Introduction
In recent years, the shift toward remote work has introduced unprecedented vulnerabilities into corporate hiring pipelines. Among the most sophisticated and organized of these threats is the infiltration of global software and IT companies by North Korean (DPRK) IT workers. Operating under synthetic identities, these individuals present themselves as highly experienced developers from all over the world to secure lucrative, long-term remote roles.
This is not a classic malware intrusion chain; it is a labor-enabled access model built around social engineering, synthetic identity operations, and platform abuse. Beyond the immediate risk of data theft, organizations that unknowingly hire these workers face severe legal and compliance risks, as employing or paying DPRK IT workers could constitute a direct breach of UN, US, and UK financial sanctions. This blog explores the complex ecosystem supporting these fake candidates, detailing our investigation into their worldwide operations, and provides organizations with a comprehensive playbook to detect and mitigate the threat.
Key discoveries
- Identified a broader DPRK IT worker-related ecosystem extending beyond previously exposed GitLab accounts and spanning GitHub, personal portfolio sites, freelancing infrastructure, and synthetic identity support materials. The activity observed in this cluster dates back to at least 2021 and remained active through March 2026.
- Observed the repeated use of synthetic or repurposed developer personas tied to overlapping GitHub repositories, email accounts, portfolio domains, and supporting documentation. The same operator-controlled assets were reused across multiple identities.
- Uncovered evidence of operational support infrastructure behind these personas. This included archived persona materials, staged job application content, AI-assisted response templates, platform access information, and lists of accounts and services used to maintain the appearance of legitimate remote developers.
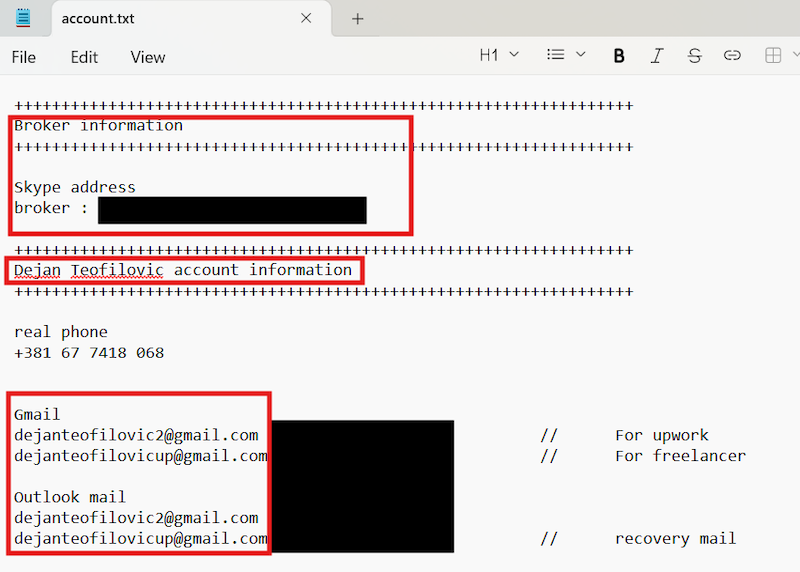
- One of the most important findings was a repository archive containing synthetic identity materials for Dominic Williams and Dejan Teofilovic. This archive provides direct insight into how “persona” packages were assembled, maintained, and potentially handed over between operators or working groups.
- This report further links the ecosystem to attempts to acquire verified Upwork accounts as early as 2021. This connection is significant because it aligns with known DPRK remote worker tradecraft: obtaining access to trusted labor platforms, deploying credible developer personas, and creating a pathway for revenue generation, insider placement, or follow-on compromise.
Who may find this blog interesting:
- Cybersecurity analysts and corporate security teams
- Human Resources and Talent Acquisition specialists
- Threat intelligence specialists
- Compliance and Legal teams
- Cyber investigators
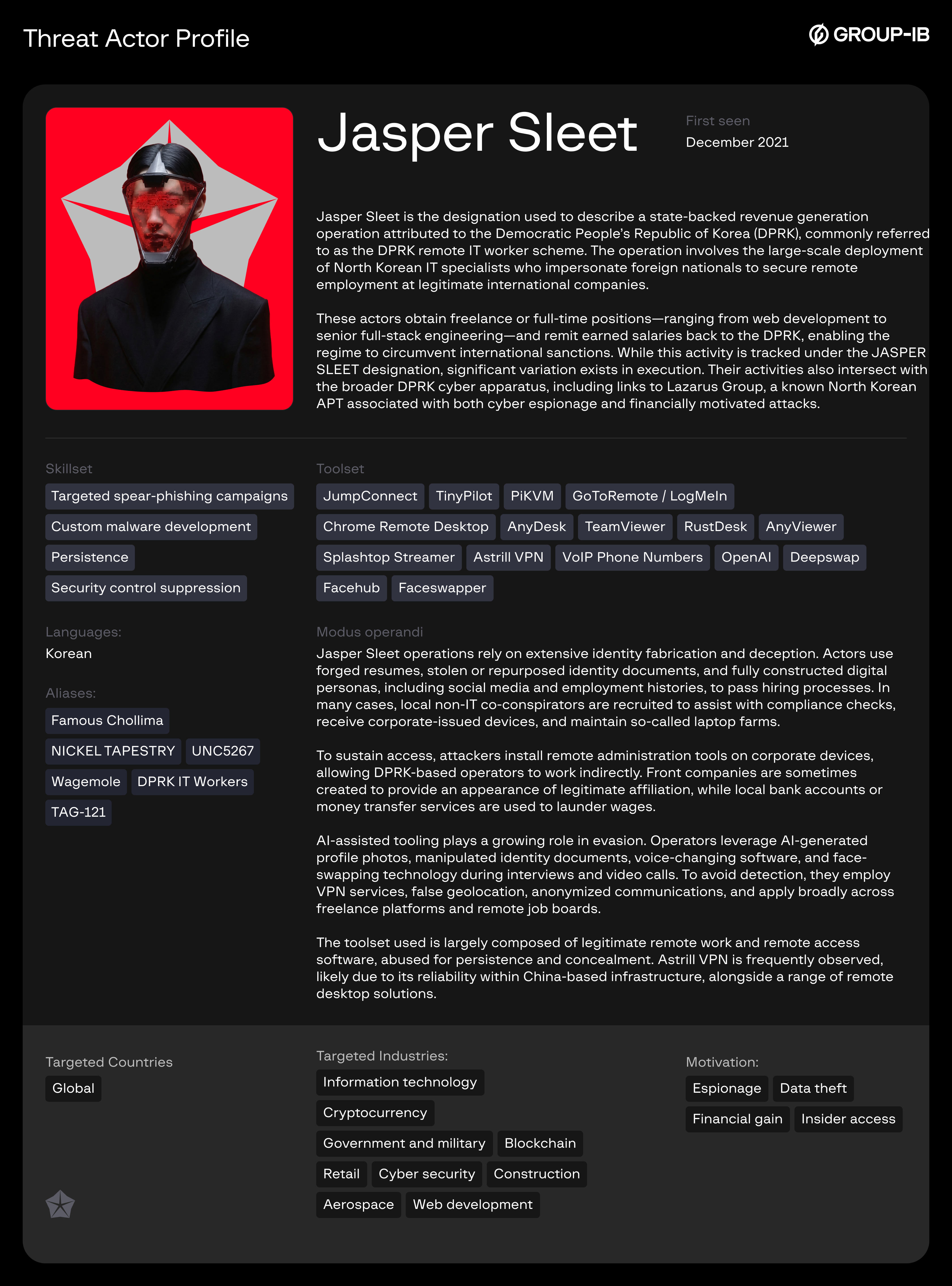
Group-IB Threat Intelligence Portal: JASPER SLEET (aka DPRK IT Workers)
Group-IB customers can access our Threat Intelligence portal for more information about the infrastructure, domains, and specific indicators of compromise related to the DPRK IT Worker ecosystem.
Investigation Overview
This research began as a pivot from prior public reporting by GitLab on DPRK IT workers. Group-IB Threat Intelligence Team assessed that the accounts exposed by GitLab likely represented only a portion of a larger network and that related infrastructure may still have been active on other platforms despite account takedowns or vendor enforcement.
Using one of the email addresses previously identified by GitLab – nicolas.edgardo1028@gmail[.]com – we traced a GitHub account, cybersage14, which served as an entry point into a wider ecosystem of overlapping personas, repositories, and supporting assets. From there, we correlated additional GitHub users, portfolio sites, resume content, contact details, and archived materials that, when analyzed together, exposed an organized remote worker support framework rather than isolated fraudulent profiles.
Our findings show a structured and repeatable workflow: create or acquire a persona, build a credible developer history, support it with hosted portfolios and project repositories, maintain associated communication and payment channels, and prepare tailored job application responses. This is not a classic malware intrusion chain. It is a labor-enabled access model built around social engineering, synthetic identity operations, and platform abuse.
Group-IB Threat Intelligence Team have reported all identified profiles linked to DPRK IT workers to GitHub. If you come across similar accounts, we encourage you to report them as well — collective efforts are key to addressing this threat.
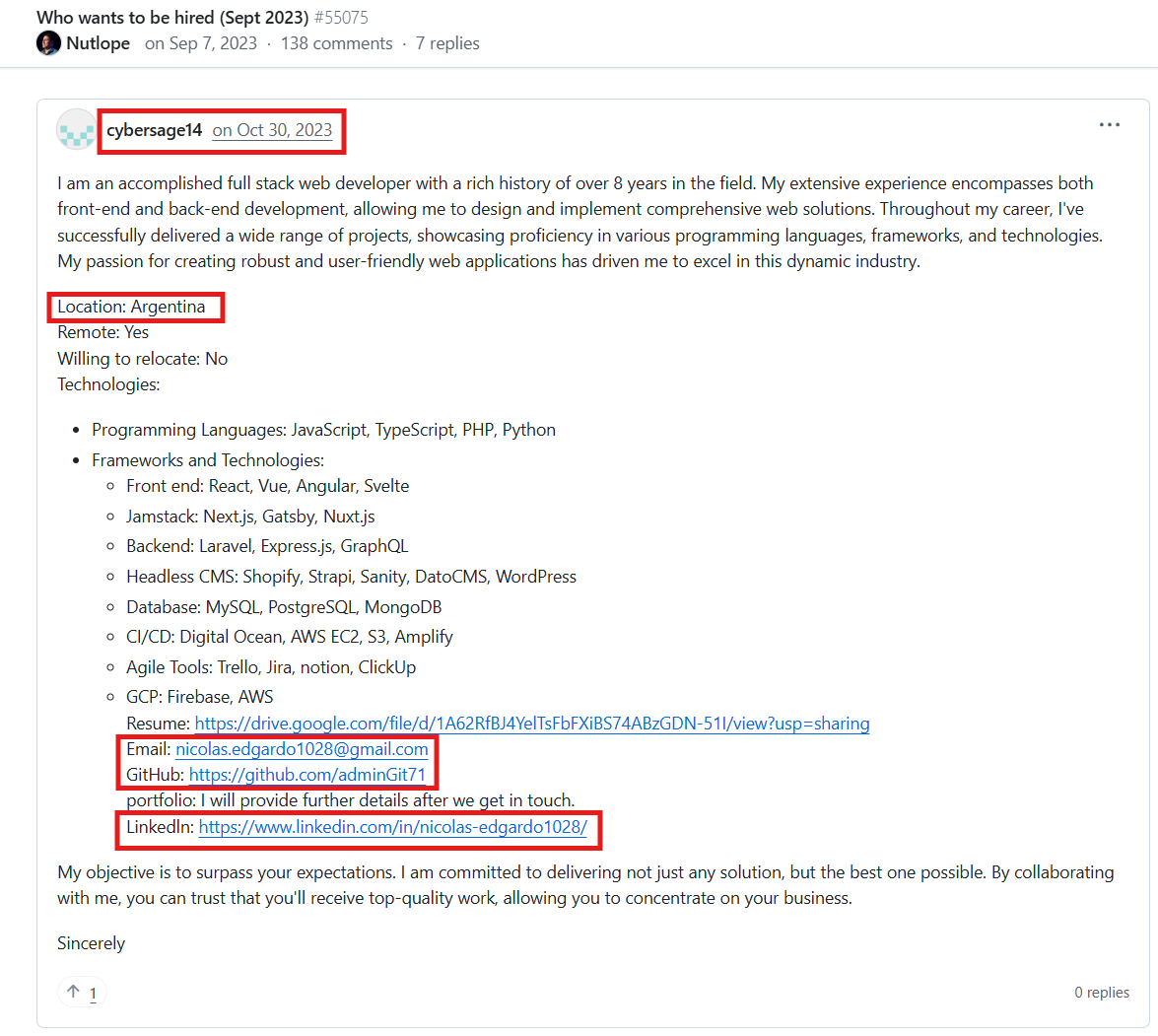
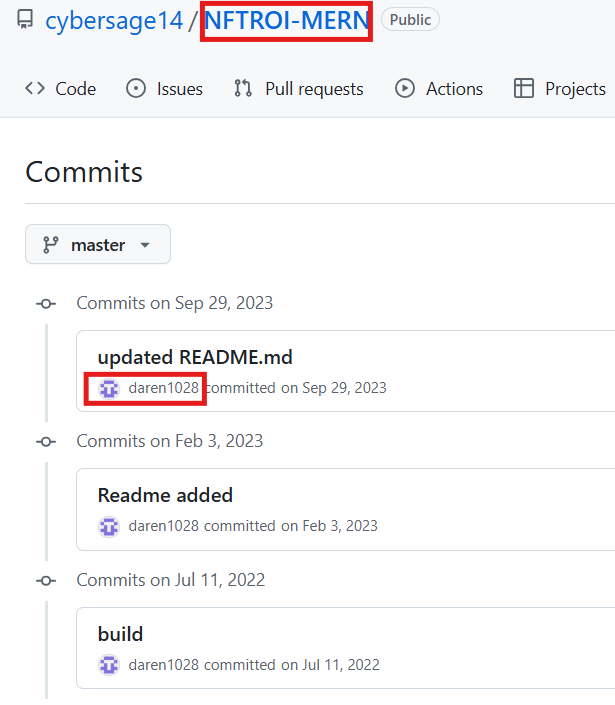
Initial Lead: cybersage14
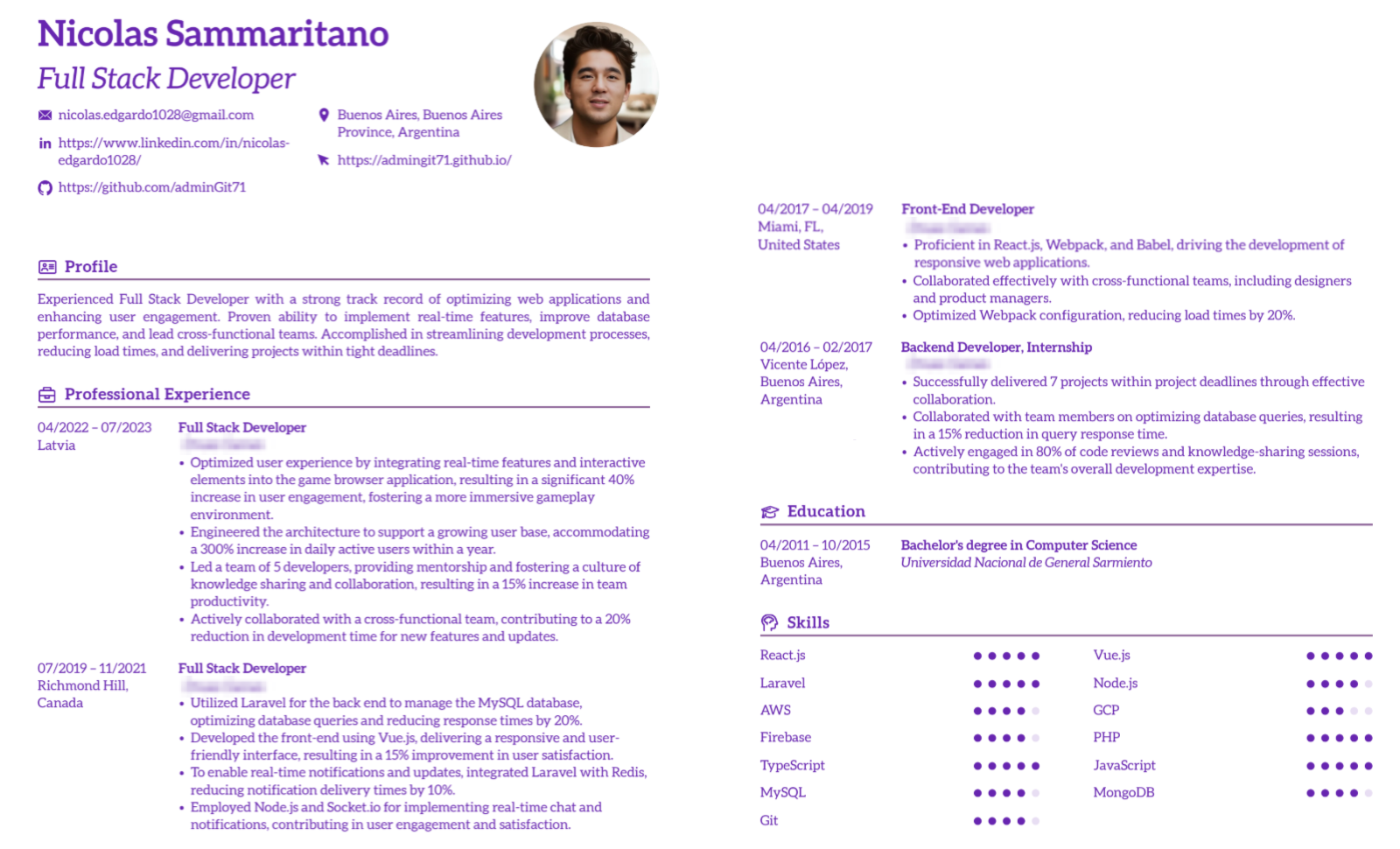
Our investigation started with the email address nicolas.edgardo1028@gmail[.]com, previously associated with DPRK IT worker activity. Open-source pivoting led us to the GitHub account cybersage14, where the user had posted a job-seeking resume in October 2023, presenting as a full-stack web developer with eight years of experience.
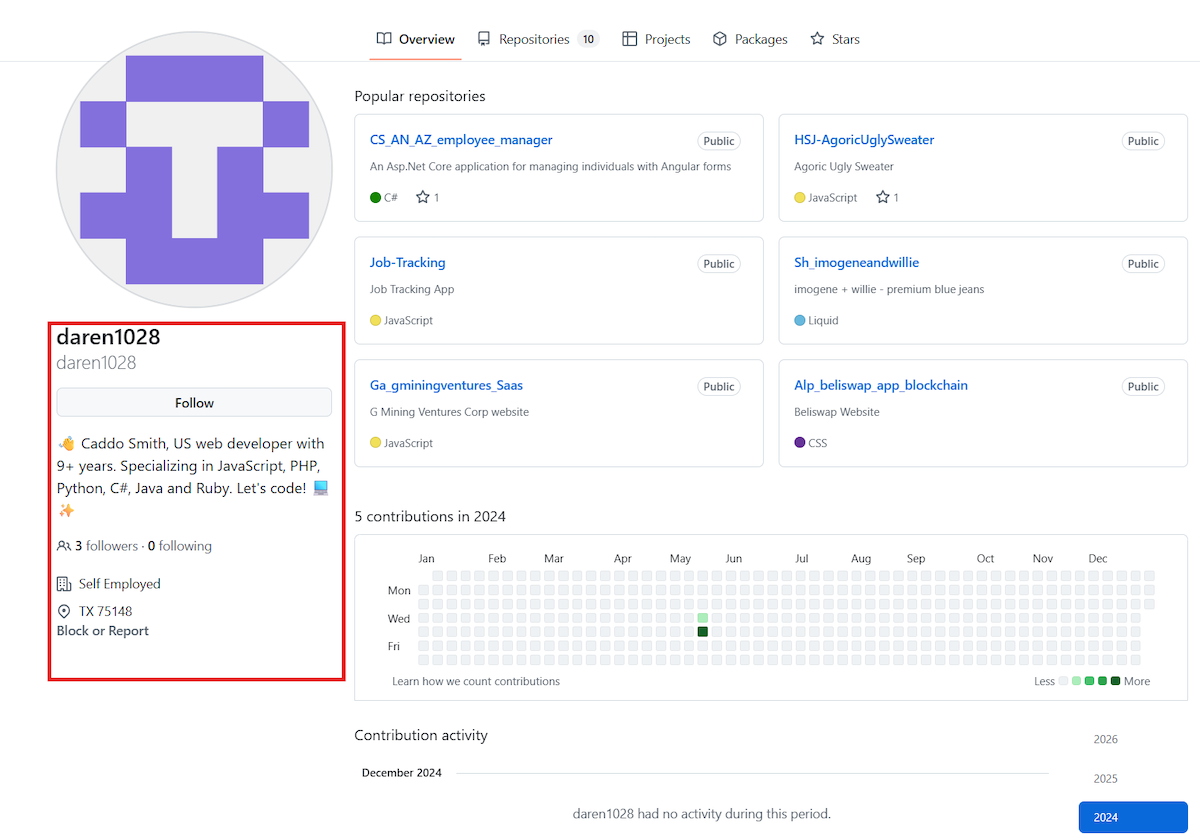
The persona initially used the name Nicolas Sammaritano, claiming to be based in Buenos Aires, Argentina. The associated image appeared AI-generated or heavily smoothed. In May 2024, the same cybersage14 account published another job-seeking post, but this time under the name Caddo Smith, allegedly from Texas, United States.
This identity shift is one of the earliest indicators that the account was being used as a reusable persona shell rather than representing a single individual. The technical profile remained largely the same, while the visible biographical layer changed.
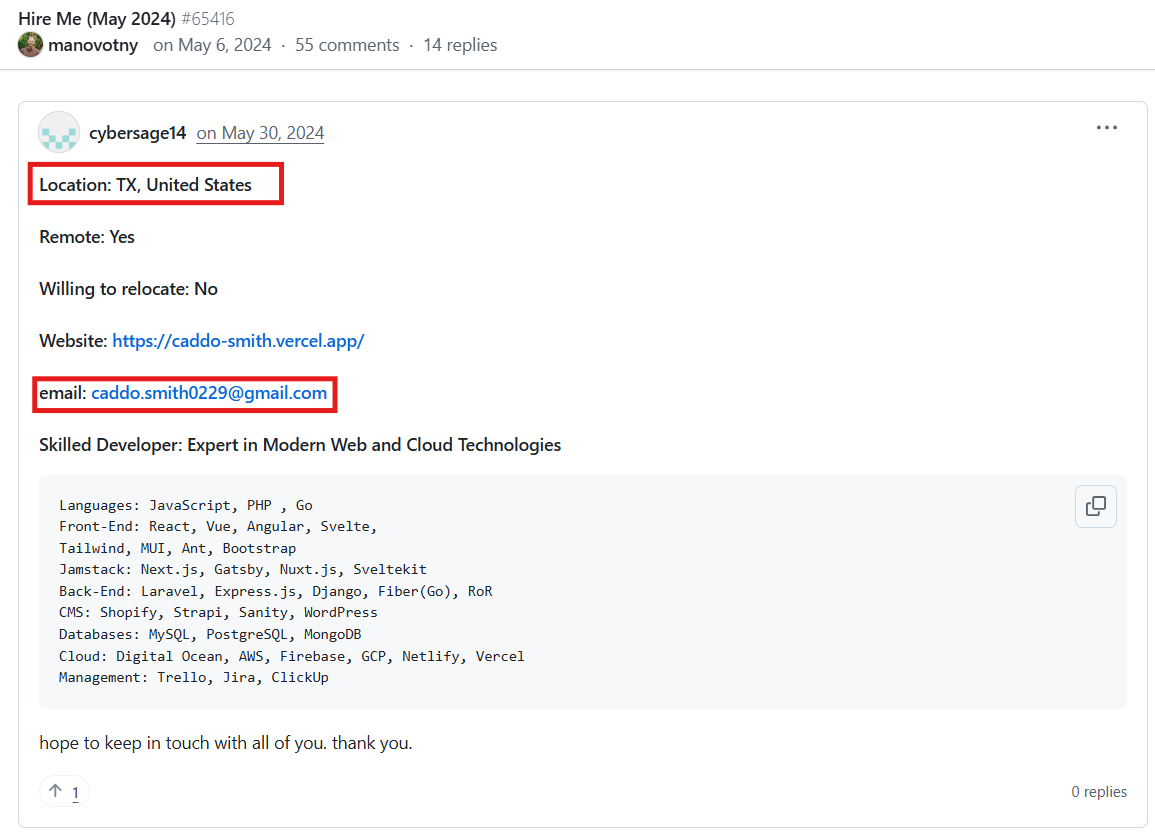
Figure 2. Another Cybersage14 contacts and profile.
Repository-level Correlation
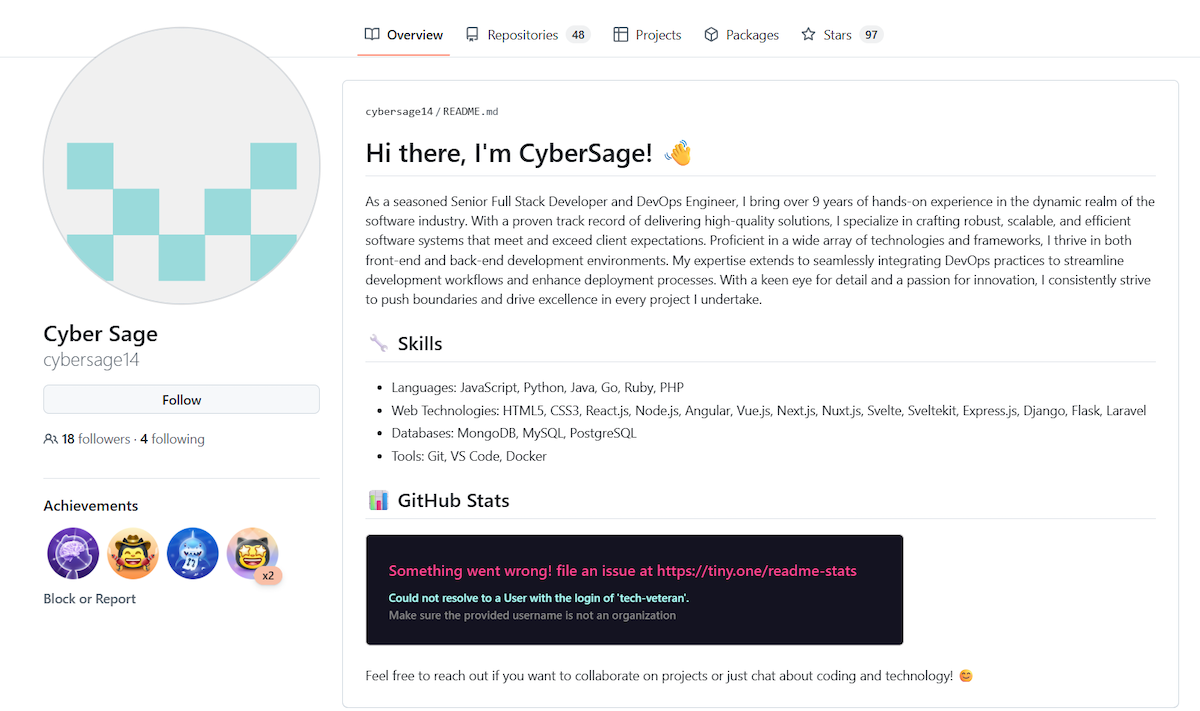
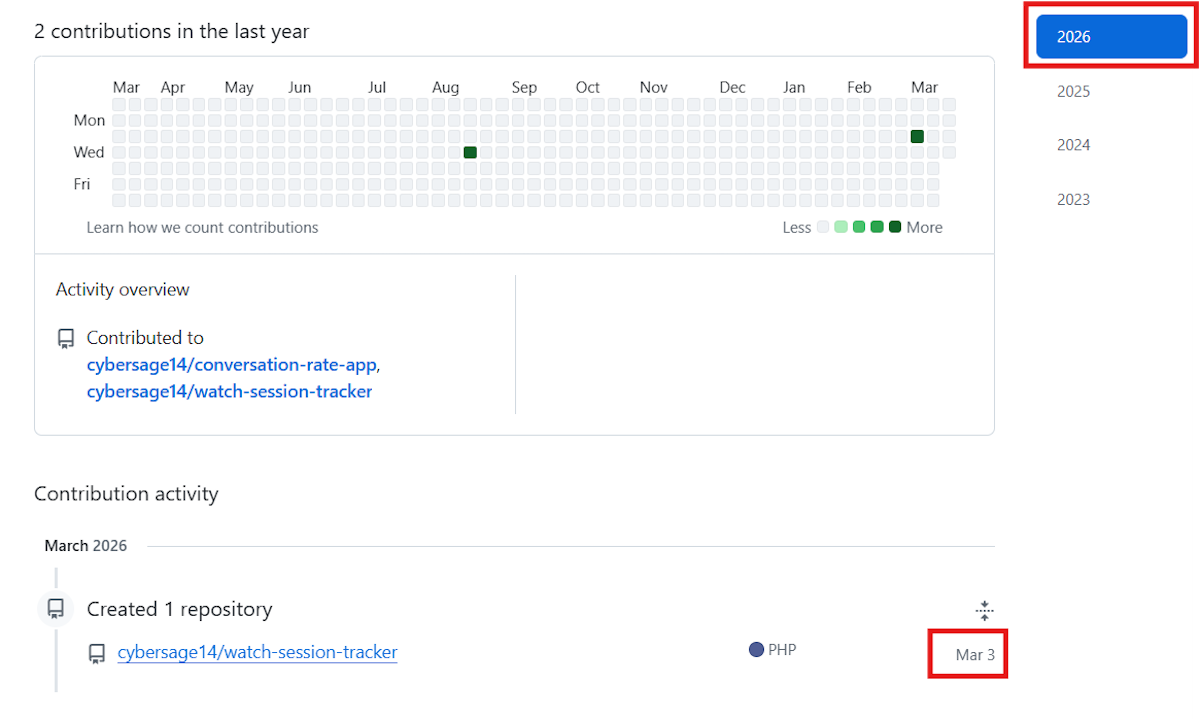
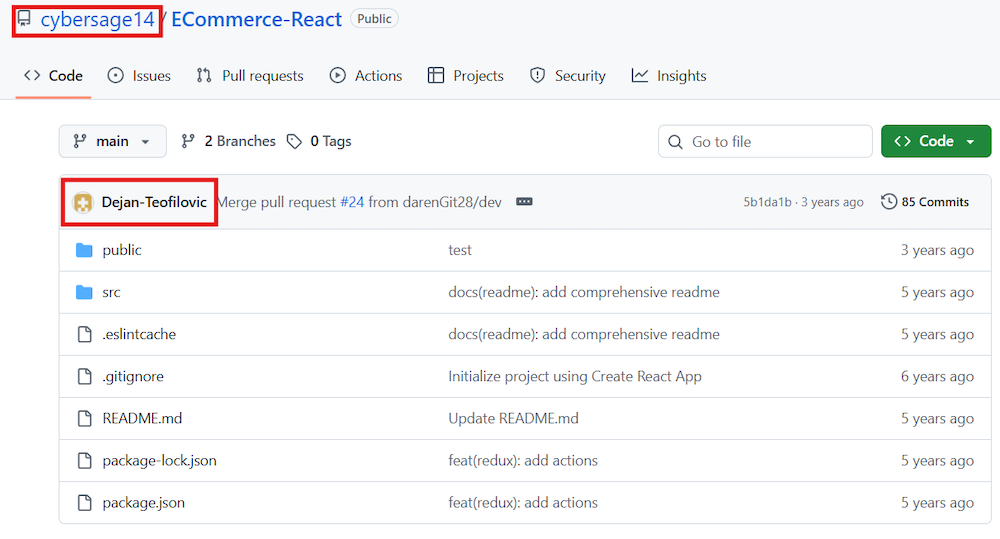
The account cybersage14 remained active through at least 3 March 2026. Examination of its repositories revealed multiple contributors and additional linked personas.
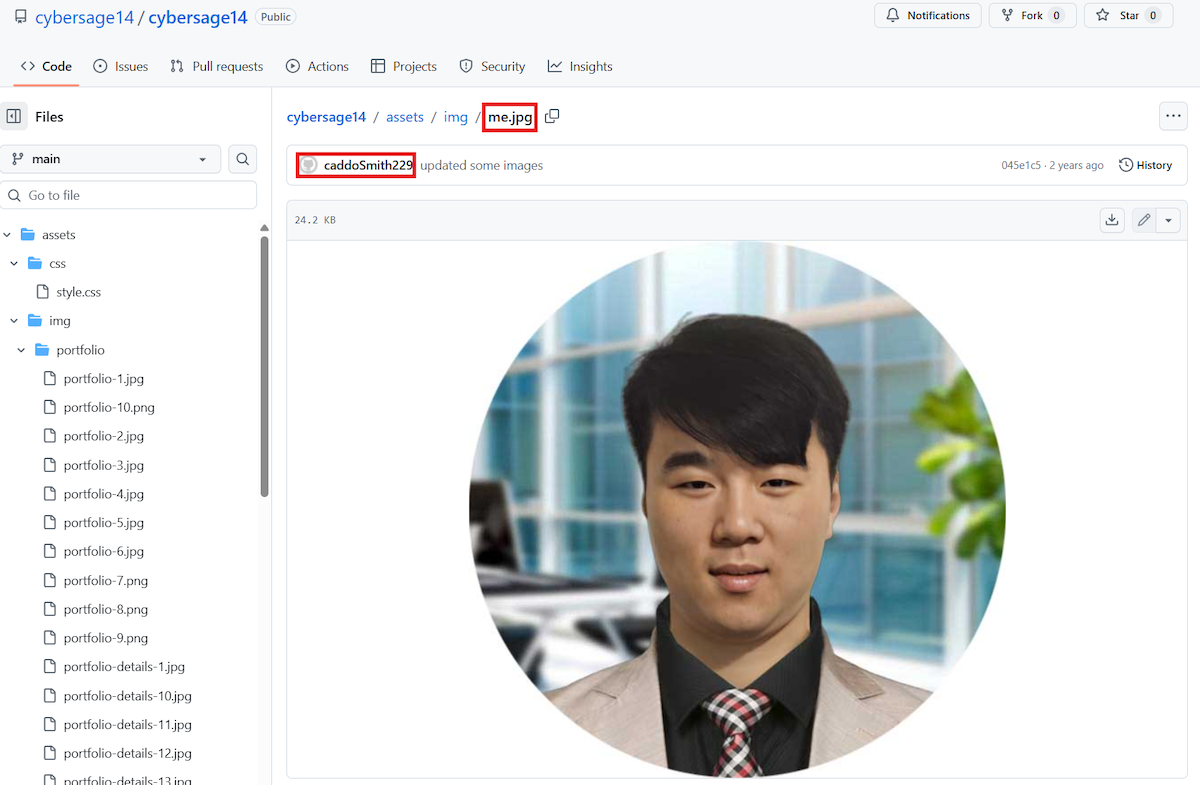
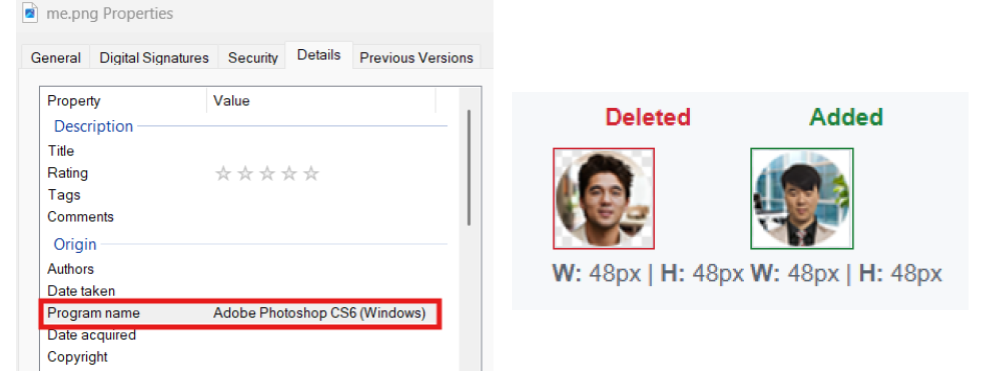
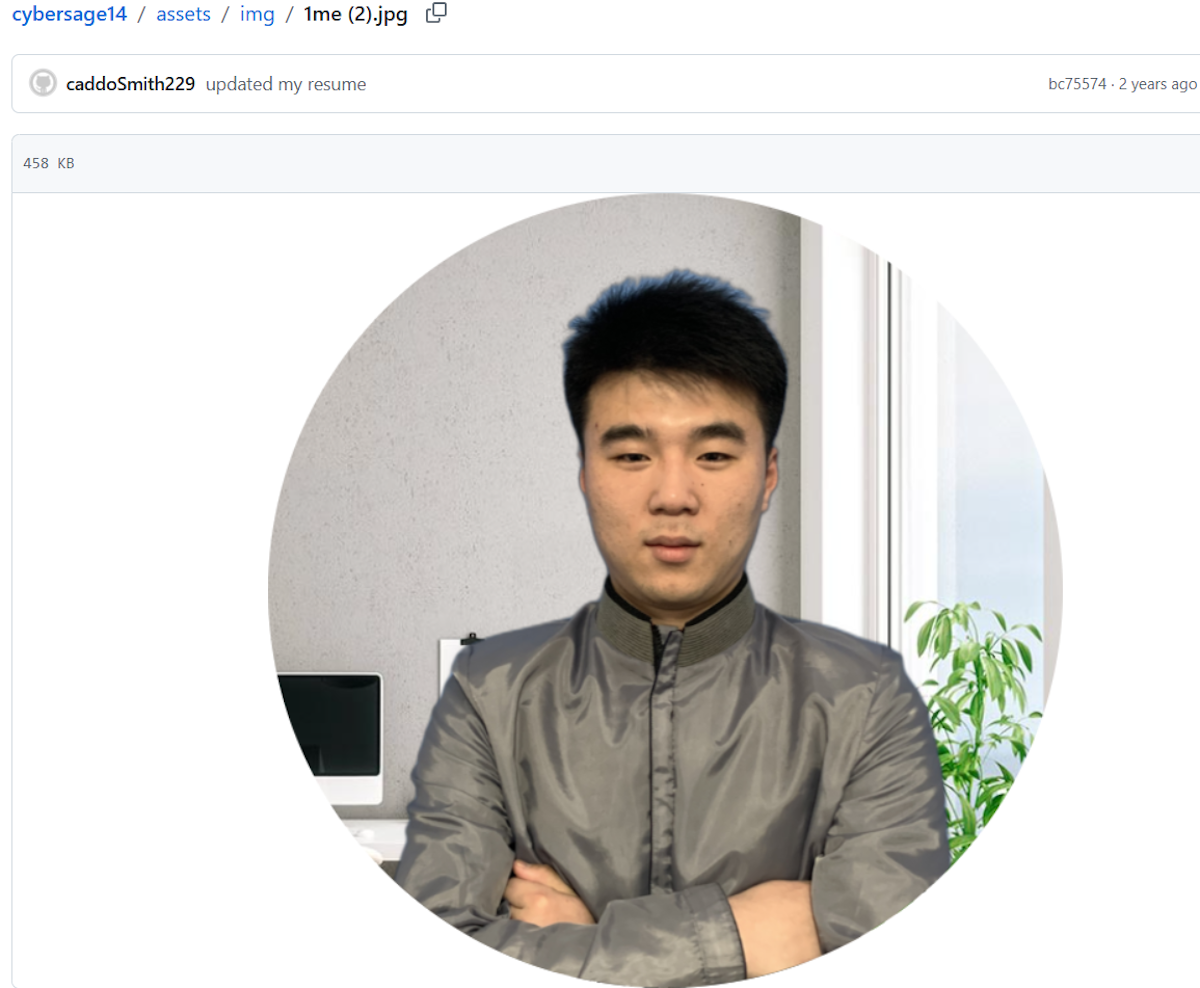
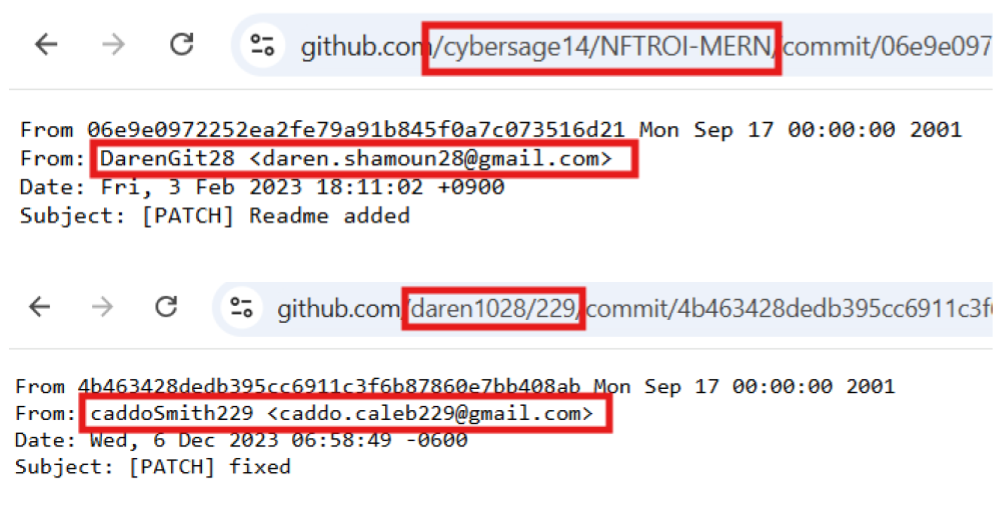
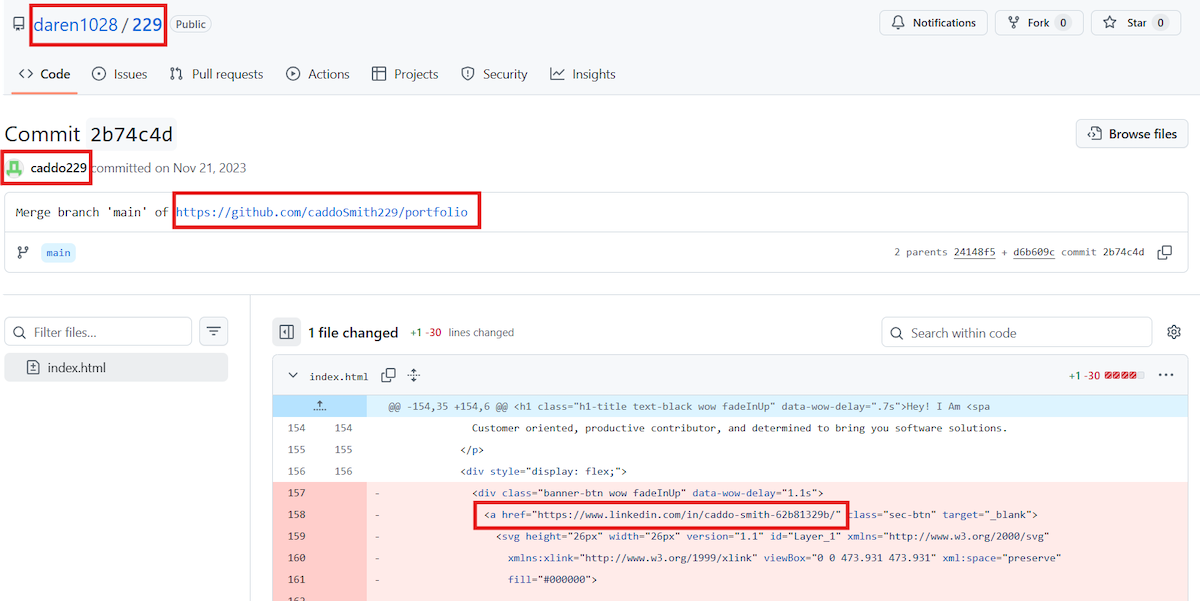
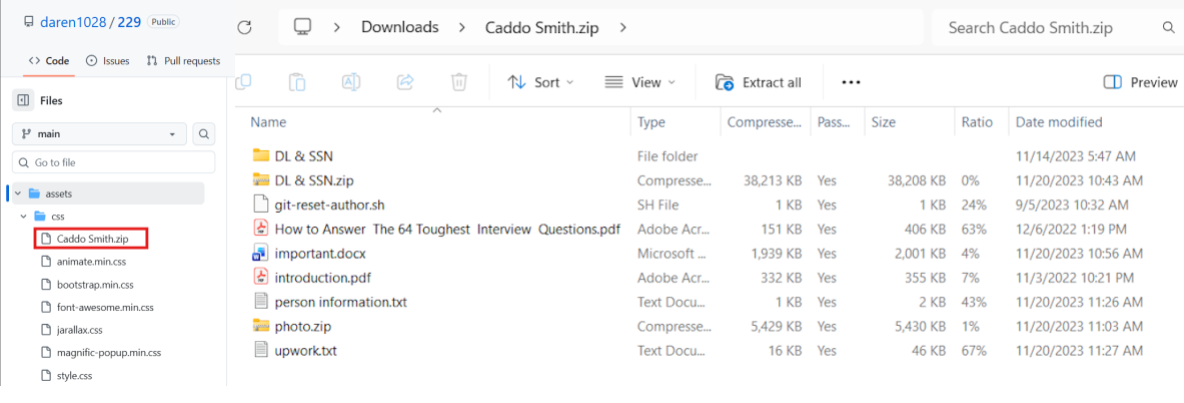
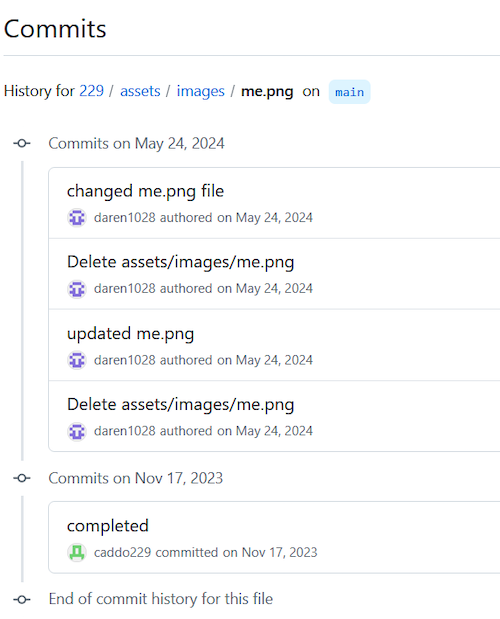
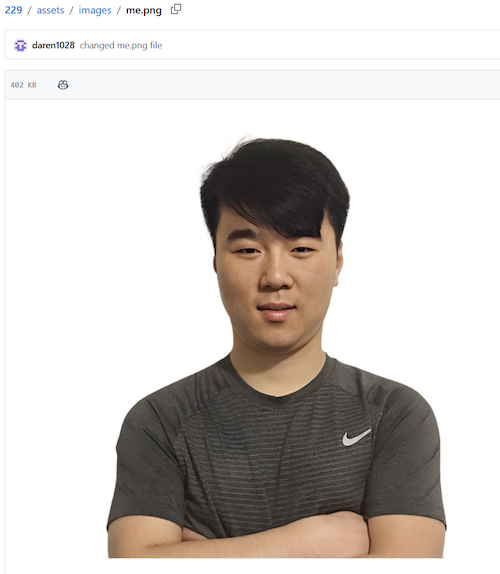
Within the cybersage14 repository, we observed commits by the user caddoSmith229, including changes to the avatar image. Embedded image artifacts indicated the use of Adobe Photoshop, consistent with manual editing rather than ordinary profile maintenance. Earlier repository history also contained a photograph more closely resembling an unedited source image.
We also identified another linked contributor, daren1028. Commit metadata exposed the email daren.shamoun28@gmail[.]com, and the repository content contained references that tied daren1028 back to the Caddo Smith persona. We also noted a naming pattern across other accounts such as adminGit71 and darentGit28, suggesting an internal convention that may have helped operators track or separate multiple identities.
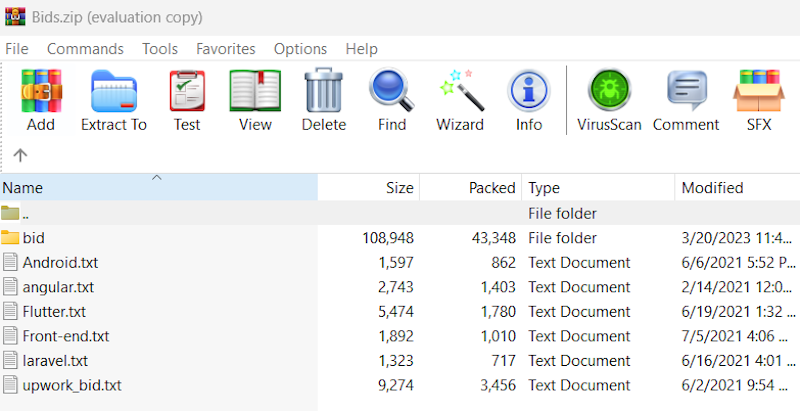
We then identified an additional account, caddo229, also associated with the Caddo Smith identity. This repository space contained a ZIP archive with data related to that synthetic persona.
There is even a new photoshopped image of Caddo Smith in a more casual style:
The significance of these findings is not merely that the personas were fake, but that multiple accounts were interacting inside a shared project and asset space, exposing common management, reuse of materials, and likely centralized handling.
Additional Personas and Identity Reuse
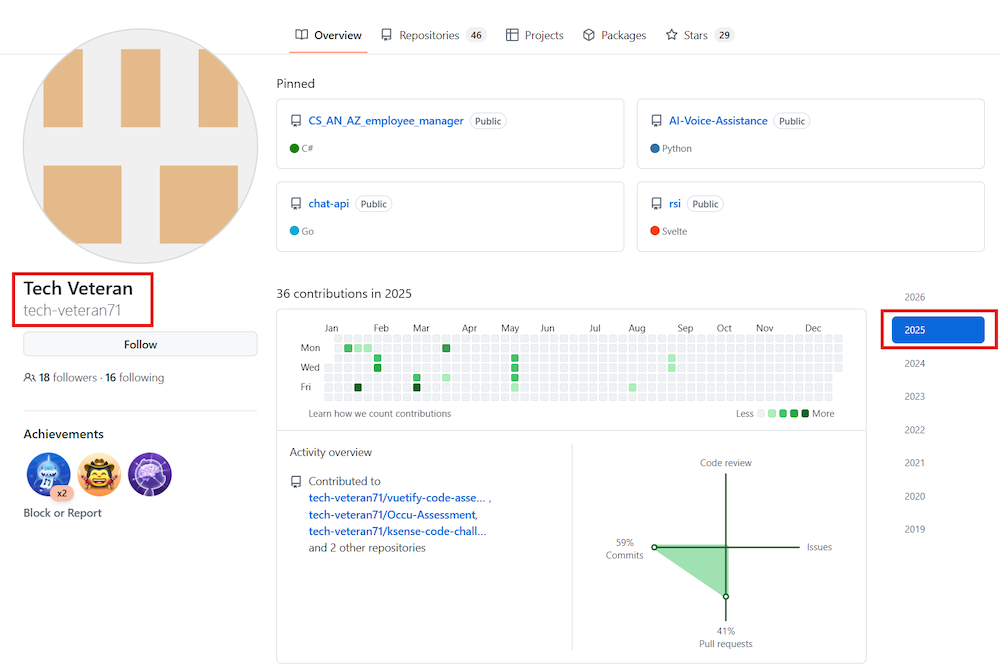
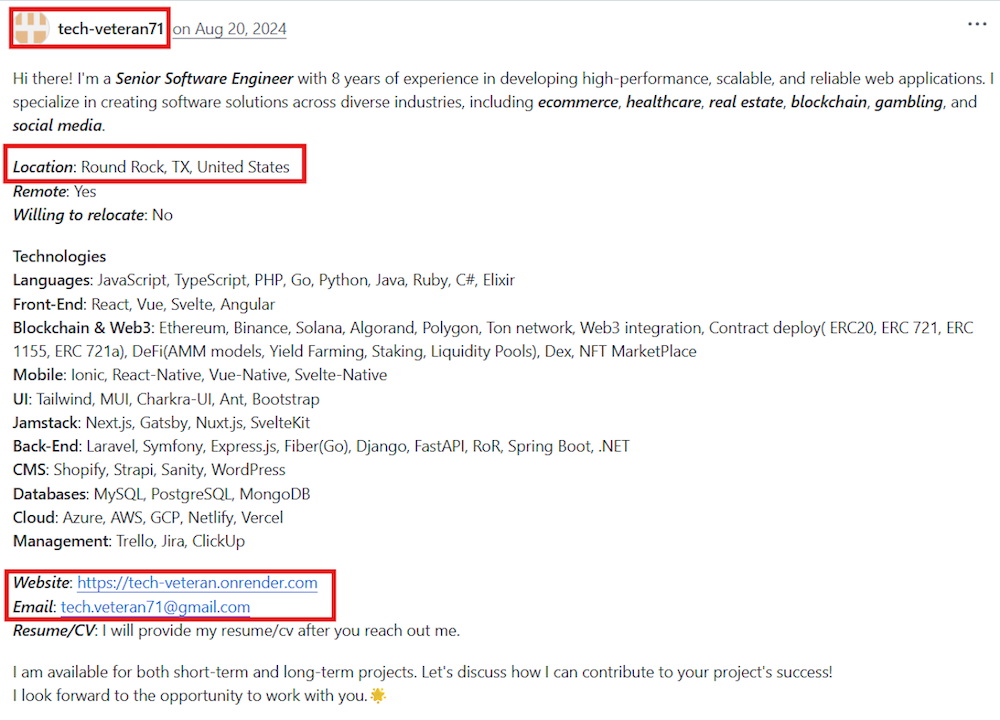
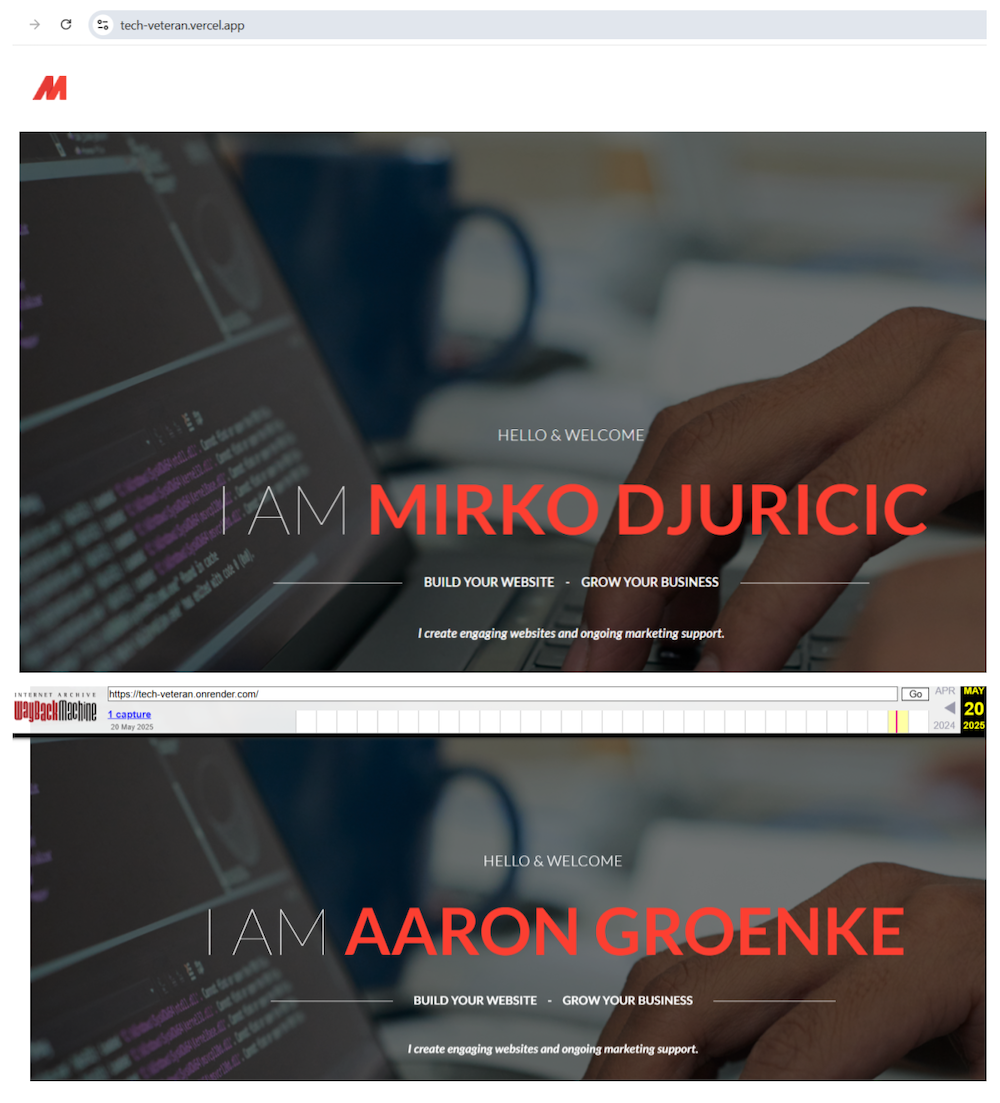
As the investigation expanded, we identified other developer personas – tech-veteran-71 – tied to the same ecosystem (he is one of the “cybersage14” followers). One associated profile used identical or near-identical projects and presented as a senior software engineer with eight years of experience. The linked portfolio and resume materials inconsistently used the names Mirko Djuricic and Aaron Groenke.
This pattern repeated across the cluster: stable technical content, interchangeable biographies, and reused infrastructure. In practical terms, the developers were not building unique personal histories for each persona. They were re-skinning a common pool of projects, resumes, and hosted pages.
Link to Upwork Account Acquisition
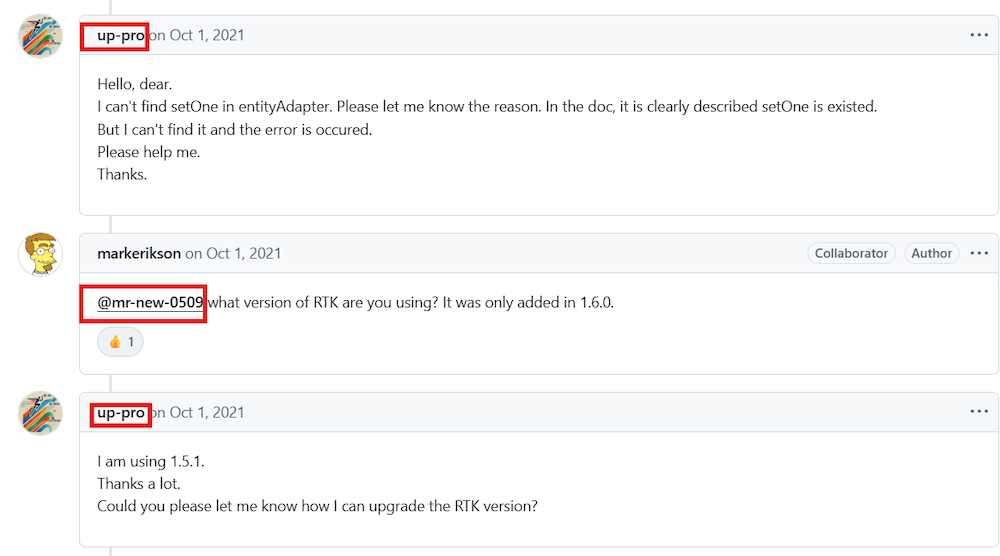
One of the pivotal findings in this research was the connection to 2021 activity related to verified Upwork accounts. While analyzing code and repository artifacts, we identified references to mr[.]new0509@gmail[.]com.
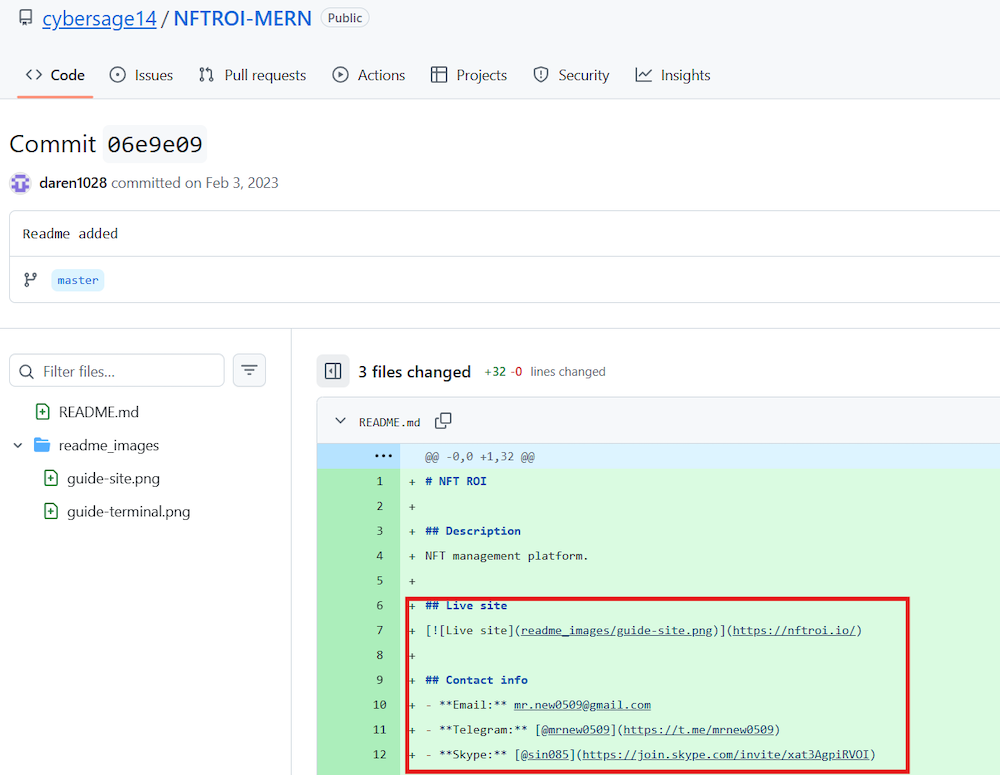
Figure 9. Connection to mr.new0509.
Using Group-IB DarkWeb forum monitoring, we found that the same contact had been seeking to buy verified Upwork accounts in 2021. This is operationally significant. Upwork is a major freelancing platform and a known vector for DPRK remote worker operations, whether to place synthetic contractors directly or to support laptop-farm-enabled employment schemes.
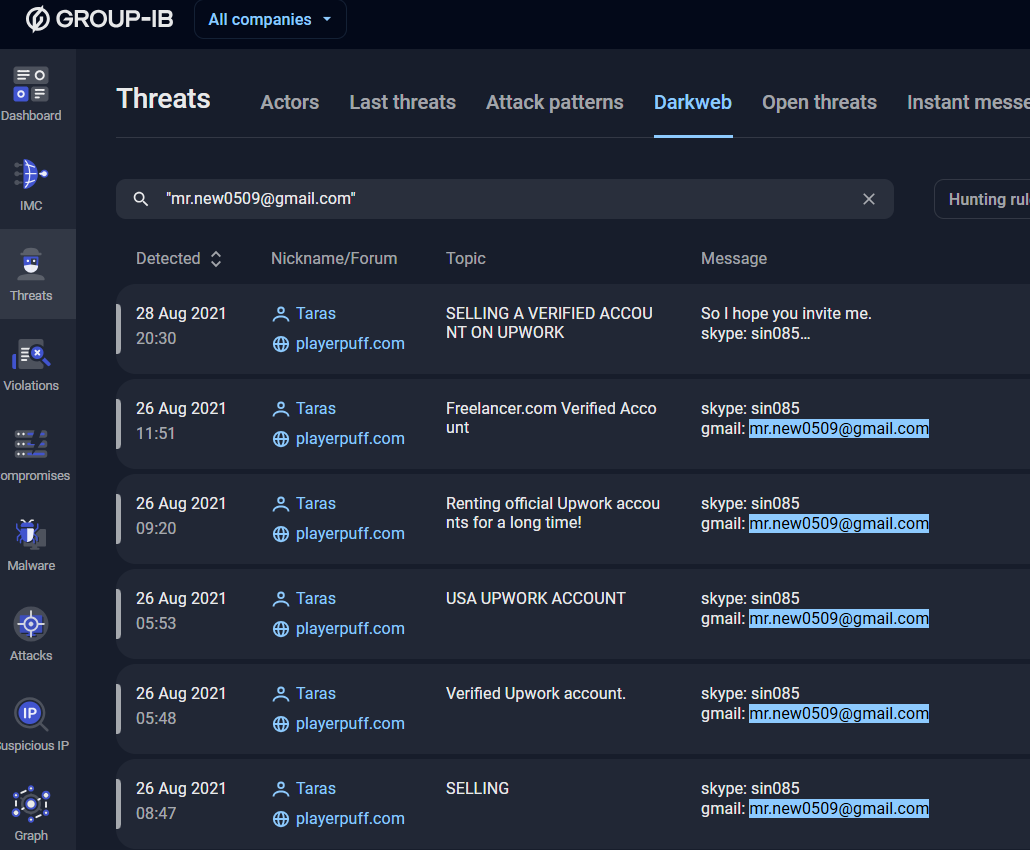
Figure 10. Screenshot from Group-IB Threat Intelligence platform (Darkweb monitoring section).
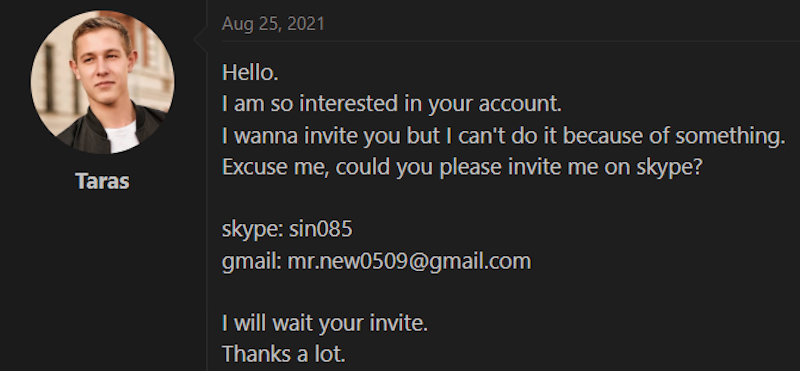
Figure 11. Screenshot from forum.
Another notable persona was Atsuo Koizumi, tied to the GitHub account up-pro, which had previously used the username mr-new-0509. The rename was visible through repository history and associated communications.
The persistence of the account into 2026 and its linkage to earlier infrastructure made it an important bridge between the public GitHub presence and older access-enablement activity.
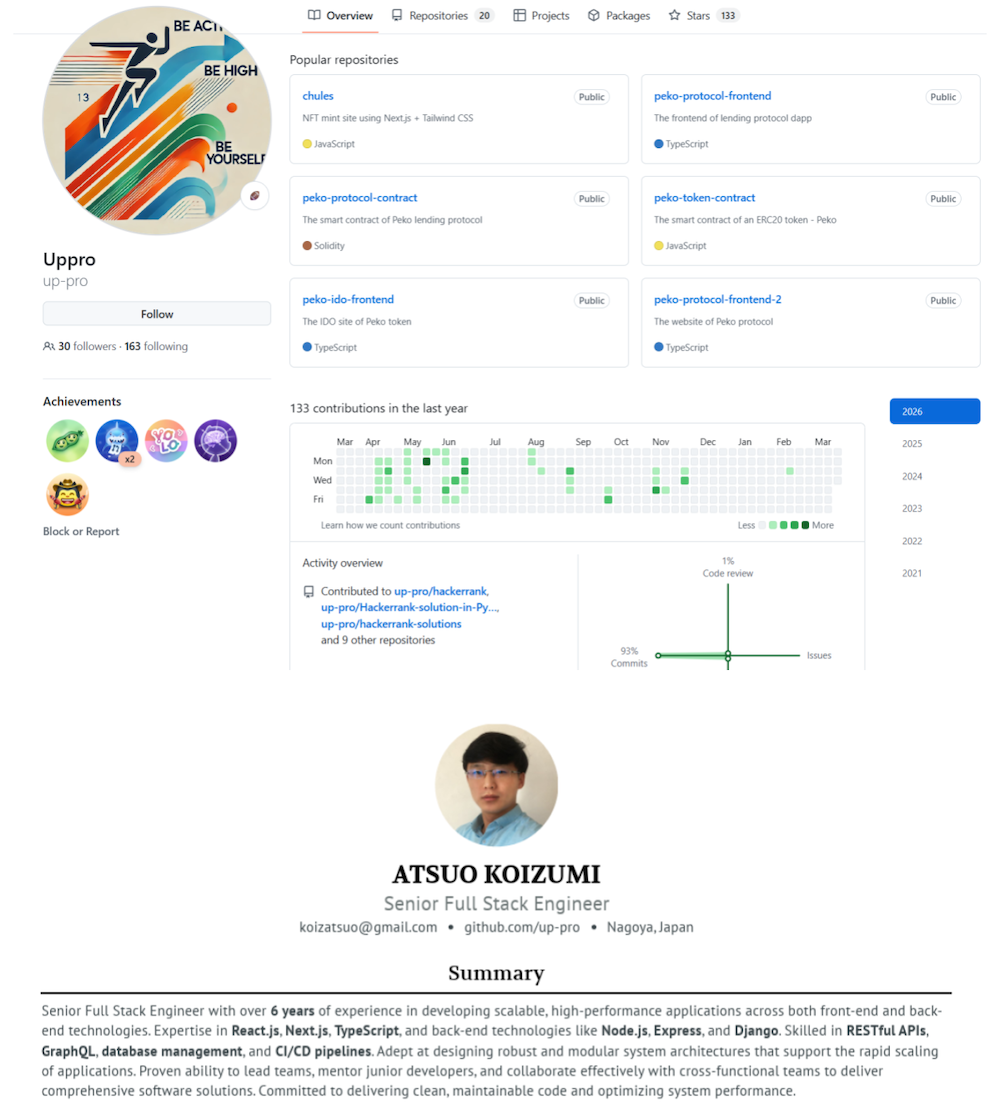
Figure 13. Information about account renaming and connected identity.
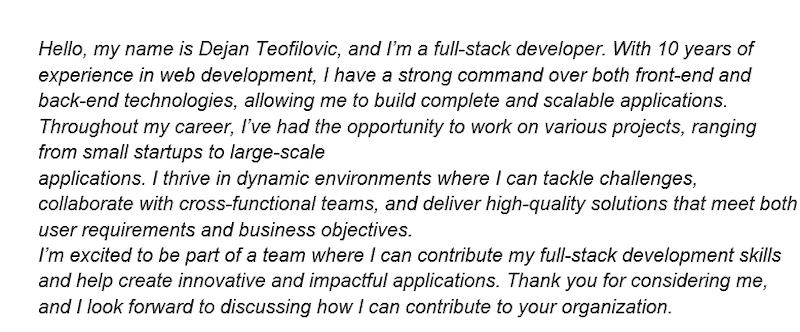
The Dejan-Teofilovic Branch
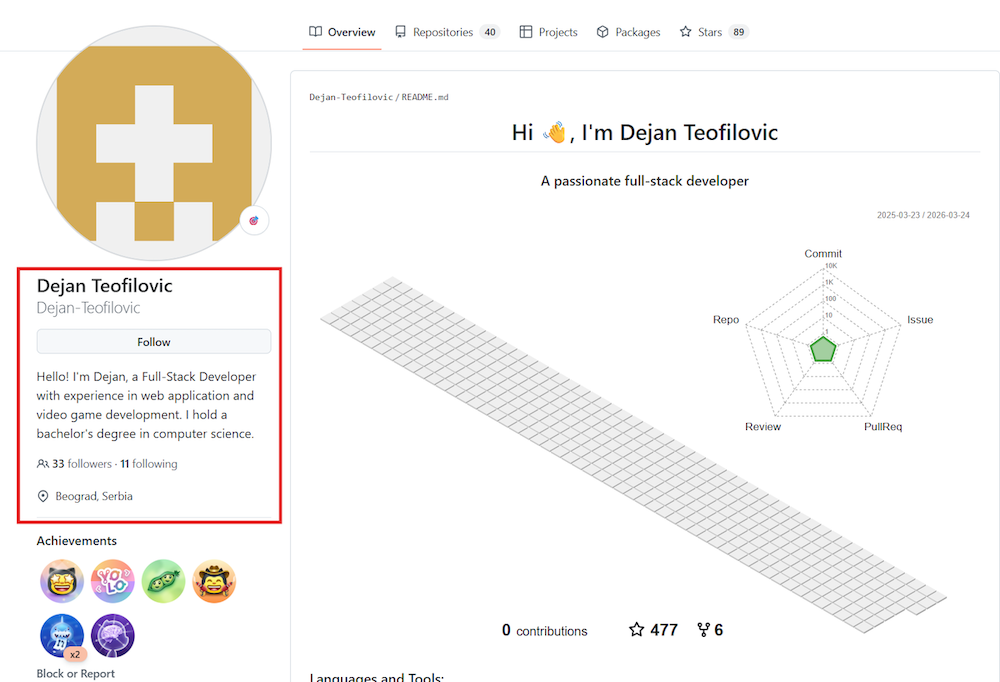
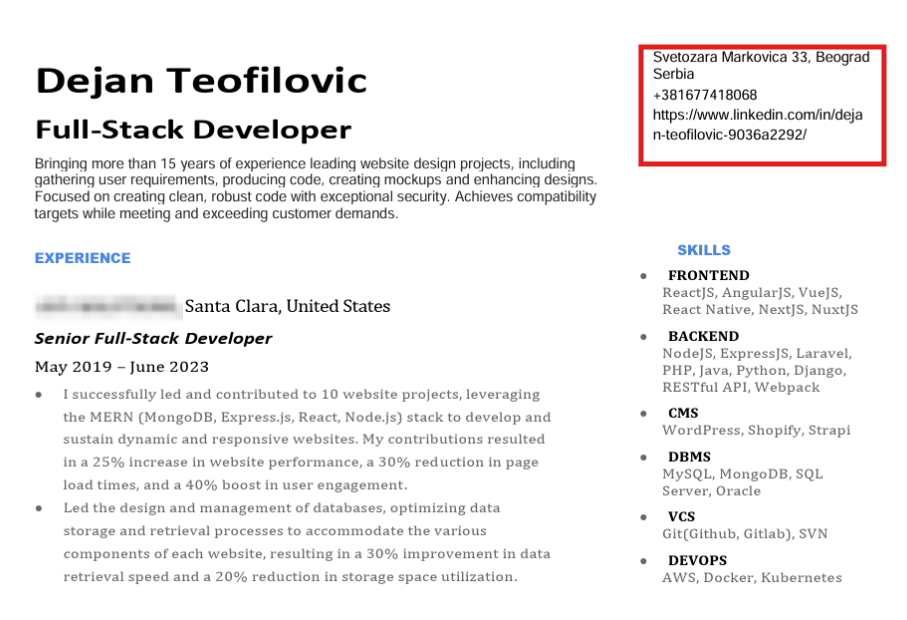
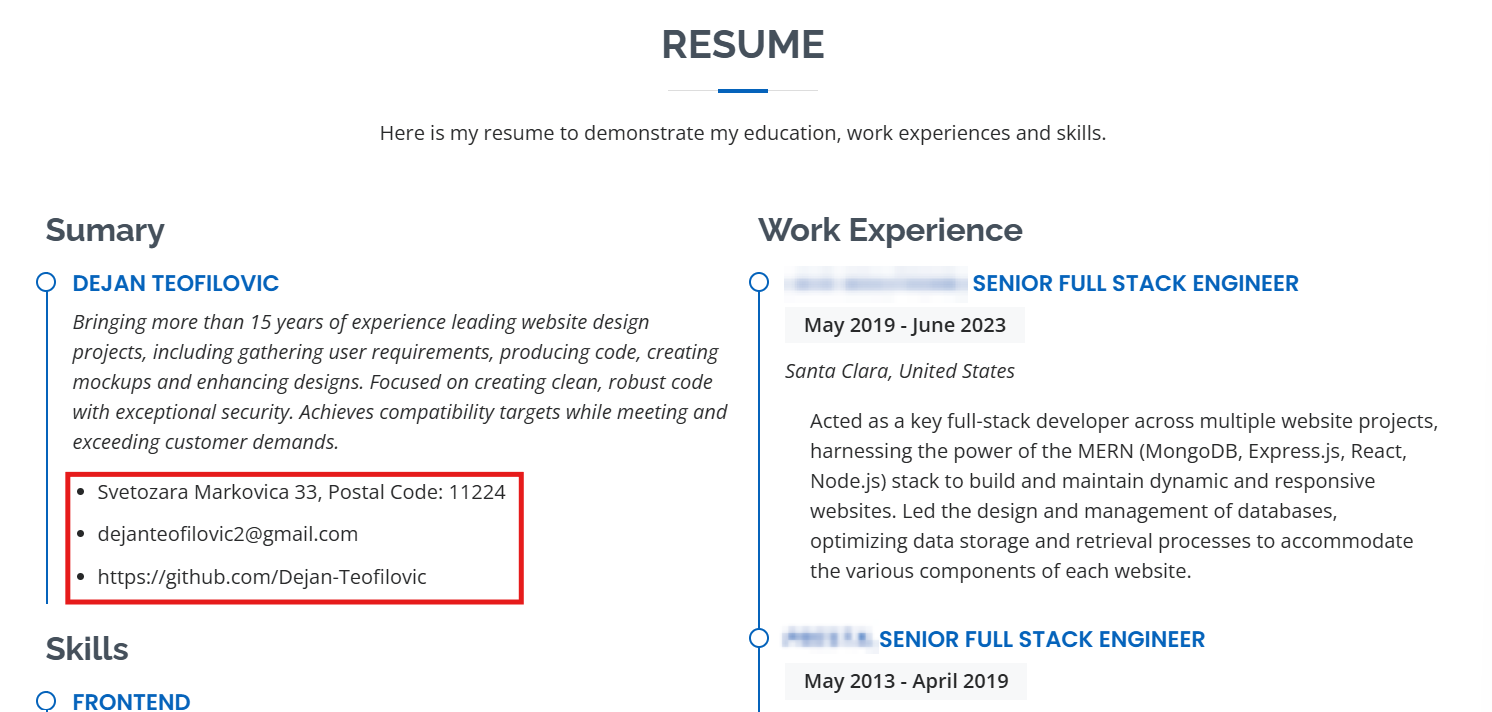
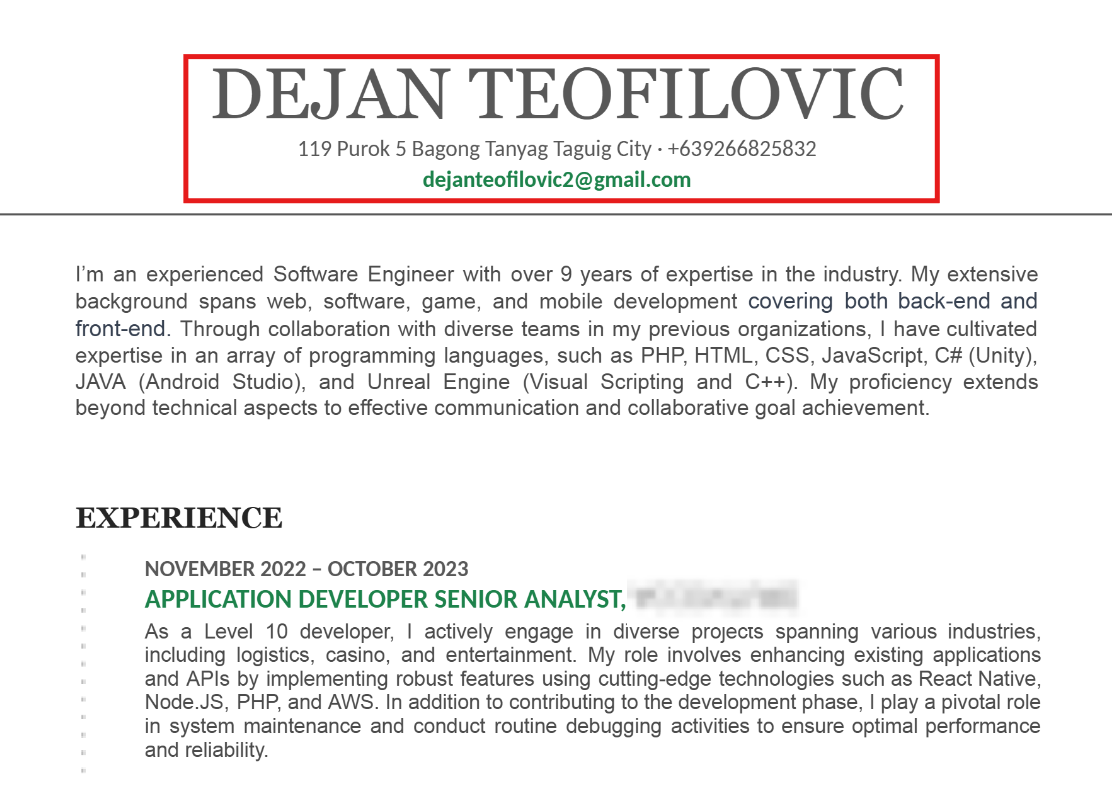
While analyzing code and repository artifacts of cybersage14, we identified references to “Dejan-Teofilovic”:
The GitHub profile presented Dejan Teofilovic as a full-stack developer with experience in web application and video game development, allegedly from Belgrade, Serbia. However, the surrounding resume and portfolio materials were inconsistent. In different places, the persona was presented as being located either in Serbia or in the Philippines, with different phone numbers and different professional histories.
This level of inconsistency is typical of synthetic identity maintenance under operational pressure. It suggests that the visible persona was adapted for different audiences or opportunities without full alignment across all public-facing assets.
We also located an image associated with the Dejan Teofilovic portfolio.
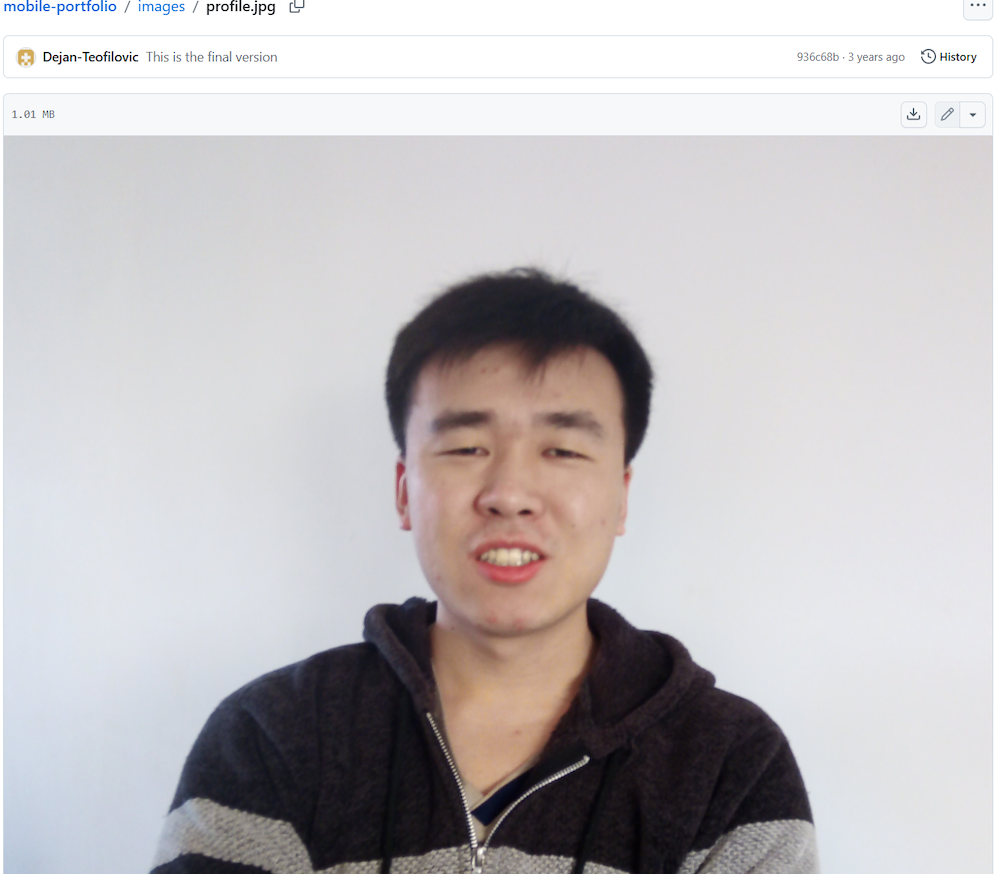
Figure 16. Photo of Dejan Teofilovic.
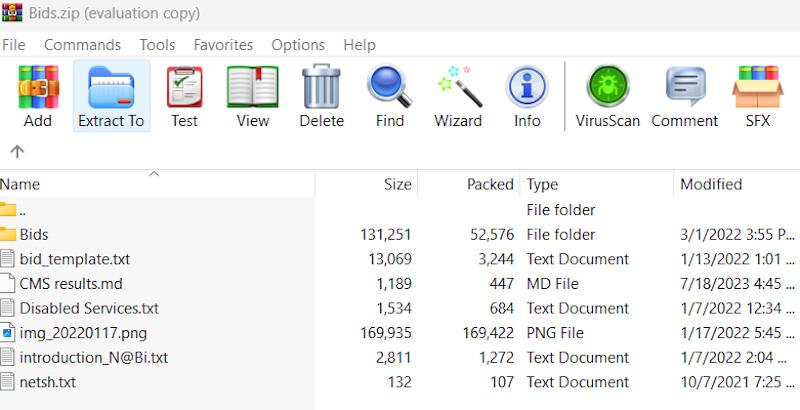
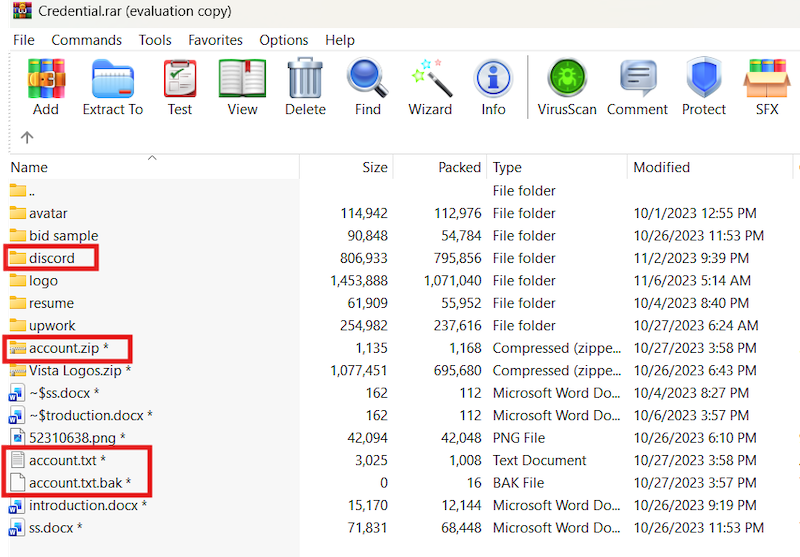
More importantly, we identified an archive left in a repository that contained synthetic identity materials associated with two personas:
- Dominic Williams
- DejanTeofilovic
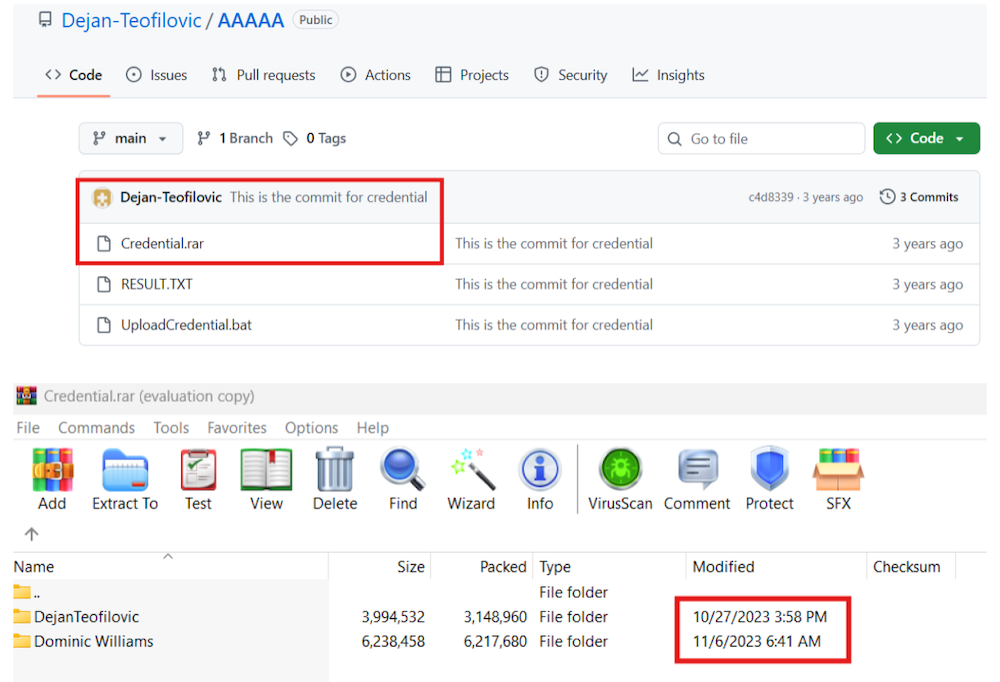
Figure 17. Information about archive, found in repository.
Persona Archive: Dominic Williams and Dejan Teofilovic
The archive was one of the most valuable finds in the investigation.
The folder for Dominic Williams contained a generated California driver’s license. The photograph matched imagery found elsewhere in the repositories, reinforcing the conclusion that this was a synthetic identity package rather than a standalone artifact.
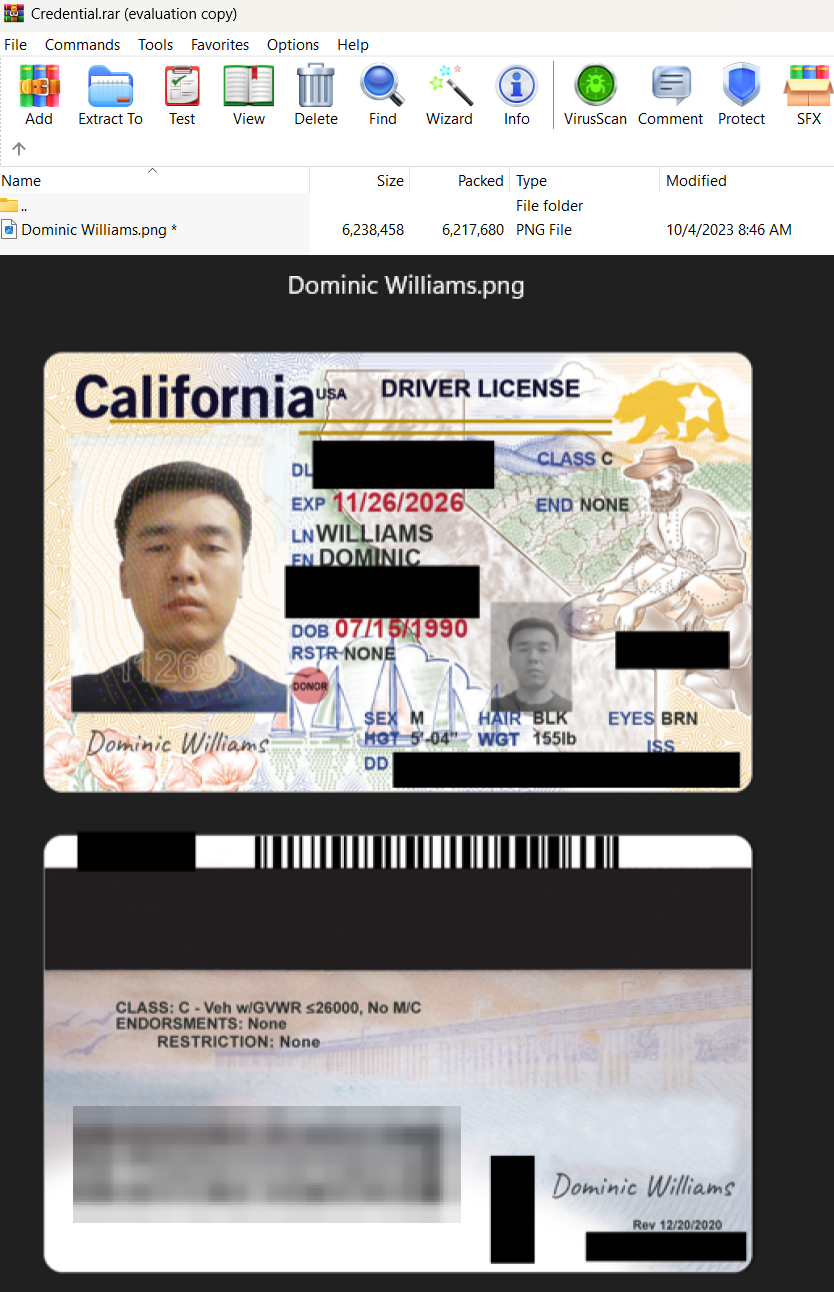
Figure 18 .Analysis of Dominic Williams folder.
The DejanTeofilovic folder was much more extensive and contained what appeared to be a more complete profile set. In our assessment, this reflects a hierarchical working model in which operators simultaneously maintain multiple remote worker profiles at different stages of maturity. Some personas appear minimally staged, while others are fully developed and ready for active job applications.
This archive also contained materials related to job search operations, account access, and service usage. In practice, it exposed not only who the persona was pretending to be, but how the persona was operationalized.
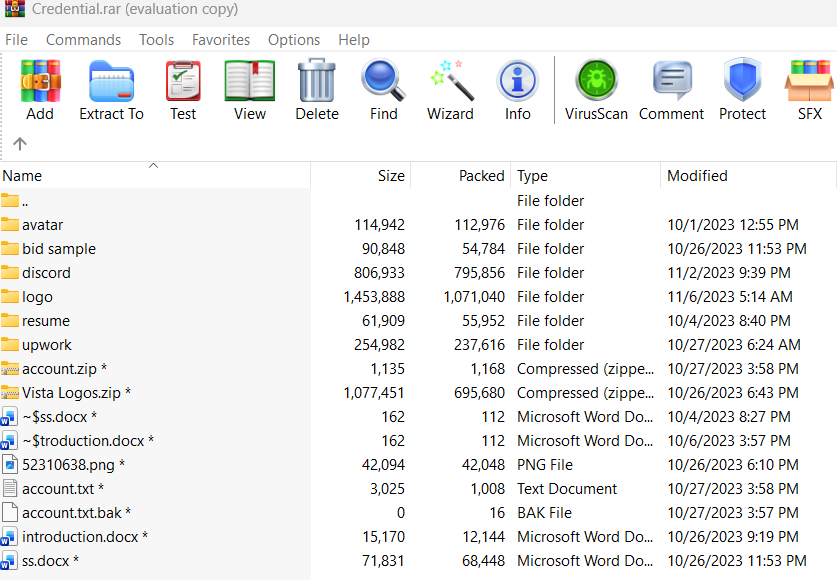
Figure 19. Listing files from of Dejan Teofilovic folder.
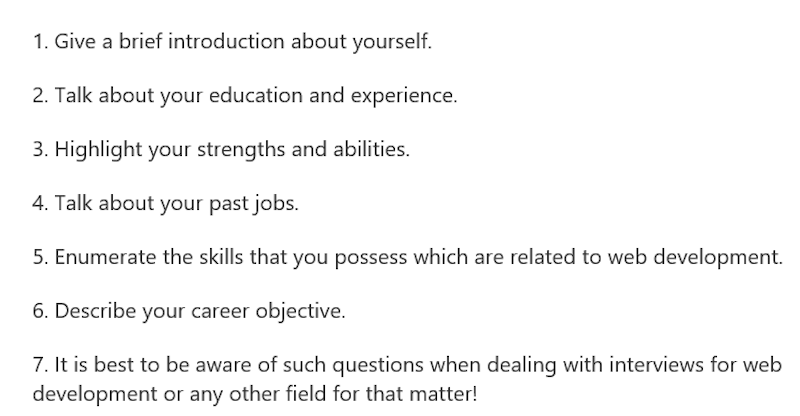
AI-Assisted Job Application Workflow
We found guidance materials and sample wording for responding to employers, including structured examples of how to present technical qualifications in a way that would maximize the chance of receiving an interview.
We also observed direct evidence that ChatGPT was used to help produce more natural-sounding English responses.
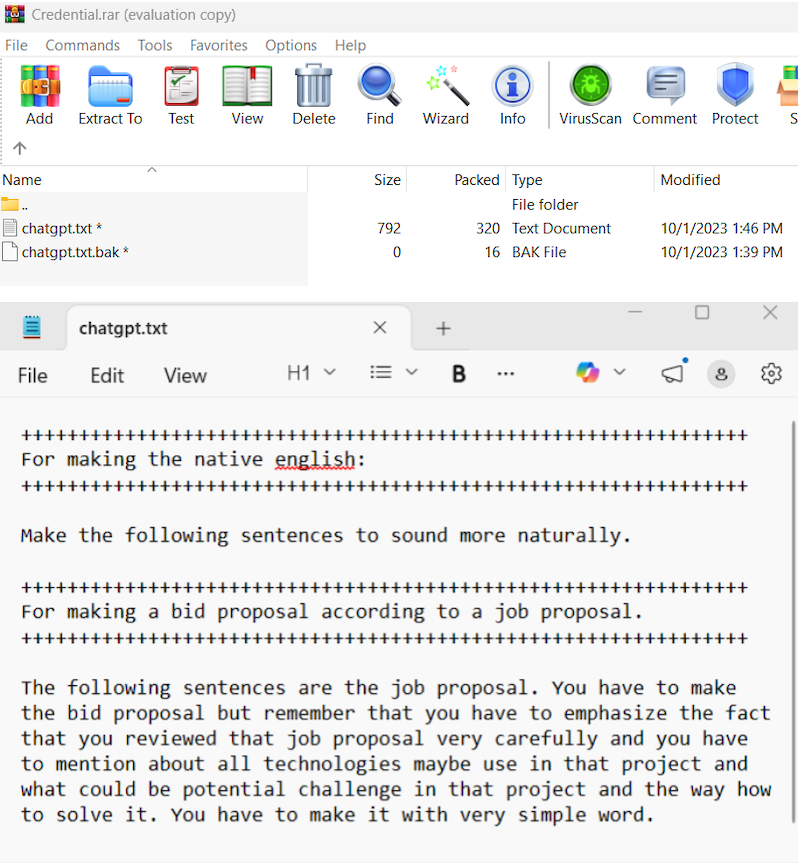
Figure 21. ChatGPT prompts found within the folder.
All responses to job postings were preserved. Based on the structure and contents of the files, it is likely that the original drafts were first generated in ChatGPT chats and later copied into a separate document that served as a centralized summary and response bank. While Group-IB researchers cannot verify the full workflow end-to-end, but the archived materials strongly suggest a process in which generated responses were collected, curated, and reused over time.
The responses varied depending on the target role, prior communication with the employer, and the perceived fit of the persona for the position.
- In some cases, the applicant stated that their skills were an exact match for the proposed role or project and argued that the employer should not waste time reviewing other candidates. These responses were clearly designed to present the persona as a strong and immediately viable choice.
- In other cases, the wording suggests that either an initial conversation had already taken place without a positive outcome, or that the operator understood that the claimed skill set might not withstand closer scrutiny. In such responses, the applicant proposed using an existing code base, presenting it as a way to accelerate development and reduce delivery time. This is an important detail, as it shows an adaptive approach: when direct qualification was less convincing, the value proposition shifted toward speed and reusable development assets.
- A separate group of responses focused less on direct self-promotion and more on proposed tooling, technical approaches, project challenges, or possible development opportunities. In these cases, the applicant attempted to demonstrate relevance by discussing the target project in practical terms rather than only describing personal experience.
In Group-IB assessment, these different response types were likely generated from pre-prepared prompts combined with project-specific information related to the vacancy the future worker intended to target. The presence of structured prompt material in the archive supports this interpretation.
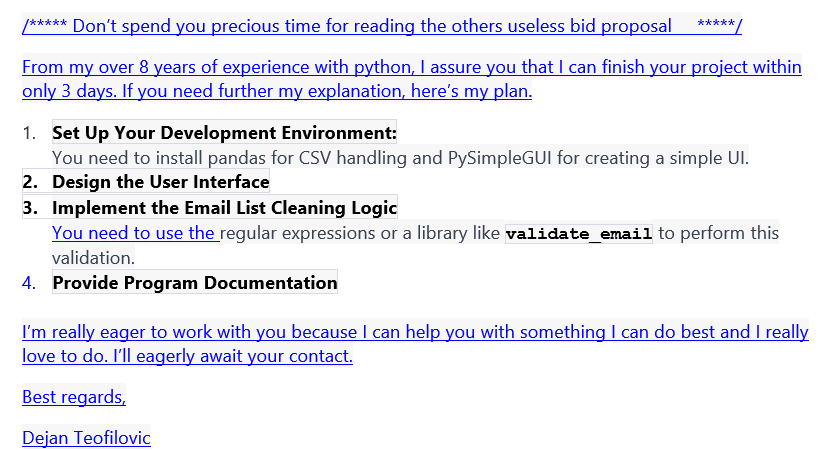
Figure 22. One of the responses listed in folder.
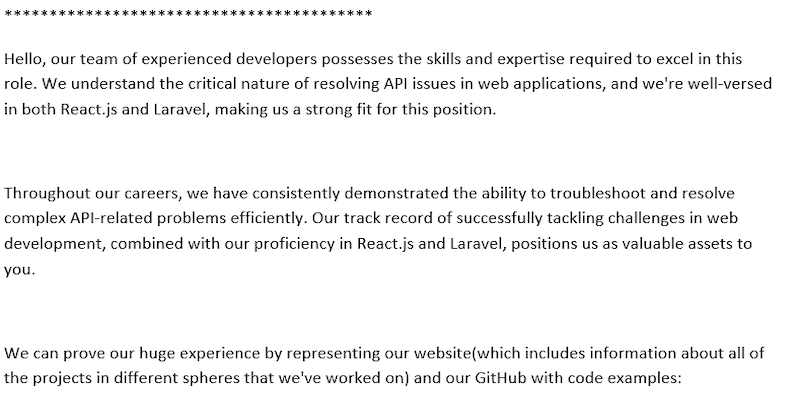
Other collections of responses found in the same archive showed additional templating and “persona” variation.
- Different worker names were used across the materials, including Sergei, David, Michael, Yilizati, and Alejandro. In our assessment, this was likely done to align the persona more closely with the geography or expectations of the market being targeted.
- In some cases, the operators presented themselves not as individual freelancers but as a development company. This likely served to create the impression that multiple developers would be assigned to the project, which could increase employer confidence by suggesting faster delivery and broader technical coverage.
- We also observed internal grouping of response templates by category, for example by skill set or by the platform where the application would be submitted. This indicates a more systematic approach to application management rather than ad hoc drafting.
An additional notable detail is that the sample response base appears to date back to 2021, based on the modification timestamps of the text files. This indicates that the response library and supporting application workflow had been in place for several years.
Synthetic identity access and services
The archive also stated that the Dejan Teofilovic account was likely acquired from an Upwork account broker. We would like to stress this point carefully: this conclusion is based on the contents of the file itself, which explicitly indicated broker involvement. Group-IB has not independently verified the broker transaction beyond what is stated within the archive files.
If we examine the list of services and account types referenced in the archive, we can better understand which tools, programs, and online services were used to create and maintain the appearance of a real, functioning person. At the same time, it is important to state the limits of our visibility: we only have the list of accounts and services as recorded in the files contained in this archive. We do not know whether these accounts remain accessible today, whether all of them were actively used, or the exact manner in which they were operated. All identified information within this report have been passed on to the organizations concerned.
The service stack referenced in the archive included the following:
- Gmail – email service used for account registration, communications, and identity support.
- AnyDesk – remote desktop application. The file listed three AnyDesk accounts. In this context, such a tool could support remote access to devices or sessions associated with the synthetic identity.
- Payoneer – global online payment solution used to receive cross-border payments.
- Wise – international money transfer service.
- PayPal – online payment service.
- Upwork – freelancing platform.
- Freelancer – freelancing platform.
- AirDroid – mobile device management suite. One note in the document stated that it was used “for phone verification,” which is a notable detail given the importance of phone validation in creating and maintaining platform accounts.
- LinkedIn – professional social network.
- GitHub – developer platform used to host code, portfolios, and visible technical activity.
- Heroku – container-based cloud Platform as a Service (PaaS) that enables developers to build, run, and scale applications in the cloud.
- Oracle – company specializing in database software, cloud-engineered systems, and enterprise software products. In this context, the reference likely relates to access to Oracle-hosted or Oracle-provided infrastructure or services, although the exact use case is not stated in the files.
- Pusher – hosted real-time API service.
- OpenAI – artificial intelligence research and deployment platform providing access to models such as GPT, DALL·E, and Codex.
- Skype phone – Skype service used for voice and video calls. The service was retired on 5 May 2025, but at the time reflected in the archive it appears to have been included as part of the communications setup.
- Discord – Instant Messenger. They communicate about work and search job opportunities in channels
- Telegram – Instant Messenger. They communicate about work and search job opportunities in channels
- Bank card and account – the files indicated a checking account and possibly an associated bank card issued by one of the banks.
Taken together, this list provides a practical view of the support layer behind a synthetic worker identity. It covers the main functions required to maintain a plausible remote worker presence: communications, remote access, social and developer profiles, payment receipt, financial operations, hosting, and AI-assisted content generation.
Conclusion
The findings presented in this report reinforce that DPRK IT worker operations remain a persistent and significant threat. This activity should not be viewed as isolated fraud or a limited set of fake freelancer profiles. It is part of a broader operational model that enables revenue generation, sanctions evasion, and access into foreign companies through legitimate business processes.
One of the most important aspects of this threat is its reliance on trusted platforms and trusted accounts. Rather than depending solely on traditional intrusion methods, DPRK-linked operators exploit the credibility of GitHub, LinkedIn, Upwork, Freelancer, payment services, portfolio platforms, and other legitimate services to build convincing professional identities. Once such accounts have accumulated history, reputation, and apparent legitimacy, they become much more effective tools for bypassing scrutiny and entering hiring, contracting, and onboarding pipelines.
The evidence in this investigation also highlights the scale of the problem. The issue is not limited to a single false identity. The archived materials, reused repositories, standardized response templates, parallel personas, and preserved access data all point to an operational model capable of supporting multiple synthetic workers at the same time. This makes the threat resilient. Even when individual personas or accounts are exposed, the underlying workflow can continue, with identities replaced, adjusted, or redeployed across different platforms and target environments.
Organizations should therefore approach this threat not only as a hiring fraud issue, but as a broader access, trust, and insider-risk challenge. DPRK IT workers are most effective in environments where remote hiring, limited verification, and low day-to-day engagement allow synthetic identities to operate without meaningful scrutiny. Where organizations build stronger familiarity with candidates and contractors, apply more rigorous validation, and maintain closer oversight during onboarding and project work, the operational space available to such actors becomes more limited.
Recommendations
Defending against this global threat requires collaboration across HR, Finance, and IT Security. Below are critical mitigations organizations must adopt:
Human Resources & Talent Acquisition
- Video Interviews: Require video for all remote interviews and consider asking candidates to disable background and face filters, which can hide AI manipulation. Be highly suspicious of candidates who refuse to appear on video or claim “broken cameras”.
- Resume & Identity Verification: Check for cloned resumes or duplicated contact information. Utilize multiple verification tools, including government ID checks, address verification, and OFAC sanctions screening. Review submitted photos for signs of AI generation or reuse.
- Rapport-Building: Use casual, rapport-building questions to subtly verify background details, location, and education during interviews to spot inconsistencies. Be mindful that threat actors might claim to reside in countries completely disconnected from their actual location.
Banking, Payroll, and Finance
- Licensed Banking Only: Prohibit salary payments to pooled accounts, e-wallets, or remitters like Payoneer, Wise, PayPal, or Cash App. Only pay salaries into licensed, deposit-accepting bank accounts.
- Validate Accounts & IDs: Confirm that the name of the employee in the HR system perfectly matches the name on their bank account. Require new hires to provide a validated government tax ID (like an SSN or NIN).
- Monitor Changes: Require dual authorization for any banking changes and strictly monitor for last-minute requests to change bank account information or shipping addresses.
Cybersecurity & IT Monitoring
- Hardware & Access: Restrict the use of personal unmanaged devices for corporate resources. Implement the principle of least privilege, ensuring new remote employees only have network-layer access to exactly what they need.
- Threat Hunting: Monitor for the use of simulated activity tools. Watch for IP-based keyboard, video, mouse (KVM) devices which actors use to remotely access corporate laptops.
- Behavioral Analytics: Flag new hires who avoid typical interactions (like meetings, Teams, or Outlook communication) and exclusively focus on accessing code repositories or sensitive internal data. Look for anomalous access to code repositories, especially massive cloning activities outside standard working hours.
Frequently Asked Questions (FAQ)
What is the ultimate goal of DPRK IT workers?
Their primary motivation is generating illicit revenue for the Democratic People’s Republic of Korea (DPRK) and its weapons programs. Secondary motives include gaining access to sensitive corporate data, source code, and intellectual property.
Are these attacks only targeting US or Western companies?
No, this is a global issue. Threat actors actively masquerade as residents of a wide variety of countries, including Argentina, the US, Serbia, Japan, Germany, Denmark, Singapore, Ukraine, Finland, Sweden, and the Philippines, allowing them to infiltrate organizations worldwide.
What are the common red flags to watch out for during the interview stage?
Red flags include a reluctance to appear on camera, inconsistent English fluency that fluctuates during the call, surface-level technical knowledge despite an impressive resume, and unexplained background noise resembling a call-center environment.
How do these fraudulent candidates manage to pass technical assessments?
They heavily utilize AI tools to generate real-time responses and code snippets during technical assessments. In some cases, It has been detected that they hired some remote workers who passed interviews for them or one of their own tech specialists answered while presenting another person on screen.
How do these threat actors circumvent traditional banking controls to receive their salaries?
They often request prepayments or attempt to route their salaries through online payment solutions, money service businesses (MSBs). In the case where they hired a real person who acted as a job seeker, then upon receiving the job, he transferred % of salary from his real bank account to the DPRK IT accounts.
How do these remote workers handle corporate hardware if they are not physically located in the country?
Since the actual operators are located overseas, they rely on domestic “laptop farms” to receive corporate devices – people they hire as remote workers. Facilitators at these farms connect the laptops to IP-based KVMs or remote access tools, allowing the worker to access the corporate network securely. A major red flag during the onboarding phase is a last-minute request to change the shipping address just before the laptop is dispatched, or an attempt to redirect the courier after shipment.
What is their typical employment lifespan?
Once hired, their lack of genuine engagement often leads to them being flagged for poor performance around the 6 to 8-week mark. However, if a synthetic worker manages to remain employed for about a year, the operators will heavily leverage that legitimate corporate experience as a verified reference to secure future roles.
MITRE ATT&CK
| T1589.001 | Reconnaissance: Gather Victim Identity Information |
| T1585.001 | Resource Development: Establish Accounts -> Social Media Accounts |
| T1588.007 | Resource Development: Obtain Capabilities -> Artificial Intelligence |
| T1199 | Initial Access: Trusted Relationship |
Indicators of Compromise (IOCs)
Group-IB advises organizations to utilize these indicators of compromise primarily for investigative hunting rather than for strict blocklisting. Because DPRK operatives frequently rely on purchased or compromised accounts to support their infrastructure, these indicators might not be exclusively malicious and could belong to legitimate users or revert to their original owners.To minimize false positives, we have refined this list to include only email addresses where we have verified the threat actors’ active control or their direct use of the identity across multiple platforms.
Portfolio sites
- tech-veteran.onrender[.]com
- chules.vercel[.]app
- chules-git-main-mr-new-0509.vercel[.]app
- healer1064.github[.]io
- chase-allen.netlify[.]app
- naruhito-kaide.netlify[.]app
- tech-veteran.vercel[.]app
- atskoi.netlify[.]app
- felix-moore.netlify[.]com
- leomasaki.vercel[.]app
- robertlopez9216.github[.]io
- caddo-smith.vercel[.]app
- skydev-hub.github[.]io
- william-gilbert.netlify[.]app
- tommykallio.vercel[.]app
- starmastar1126.github[.]io
- chules-mr-new-0509.vercel[.]app
- jacob-rd.netlify[.]app
- portfolio-k8jev6vlb-dejan-teofilovics-projects.vercel[.]app
- caddo-portfolio.vercel[.]app
- masculus.vercel[.]app
- naruhito-kaide.netlify[.]app
Email Indicators
- aaron.groenke111391@gmail[.]com
- aaron.groenke111391@outlook[.]com
- afteryou725@gmail[.]com
- aim1005achieve@gmail[.]com
- Bluxboy80@gmail[.]com
- bremaster0806@gmail[.]com
- bruno.jackson.dev@gmail[.]com
- caddo.caleb229@gmail[.]com
- caddo.smith0229@gmail[.]com
- chase.allen.tech@gmail[.]com
- cliffahleongtech@gmail[.]com
- cloudstrifeinfinite@gmail[.]com
- colleen.cl.hillyard@gmail[.]com
- daren.shamoun28@gmail[.]com
- dejanteofilovic2@gmail[.]com
- dejanteofilovicup@gmail[.]com
- dev@flosports[.]tv
- developer789222@gmail[.]com
- devking877@gmail[.]com
- devondeveloper99@gmail[.]com
- fantasy971114@gmail[.]com
- ferix.moore@gmail[.]com
- freshtinygrow@gmail[.]com
- geniusdev1108@gmail[.]com
- goldendev726@gmail[.]com
- jacob.rd.dev@gmail[.]com
- jacobbush211@gmail[.]com
- johnwadelinson@gmail[.]com
- koizatsuo@gmail[.]com
- liam.perrin.dev@outlook[.]com
- luckyman012357@gmail[.]com
- luckysmile0502@gmail[.]com
- lunadev823@gmail[.]com
- lyappunov19@outlook[.]com
- magnus.masculus971114@gmail[.]com
- masculus1114@gmail[.]com
- mateomuhannad@gmail[.]com
- maxwellreshel0709@outlook[.]com
- mr.new0509@gmail[.]com
- mykytafullstack@gmail[.]com
- naruhitokaide@gmail[.]com
- nektarioskampourakis571@gmail[.]com
- nicolas.edgardo1028@gmail[.]com
- oleksandr.sytnikov0413@gmail[.]com
- oliwerpalm@outlook[.]com
- progdev77@gmail[.]com
- proharvester@outlook[.]com
- raikovskyi830@gmail[.]com
- ranko746.dev@gmail[.]com
- ripaelit1111@gmail[.]com
- smartdev531@gmail[.]com
- starmastar1126@gmail[.]com
- superdev00527@gmail[.]com
- tech.veteran71@gmail[.]com
- ubiuquitosutrusty@gmail[.]com
- web.fan.0509@gmail[.]com
GitHub Indicators
- https://github[.]com/Achilleus0612
- https://github[.]com/adminGit71
- https://github[.]com/aimachieve
- https://github[.]com/alchemist0404
- https://github[.]com/Blux61
- https://github[.]com/boldempha
- https://github[.]com/Bravodev88
- https://github[.]com/bremaster
- https://github[.]com/caddo229
- https://github[.]com/caddoSmith229
- https://github[.]com/chase-allen-tech
- https://github[.]com/cybersage14
- https://github[.]com/Dejan-Teofilovic
- https://github[.]com/deterrionc
- https://github[.]com/devking877
- https://github[.]com/fantasy1114
- https://github[.]com/freshtinygrow-crypto
- https://github[.]com/Gold-Dev726/
- https://github[.]com/harrycorfu
- https://github[.]com/healer1064/
- https://github[.]com/hermes1108
- https://github[.]com/Lyappunov
- https://github[.]com/masculus
- https://github[.]com/metacoffee0x17
- https://github[.]com/mr-new-0509
- https://github[.]com/naruhitokaide
- https://github[.]com/OlekSytn
- https://github[.]com/pioneer830
- https://github[.]com/sharkxhunter/
- https://github[.]com/Shiny0805/
- https://github[.]com/silivex
- https://github[.]com/Skydev-hub
- https://github[.]com/smart1206
- https://github[.]com/Smartdev0022
- https://github[.]com/superdev0527
- https://github[.]com/Talent0407
- https://github[.]com/tech-veteran71
- https://github[.]com/tommy725
- https://github[.]com/up-pro
- https://github[.]com/wissen-snake
DISCLAIMER: All technical information, including malware analysis, indicators of compromise and infrastructure details provided in this publication, is shared solely for defensive cybersecurity and research purposes. Group-IB does not endorse or permit any unauthorized or offensive use of the information contained herein. The data and conclusions represent Group-IB’s analytical assessment based on available evidence and are intended to help organizations detect, prevent, and respond to cyber threats.
Group-IB expressly disclaims liability for any misuse of the information provided. Organizations and readers are encouraged to apply this intelligence responsibly and in compliance with all applicable laws and regulations.
This blog may reference legitimate third-party services such as Telegram and others, solely to illustrate cases where threat actors have abused or misused these platforms.
This material is provided for informational purposes, prepared by Group-IB as part of its own analytical investigation, and reflects recently identified threat activity.
All trademarks referenced herein are the property of their respective owners and are used solely for informational purposes, without any implication of affiliation or sponsorship.