Windows Prefetch files were introduced in Windows XP and since that time have helped digital forensics analysts and incident responders find evidence of execution.
These files are stored under %SystemRoot%\Prefetch and designed to speed up application startup process. If we look at any of such files, we can see that their names contain two parts: executable name and an eight-character hash of this executable’s location.
Prefetch files contain various metadata: executable name, run count, volume information, files and directories referenced by the executable, and, of course, timestamps. We usually use a Prefetch file’s creation timestamp as the timestamp of the first execution, also it has embedded timestamp of the last execution, and since version 26 (Windows 8.1) – seven previous last run times.
Let’s take one Prefetch file, parse it with Eric Zimmerman’s PECmd, and look at each part of the output. For demonstration purposes I’ll parse CCLEANER64.EXE-DE05DBE1.pf.
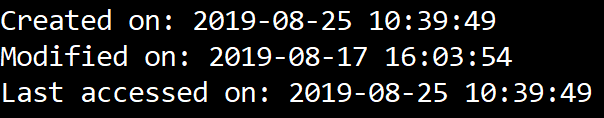
Ok, I’m going to start from the top. First of all, we have file’s timestamps:
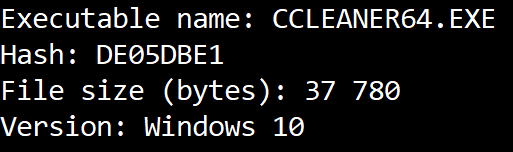
Next we have the executable’s name, it’s path’s hash, the executable’s size and Prefetch file’s version:
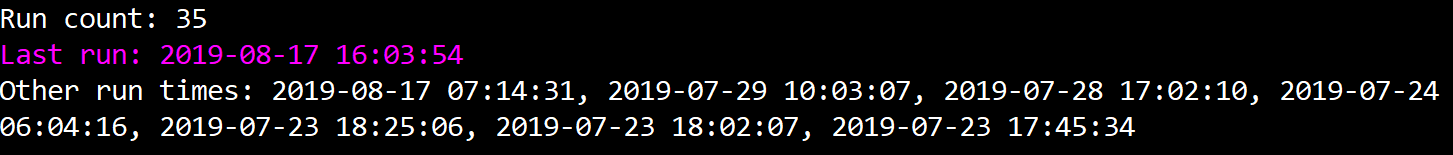
As we have Windows 10 version, next we see the run count, last run timestamps and seven more previous last run times:
Next, we can see the information about the volume, including its serial number and creation timestamp:
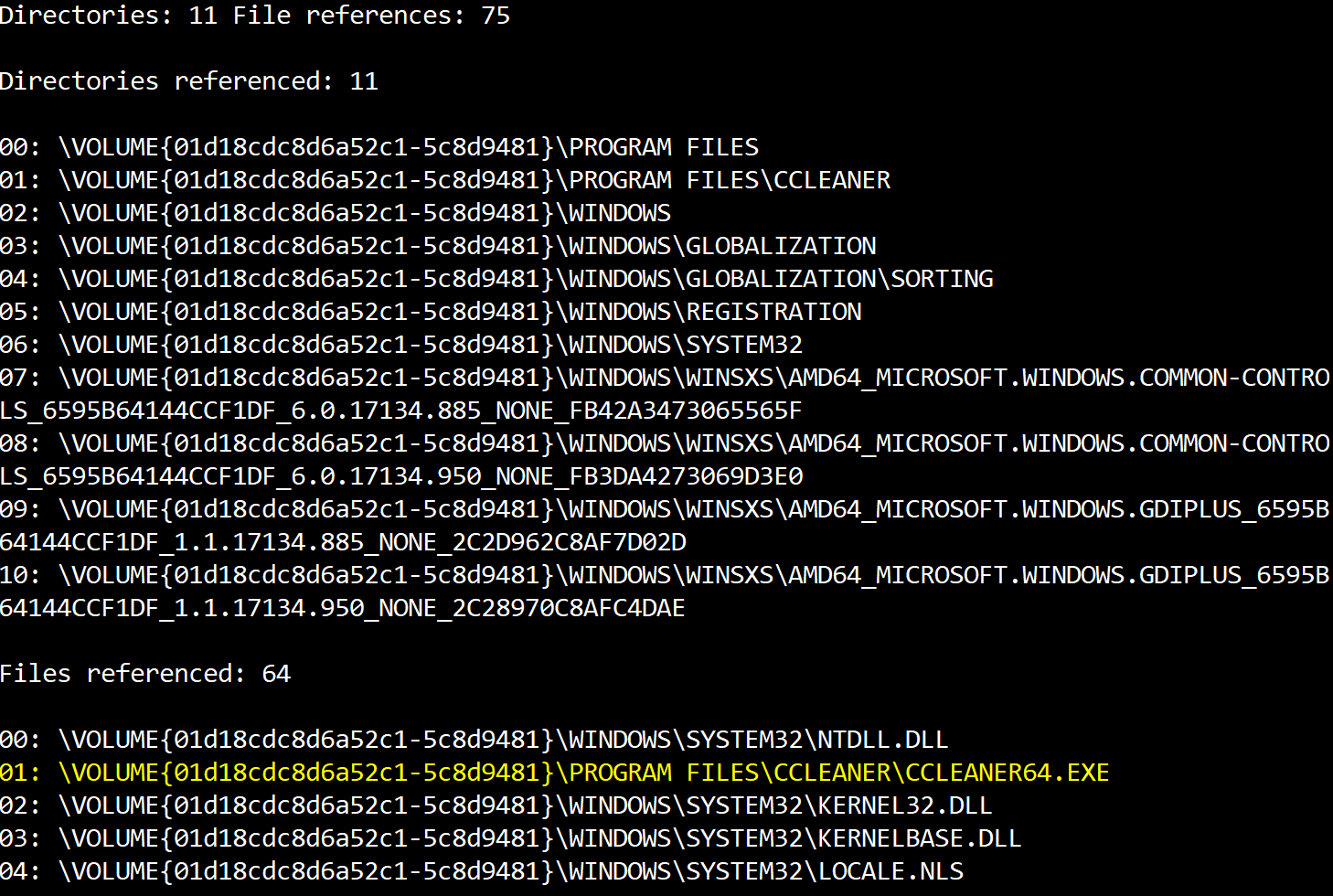
And last, but not least – referenced files and directories:
So, files and directories referenced by the executable is what I want to focus on today. This feature enables us as digital forensic analysts, incident responders or threat hunters to track not only facts of execution of this or that, but also, in some cases, exact techniques used by adversaries. Attackers use data wiping tools, like SDelete, quite often nowadays, so ability to find at least traces of different tactics and techniques usage is a must-have skill for any modern defender.
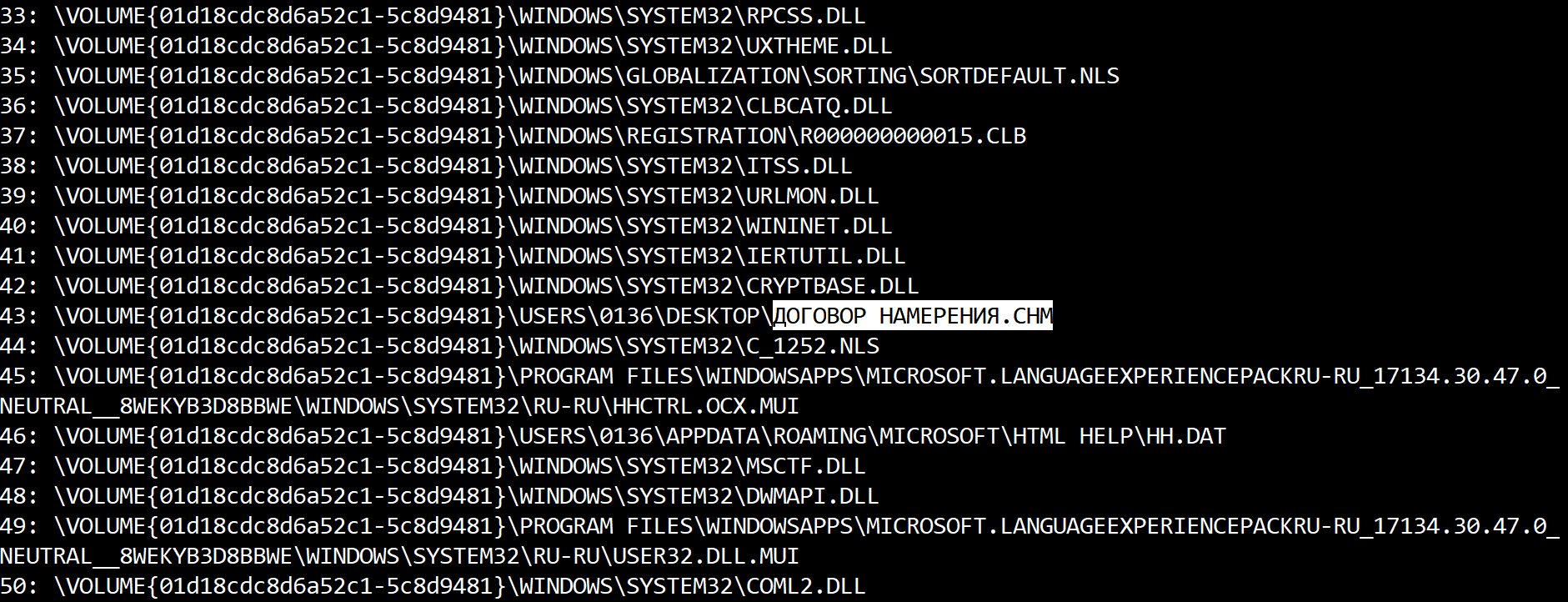
Let’s start from the Initial Access tactic (TA0001) and the most common technique – Spearphishing Attachment (T1193). Some APT groups choose weaponized attachments in a creative way. For example, Silence Group used weaponized CHM files in their spear phishing campaigns. Here another interesting technique – Compiled HTML File (T1223). These files are run with hh.exe, so if we parse its Prefetch file, we can understand what exactly was opened by the victim:
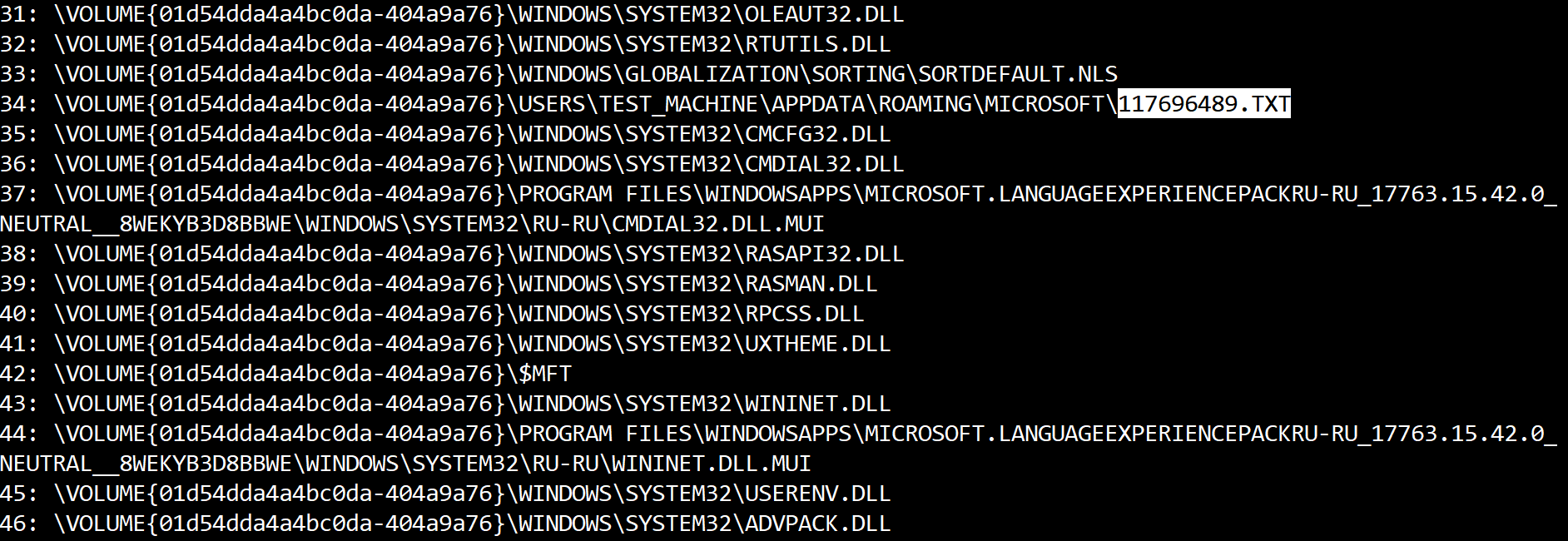
Let’s keep digging into real-world examples and continue to the next tactic – Execution (TA0002), and CMSTP (T1191) technique. The Microsoft Connection Manager Profile Installer (CMSTP.exe) may be used by attackers for launching malicious scripts. A good example is Cobalt Group. If we parse CMSTP.exe‘s Prefetch file and look at Files referenced section, we can find what exactly was run with it:
So here we have a JavaScript scriptlet saved into 117696489.txt that was run by attackers with CMSTP.
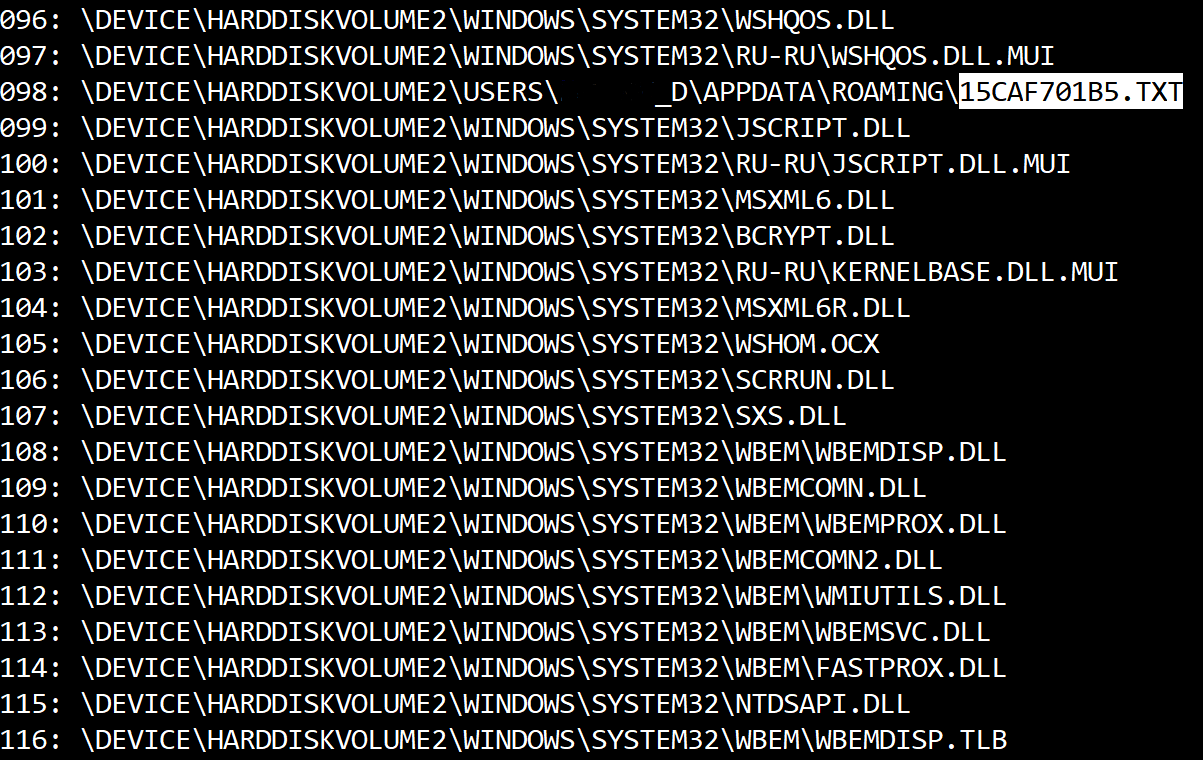
Let’s continue with execution examples – Regsvr32 (T1117). Regsvr32.exe is commonly used by attackers to execute arbitrary binaries. Here is another example from Cobalt Group – these guys used regsvr32.exe to run scripts, so, again, if we look inside the Prefetch file of this executable, we can find the location and name of the executed script:
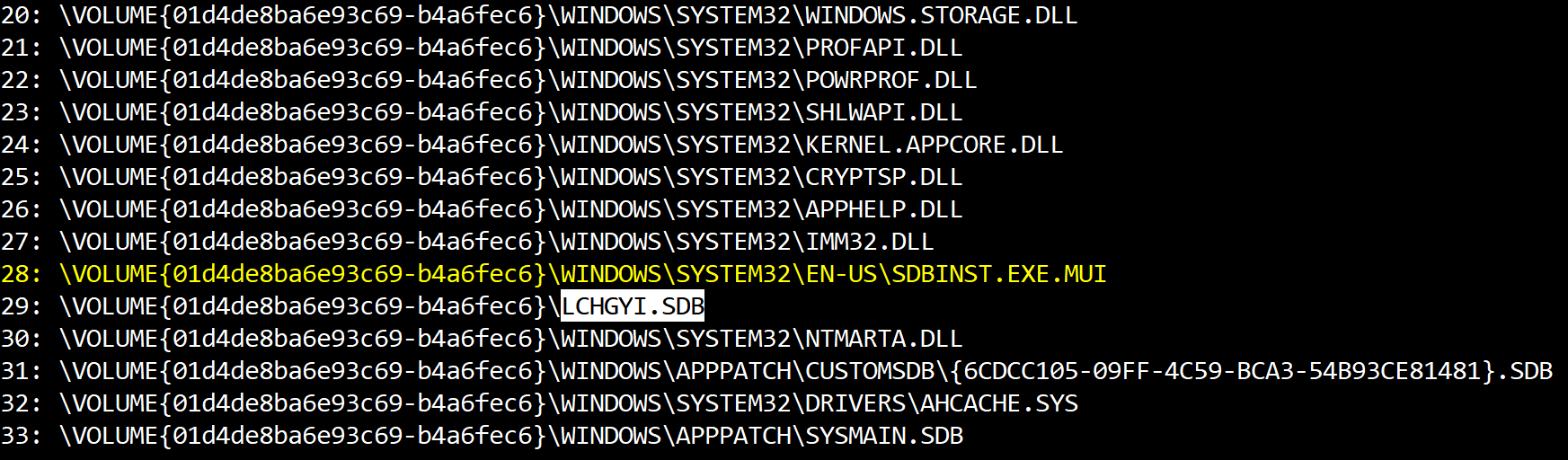
Next tactics – Persistence (TA0001) and Privilege Escalation (TA0004), and Application Shimming (T1138) as an example. This technique was used by notorious Carbanak/FIN7 for persistence. Usually sdbinst.exe is used for working with shim database files (.sdb), so we can use its Prefetch file to uncover databases file names and locations:
Here we have not only the file used for installation, but also the name of installed custom database.
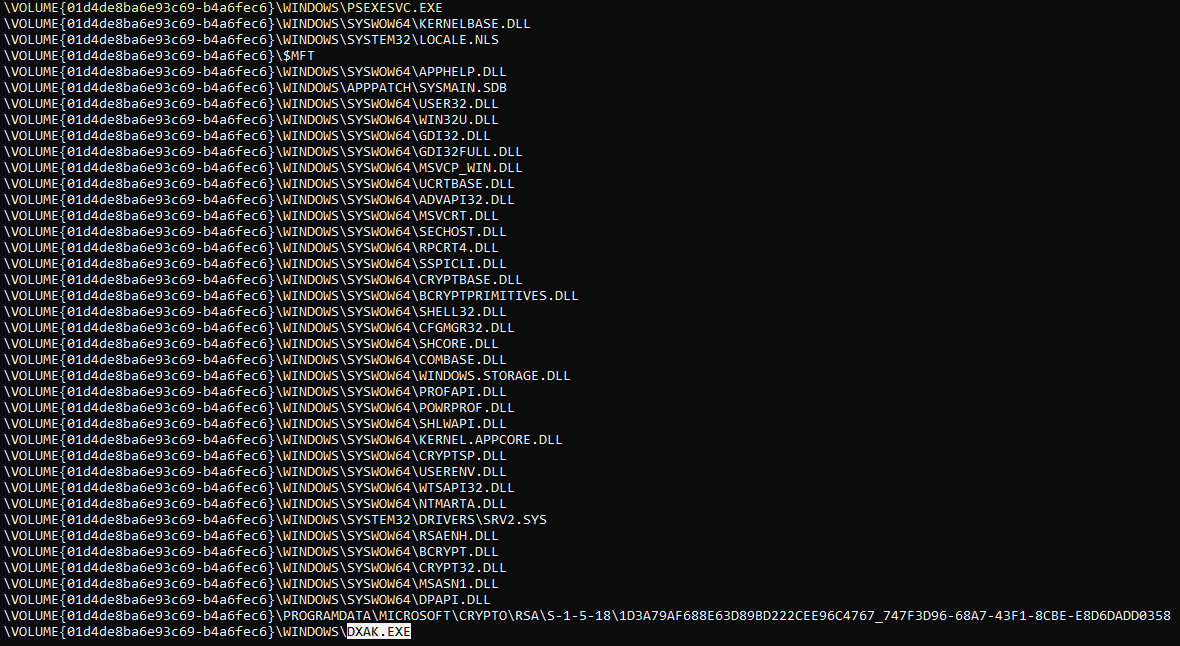
Let’s keep going and look at one of the most typical examples of lateral movement (TA0008) – PsExec, which interacts with the ADMIN$ network share (Windows Admin Shares, T1077). A PSEXESVC service (it may have random name, of course, as it can be renamed by the attacker using –r switch) will be created on the target system, and if we parse this executable’s Prefetch file, we can see what exactly was run:
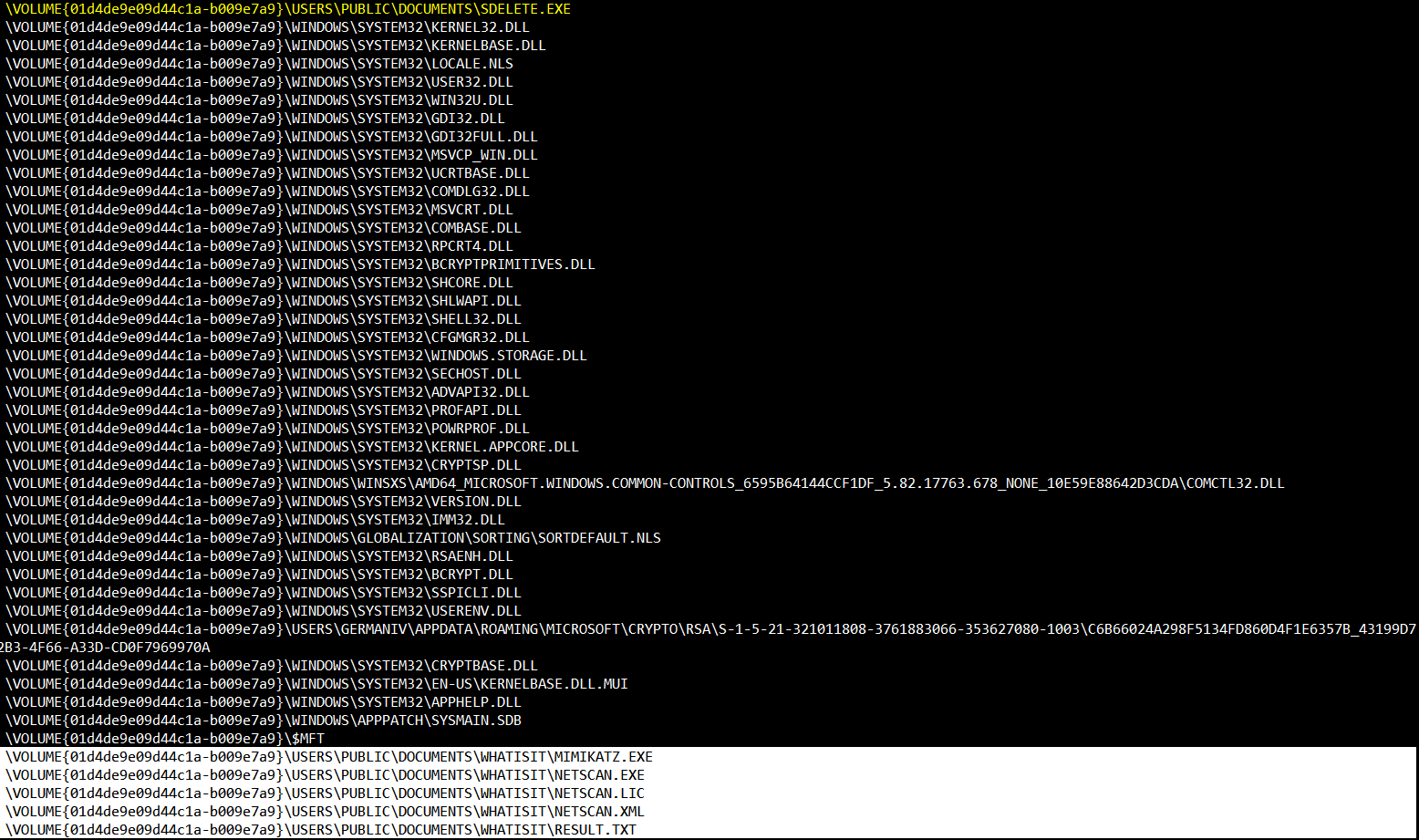
Let’s finish with what we started from – file deletion (T1107). Many adversaries use SDelete utility to remove software they used during a number of stages of the attack lifecycle. If we look at sdelete.exe Prefetch file, we can clearly see what was deleted with the help of it:
Of course, it’s not the whole list of techniques that can be found as the result of Prefetch files analysis, but it should be enough to understand, that such files can be used not only for finding evidence of execution, but also for uncovering exact tactics and techniques used by the adversary.
Benefit from the fastest incident response from industry leaders
Group-IB Incident Response experts apply the most up-to-date knowledge about the threat landscape