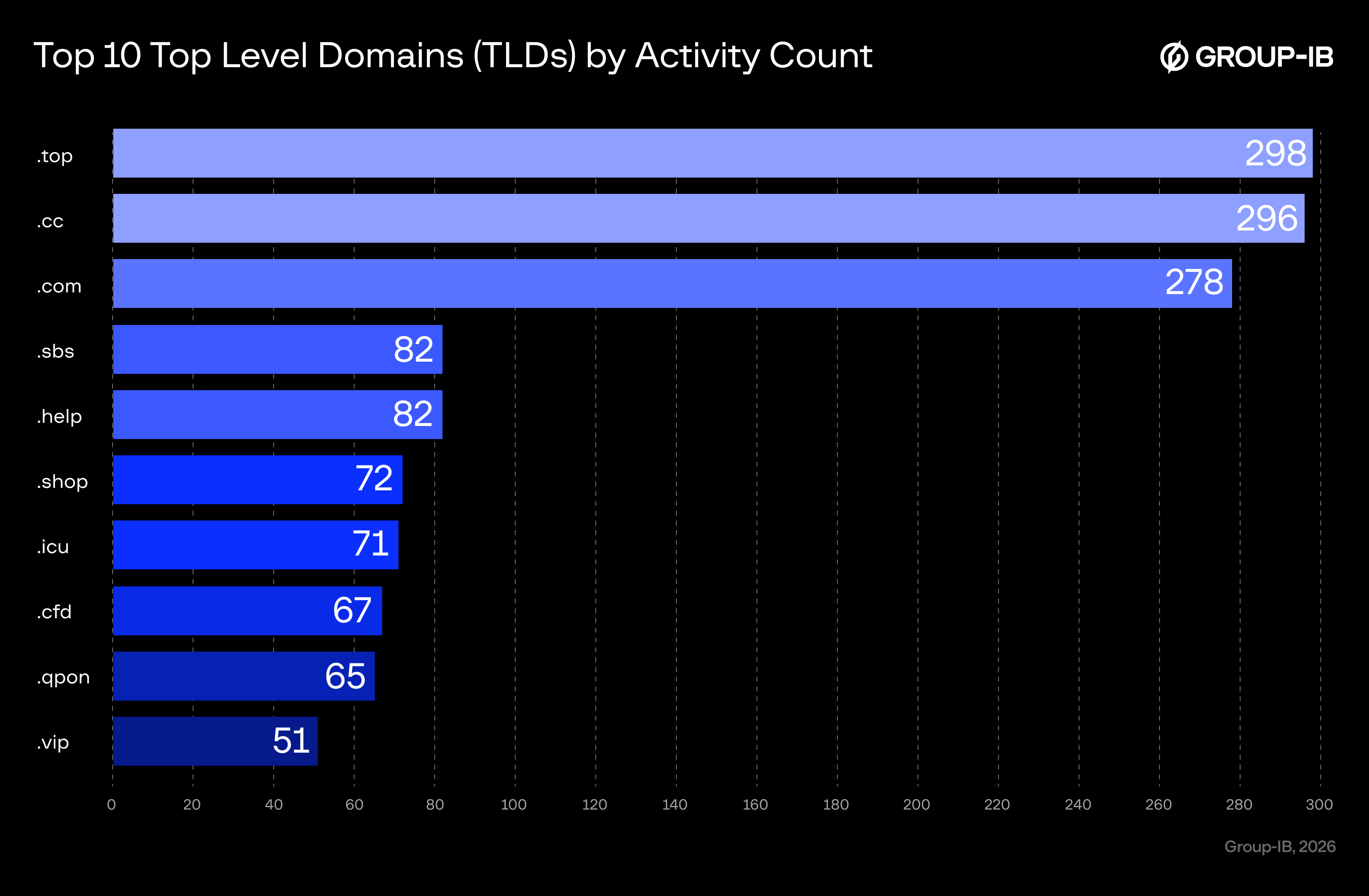
Figure 9. Top TLDs most commonly used in this scheme.
While it may be difficult to confirm the true reasons attackers choose any specific registrar to register phishing domains, the following chart is included in this report to highlight the top 10 registrars seemingly favoured by attackers in this scheme as observed by Group-IB researchers for this investigation.
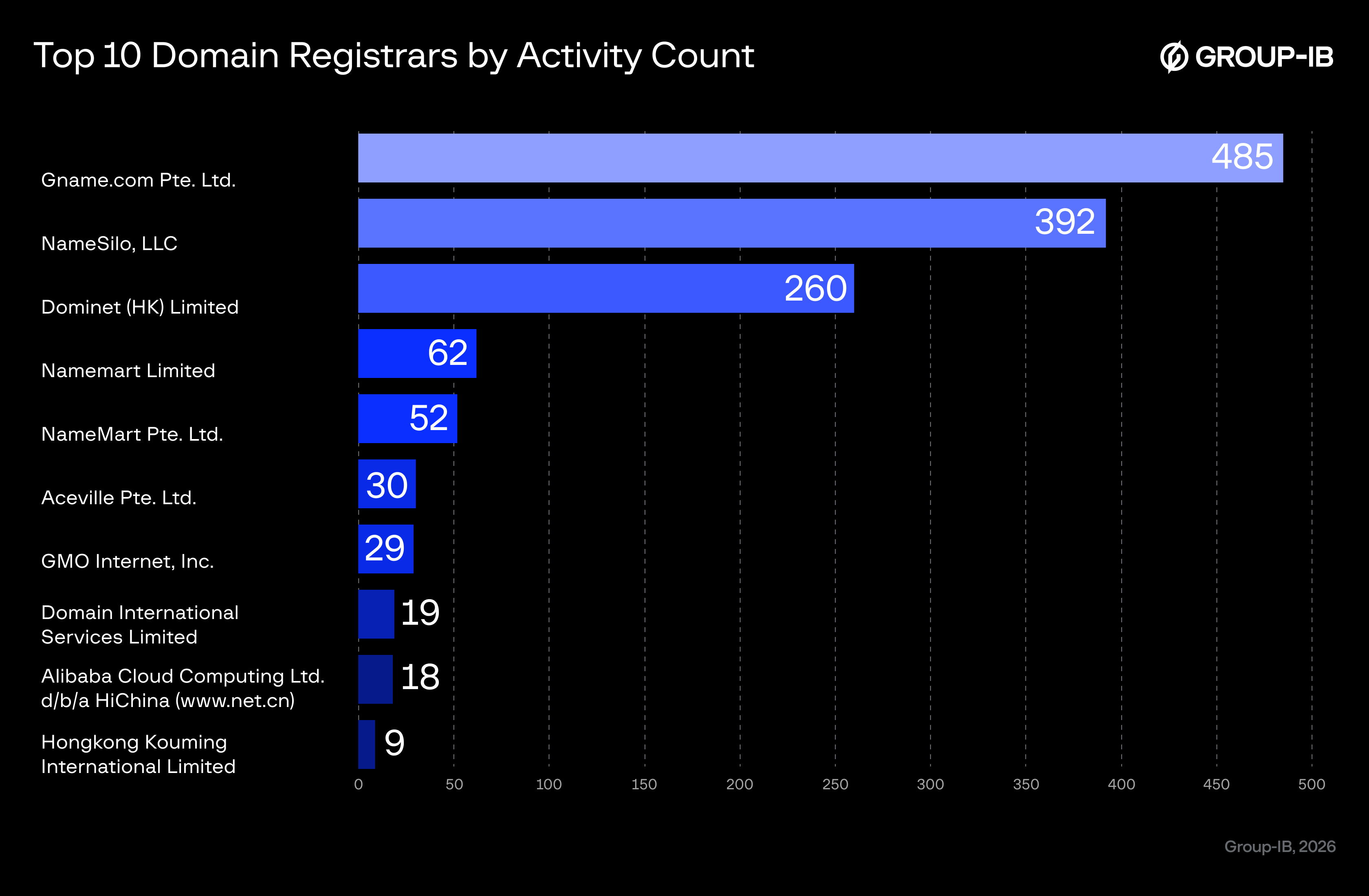
Figure 10. Top domain registrars seemingly favoured by attackers in this scheme.
The Phishing URL
This scheme is made more convincing through localized targeting where the threat actor would try mimicking the names of specific client organizations commonly used by the general public. For example, they would deploy a URL like meapostal[.]click/index.html targeting a Middle East/Africa region entity (MEA).
To deliver the scam, the attacker sends a phishing link to victims via SMS using various spoofing or bulk-message techniques. These links are typically optimized for mobile devices, since most victims open SMS messages on their phones.
Phishing pages often behave differently depending on the user agent, showing their full content only when accessed from a mobile browser. In many cases, the attacker adds a mask or endpoint at the end of the URL such as index.html, eg, i, org, or similar to force the page to load correctly and display the phishing content.
These URL masks not only make the link appear more legitimate but also ensure that the malicious page renders properly on mobile devices, increasing the likelihood of victim engagement.
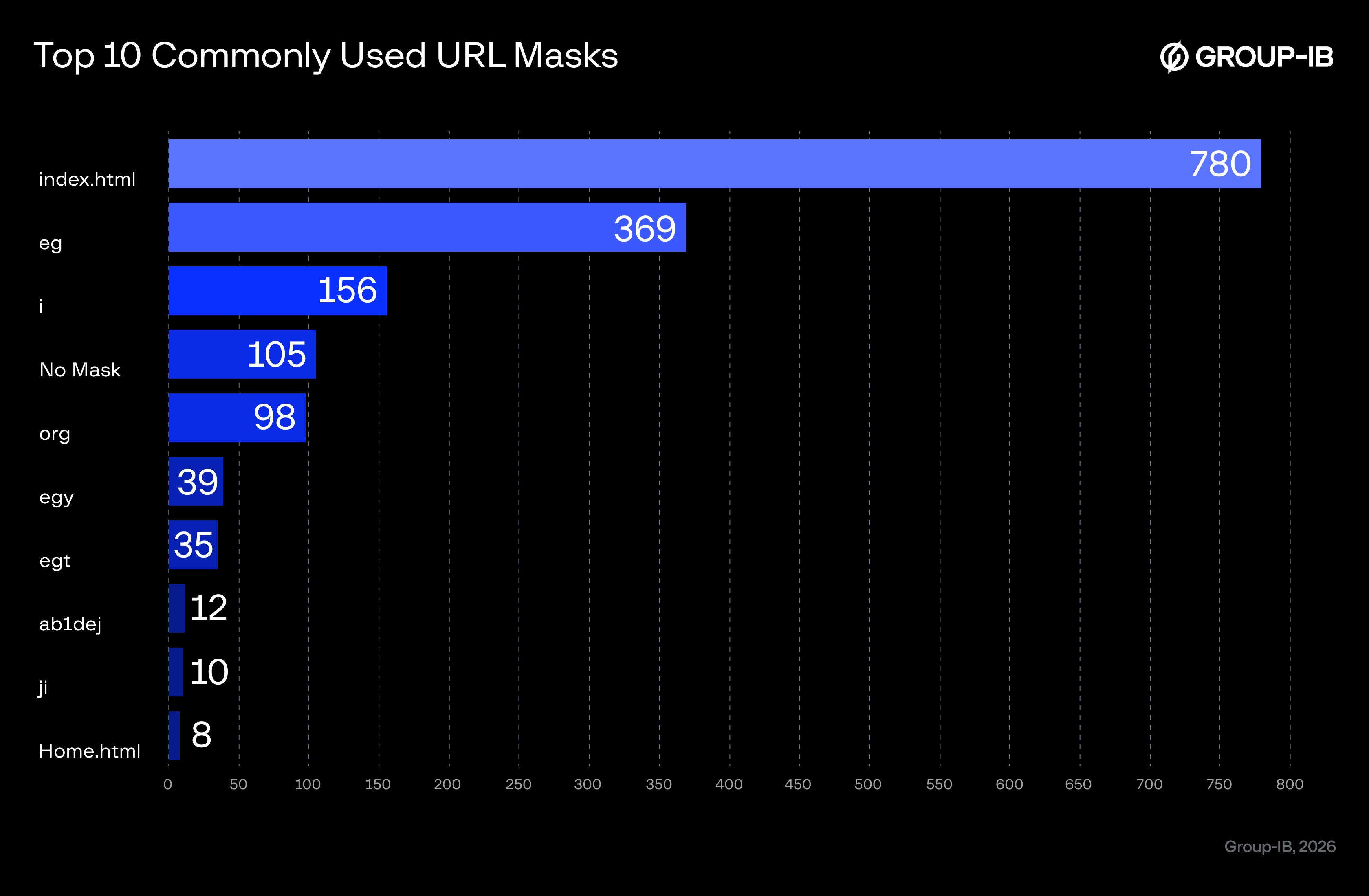
Figure 11. Top 10 URL masks favoured by phishing scams.
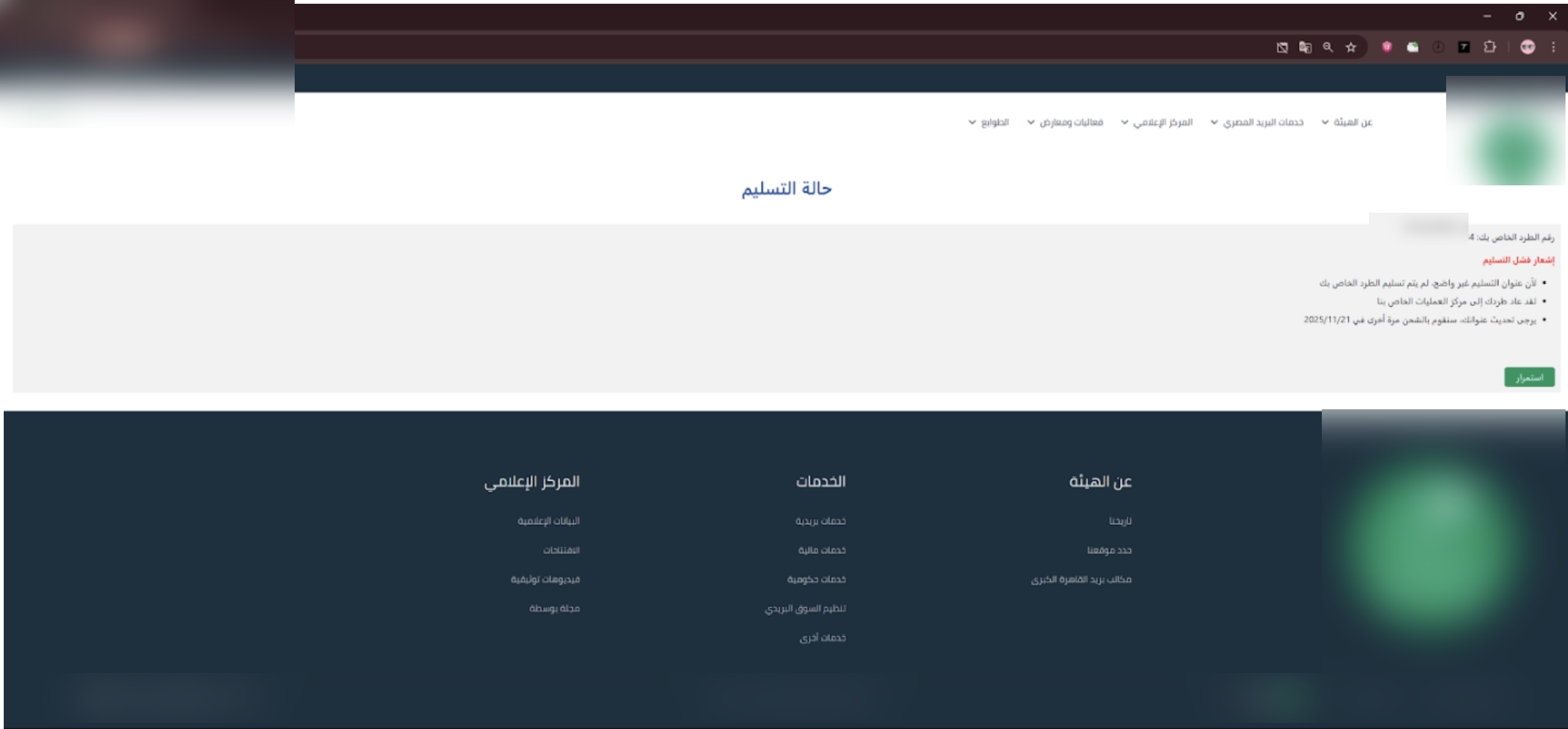
Fake Shipment Tracking Phishing Page Samples
As this scheme is global, Group-IB researchers have also compiled examples of fake shipment tracking phishing content tracked all over the world too:
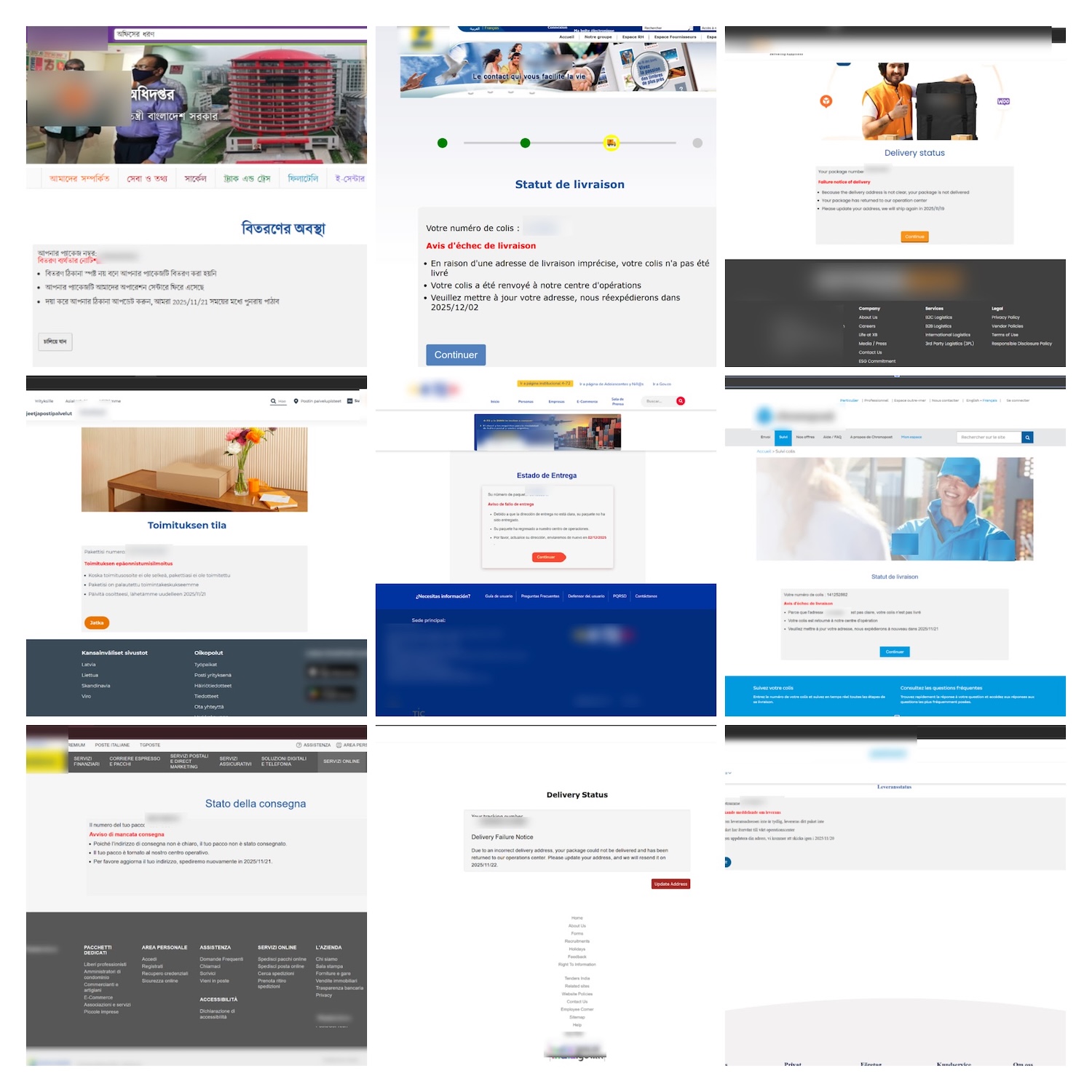
Figure 13. Examples of fake shipment tracking phishing content seen globally.
Interactive Phishing
Phishing links often come with very detailed and convincing “information” about fake shipments that include:
a – Shipment number or tracking ID.
b – Reasons for non-delivery.
c – Seemingly legitimate requests to update personal information such as home address information to resume the shipment process.
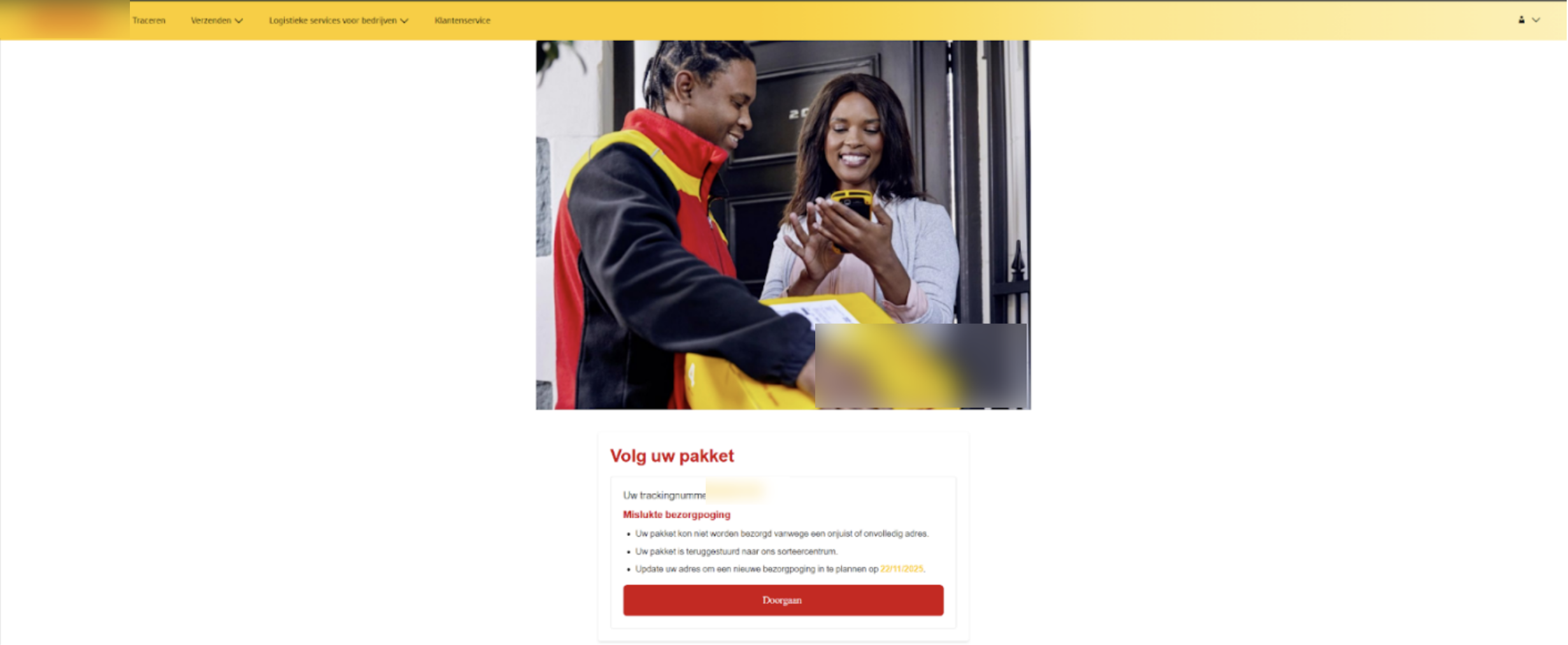
Figure 14. Fake shipment tracking scams work because such tracking updates have become commonplace.
Since courier and parcel services are so widely used today, most people who actively shop on e-commerce platforms may be having goods shipped from all over the world with complex logistic handling from initial pickup to last mile delivery. It has become commonplace to receive multiple shipment or tracking information, and scammers rely on this trend and behaviour to bypass general scrutiny. The victim trusts the process and proceeds to fill in the missing information.
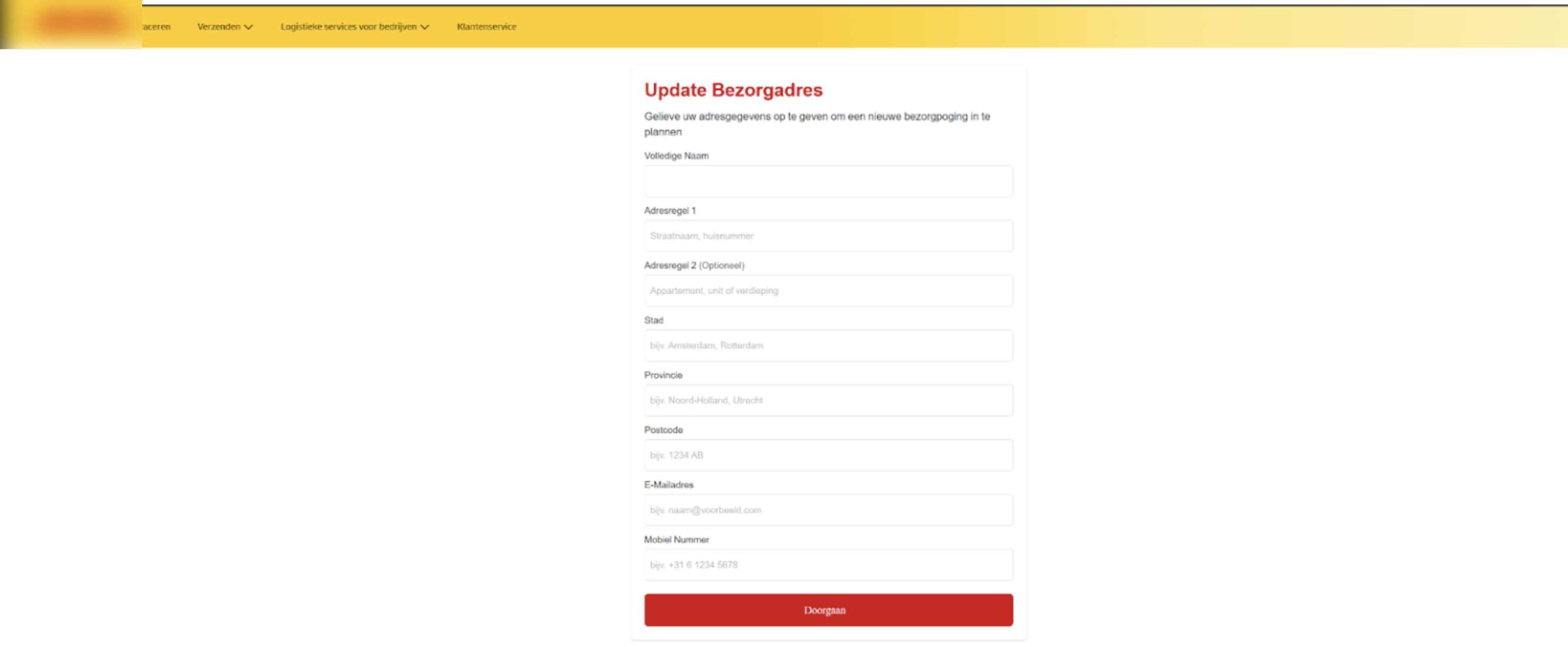
Figure 15. Once victims click through the fake tracking notice, their trust is abused to harvest personal and financial information.
After the victim fills in the missing information, the page will then request for payment for the shipment to be resent. Victims will need to fill in credit card or banking account details to process the payment, this is where victim funds and credentials are both stolen.
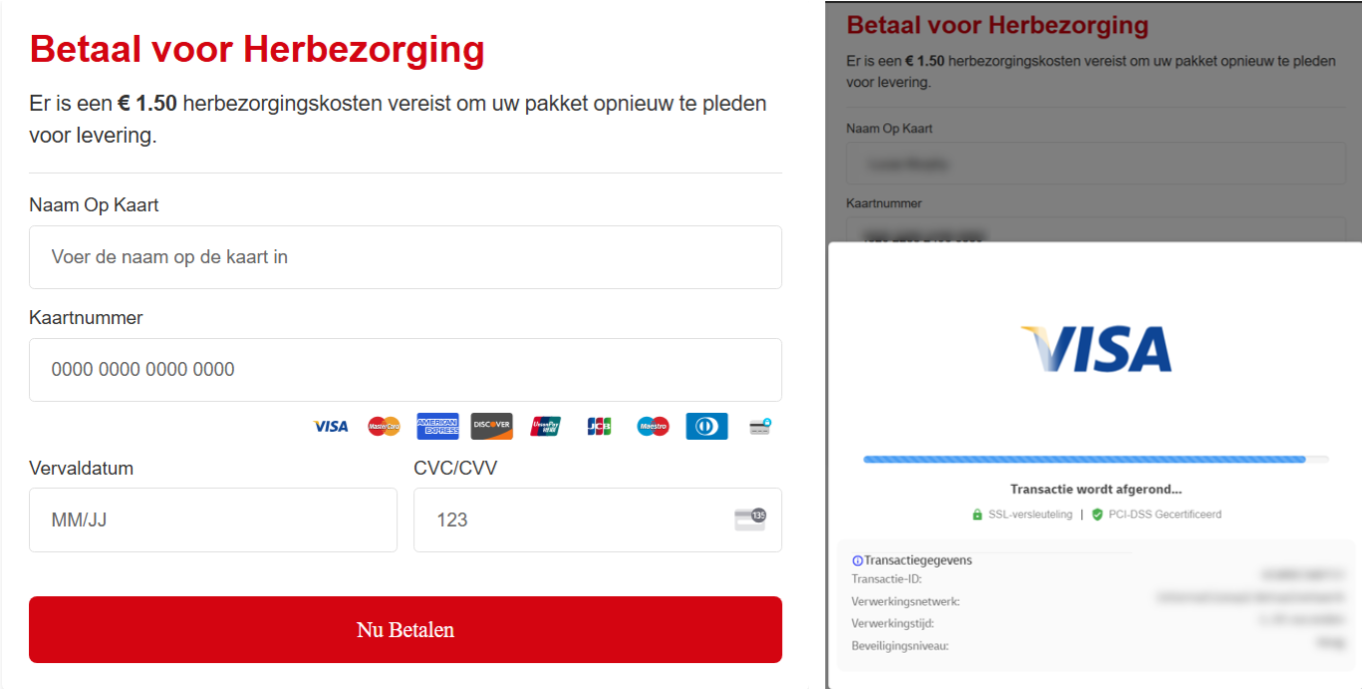
Figure 16. Besides credential harvesting, a second payment stage directly steals victim funds.
HTML Code Analysis
Embedded Scripts
Group-IB investigations into the phishing pages have found a common trend of embedded scripts hidden within the HTML code that carry out the credential harvesting attacks.
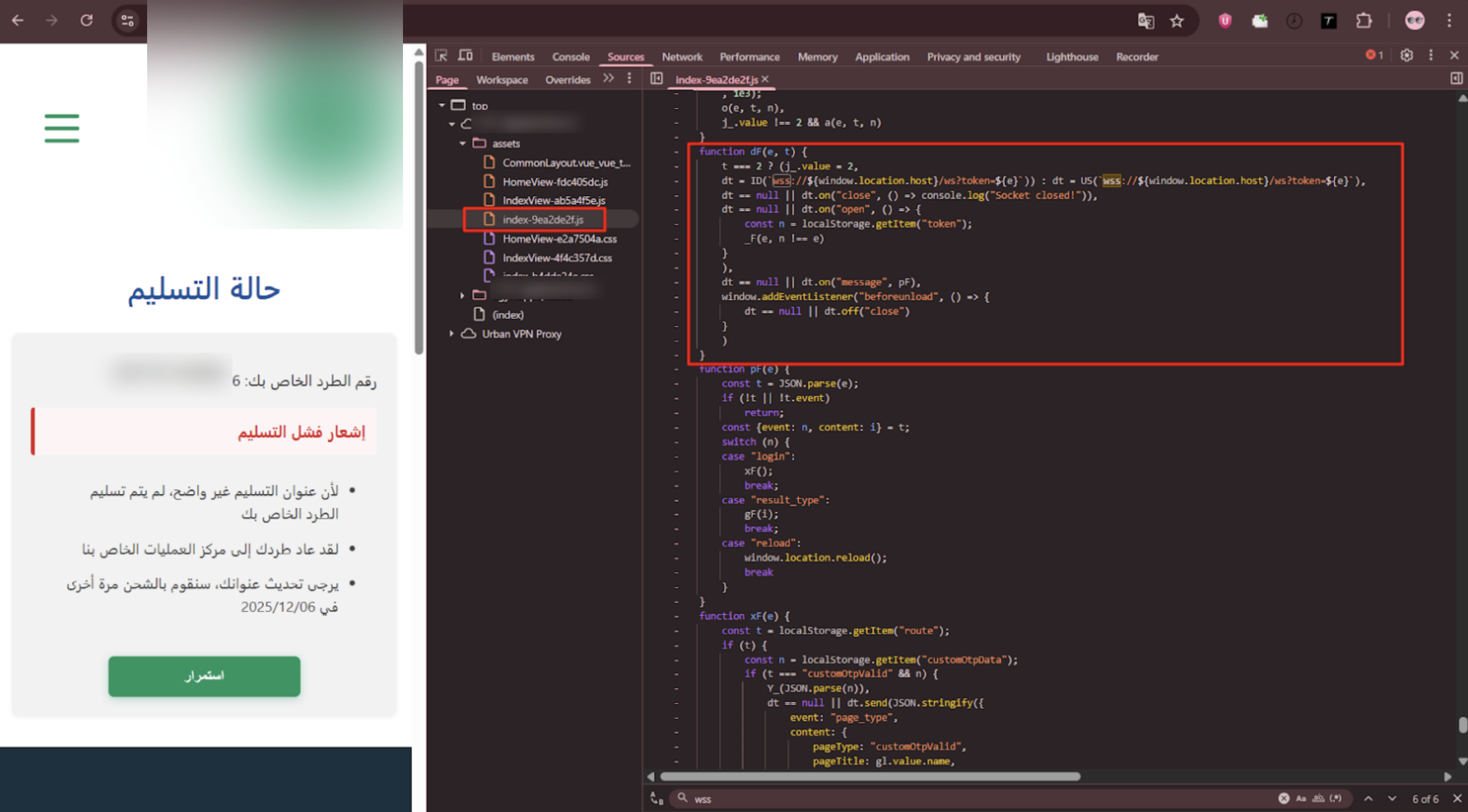
Figure 17. Credential harvesting scripts are embedded in the HTML code of the phishing pages.
The attacker makes the initial configuration and opens a WebSocket connection for real-time, bidirectional communication with a server hosted on the same domain.
(wss://${window.location.host}/ws)
This allows for real-time keylogging and exfiltration, immediately sending every keystroke and form input (including sensitive data like card numbers, CVV, and OTPs) to an attacker-controlled server via the persistent WebSocket connection.
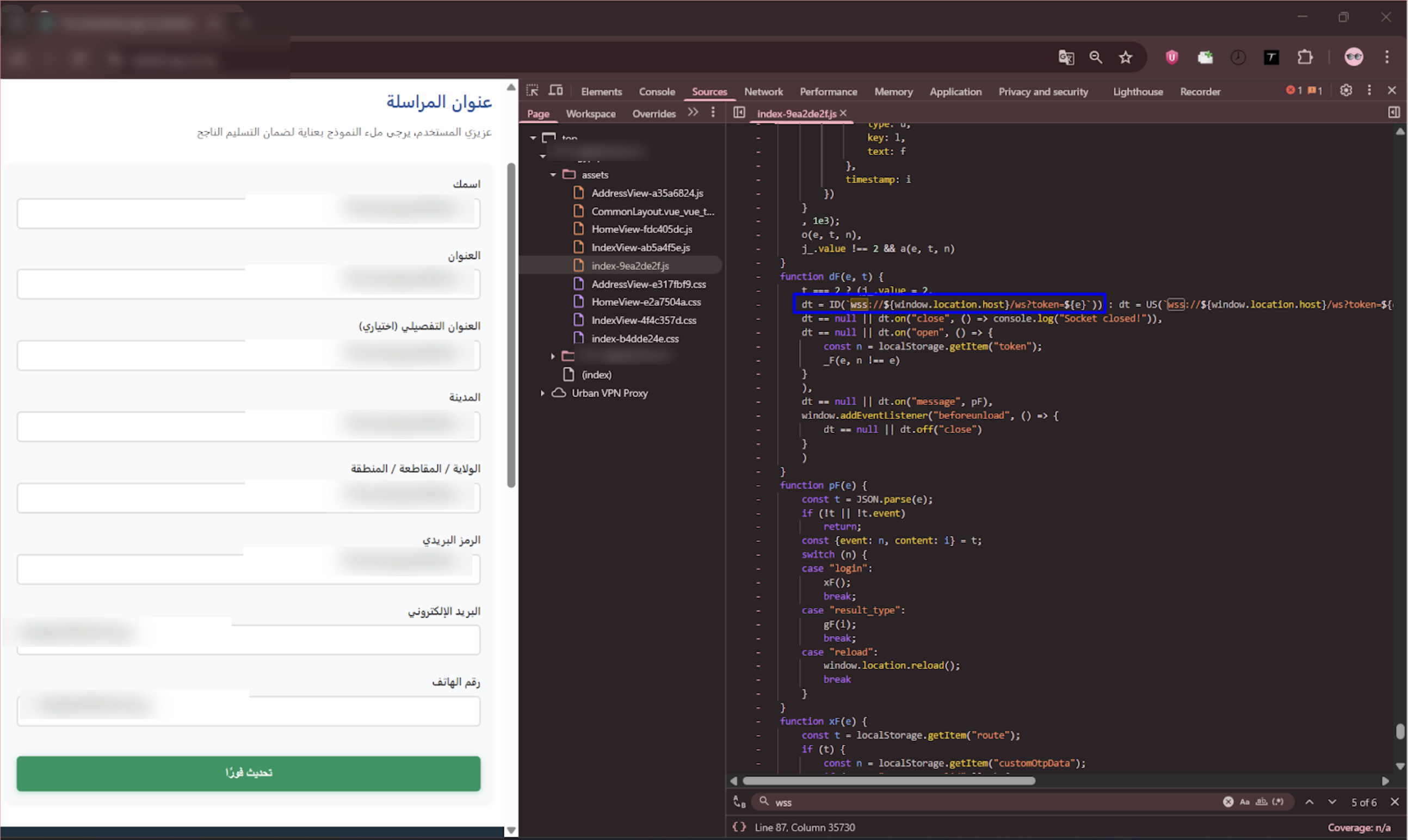
Figure 18. An open WebSocket connection allows for real time keylogging and data exfiltration.
Victim Information Tracking
The script is also observed to generate aUUID token to track each individual user’s session, suggesting that the scheme is not a small operation and the attackers are highly organized.
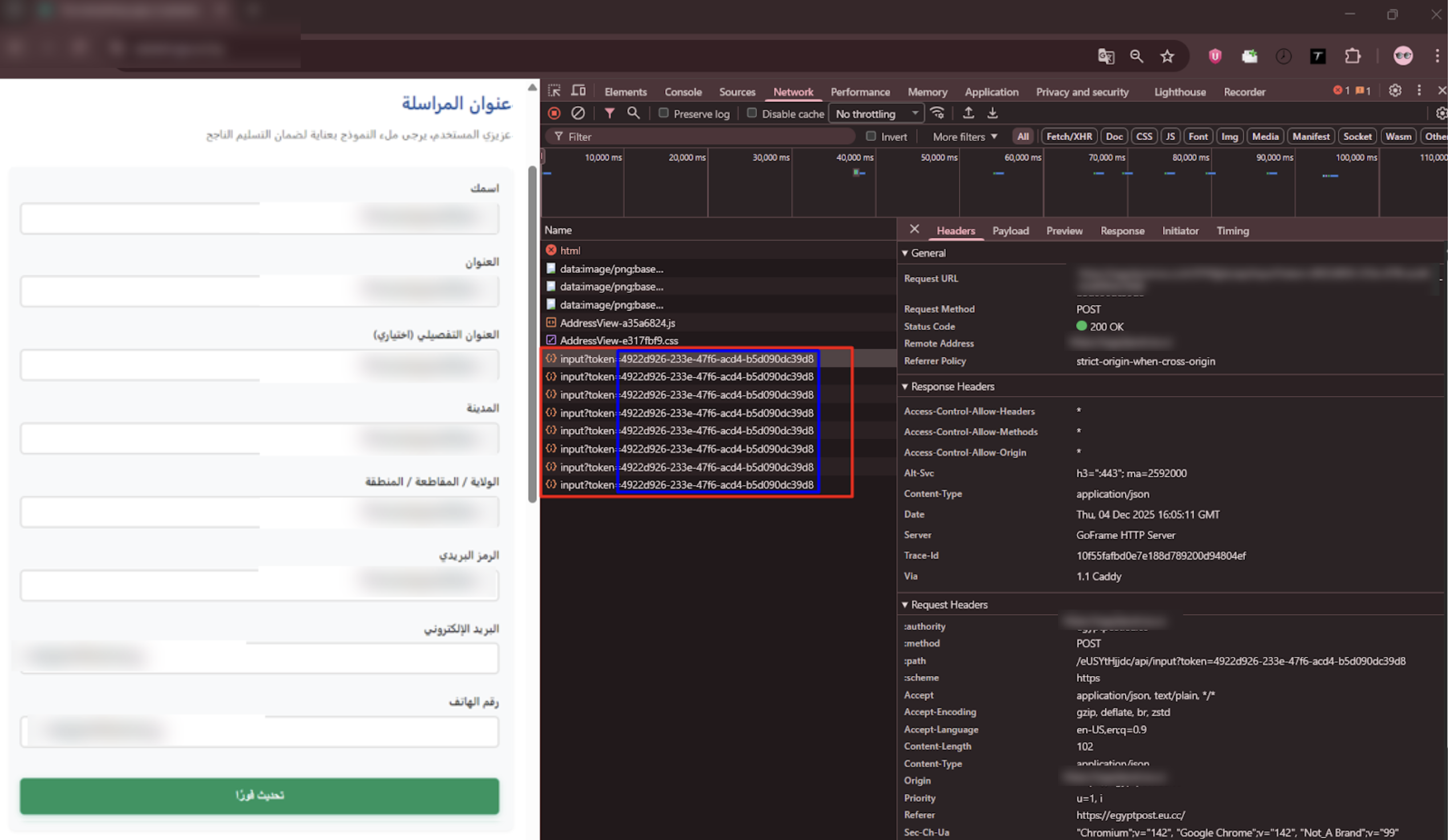
Figure 19. The script generates UUID tokens to track individual sessions.
Fake Parcel Tracking Is Only The Beginning
While the focus of this blog’s research is the fake shipment tracking scam, the same scheme extends into other industries beyond postal services. It targets online shops, transportation apps, electricity and fines bill payments, online platform subscriptions, and telecommunications providers.
Conclusion
The rise of the “fake shipment tracking” scam is a direct consequence of the world’s increasing reliance on global e-commerce and delivery services. Scammers are exploiting both consumer familiarity with parcel tracking notifications, which have become a commonplace activity ingrained into most of our daily lives and the universal anxiety of a missed package by using high pressure tactics, domain lookalikes, and sophisticated Sender ID spoofing to steal sensitive data.
As these fraudulent messages continue to circulate globally, understanding how they work is the first step in protection. For individuals, the core defense remains constant: never click unsolicited tracking links. Always verify a delivery status by navigating to the official courier website manually, following only official links from e-commerce platforms used and known tracking numbers from your real purchases and invoices. For businesses, a proactive defense including public education, robust domain security, and providing verification tools is essential to build trust and protect customers from pervasive social engineering threats.
Recommendations
For individuals:
- Never click on tracking links sent via SMS, WhatsApp, or email. Instead, manually visit the courier’s official website and enter your tracking number.
- Verify unsolicited tracking numbers against known purchases or parcels you are expecting before taking any further action.
- Check the sender: Real delivery companies do not use random numbers or private emails.
- Be Suspicious of urgent warnings that demand immediate action. Phishing messages often include social engineering cues designed to pressure victims into action and bypass common sense checks.
- Look for domain red flags of unfamiliar or uncommon domain names such as [.]xyz, [.]sbs, [.]top, [.]click, etc.
- Triple check before entering any payment information online. Legitimate courier companies usually do not request payment for simple administrative tasks such as address updates or scheduling redelivery.
- Use security tools that provide features such as SMS spam filtering, email phishing detection and browser warnings.
- Report suspicious messages to your postal service or local cybersecurity authority to help protect others.
For businesses and platforms:
- Educate the public and customers by regularly publishing alerts about ongoing phishing attempts using your brand. Share examples of fraudulent messages and official contact channels.
- Strengthen official domains using strong authentication and domain security protocols such as DMARC, SKIM and SPF to reduce emails sent under your company name.
- Employ a brand protection service — such as Group-IB’s Digital Risk Protection Platform — that can actively track fake domains, fraudulent pages and suspicious TLD registrations impersonating your brand.
- Provide a public verification tool that allows customers to verify tracking numbers, check and confirm official messages and communication channels to immediately reduce scam success rates.
- Ensure strong branding practices in official messages such as consistent short codes, single verified domain, and secure https links. Scammers struggle to mimic consistent patterns.
- Work with mobile operators to filter scam SMS patterns and block impersonation attempts before they reach the customer.
- Having a clear reporting channel makes it easy for customers to forward suspicious messages for verification. A simple email like “fraud@yourcompany.com” can greatly reduce damage.
Frequently Asked Questions (FAQ)
What is the fake shipment tracking scam and how does it affect victims?
Also known as fake parcel/postal/delivery tracking, criminals send fraudulent delivery failure notices to victims with phishing links intended to harvest personal and banking credentials, which can cause direct loss of funds. Read more about phishing on the Group-IB Knowledge Hub.
Why are fake shipment tracking scams increasing?
In the age of e-commerce, postal and courier services have become the backbone of the global marketplace. Over 161 billion parcels shipped worldwide in 2022 alone. The likelihood of the average person receiving packages and such delivery notices on a regular basis has become commonplace in today’s society. Criminals exploit this trend to blend into daily digital traffic and bypass casual scrutiny.
What are the techniques that scammers use?
Some of the most common methods used by scammers in fake shipment tracking schemes include:
- Sending spoofed SMS messages that can appear to come from legitimate sources.
- Registering and creation of phishing domains and websites.
- Embedding malicious scripts to harvest victim credentials.
- Social engineering tactics to instill urgency such as potential loss of packages, increased fines and taxes, or redelivery and handling fees, urging victims to act immediately.
What do cybercriminals do with stolen credentials?
They are often sold on the dark web or used in other fraud campaigns and attacks. Read more about the dark web here.
Indicators of Compromise (IOCs)
Network IOCs
- posties[.]icu
- estafmox[.]help
- nrcsnap[.]com
- pkgov[.]shop
DISCLAIMER: All technical information, including malware analysis, indicators of compromise and infrastructure details provided in this publication, is shared solely for defensive cybersecurity and research purposes. Group-IB does not endorse or permit any unauthorized or offensive use of the information contained herein. The data and conclusions represent Group-IB’s analytical assessment based on available evidence and are intended to help organizations detect, prevent, and respond to cyber threats.
Group-IB expressly disclaims liability for any misuse of the information provided. Organizations and readers are encouraged to apply this intelligence responsibly and in compliance with all applicable laws and regulations.
This blog may reference legitimate third-party services such as Telegram and others, solely to illustrate cases where threat actors have abused or misused these platforms.
This material is provided for informational purposes, prepared by Group-IB as part of its own analytical investigation, and reflects recently identified threat activity.
All trademarks referenced herein are the property of their respective owners and are used solely for informational purposes, without any implication of affiliation or sponsorship.