Igor Mikhailov is a digital forensic analyst of the digital forensic laboratory at Group-IB and the picture below shows how one of his business cards looked like. These are hardware keys of forensic tools that the digital forensic analyst used conducting forensic examinations. The cost only of these products exceeds tens of thousands of dollars and there are other free and commercial software products. Which tool is better to use for examination? Especially for our readers, Igor Mikhailov decided to give his review of the best software and hardware solutions for computer forensics.
Digital forensic examiner’s briefcase
Computer forensics involves an investigation of a great variety of digital devices and data sources. The examiner can use both software and hardware tools during examination and most of them cost a lot. Not every organization can afford such expenses, let alone an individual specialist. We, in Group-IB, do not scrimp on the tools and it allows us to conduct examinations with due diligence and in a timely manner.
Mobile forensics, hardware tools
Cellebrite UFED Touch 2 is a product that was originally developed for work in field conditions. The product is conceptually divided into two parts:
- Branded tablet Cellebrite UFED Touch 2 (or UFED 4PC – software analogue of Cellebrite UFED Touch 2 installed on a digital forensic analyst’s computer or laptop): used only for data extraction.
- UFED Physical Analyzer – software part of the product designed to analyze data extracted from mobile devices.
The concept of usage of this equipment assumes that a digital forensic analyst extracts data in the field with the help of Cellebrite UFED Touch 2 and then in the laboratory analyzes them using the UFED Physical Analyzer. The laboratory version of the product is two independent software products – UFED 4PC and UFED Physical Analyzer – installed on the digital forensic analyst’s computer.
As for today, this complex provides data extraction from as many mobile devices as possible. Some of the data may be lost by the UFED Physical Analyzer program during the analysis. This is due to the old bags that were sort of fixed in new versions of the program but they occur. That is why we recommend to check that the data analysis conducted by the UFED Physical Analyzer was done completely.
MSAB XRY / MSAB XRY Field is an analogue of Cellebrite products developed by the Swedish company Micro Systemation. Unlike the Cellebrite paradigm, Micro Systemation suggests that in most cases their products will be used on desktop computers or laptops. The product is supplied with the brand USB-hub that has recognizable appearance, a set of adapters, and data-cables for connecting different mobile devices. The company also offers hardware products MSAB XRY Field and MSAB XRY Kiosk, which are designed for data extraction from mobile devices. The products have form of tablet and kiosk. The practice has shown that these products are good for data extraction from obsolescent mobile devices.
From a certain moment, hardware tools for chip-off (method of data extraction directly from a mobile device’s memory chip) designed by the Polish company Rusolut became popular. Using the device, we can extract data from damaged mobile devices or from mobile devices locked with the PIN-code or picture password. Rusolut provides a several sets of adapters for data extraction from certain mobile device models. For example, a set of adapters for data extraction from memory chips that are usually used in “Chinese mobile phones”. However, the widespread use of user data encryption in top models by the mobile device manufacturers has led to the fact that this solution is gradually losing relevance. It is possible to extract data from the memory chip, but it will be encrypted and its decryption is a sophisticated problem.
Mobile forensics, software tools
Following the development of mobile forensics, you can see that the mobile devices analysis programs developed in parallel with the functionality of mobile devices. Earlier a digital forensic analyst or a person who ordered the investigation could get only data from the phone book, SMS, MMS, calls, graphic and video files, now the digital forensic analyst is asked to extract more data. In addition to the above mentioned, as a rule, you need to extract:
- data from messengers;
- emails;
- browsers history;
- geolocation data;
- deleted files and other deleted information/records.
And this list is constantly expanding. All of these types of artifacts can be extracted with the software described below.
«Oxygen Software» is one of the best programs for data extracted from mobile device analysis. You should use this program if you want to extract maximum data from a mobile device. Integrated viewers of SQLite databases and plist-files allow you to manually examine specific SQLite databases and plist-files as thoroughly as you need.
Initially, the program was developed for use on computers, so using it on a netbook or tablet (devices with a screen size of 13 inches or less) will be uncomfortable.
A feature of the program is the tight binding of the paths, where the files are located, of application database. All applications that are installed on smartphones store their data in one or several files – databases. These databases are located in particular catalogues. If the location of database is changed after update of the application then the “Oxygen Software” will not be able to find the database (as the files of the particular application have to be located by the specified path and nowhere else) and consequently will not extract its data. That is why the examination of the databases will have to be done manually via “Oxygen Software” file browser and auxiliary utilities.
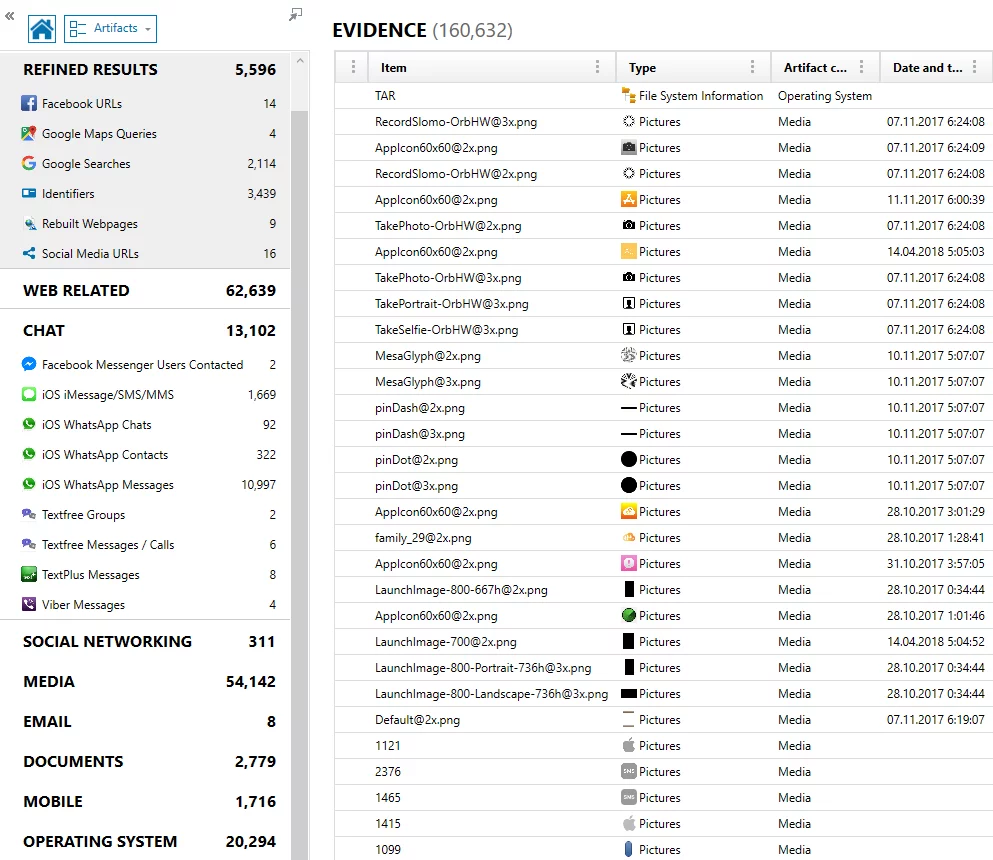
The results of a study of a mobile device in the Oxygen Forensic Suite program:
The trend of recent years is “fusion” of the programs functionality. The manufacturers that originally develop programs for mobile forensics introduce the functionality of hard drives examinations in their products. The manufacturers of forensics products that are specialized on hard drives examination add the functionality of mobile devices examination. Both types of manufacturers add the functionality of data extraction from cloud storages, etc. As a result, we have “multifunctional programs” with the help of which we can conduct examination of mobile devices, hard drives, extract data from cloud storages, and analyze the data extracted from all these sources.
In our list of the best programs for mobile forensics such programs take two places: Magnet AXIOM – the program of the Canadian company Magnet Forensics, and Belkasoft Evidence Center – the solution of Belkasoft. These programs with their functionality are inferior in data extraction comparing with the software and hardware tools described above, but they are good for data analysis and can be used for ultimate different types of artefacts extraction control. Both programs are actively developing and rapidly gaining their functionality in mobile devices examination.
AXIOM program’s window of evidence source of mobile data:
Results of mobile device examination via Belkasoft Evidence Center:
Computer forensics, hardware write-blockers
Tableau T35U – a hardware write-blocker by the Tableau Company that allows to safely connect the examined hard drives to the researcher’s computer via USB3 bus. This write-blocker has sockets that allow to connect hard drives via IDE and SATA interfaces (if you have adapters you can also connect hard drives with other interfaces). The feature of the write-blocker is an ability to emulate “read-write” operations. It is useful for hard drives examination that contain malicious software.
Wiebitech Forensic UltraDock v5 – a hardware write-blocker by the CRU Company. The functionality of the product is comparable to the functionality of Tableau T35U. This write-blocker can be paired with the digital forensic analyst’s computer via great amount of interfaces (in addition to USB3, it can be connected via eSATA and FireWire interfaces). If you connect a hard drive to this write-blocker, access to which is limited by the ATA password, a message about limitation will appear on the display of the write-blocker. In addition, when a hard drive with a hidden area DCO (Device Configuration Overlay) is connected, this zone will be automatically unlocked so that a digital forensic analyst can copy the data in it.
Both write-blockers use the USB3 bus connection as the main, which provides comfortable working conditions for the digital forensic analyst during cloning and analyzing process of data storage device.
Computer forensics, software solutions
Old stuff for non-routine procedures
Fifteen years ago, the undisputed leaders of computer forensics were Encase Forensics and AccessData FTK. Their functionality complemented each other and allowed to extract the maximum number of different types of artifacts from the examined devices. Nowadays, these projects are outsiders of the market. The current functionality of Encase Forensics is not up to the requirements of the modern software for examination of computers and servers running Windows OS. The use of Encase Forensics remains relevant in “non-routine” cases: when you need to examine computers running Mac OS or a server running Linux OS or extract data from rare file formats. Ensripts macro language built into Encase Forensics contains a large library of scripts implemented by the manufacturer and enthusiasts: using them, you can analyze a large number of different operating and file systems.
AccessData FTK tries to support the functionality of the product up to the level, but the processing time for the data storages significantly exceeds the reasonable amount of time that an average specialist can afford to spend on examination.
The features of the AccessData FTK product are:
- keywords search is implemented at a very high level;
- analytics of various cases, allowing to identify correlation in devices seized for various cases;
- option of interface customization;
- it supports rare file formats (for example, Lotus Notes databases).
Both Encase Forensics and AccessData FTK can process a large number of data measured in hundreds of terabytes.
Young and promising
The undisputed leader in computer forensics is Magnet Axiom. The program not only gradually develops, but also includes functional entire segments: examination of mobile devices, data extraction from cloud storages, examination of devices running MacOS, etc. The program has user-friendly and functional interface that can be used for investigations related to the computers or mobile devices security.
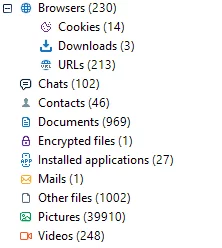
The analogue of Magnet AXIOM is Belkasoft Evidence Center. Belkasoft Evidence Center allows to extract and analyze data from mobile devices, cloud storages and hard drives. The program allows, during examination of hard drives, to detect encrypted files and partitions, extract files by a specified extension, data from web-browsers, chats and information about cloud services, geolocation data, e-mails, social networks and payment systems data, thumbnails, system files, system logs, etc. It has flexible customizable functionality for deleted data extraction.
Advantages of the program:
- a wide range of artifacts that can be extracted from various data storages;
- decent built-in SQLite database viewer;
- data collection from remote computers and servers;
- integrated functionality of checking detected files via VirusTotal.
The basic configuration of the program has a moderate price. Other modules that extend the functionality of Belkasoft Evidence Center can be purchased separately. In addition to the basic configuration, it is strongly recommended to buy the “File Systems” module, without which it is not convenient to work with the examined data storages.
As for disadvantages of the program: the interface of the program is not user-friendly and it is not obvious how to conduct separate actions. It takes training how to use the program to work in it efficiently.
The main Belkasoft Evidence Center window that shows the statistics of the forensic artifacts detected during examination of a specific device:
X-Ways Forensics conquers the digital forensics market step-by step. This program is a Swiss Army knife of computer forensics. Multi-functional, accurate, reliable and compact. A feature of the program is the high speed of data processing (comparing with other programs in this category) and the optimal functionality that covers the basic needs of a digital forensic analyst in computer forensics. The program has a built-in mechanism to minimize false-positive results, meaning that the digital forensic analyst who recovers files from a 100 GB hard drive, gets not a 1 TB of recovered files (most of which are false-positive results, as is usually happens when you use recovery programs), but those files that were really recovered.
Using X-Ways Forensics you can:
- find and analyze email data;
- analyze web-browsers history, Windows OS logs and other system artefacts;
- filter results, remove unnecessary, leave only valuable and relevant;
- make a timeline and see activities in the relevant period;
- rebuild RAID;
- mount virtual disks;
- check for malware.
The program has proven itself to be good at the manual analysis of hard drives removed from video recorders (CCTV). There is a possibility to integrate third-party developers’ modules to the program using its functionality.
Disadvantages of X-Ways Forensics:
- plain interface;
- absence of full scale built-in SQLite database viewer;
- the program requires in-depth training: it is not obvious how a digital forensic analyst should conduct actions required to get the proper results.
Data recovery, hardware tools
Nowadays, there is only one leader of such products in the digital forensics market – ACELab. The company produces hardware tools for analysis, diagnostics and recovery of hard drives (PC-3000 Express, PC-3000 Portable, PC-3000 UDMA, PC-3000 SAS), SSD drives (PC-3000 SSD complex), USB flash drives (PC-3000 Flash complex), RAID (PC-3000 Express RAID complexes, PC-3000 UDMA RAID, PC-3000 SAS RAID). The leadership of ACELab on the hardware tools market is determined by the high quality of the products mentioned above and the price policy, which create obstacles to the competitors who want to enter the market.
Data recovery, software tools
Despite the fact that there is a large number of various recovery programs, both commercial and free, it is hard to find a program that would correctly and fully recover different types of files in different file systems. Nowadays, there are only two programs with approximately the same functionality, which satisfy the requirements: R-Studio and UFS Explorer. Other thousands of programs for data recovery either underperform in functionality comparing with above mentioned programs or significantly inferior to them.
Open source software
Autopsy is a convenient tool for analysis of the computers running Windows OS and mobile devices running Android operating system. It has a graphical interface. The tool can be used for investigation of computer-related cases.
Photorec is one of the best free programs for data recovery. It is a good substitution to the commercial analogues.
Eric Zimmerman Tools is a set of free tools, each of which allows to examine a specific Windows artefact. As practice has shown, Eric Zimmerman Tools increases efficiency of digital forensic analyst’s performance in the field. Nowadays, these tools are available as a set of programs – Kroll Artifact Parser and Extractor (KAPE).
Linux based distributions
SIFT is a Linux distribution developed and supported by commercial organization SANS Institute, which specializes in cyber security training and incident response. SIFT contains a large number of current versions of free programs that can be used both to extract data from various sources and to analyze them. SIFT is used for trainings that the company conducts and it constantly updates. The convenience of work is determined by the specific tool, located in this distribution, with which a digital forensic analyst works.
Kali Linux is a unique Linux distribution, which is used by digital forensic analysts both for conducting a security audit and for conducting investigations. In 2017, “Packt Publishing” published a book by Shiva V. N Parasram “Digital Forensics with Kali Linux”. The book gives tips on how to conduct coping, examination and analysis of computers, storages, copies of RAM data and network traffic with the help of tools included in this set.
Conclusion
This article is the result of my practice experience of work with the described hardware and software tools that I use conducting forensic examination of computers and mobile devices. I hope that the article will be useful for digital forensic analysts who plan to purchase hardware and software tools for conducting forensic examination and investigation of cases.