Introduction: Cybersecurity and business still seem to align more in conversations than in reality
Cybersecurity is widely discussed at the boardroom table, but integrating it into the broader business context is where the gap lies: it shows up in uninformed security investments and decisions, misaligned business expectations, increased threat exposure without threat prioritization, and a lack of shared understanding of the current vs. desired security posture.
So, how do you build a concrete cybersecurity strategy that not only defines the vision but also shows you how to achieve it? This is one of the core themes discussed in Gartner’s publicly available Cybersecurity Strategy insights. Below, we build on the thinking behind that cycle with Group-IB’s own interpretation of what each stage means in practice, and where most organisations fall short.
Group-IB’s interpretations of each theme
After a breakdown of the core planning cycle, which outlines the essential steps for effective cybersecurity planning, we now examine the key themes, all designed to help organizations overcome challenges in developing strategies for the present year and beyond.
1) Cybersecurity as a significant business risk
Our breakdown
Businesses’ needs and priorities shift in real time, while security comes later, as a control layer that’s checked on, perhaps, quarterly/biannually/annually. What we’re left with is a gap in board-level understanding of cybersec planning vs operational disconnect.
Cybersecurity becomes a cost center when you can’t envision and account for its impact on the business. Thus, the need to align security planning and proposed actions with the business context (which includes business, technological, and environmental drivers) is crucial.
The real-life situation today’s leaders face
Cybersecurity planning and implementation today mostly focus on checklist items or basic hygiene measures for compliance and monitoring. Threat-context planning takes a backseat due to its continuous, time-sensitive, and resource-intensive nature. Businesses fall short in conveying shifts (M&As, technology rollouts, legal and regulatory, product, brand growth and adoption, etc.) in real-time, leading to misalignment and inconsistent planning.
Our take on orchestration
Oftentimes, during strategy planning meetings, security teams are asked generic questions such as “how secure are we?”, answers to which are far more complex. To address them precisely, there should be prior discussions:
- Cross-team brainstorming to understand different departments’ objectives, risk dependencies, and plans. Their responses can then be mapped to threats, controls, and priorities.
- Training teams to be more business-aligned and set controls to support business (especially incorporating key drivers as discussed) and high-priorities (identities, assets, and infrastructure changes that need security).
- Proper assessments need to be conducted, and insights gained need to be leveraged to strengthen defenses.
2) Security objectives need to be widely accepted and communicated
Our breakdown
Security objectives need to be cascaded across the board in a way that they’re clearly understood and are non-objectionable. As security planning becomes more business-oriented, proper resource allocation, support, and prioritization goals can then be established.
The real-life situation today’s leaders face
Although cyber and business should speak the same language, establishing the lingua franca isn’t easy. Not all teams are technically fluent, so risks that might come with adopting a new application (vulnerabilities in SaaS solutions, PII exploitation, risks of open ports and connections to third-party software) and their prioritization might be difficult to grasp.
Our take on orchestration
To achieve company-wide understanding, consensus, and alignment, the security team needs to flip the script and convey how each activity impacts brand, revenue, and shareholder value. Ask questions like: What business process is dependent on this SaaS? If exploited, does it leak M&A documents, customer PII, or trade secrets? What would it take to mitigate it, and what would the cost be? Can the current team handle it, or does it need partner intervention?
3) Gap analysis of current vs desired security state
Our breakdown
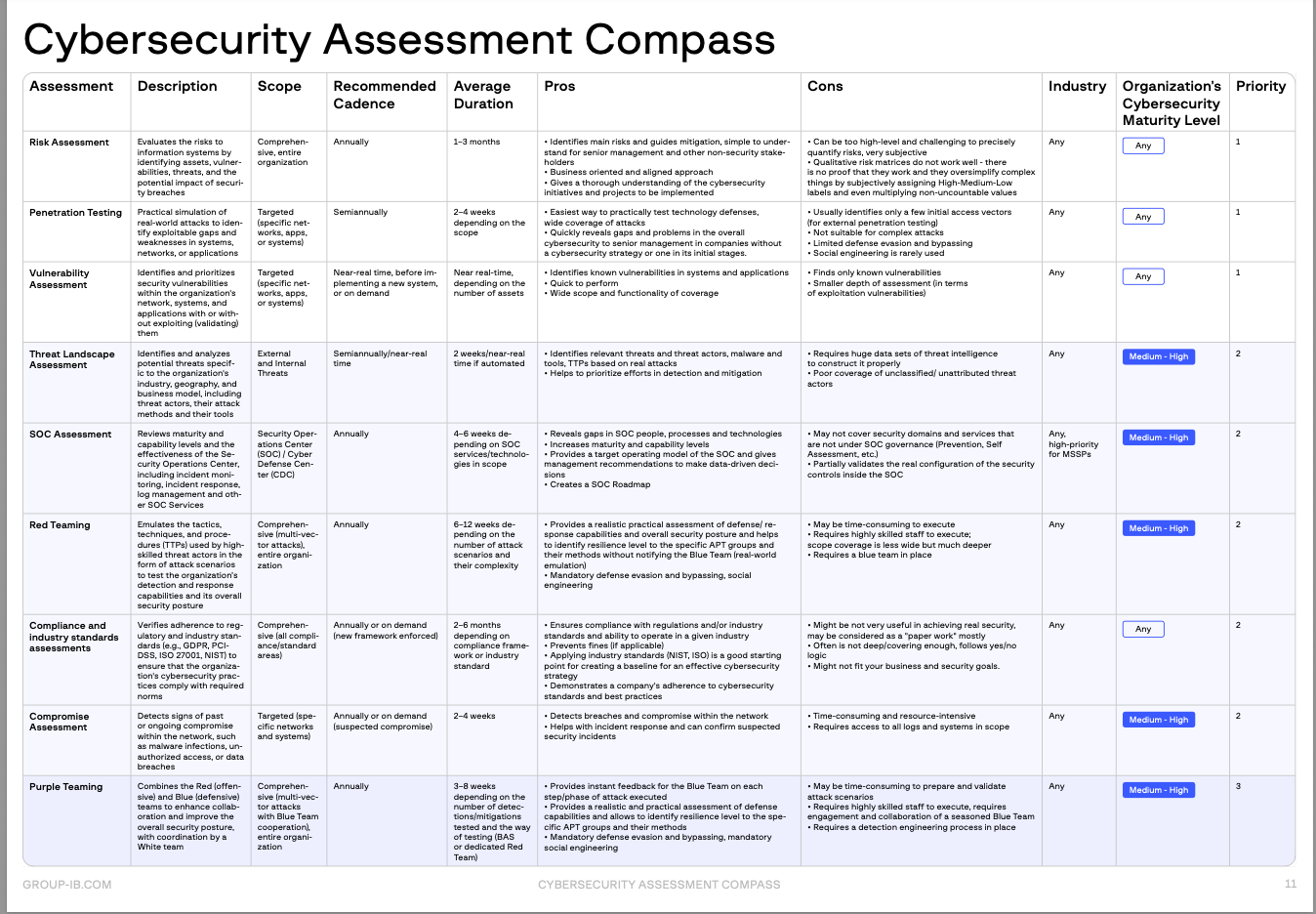
Multifaceted assessments are required to provide a clear, accurate picture of your security program and its effectiveness across business domains such as operations, people, and infrastructure. The assessments must include, but are not limited to, vulnerability assessments, risk assessments, audit, and consulting for control effectiveness.
This helps businesses identify critical gaps between the current state and the vision statement. However, while some clear actions can be derived from gaps, some aren’t that straightforward — this requires stakeholders to sit in prioritization exercises.
The real-life situation today’s leaders face
Some gaps, often related to processes or resources, are difficult to explain to the board and are therefore deprioritized and undervalued. They may be seen as unnecessary overhead: more paperwork, another checklist item, rather than directly impacting risk reduction.
Our take on orchestration
While some gaps have clear, measurable outcomes, others require more than just technical fixes. Gartner uses the term “governance maturity” to describe how well an organization makes and owns security decisions in line with business risk. It’s not something you can solve with a single tool or framework. Improving maturity affects risk appetite, security culture, and training. Leaders need to clearly define what maturity means for their organization, what changes in process or behavior are required, and what outcomes the business expects from that improvement.
For any type of gap, framing must begin with exposure and cost, followed by clear, measurable outcomes. Convey the cost of inaction through real-world incidents and internal audit findings. For example: “In 2023, a peer bank lost $1.2M due to misrouted phishing responses, caused by unclear ownership and response/escalation workflows. That’s exactly what this fix addresses.”
When measuring initiatives, choose frameworks such as CMMI or Gartner’s IT Maturity Scale, feedback scoring surveys for CISOs, department heads, and risk owners, and business impact analyses.
4) The need for modular cybersecurity planning
Our breakdown
The business moves, but security doesn’t. That’s a major gap and a big reason why most strategies fall short. Cybersecurity leaders must tailor the planning process to the changing organization’s people, processes, and resources. This includes a modular roadmap that can be adapted to respond to real-world threats, changing priorities, maturity, and capacity.
How do we do it? Instead of building and delivering a single, comprehensive plan, break the strategy down into modules (each having a different owner and focus), allowing teams to develop, update, or prioritize based on their discretion.
The real-life situation today’s leaders face
A modular strategy sounds vague unless broken down into clear actions for each team. Adaptive security planning is challenging as security plans do not move consistently with the business. With longer budget and approval cycles, leaders are locked into linear plans, creating misalignment.
Our take on orchestration
Threats move fast. Modular planning helps you pivot fast when threats, regulations, or priorities change. An example of such modules could include separate security initiatives such as identity and access security, email security, fraud prevention, detection, and analytics, or cloud security, supported by planning artefacts like roadmaps, assessments, and metrics.
These security initiatives can be worked on independently while remaining interoperable. Each module has an owner, a maturity level/score (e.g., Identity & Access = Level 2, Email Security = Level 4), and a purpose within the overall defense strategy. Actions can be split between short-term (for the budget) and long-term (for the board, investors). What you get is an adaptive strategy where only 1–2 modules need updates per quarter.
Let your CTI drive modular pivot points by continuously monitoring shifts in the threat landscape and re-evaluating accordingly.
5) Avoiding over-dependence on frameworks and benchmarking
Our breakdown
While benchmarking offers a general perspective for reference, strategies should be built on unique cultural and business needs. Security frameworks like ISO 27001, NIST CSF, or CIS help you build controls, ensure governance, and identify and manage risk, but they’re insufficient in ensuring resilience.
The real-life situation today’s leaders face
Businesses are concerned with regulatory protocols, certifications, and governance compliance. Even if, as security leaders, we want to move toward threat-informed, risk-prioritized strategies, we’re still routinely asked: “Are we aligned with ISO/NIST?” and not “Are we protected against the threats that matter most?”
Our take on orchestration
You can be compliant and still be critically exposed. This is why there needs to be a shift from asking “Are we aligned with ISO/NIST?” to “Are we protected against the threats that matter most?”
Frameworks give you structure. Benchmarking gives you a sense of where you stand relative to peers. But neither tells you what specific threat actors are targeting your industry, your region, or your infrastructure right now. That requires tailored threat intelligence applied to the strategy, not consulted afterwards.
6) Quarterly planning and progress reporting for cybersecurity programs
Our breakdown
There are various methods to document and review progress, ranging from balanced scorecards, Governance, Risk, and Compliance (GRC)-generated reports, and in-house developed dashboards that offer outcome-driven metrics. Be clear about:
- expected benefits that were fully or partially realized
- expected benefits that were not realized
- unexpected benefits materialized
- unexpected issues or disadvantages materialized
- projects on which the jury is still out
- triggers to security responses or challenges that might require a change to the strategy
The real-life situation today’s leaders face
Strategic review and tracking, especially if you’re a business that is understaffed and stretched thin, is not an operational reality. Strategy review and progress reporting require unified security views, after-support, and constant adaptation. Also, converting metrics and improvements into numbers that matter to executives is essential, but GRC tools and scorecards are too generic to capture that.
Our take on orchestration
Most businesses find it hard to support strategic reviews, but it is doable if, just like the planning process, reporting is modularised: per region, vertical, or business unit. This ensures technical findings are easier to translate, act on, and justify, all of which lead to operational improvements.
Discussion-based simulation tabletop exercises (aimed at enhancing the incident response and crisis management capabilities of the end user) can be conducted across multiple organizational levels to pressure-test the strategy in real conditions.
If not done in-house, businesses can also benefit from advisory services on posture gaps, project roadmaps, and prioritization of security initiatives based on threat landscape shifts.
From strategy to enablement: What support do you need to turn insights into action?
Should you build the planning processes entirely in-house, hire an external consultancy to do the heavy lifting, or look for vendors with niche expertise in specific areas? The honest answer is that it depends on where your gaps actually are.
Consultants provide a nuanced external view — broader threat landscape insights, attack trends, benchmarking against peers, recommendations on tools and vendors, policy frameworks, and support with specialized capabilities like migrations or posture assessments. But strategy must come from within. Your internal teams understand shifting operational realities, business priorities, and company culture better than anyone else. Consultants can support the process, but implementation and execution are where misalignment and lack of ownership most often appear.
Another critical factor is limited customization. General advisory firms can diagnose problems, but rarely have the threat intelligence infrastructure to tell you what’s actually coming for your industry, your region, and your infrastructure right now.
A Group-IB suggested approach: businesses must continuously assess and evolve their security posture to keep pace with shifting threats and business goals. Planning, resourcing, prioritization, tooling, and investing, adopting new services, or addressing infrastructure changes – they should be tied to business reality (goals, risks, and operational shifts), and mature with business.
Your first priority should be focusing on core, high-stakes operations and assets, then identifying gaps with expert-led assessments. Group-IB’s Assessment Compass helps you identify where you are today—and what you need to overcome future security complexities.
Based on assessment findings, you not only build implementation plans and strategy roadmaps, but it also serves as a communication tool.
Group-IB generates a dynamic Threat Landscape (which is a part of the “environmental drivers” mentioned previously) from our proprietary Threat Intelligence, focusing on the most relevant threats, actors, and TTPs. Our methodology aligns seamlessly with the MITRE ATT&CK framework, ensuring precision and relevance.
While Gartner’s guidance focuses on orchestration, modular planning, and improved visibility today, many organizations are already exploring how these foundations can evolve toward more predictive, intelligence-led defense models as threat complexity continues to accelerate.
To understand how shifting drivers translate to risks for your business and plan your cybersecurity to build real resilience, reach out to our experts here.
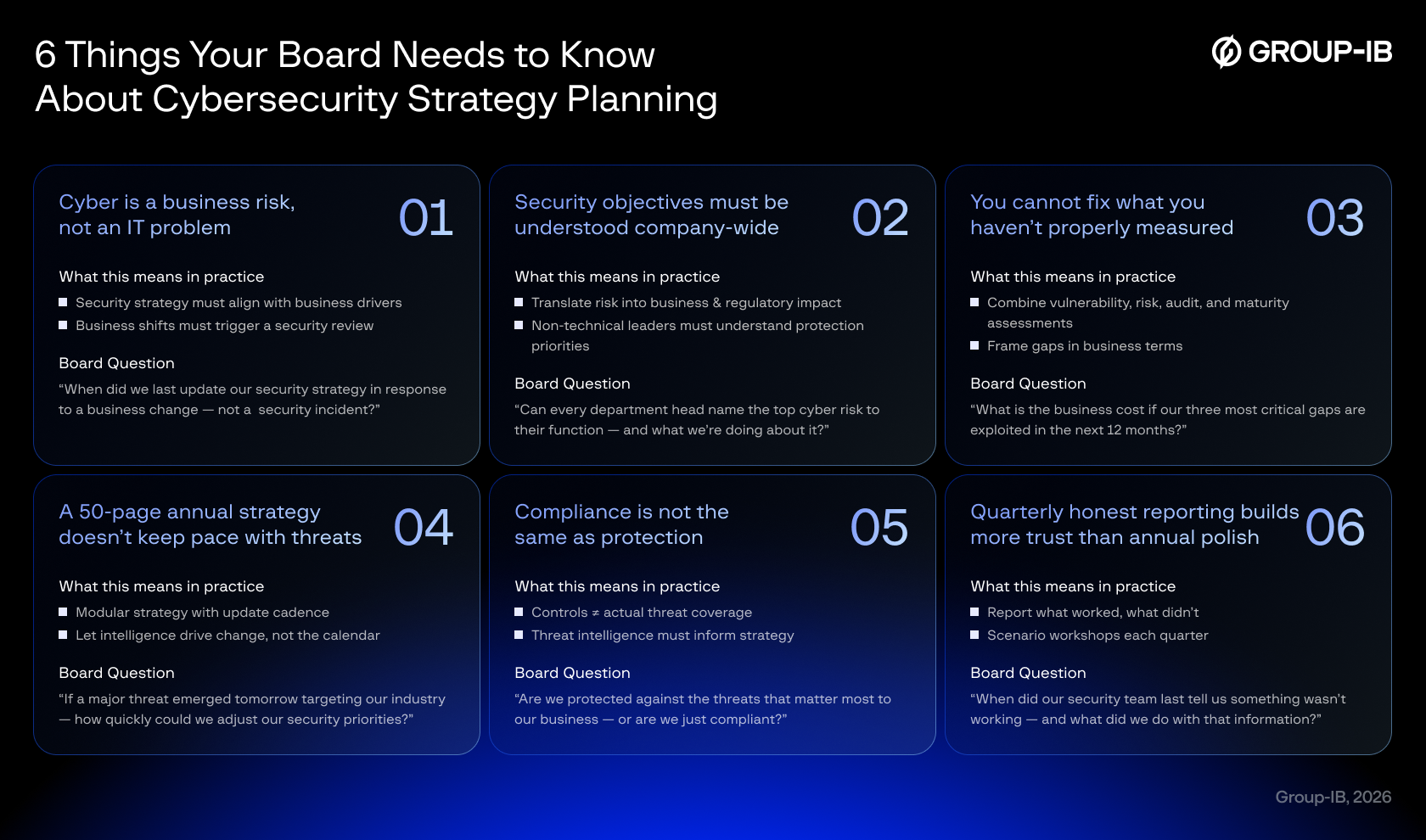
Important handout
Use this infographic in your next board meeting to thoroughly go through the key themes to convert abstraction into an action plan and build a future-proof cybersecurity strategy for the year.
FURTHER READING
For deeper reading on cybersecurity strategy planning best practices, we recommend: “Cybersecurity Strategy Planning Best Practices,” Gartner, Inc. | G00829823 | Tom Scholtz, Will Candrick, Richard Addiscott | May 2025
Available to Gartner subscribers at gartner.com