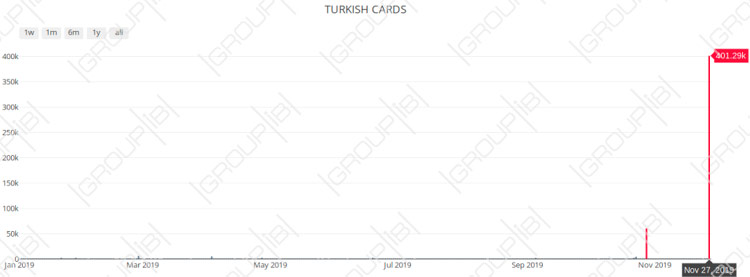
Group-IB, a Singapore-based cybersecurity company that specializes in preventing cyberattacks, has detected a massive upload of debit and credit card records mostly related to the largest Turkish banks on one of the most popular underground cardshops. More than 460,000 records in total were uploaded between Oct. 28 and Nov. 27. The underground market value of the database is estimated at more than $0.5 million. Upon discovery of this database, Group-IB has informed proper local authorities about the sale of the payment records, so they could take necessary steps.
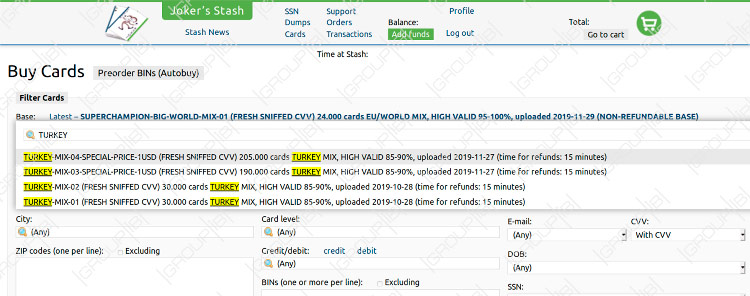
Using its own unique tools for underground forums and cardshops monitoring, research and analysis Group-IB Threat Intelligence team has discovered that compromised payment records predominantly related to TOP 10 Turkish banks were uploaded in four parts to Joker’s Stash one of the most popular underground cardshops. The first two databases named «TURKEY-MIX-01 (FRESH SNIFFED CVV) 30.000 cards TURKEY MIX, HIGH VALID 85-90%, uploaded 2019-10-28 (NON-REFUNDABLE BASE)» and «TURKEY-MIX-02 (FRESH SNIFFED CVV) 30.000 cards TURKEY MIX, HIGH VALID 85-90%, uploaded 2019-10-28 (NON-REFUNDABLE BASE)» went on sale on 28.10.2019 and had 60,000 pcs. All the cards in these two parts were sold at 3$ each.
The two other parts of the database under the names «TURKEY-MIX-03-SPECIAL-PRICE-1USD (FRESH SNIFFED CVV) 190.000 cards TURKEY MIX, HIGH VALID 85-90%, uploaded 2019-11-27 (time for refunds: 15 minutes)» and «TURKEY-MIX-04-SPECIAL-PRICE-1USD (FRESH SNIFFED CVV) 205.000 cards TURKEY MIX, HIGH VALID 85-90%», uploaded 2019-11-27 (time for refunds: 15 minutes) were uploaded on 27.11.2019. «TURKEY-MIX-03» had roughly 190,000 records, while «TURKEY-MIX-04» had about 205,000 cards. The cards were valued at 1$ each.
Neither of these four parts that went on sale had been promoted prior either in the news, on card shop or even on forums on the dark net. It is also worth noting that the cards from Turkey are very rare on the cardshops, in the past 12 months this is the only big sale of payment cards related to Turkish banks.
A breakdown of the data indicated that all the cards could have likely been compromised online either due to phishing, malware or increased activity of Java-Script sniffers. All the compromised credit and debit cards records in this database were identified as raw cards data also known as „CCs“ or „fullz“ and contained the following information: card number, expiration date, CVV/CVC, cardholder name as well as some additional info such as email, name and phone number, which, unlike card dumps (the information contained in the magnetic stripe), cannot be obtained through the compromise of offline POS terminals. Upon identification of this information, Group-IB team has immediately alerted relevant Turkish local authorities about the sale of the payment records, so the former could take appropriate measures and mitigate the risks. The source of this data compromise remains unknown.

Head of Group-IB сybercrime research unit
According to Group-IB’s annual Hi-Tech Crime Trends 2019/2020 threat report, presented at CyberCrimeCon in Singapore, the size of the carding market grew by 33 percent and amounted to USD 879.7 million from H2 2017-H1 2018 to H2 2018 H1 2019. The sale of raw card data, exactly the same type of payment records offered in this case with Turkey (expiration date, CVV/CVC, cardholder name) is also on rise today, having increased by 19 percent in the corresponding period, one of the key reasons behind this trend could be JavaScript-sniffers (JS-sniffers), which is a type of malware designed to steal customer payment data from online stores: payment card numbers, cardholder names, addresses, user credentials etc. In 2019 alone, Group-IB experts identified at least 38 different families of JS-sniffers, with this number continuously growing and already exceeding the number of banking Trojans for PC and Android. Most JS-sniffer families are designed to steal information from the payment forms from the websites running on specific CMS (content management systems), however there are also universal ones they can steal information from payment forms and do not require modifications tailored to specific websites.
To avoid a card being compromised online due to JS-sniffers, Group-IB experts recommend that users should have a separate pre-paid card for online payments, set spending limits on cards, used for online shopping, or even use a separate bank account exclusively for online purchases. The admins of eCommerce websites, in their turn, need to keep their software updated, carry out regular cybersecurity assessments of their websites and not hesitate to seek assistance from cybersecurity specialists whenever needed.