Introduction
Infostealer malware remains one of the most effective tools for gaining unauthorized access to corporate networks. It collects sensitive data from infected devices (often called bots), including browser credentials, passwords, cookies, credit card details, and cryptocurrency wallet information.
The data extracted by infostealers is actively traded across cybercriminal underground markets and frequently serves as a starting point for further attacks. These logs are commonly used to establish initial access for ransomware operations, enable data breaches, and facilitate fraud schemes such as Business Email Compromise (BEC).
Phantom Stealer is one such threat — a .NET-based infostealer sold commercially as part of the “Phantom Project,” a toolkit that bundles a stealer, a crypter, and a remote access tool under subscription tiers. Once executed, Phantom Stealer harvests saved passwords, cookies, autofill data, and payment cards from Chrome and Firefox-based browsers, extracts Discord, Telegram, and Outlook session data, captures Wi-Fi credentials, and exfiltrates everything via Telegram, Discord, SMTP, or FTP. Its consistent delivery through phishing makes email the earliest choke point — and the best opportunity to stop it.
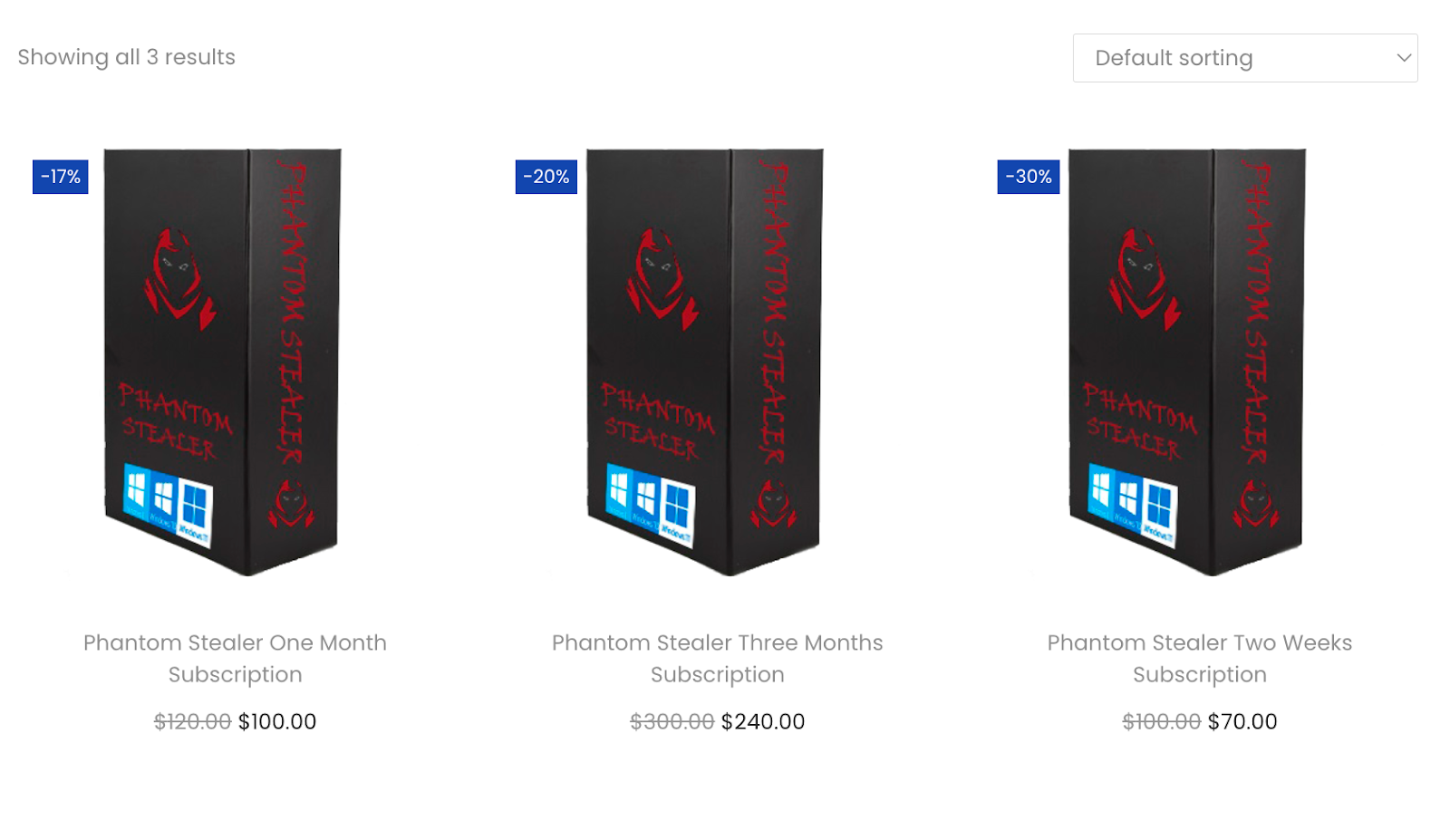
Figure 1. Phantom Stealer subscription tiers advertised on the project’s website
More information about the Phantom Stealer, related IOCs and infrastructure indicators can be found in the Group-IB Threat Intelligence platform.
This post is the latest entry in Group-IB’s Email Protection Spotlight series, which highlights real-world phishing, explains adversary tactics, and shows how Business Email Protection uses advanced detection and global threat intelligence to stop threats before they can impact your business.
Case Study
Between November 2025 and January 2026, Group-IB’s Business Email Protection detected a sustained Phantom Stealer delivery campaign targeting European logistics, manufacturing, and technology organizations. Across five distinct waves, all phishing emails were blocked before reaching end users. The threat actor targeted multiple unrelated companies on the same day — spray patterns that are a hallmark of stealer-as-a-service operations.
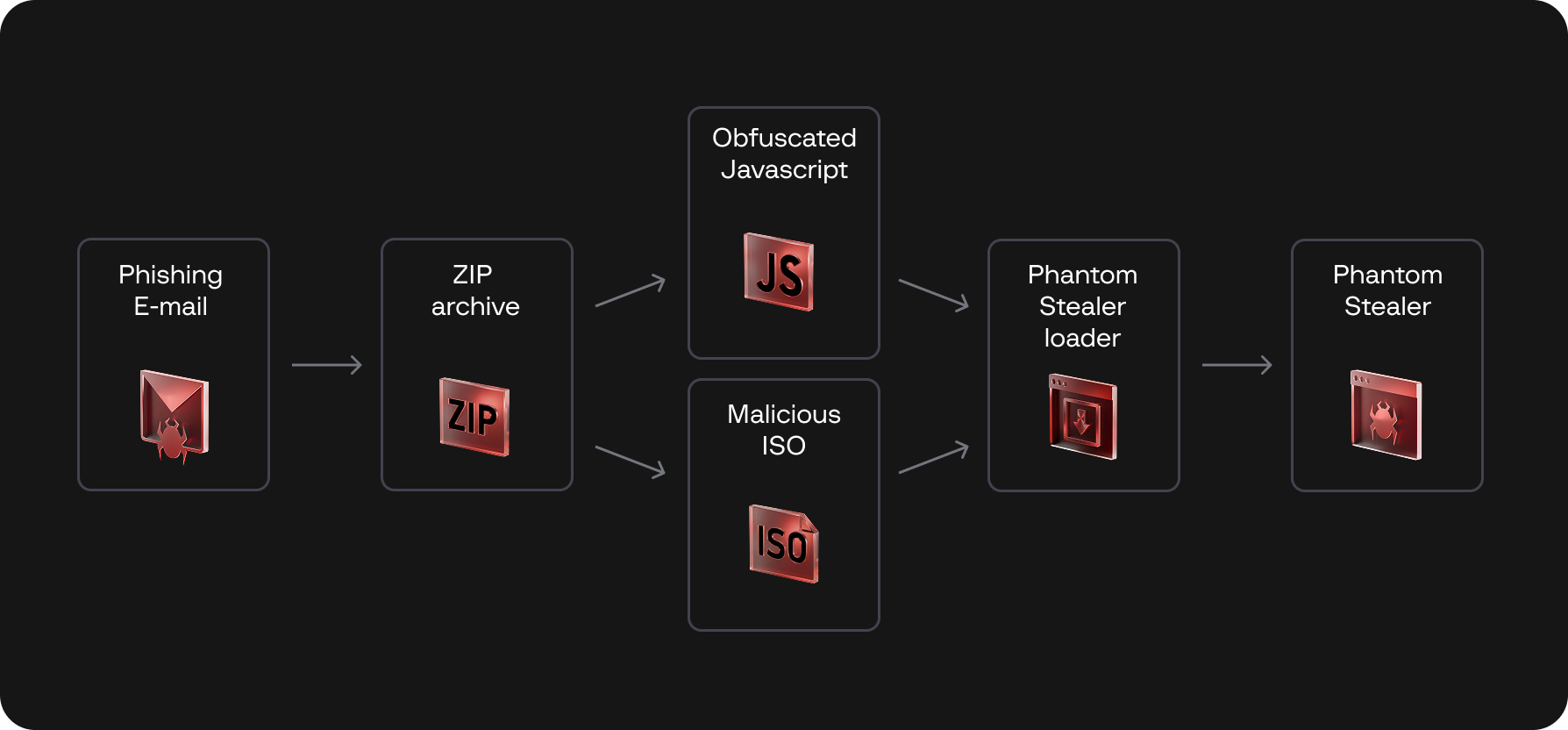
Figure 2. Attack chain from phishing email to Phantom Stealer execution
More information about the recent Phantom Stealer’s attack, related IOCs and phishing indicators, can be found in the Group-IB Threat Intelligence platform.
Email сharacteristics and tactics
Every email originated from the same spoofed sender — impersonating a legitimate equipment trading company. The threat actor maintained this identity across all waves, rotating only subject lines, attachment filenames, and sending infrastructure.
Subject lines followed procurement-themed patterns — RFQ, INQ, ENQ, and PO# references designed to blend with legitimate business correspondence. Each wave used a different subject template, but all carried the same structure: a procurement keyword followed by alphanumeric reference codes.
The body was deliberately short — two to three sentences requesting a quotation — followed by an elaborate professional signature block with full company details, phone numbers, and address. This inverted ratio of body to signature lends legitimacy while evading text-based classifiers. Consistent spelling errors across all waves — “Incase” instead of “In case,” and the missing preposition in “do not hesitate let us know” — point to a single reused template.
Each email carried an archive attachment (.tar, .7z, .zip, or .rar depending on the wave) containing an obfuscated JavaScript dropper or a malicious executable.
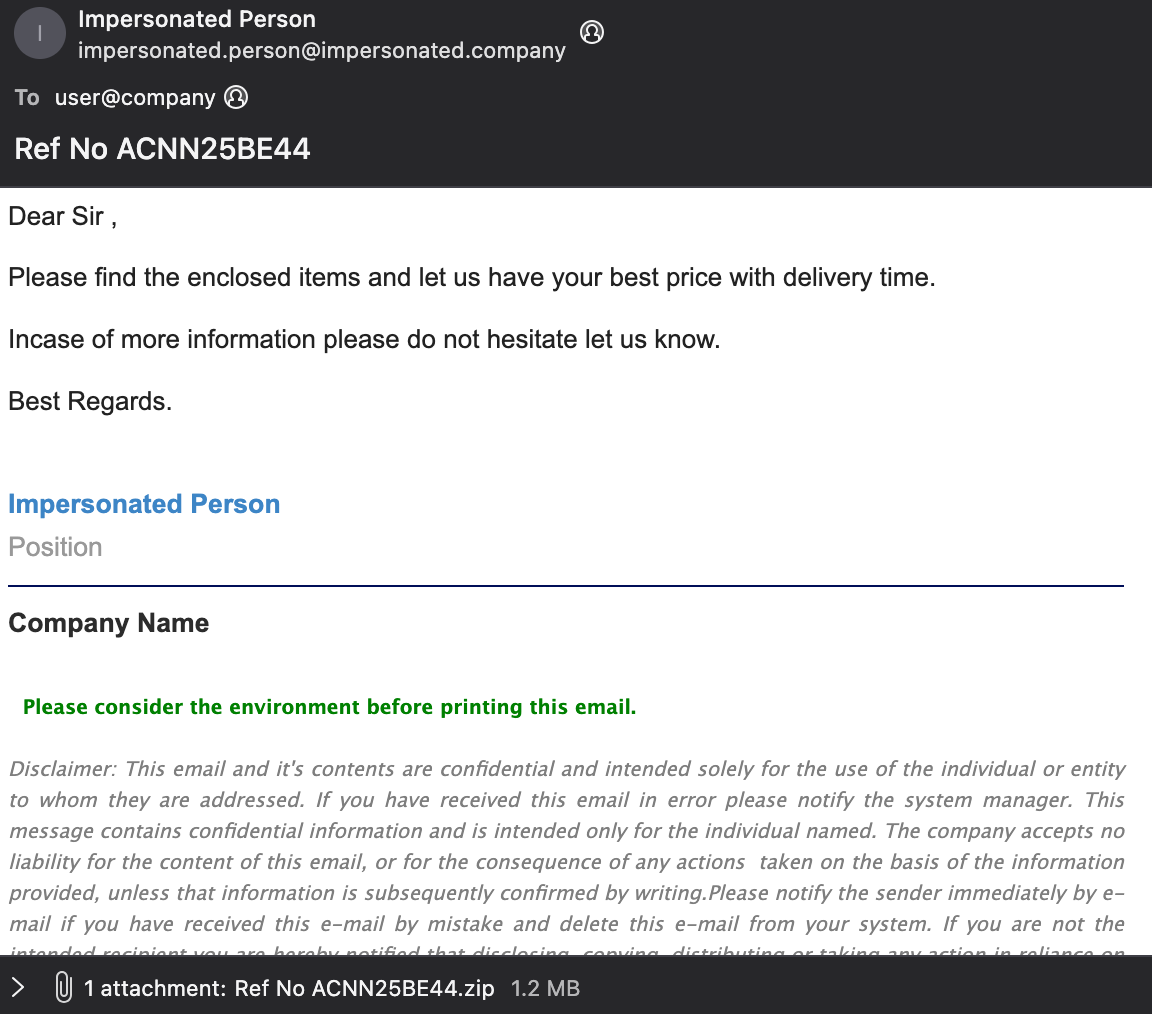
Figure 3. Phishing email with procurement-themed subject
Signs of malicious activity
There are several technical indicators that exposed this campaign:
- SPF failure: The sending IP was never authorized by domain’s SPF record, resulting in a consistent fail verdict across every email in the campaign
- No DKIM signature: None of the emails carried a valid DKIM signature for the claimed domain
- Impersonal greeting with template reuse: “Dear Sir/Madam” greetings and the same body template across every wave, with only reference numbers changed
These indicators — spoofed business identity, authentication failures, and structural fingerprints of automated tooling — mark this as a coordinated stealer delivery campaign.
Indicators of compromise
Domains:
- scxzswx[.]lovestoblog[.]com
- Exczx[.]com
IPs:
- 108[.]171[.]108[.]248
- 216[.]131[.]75[.]250
- 195[.]177[.]94[.]6
- 213[.]209[.]157[.]187
- 185[.]147[.]214[.]250
- 216[.]131[.]77[.]250
- 216[.]131[.]112[.]239
- 104[.]36[.]180[.]119
Detection with Business Email Protection
Group-IB’s Business Email Protection detects and blocks Phantom Stealer delivery campaigns by correlating signals across multiple detection layers.
Our multi-layer detection approach includes:
- Sender and infrastructure analysis: BEP detects SPF failure and missing DKIM for the claimed sender domain, while the Message-ID aligns with the From domain — a structural indicator of a purpose-built impersonation tool rather than a misconfigured server.
- Content and linguistic signals: ML classification, subject analysis, and greeting patterns identified suspicious content reused across waves.
This signal correlation — authentication failures, impersonation detection and linguistic fingerprinting — blocked all Phantom Stealer emails before they reached the inbox, even as the threat actor rotated subjects, archive formats, and sending IPs between waves.
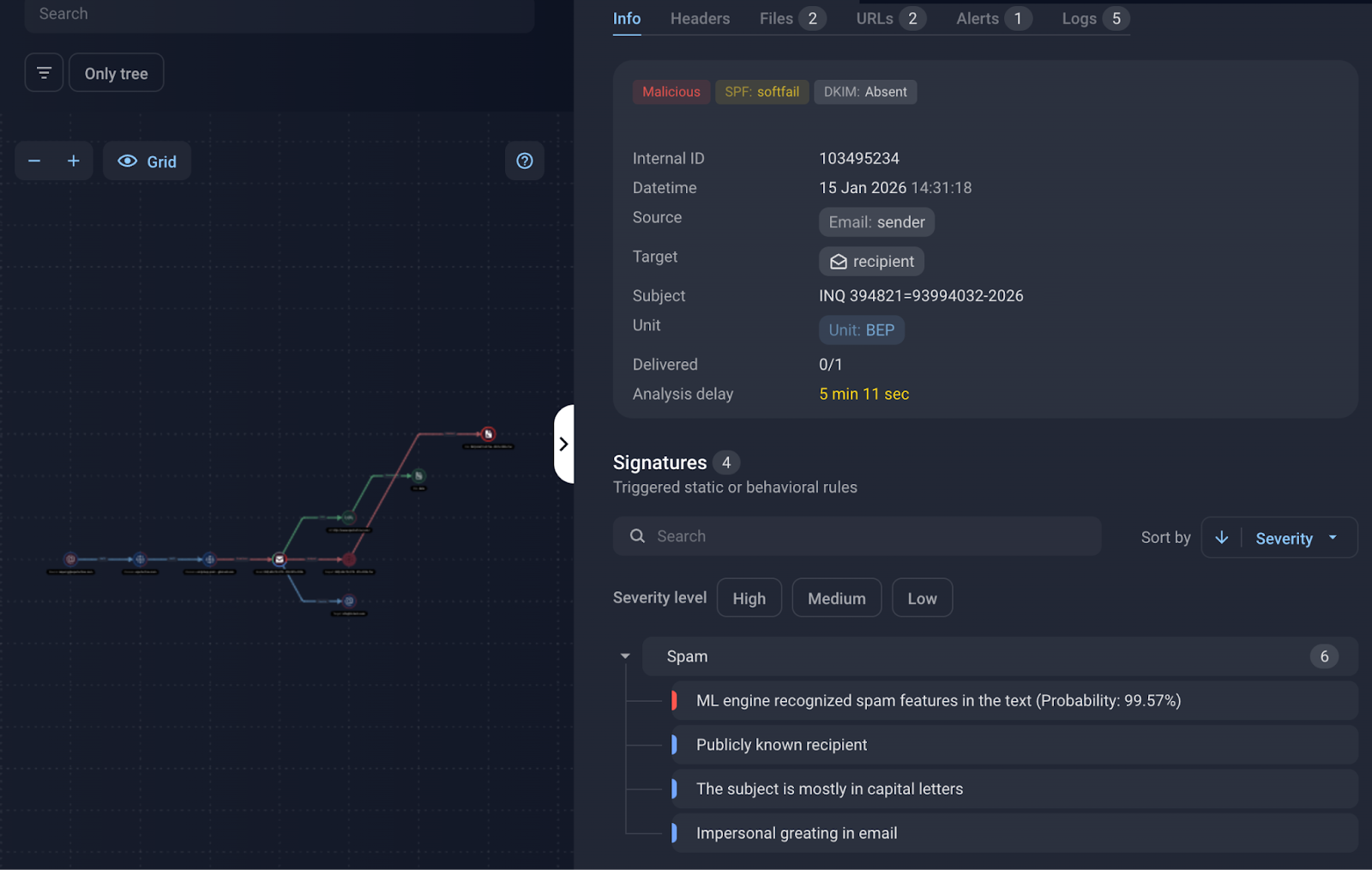
Figure 4. Business Email Protection interface showing detection signals for a Phantom Stealer email
Detection with Malware Detonation Platform
Group-IB’s Malware Detonation Platform (MDP) provides an additional layer by analyzing the Phantom Stealer payload in a controlled environment. When BEP extracts the archive attachment and detonates the dropper, MDP traces the full execution chain — from initial script through staged payload retrieval to the final .NET stealer binary — and returns a malicious verdict.
Across the entire campaign, MDP confirmed malicious behavior on every detonated sample. The platform identified credential harvesting routines, anti-analysis evasion, and data exfiltration attempts, providing definitive classification even when individual email-layer signals carried moderate confidence.
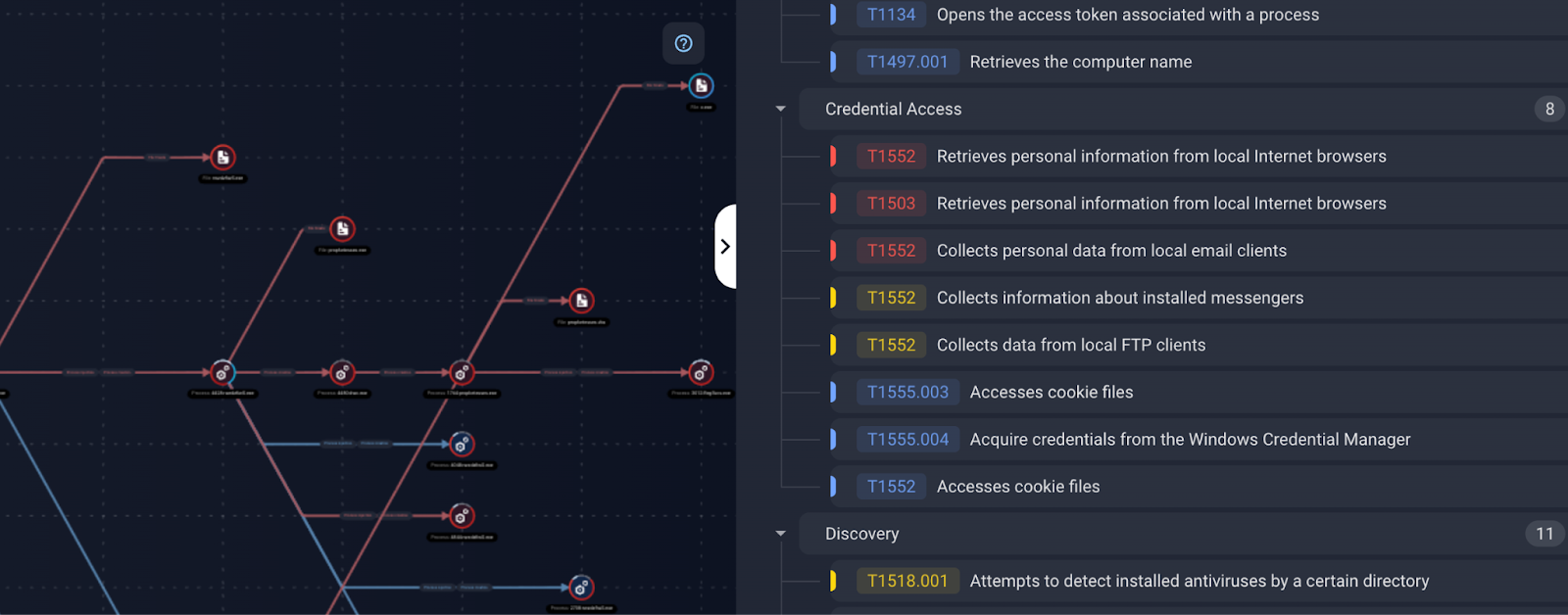
Figure 5. Malware Detonation Platform report showing Phantom Stealer execution chain
Conclusion
Phantom Stealer is one example of a broader pattern: credential theft scaling through commercial stealer-as-a-service operations, where the outcome is identity-driven compromise that often leads to ransomware or business email fraud.
By combining email-layer detection through Business Email Protection with binary-level analysis through the Malware Detonation Platform, Group-IB blocked this campaign at multiple stages — from the phishing email to the payload itself.
Group-IB’s Business Email Protection team continuously monitors emerging supply chain threats, analyzes adversary techniques targeting developer ecosystems, and updates detection models to protect our customers against evolving email-based attacks on critical infrastructure.