Get 24/7 incident response assistance from our global team
- APAC: +65 3159 4398
- EU & NA: +31 20 890 55 59
- MEA: +971 4 540 6400
- LATAM: +56 2 275 473 79
Get 24/7 incident response assistance from our global team
Please review the following rules before submitting your application:
1. Our main objective is to foster a community of like-minded individuals dedicated to combatting cybercrime and who have never engaged in Blackhat activities.
2. All applications must include research or a research draft. You can find content criteria in the blog. Please provide a link to your research or research draft using the form below.
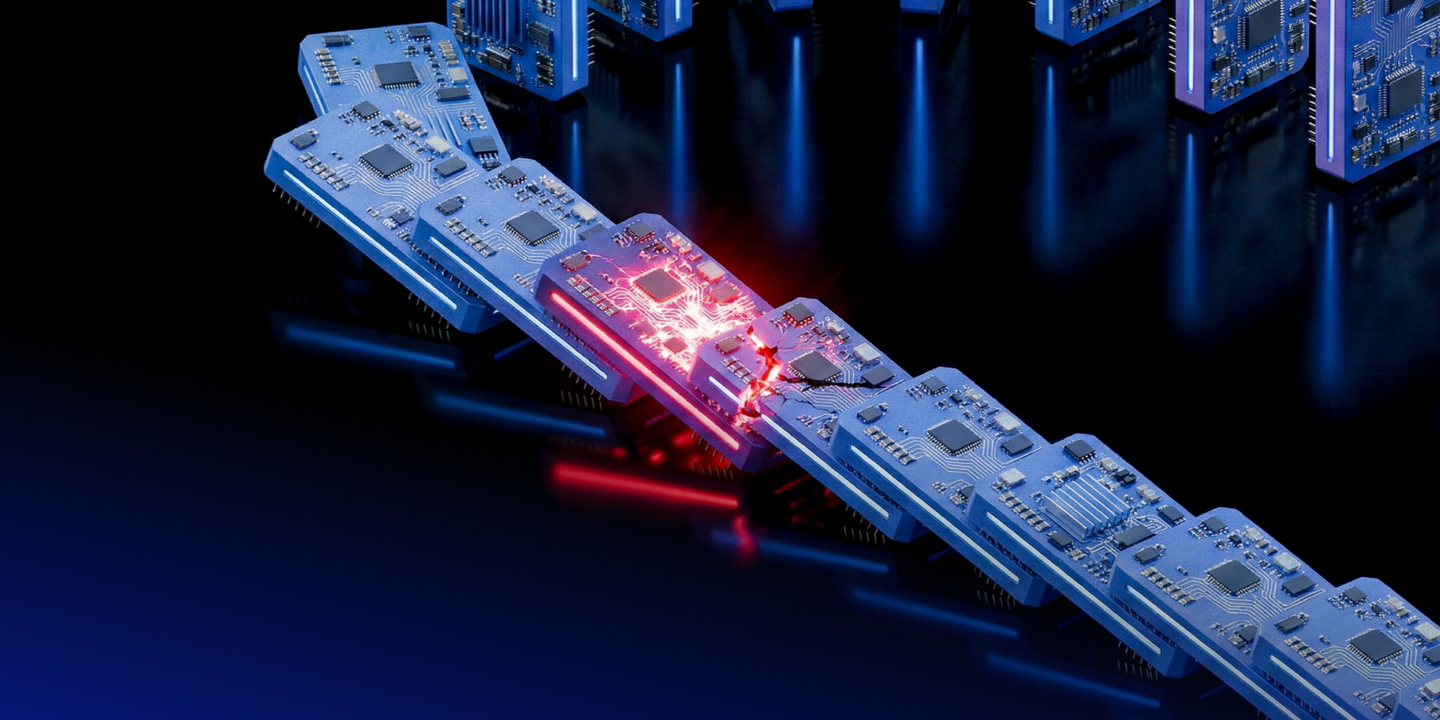
Supply chain attacks have become the defining force in today’s cyber threat landscape. Rather than targeting organizations directly, attackers exploit trusted vendors, SaaS platforms, open-source dependencies, and OAuth integrations to gain inherited access that silently spreads across entire ecosystems. What appear to be isolated incidents like phishing, ransomware, data breaches, malware are increasingly interconnected stages of a single supply chain-driven attack model. Stolen tokens, API keys, and service accounts enable threat actors to move laterally across trusted environments while blending in as legitimate users.
In this webinar, we’ll cover
Join us to understand how to break the domino effect before it spreads.The same webinar is also available in German.