Our recent comprehensive report features an in-depth analysis of JS-sniffers’ darknet market, their entire infrastructure and the monetization methods. Group-IB researchers have discovered 38 families of JS-sniffers, whereas only 12 were known previously.
Last two blog posts were dedicated to the analysis of ReactGet and G-Analytics families of JS-sniffers, and this blog post focuses on the Illum family. We discovered that this family of JS-sniffers is capable of injecting fake payment forms and conceal the legitimate payment forms on e-commerce websites.
Meet Illum
Group-IB researchers discovered Illum JS-sniffers family designed to steal payment data of customers of online stores using the injection of fake payment forms that concealed the original payment form on the website and sent filled in credentials to the attackers’ server. While analyzing the activities of Illum operators, we discovered and examined the server for storing their tools and samples of malicious scripts and for collecting the stolen data. Illum is a family of credit card JS-sniffers that was used in attacks on Magento websites.
While analysing the network infrastructure used by cybercriminal group that owns the Illum family, Group-IB discovered several tools used by the attackers: malicious scripts, exploits, and fake payment forms, as well as a list of samples of JS-sniffers linked to rival cybercriminal groups. Based on the registration dates of the domain names used by the group, it is likely that the infection campaign started at the end of 2016.
Description
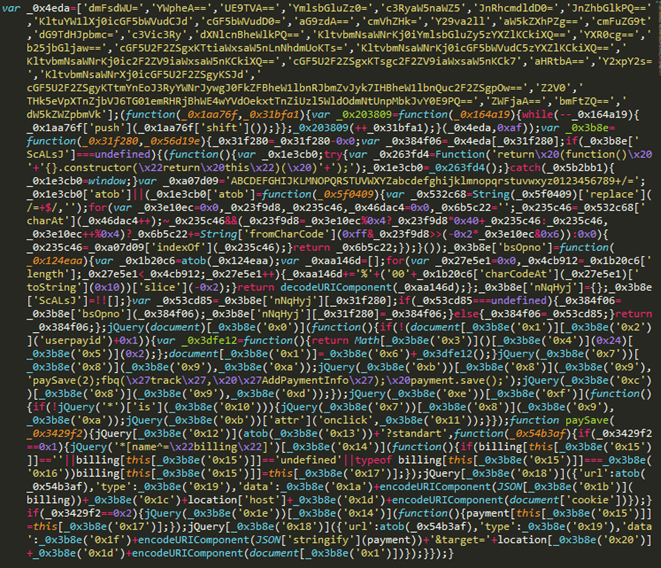
The first detected versions of the Illum JS-sniffer were injected into the client-side source code of a compromised online store. Stolen data was sent to the gate cdn.illum[.]pw/records.php; the gate’s URL address was Base64-encoded.
Our analysts later revealed a packed version of the JS-sniffer from the same family, which used a different gate address: records.nstatistics[.]com/records.php.
According to the post by Willem de Groot, the same gate was used for the JS-sniffer as the one used in an attack on an online store https://www.csu-shop.de/, owned by the German political party CSU.
Analysis of attackers’ server
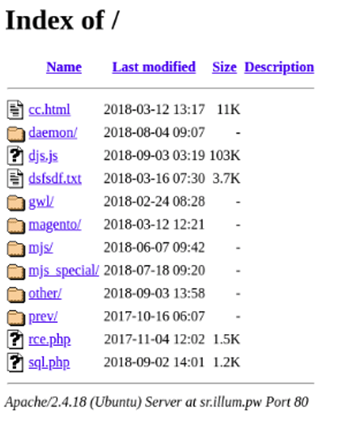
Group-IB researchers detected and analyzed the website that the operators of the Illum family used as storage for tools and scripts and as a gate for collecting stolen credentials.
Among all the tools used by the attackers, our analysts discovered specific scripts and exploits for Linux privilege escalation, for example the “Linux Privilege Escalation Check Script” developed by Mike Czumak, as well as the exploit for CVE-2009-1185.
To carry out the attacks on e-commerce websites, the attackers used two exploits: the first one injects arbitrary code to the core_config_data by using the CVE-2016-4010 vulnerability, while the second one exploits the RCE vulnerability in CMS Magento plugins and executes arbitrary code on the webserver of the Magento website.
Moreover, during the analysis of the attackers’ web server, Group-IB analysts detected various fake payment forms and samples of JS-sniffers. As can be seen from the list below, some scripts were created for a specific online stores, while others were created for specific payment gateways or CMS. For example, the malicious scripts segapay_standart.js and segapay_onpage.js were created to infect websites that use the Sage Pay payment gateway.
| Script | Gate |
|---|---|
| http://sr.illum[.]pw/mjs_special/visiondirect.co.uk.js | //request.payrightnow[.]cf/checkpayment.php |
| http://sr.illum[.]pw/mjs_special/topdierenshop.nl.js | //request.payrightnow[.]cf/alldata.php |
| http://sr.illum[.]pw/mjs_special/tiendalenovo.es.js | //request.payrightnow[.]cf/alldata.php |
| http://sr.illum[.]pw/mjs_special/pro-bolt.com.js | //request.payrightnow[.]cf/alldata.php |
| http://sr.illum[.]pw/mjs_special/plae.co.js | //request.payrightnow[.]cf/alldata.php |
| http://sr.illum[.]pw/mjs_special/ottolenghi.co.uk.js | //request.payrightnow[.]cf/alldata.php |
| http://sr.illum[.]pw/mjs_special/oldtimecandy.com.js | //request.payrightnow[.]cf/checkpayment.php |
| http://sr.illum[.]pw/mjs_special/mylook.ee.js | //cdn.illum[.]pw/records.php |
| http://sr.illum[.]pw/mjs_special/luluandsky.com.js | //request.payrightnow[.]cf/checkpayment.php |
| http://sr.illum[.]pw/mjs_special/julep.com.js | //cdn.illum[.]pw/records.php |
| http://sr.illum[.]pw/mjs_special/gymcompany.es.js | //request.payrightnow[.]cf/alldata.php |
| http://sr.illum[.]pw/mjs_special/grotekadoshop.nl.js | //request.payrightnow[.]cf/alldata.php |
| http://sr.illum[.]pw/mjs_special/fushi.co.uk.js | //request.payrightnow[.]cf/checkpayment.php |
| http://sr.illum[.]pw/mjs_special/fareastflora.com.js | //request.payrightnow[.]cf/checkpayment.php |
| http://sr.illum[.]pw/mjs_special/compuindia.com.js | //request.payrightnow[.]cf/alldata.php |
| http://sr.illum[.]pw/mjs/segapay_standart.js | //cdn.illum[.]pw/records.php |
| http://sr.illum[.]pw/mjs/segapay_onpage.js | //cdn.illum[.]pw/records.php |
| http://sr.illum[.]pw/mjs/replace_standart.js | //request.payrightnow[.]cf/checkpayment.php |
| http://sr.illum[.]pw/mjs/all_inputs.js | //cdn.illum[.]pw/records.php |
| http://sr.illum[.]pw/mjs/add_inputs_standart.js | //request.payrightnow[.]cf/checkpayment.php |
| http://sr.illum[.]pw/magento/payment_standart.js | //cdn.illum[.]pw/records.php |
| http://sr.illum[.]pw/magento/payment_redirect.js | //payrightnow[.]cf/?payment= |
| http://sr.illum[.]pw/magento/payment_redcrypt.js | //payrightnow[.]cf/?payment= |
| http://sr.illum[.]pw/magento/payment_forminsite.js | //paymentnow[.]tk/?payment= |
The domain name paymentnow[.]tk, which was used as a gate in the script payment_forminsite.js, was detected as subjectAltName in several SSL certificates linked to the CDN service CloudFlare. Moreover, this host was used to store a file named evil.js. Based on the script name, we can assume that the file could have been used during the exploitation of CVE-2016-4010, which makes it possible to inject malicious code into a Magento website’s footer. The file named “evil.js” used the host request.requestnet[.]tk as a gate address, which has the same certificate as paymentnow[.]tk.
Fake payment forms
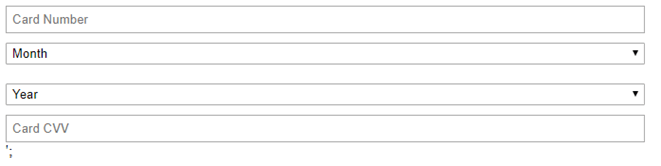
The picture below is a screenshot of a fake payment form that was used during the infection of an e-commerce website with a credit card JS-sniffer. The JS-sniffer steals any information filled into this fake form, while the original form remains hidden.
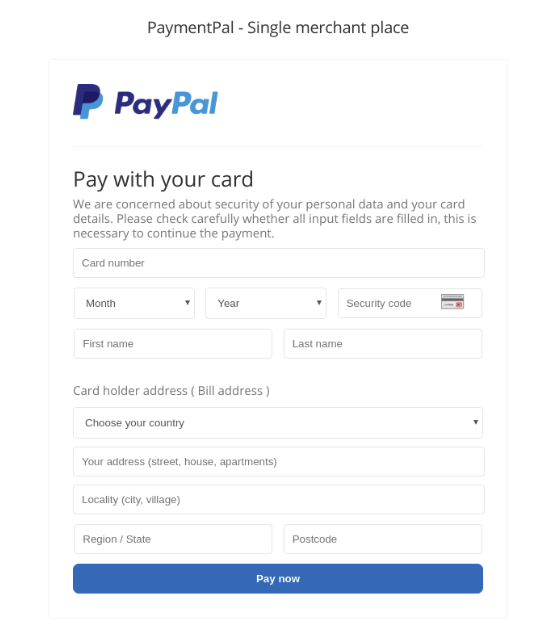
The screenshot below shows a fake PayPal payment form used to infect websites that accept payments via PayPal.
Infrastructure
| Domain | Detection / creation date |
|---|---|
| cdn.illum.pw | 27/11/2016 |
| records.nstatistics.com | 06/09/2018 |
| request.payrightnow.cf | 25/05/2018 |
| paymentnow.tk | 16/07/2017 |
| payment-line.tk | 01/03/2018 |
| paymentpal.cf | 04/09/2017 |
| requestnet.tk | 28/06/2017 |
Crime without punishment: in-depth analysis of JS-sniffers
Group-IB experts have researched this type of malware and have discovered at least 38 families of JS-sniffers, whereas only 12 were known previously.