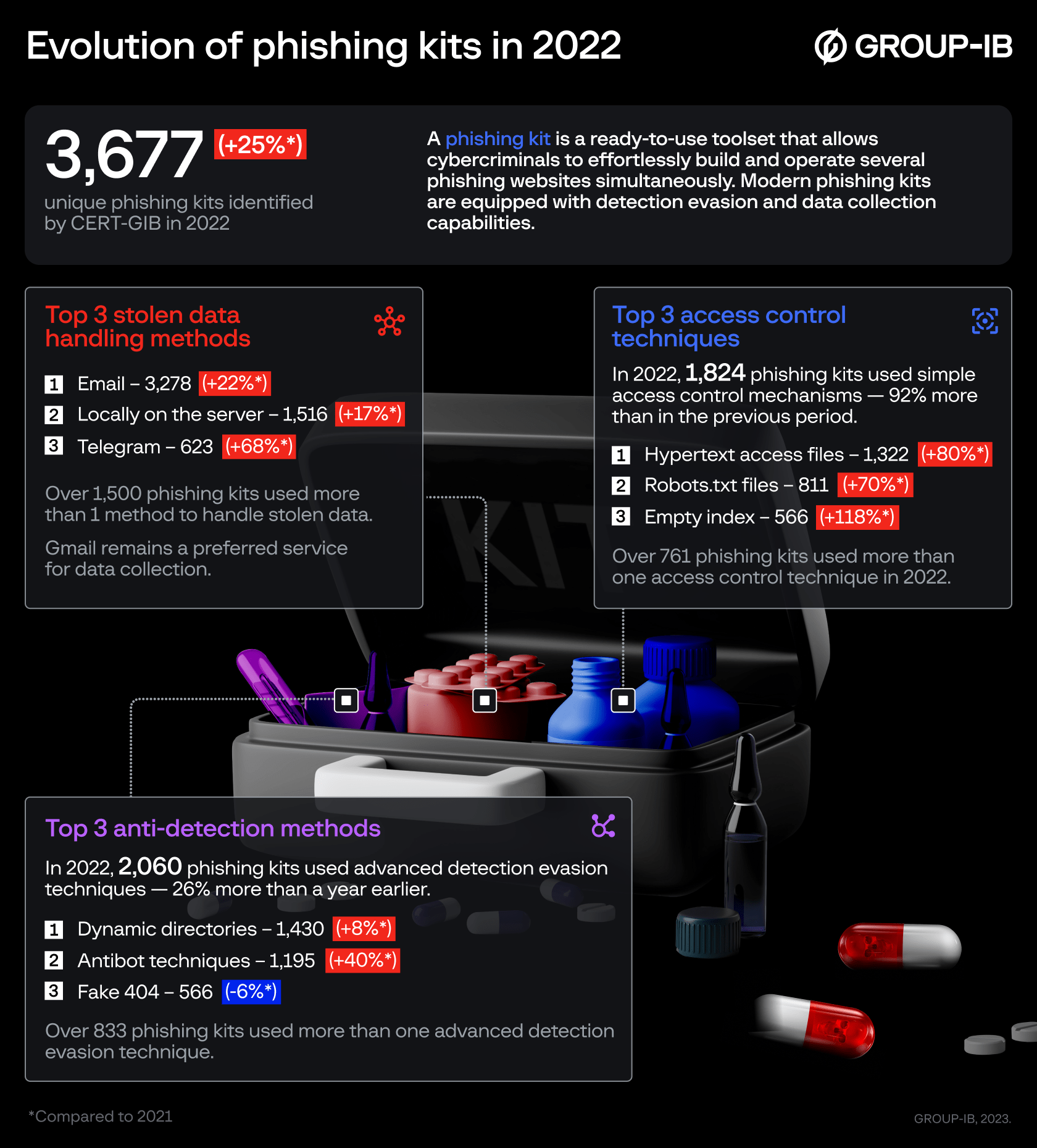
Group-IB, a global cybersecurity leader headquartered in Singapore, has recorded a 25% increase in the use of phishing kits in 2022. The key phishing trends observed by Group-IB’s Computer Emergency Response Team (CERT-GIB), based on the analysis of more than 6,000 phishing kits extracted in 2021 and 2022, are the increasing use of access control and advanced detection evasion techniques. CERT-GIB notes that the rise in evasive tactics, such as antibot techniques and randomization, poses a significant challenge for conventional detection systems and extends the lifespan of phishing campaigns.
CERT-GIB, which serves as the first line of defense for Group-IB and its customers, identified 3,677 unique phishing kits in 2022, 25% more than in 2021. A phishing kit is a set of tools that enables cybercriminals to create and operate several phishing pages at once. These are useful tools for threat actors, as they allow them to effortlessly build and maintain the infrastructure needed to carry out large-scale phishing campaigns, move from one host to another in case of blocking, and collect stolen data.
Email reigns supreme but Telegram surges
Phishing websites are designed to harvest personal data and require a specific method to collect and store it. CERT-GIB found that the bulk of stolen data is still handled via email. In total, just under half of the phishing kits from 2022 seen by CERT-GIB relied on email to handle stolen information with Gmail being the most preferred email service used for data collection among phishing kit creators (45%).
A continuing trend is the sustained popularity of Telegram for stolen data collection. According to CERT-GIB, the number of phishing kits that use Telegram to collect stolen data almost doubled in 2022 compared to the preceding year. In 2021, 5.6% of phishing kits seen by CERT-GIB used Telegram to handle stolen data. One year later, the share of Telegram increased to 9.4%. The messenger’s flexibility and convenience allow cybercriminals to process and manage compromised information almost in real-time.
Many phishing kits employed more than one method to handle stolen data. For example, in 2022, approximately 1,500 phishing kits contained the functionality for transferring stolen data either via Telegram, email or by writing the data to a file locally on the server, which indicates their growing sophistication.
Laying low
Alongside the increased use of Telegram, phishing attacks are becoming more complex as cybercriminals focus on enhancing evasion capabilities to avoid detection and takedown. CERT-GIB split the evasion techniques identified in phishing kits over 2021-2022 into two categories: trivial access control mechanisms and more advanced detection evasion methods.
Within the first category, hypertext access (.htaccess) became the most popular technique in 2022 – 20% of detected phishing kits employed this tactic. The configuration file allows a website operator to restrict access to specific directories based on the visitor’s IP address. The second most popular access control strategy in 2022 was robots.txt (seen in 12% of kits) — another configuration file that prevents bots and search engine crawlers from accessing the website. Overall, the use of simple access control mechanisms increased by 92% to 1,824 in 2022 compared to the preceding year, when 951 phishing kits used some sort of selective restriction.
To hinder the work of cybersecurity specialists and off-the-shelf cybersecurity solutions, more phishing kits are packed with advanced detection evasion techniques. Basic mechanisms include blacklisting of cybersecurity vendors’ IPs and hostnames. More sophisticated tactics involve the use of antibots, randomization of directories, etc. Such tactics were used by 2,060 phishing kits seen by CERT-GIB in 2022, 26 % more than a year earlier. Notably, in 2022, Group-IB researchers observed a 40% increase in the use of anti-bot technologies designed to prevent automated cybersecurity scanners from identifying phishing content.
One of the phishers’ main goals is to extend the life of their websites. Hence, the most commonly used detection evasion technique was dynamic directories. Phishing operators create random website folders that are only accessible by the recipient of a personalized phishing URL and cannot be accessed without the initial link. This technique allows phishers to evade detection and blacklisting as the phishing content will not reveal itself. Dynamic directories were utilized by 22% of phishing kits detected in 2022 by Group-IB. Another popular tactic (observed in 11% of phishing kits in 2022) is the use of fake 404 pages displayed to visitors if their device parameters, geolocation, and referrer do not match the victim’s profile.
“Automation enables phishers to create and manage hundreds of websites every day. Extracting and monitoring for phishing kits is an essential part of protecting against phishing attacks. It can help identify and block phishing before it causes massive damage. Additionally, analysis of phishing kits is invaluable from an intelligence gathering perspective as it provides valuable insights into the TTPs of adversaries. In many cases, it can also help to identify phishing kit developers which is useful for prosecution of threat actors.”

CEO of Group-IB
Over the past 10 years, Group-IB’s Threat Intelligence has built a large collection of phishing kits that is updated in real time. This knowledge helps us stop brand impersonation attacks and investigate phishing campaigns more effectively. Notably, the infamous 0ktapus campaign targeting over 130 companies, relied on a simple phishing kit. By tracking down this phishing kit, Group-IB researchers were able to uncover the whole phishing operation and establish the alleged identity of the perpetrator.