Background
In September 2023, Group-IB’s threat intelligence analysts uncovered a Spanish-speaking criminal group operating a sophisticated phishing-as-a-service platform. What set the group apart was not just their technical capabilities but also their brazen use of artificial intelligence to industrialize fraud at an unprecedented scale.
The gang, which called itself “GXC Team,” had been quietly building a criminal empire since early 2023. Operating through Telegram channels and the underground forum Exploit.in, they offered a full-service fraud toolkit including custom phishing kits mimicking 36 Spanish banks and 30 international institutions, Android malware designed to intercept one-time passwords, and, most alarmingly, AI-powered voice calling capabilities that could generate convincing scam calls in real time.
The criminals didn’t hide their ruthless approach. One of their Telegram channels was called “Steal everything from grandmas.”
Behind the scenes
GXC Team’s business model was classic. For anywhere from $150 to $900, customers could purchase phishing kits tailored to specific banks. For approximately $500 per month, they received the full package: phishing kit, Android malware, domain registration, hosting, and technical support, which equates to a complete Crime-as-a-Service ecosystem.
The scheme worked like clockwork. Victims would receive smishing messages directing them to fake but convincing banking portals. Once the victims had entered their credentials, the threat actors, who were watching in real time through a “live panel”, could control what information to request next: national ID documents, payment card details, or physical addresses.
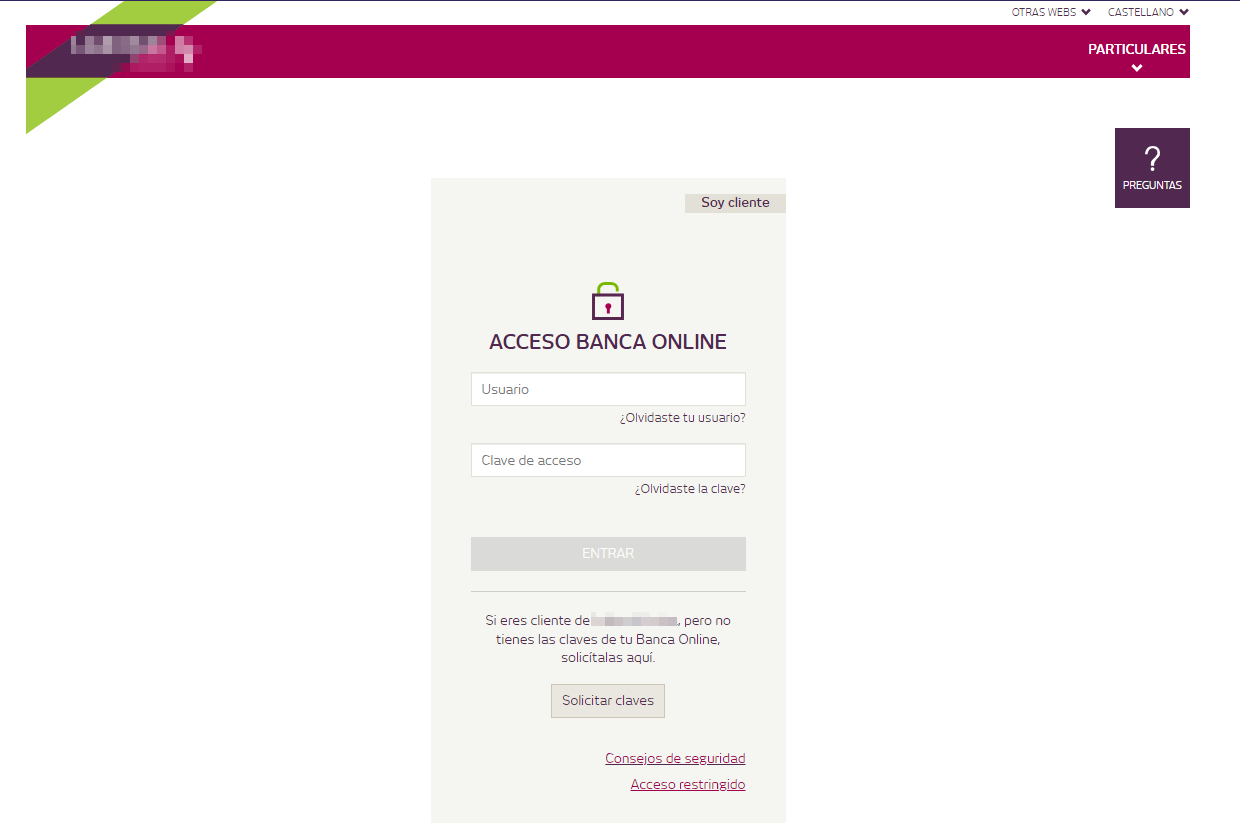
Figure 1. Example of the initial phishing website
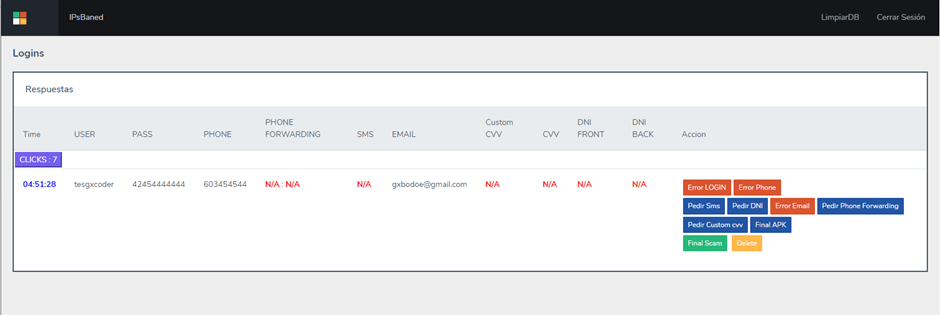
Figure 2. Screenshot of the phishing kit’s live admin panel
But the most striking innovation came at the final stage. Instead of simply harvesting credentials, the phishing pages would prompt victims to download a “banking security app” to “prevent fraud.” The cruel irony was that this app was actually malware that silently intercepted every SMS message, including one-time passwords sent by banks to authorize transactions.
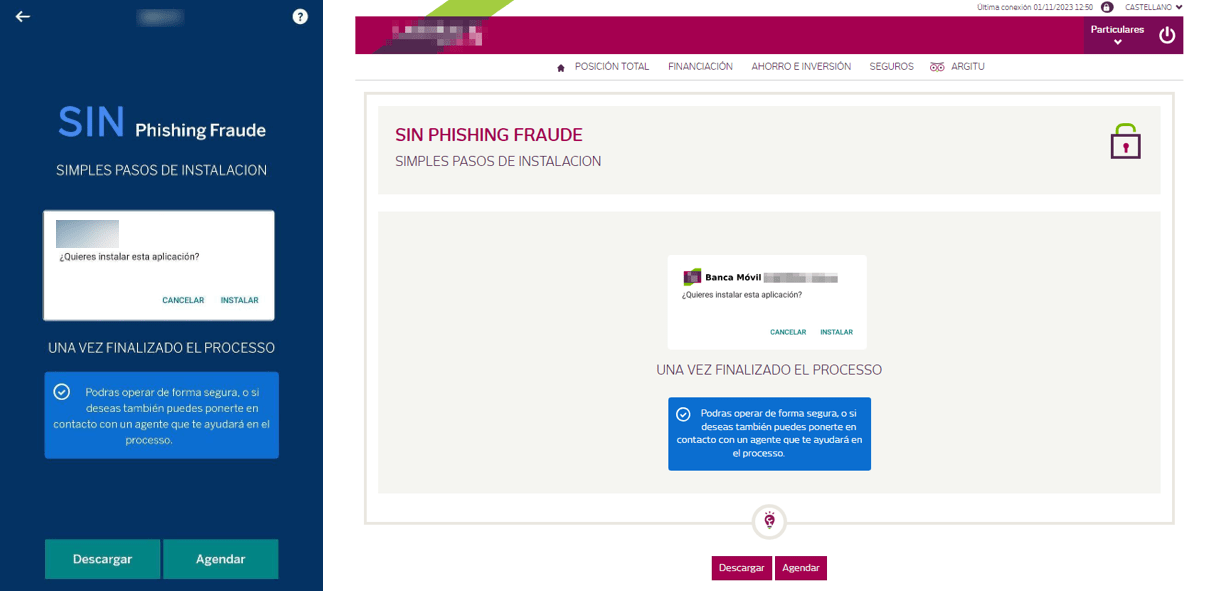
Figure 3. Example of a phishing page asking its victims to install a “banking app” under the guise of preventing fraud attempts
With credentials obtained and OTP codes flowing to their Telegram bots, the criminals had everything they needed to drain accounts.
The AI voice caller added another layer of deception. Victims would receive automated calls, generated on demand from the phishing kit’s admin panel, purportedly from their bank and instructing them to provide 2FA codes or take other actions. The voice sounded human and the requests seemed legitimate. Yet in the end, their money disappeared.
Impact
For nearly two years, GXC Team operated with impunity. Although exact figures are still being determined, Spanish authorities have attributed millions of euros in financial losses to the group.
The damage extended far beyond direct theft. Customers of more than 30 financial institutions had their credentials harvested and their trust in digital banking shaken. Government services and eCommerce platforms in five countries were impersonated. It is impossible to calculate the reputational cost to the institutions whose brands were weaponized.
Group-IB’s investigation identified over 288 phishing domains, 9 variants of Android malware, and a network of criminal customers who had purchased GXC Team’s services to run their own fraud operations.
Storyline
In July 2023, Group-IB analysts first came across GXC Team while monitoring underground forums and Telegram channels for emerging threats targeting the financial sector. The group’s package offerings and their focus on Spanish banks suggested it was a regional threat worth investigating.
The investigation expanded rapidly. In September 2023, Group-IB’s Cybercrime Investigation team began mapping the group’s technical infrastructure, analyzing malware samples, and cataloging the growing list of phishing domains attributed to the threat actor. By analyzing the Android malware, Group-IB experts traced the command-and-control infrastructure back to specific criminal operators.
Email addresses, phone numbers, cryptocurrency wallets, social media accounts – each piece of evidence narrowed the circle. In total, Group-IB gathered and analyzed over 100 assets tied to the threat actors. The investigation pivoted from infrastructure to identity.
Once the Group-IB team achieved full attribution of the core threat actors, including the mastermind behind the operation, the entire intelligence package was shared with Spanish law enforcement.
The Guardia Civil’s Department against Cybercrime launched a methodical investigation based on the intelligence gathered by Group-IB. Both patience and precision were pivotal to track down a suspect who had adopted a “digital nomad” lifestyle and was constantly relocating between Spanish provinces and using stolen identities to secure housing, phone lines, and payment cards.
A year-long forensic analysis of cryptocurrency transactions helped trace the flow of stolen funds through various digital platforms. The net was closing.
And justice for all
In May 2025, the Spanish Guardia Civil carried out six simultaneous raids across Spain. As a result, the mastermind known as “GoogleXcoder”, a 25-year-old Brazilian, was arrested in San Vicente de la Barquera, Cantabria. Additional operations swept through Valladolid, Zaragoza, Barcelona, Palma de Mallorca, San Fernando, and La Línea de la Concepción.
Authorities seized electronic devices containing phishing source code, communications with criminal customers, and financial records. Stolen funds were recovered from digital platforms, and the Telegram channels used to orchestrate the scams went dark. To this day, however, investigators continue to analyze forensic evidence related to the gang.
Apart from the operation’s mastermind, six criminals who had purchased GXC Team’s tools to run their own attacks were identified and apprehended. The arrests neutralized key enablers of the criminal ecosystem and significantly disrupted the supply of tools used in widespread banking fraud schemes.
Conclusion
Group-IB has been at the forefront of cybercrime investigations for over two decades, collaborating with INTERPOL, Europol, Afripol and law enforcement agencies worldwide. The GXC Team takedown bears witness to the company’s continued commitment to dismantling criminal ecosystems and protecting the digital economy.
The investigation helped to dismantle one of Spain’s most active cybercrime networks. But it also highlighted a systemic challenge: threats like GXC Team operate in spaces that most organizations can’t monitor alone such as underground forums, encrypted channels, and criminal marketplaces. For nearly two years, a sophisticated fraud operation targeting dozens of financial institutions grew in these shadows.
Law enforcement and cyber investigators can identify and dismantle such networks. But the missing force multiplier is the financial sector itself. When banks join the fight — sharing intelligence, acting on early warnings, and collaborating on takedowns — criminal operations lose their runway. It’s today’s reality, not a future dream. Customers can be protected before their accounts are drained, while reputational damage suffered by banks can be prevented rather than managed. Solutions like Group-IB’s Cyber Fraud Intelligence Platform were created to enable organizations to share fraud intelligence in real time and act on threats before they can escalate.
Fraudsters and criminals are eager to join forces. The next GXC Team is already emerging. It’s time for banks, enterprises, and their customers to fight back together. Can you afford not to join in?


























