Introduction
What began as a simple scheme to inflate social media metrics has evolved into a sophisticated threat that is quietly reshaping the economics of digital fraud. Over the past decade, fraud prevention teams have invested heavily in device fingerprinting and emulator detection and that investment paid off; classic emulators and bot activities became predictable, easy to detect and block. However, attackers adapted. They moved to cloud phones – remote-access Android devices running in data centers. For all intents and purposes, these are real phones, running genuine firmware, exhibiting natural sensor behavior, and presenting valid hardware attestation. Plus, they’re accessible to anyone with just $10 to spare and an internet connection. What makes this threat unlike any other is its invisibility. To fraud detection systems, cloud phone activity such as mobile banking appears indistinguishable from a legitimate device.
This report traces the evolution of cloud phones from harmless social media engagement automation to industrial-scale financial fraud, examines why traditional device fingerprinting fails against cloud phones, and reveals updated detection methodologies that are beginning to close this dangerous gap.
Key discoveries
- Cloud phones are significantly harder to detect than emulators as they present realistic hardware configurations, valid identifiers, and plausible system properties.
- Cloud phones now facilitate industrial-scale dropper account creation worth £485.2 million in APP (Authorized Push Payment) fraud losses in the UK alone for 2023.
- Dropper accounts created and maintained on cloud phone instances can preserve consistent device telemetry, bypassing traditional device-change detection mechanisms in banking environments.
- Major cloud phone platforms like LDCloud, Redfinger, and GeeLark offer device rentals for as little as $0.10-0.50 per hour, making fraud infrastructure accessible to anyone with minimal capital investment.
- Darknet markets actively trade pre-verified dropper accounts created on cloud phones, with Revolut and Wise accounts priced at $50-200 each, often including continued access to the cloud phone instance.
Who may find this blog interesting:
- Cybersecurity analysts and corporate security teams
- Malware analysts
- Threat intelligence specialists
- Cyber investigators
- Computer Emergency Response Teams (CERT)
- Law enforcement investigators
- Cyber police forces
Group-IB Fraud Intelligence Portal:
Group-IB customers can access our Fraud Intelligence portal for more information about the credit fraud scheme described in this blog.
How It All Began
The business of “likes”
Social media has long since become a fully-fledged attention infrastructure. Brands are built here, businesses are launched, political narratives are shaped, and career paths are forged. In such an environment, the metrics of “popularity”— followers, likes, and views — become currency. The earliest methods of social media promotion were simple, involving manual viewing, liking, and subscribing, but these tasks were quickly automated and turned into a separate industry.
Multiple accounts, one person
The emergence of multi-account management on social media was a significant milestone. A single person could create multiple accounts using just one device. This allowed for massive activity without involving others. It quickly became clear that this scheme needed to be blocked. Companies learned to easily identify cases of large numbers of accounts appearing on a single device. This was made possible with the help of the device’s unique technical fingerprints. As a result, many apps adopted a similar rule limiting the number of accounts that can be created or managed on one device. While it is possible to purchase a large number of physical devices to overcome this restriction, it’s often not worth the trouble…or cost.
Mobile sandboxes and emulators

Figure 1: Example of mobile sandbox and emulators originally designed as developer testing environments.
Why buy real devices if you can create virtual, fake ones? This is where tools originally created for testing have come to be exploited. Emulators allowed the creation of a huge number of virtual devices and the effective automation of interactions with any application. In turn, virtual environments allowed for the installation of multiple applications on a single device. In Sandbox and virtual environments, emulators started replacing physical devices. Fraudsters no longer needed to rely on a single device to manage multiple accounts and could effectively create multiple virtual devices and set up separate accounts on each of them.
Protection measures caught up
However, such sandboxes and emulators introduced their own detection vectors that proved to be easily identifiable too. Emulators often report suspicious hardware configurations, such as x86 processors on devices claiming to be ARM-based, unusual CPU architectures, or GPU models that don’t exist in any real phone. Touch event timing, accelerometer noise patterns, and sensor fusion characteristics all differed measurably from real physical devices. The file system structure of an emulator contained revealing signs as well, with the presence of emulator-specific binaries serving as major giveaways. Major platforms started deploying emulator detection at scale and their detection rates for common emulators approached 95% or higher, making emulators increasingly impractical for large-scale fraud operations.
The Emergence of Virtual Phone Farms and Cloud Phones
The next wave of fraud came with virtual phone farms that were actual physical “phone farms”. These initially comprised racks of real Android devices used for app installs, sending/receiving SMS, ad fraud, and as social media bots. These farms could scale to thousands of physical phones connected via USB hubs for centralized control. These were genuine devices with authentic IMEIs, real sensors, and full radio stacks which were difficult to detect and showed no signs of a virtual environment.
This method improved the “realism” of the devices, but remained expensive and geographically bound, a downside that would be removed by the next wave of evolution. As infrastructure matured, these farms would evolve into cloud-based virtual mobile infrastructures (VMI), leveraging software emulators or cloud technology to mimic phone behavior, including unique device IDs, IP addresses, and geolocations. The transition to cloud phones followed classic SaaS economics: why own infrastructure when you can rent it? Between 2020 and 2023, a new industry emerged offering Cloud Phone Platforms or Remote Phone Services. These platforms recognized that the same device farm infrastructure that fraudsters were building, could be offered as a cloud service, with marketing that emphasized legitimate use cases.
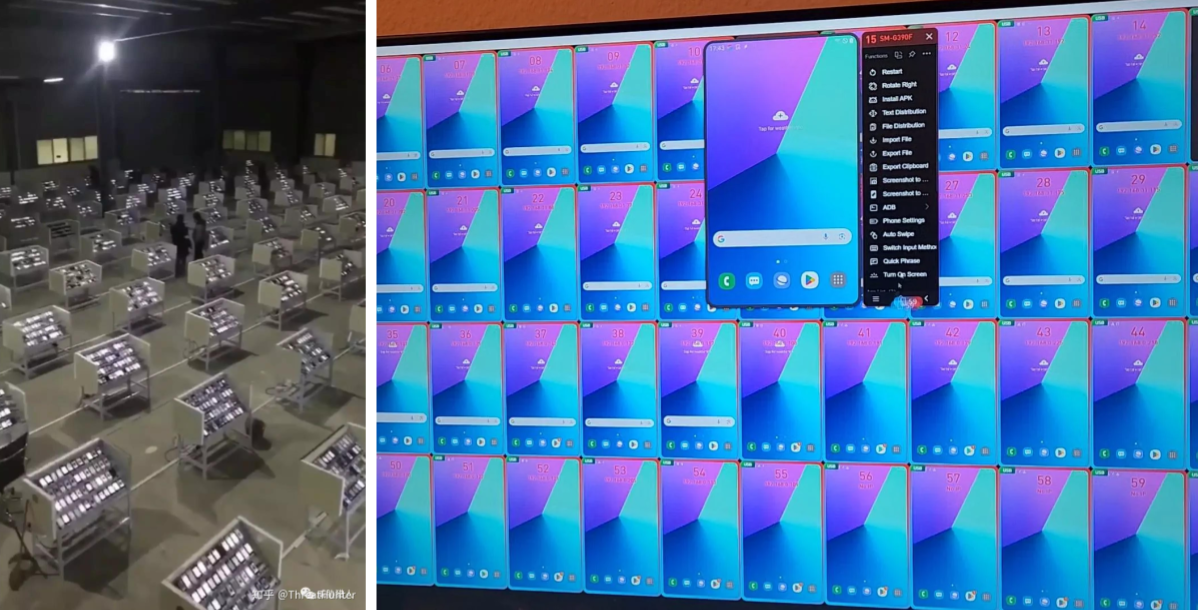
Figure 2: Physical and Virtual Phone Farms.
The Transition from “Harmless” Likes to Something More Serious
As the criminal use cases for phone farms started to grow beyond mere exploitation of social media engagement and ad fraud, a whole new market emerged for it. Cloud phones started to be sold in the form of phone box devices. These machines were essentially a box consisting of a collection of mobile phone motherboards. They could contain up to 20 individual mobile devices and all could be run simultaneously.
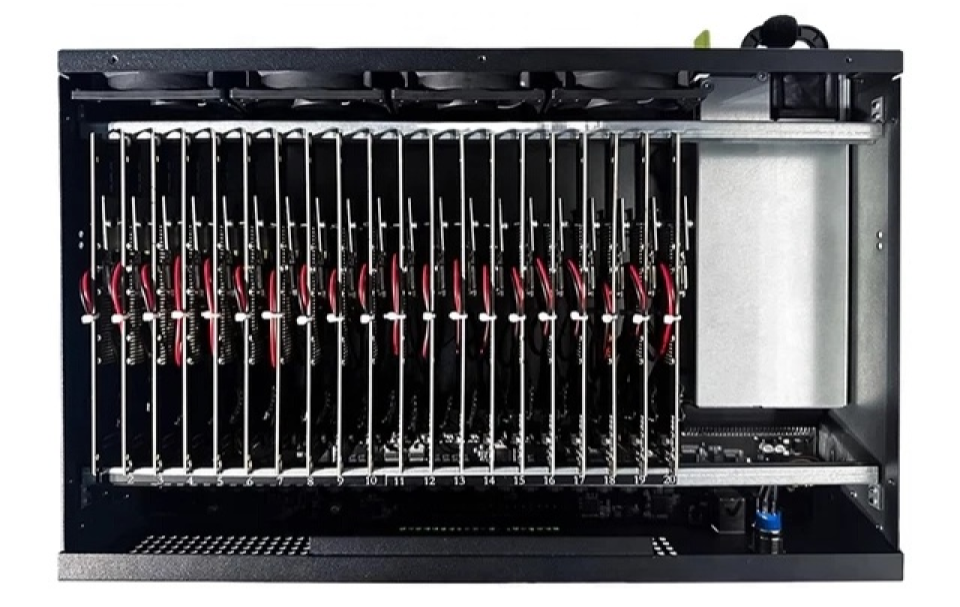
Figure 3: A phone box device running multiple mobile phone motherboards.
In other cases, access to cloud-based phone instances was sold as an online service. Several platforms emerged as leaders in the cloud phone space, each with distinct characteristics and target markets.
- Redfinger (红手指) is a Chinese platform launched in 2019 that claims over 10 million users globally, offering Android devices with customizable configurations at pricing of $10-30 per month per device instance. Its primary marketing focuses on game farming and app testing, though its actual usage patterns suggest significant fraud applications.
- VMOS (Virtual Mobile Operating System) initially launched as a local virtualization app before pivoting to cloud services in 2021, providing both on-device virtualization and cloud-hosted instances with features including root access and system-level customization. It’s particularly popular in Chinese and Southeast Asian markets where technical users appreciate the level of control it offers.
- GeeLark launched in 2021 with an explicit focus on social media management, marketing specifically to e-commerce and social media marketers who need to manage multiple accounts. It offers team management features and batch operations that allow coordinated activity across dozens or hundreds of accounts simultaneously, while claiming to provide “anti-detection” fingerprint protection for avoiding false positives from platform security systems but in practice enables evasion of fraud detection.
- DuoPlus targets e-commerce and cross-border sellers with integrated automation tools for platform-specific workflows, emphasizing “stable IP addresses” and “real device environments” in its marketing materials.
- LDCloud and NBE Cloud Phone focuses on gaming and app testing applications, offering bulk discounts for large deployments and providing API access for programmatic control that allows sophisticated users to build custom automation on top of the cloud phone infrastructure.
Cloud phones quickly gained popularity among fraudsters and were used not only for social media promotion but also abuse in marketplaces and online games. The iGaming sector became one of the earliest large-scale targets. Bonus abuse and referral farming required multiple seemingly independent accounts which could easily be facilitated by cloud phones each with unique device identities. Mobile games with real-money economies faced a specific problem: bot farming of in-game currency and resources. In games like RuneScape Mobile, PUBG Mobile, and various gacha games, automated accounts can farm in-game resources that have real-world value through unofficial markets, exploit game economies through coordinated market manipulation where hundreds of bot accounts work together to control prices, and snipe limited items or exploit early-game bonuses to gain unfair advantages.
Next Target: The Financial Industry and Banks
For years, financial services relied primarily on knowledge-based authentication through passwords and security questions, with transaction monitoring serving as the main fraud detection mechanism. Device identity was a secondary signal — useful for fraud detection but not central to the security model. The rise of Account Takeover (ATO) attacks made password-based authentication insufficient on its own. As banking shifted from web browsers to mobile apps, device fingerprinting needed to become more reliable and comprehensive. This step was critical in fighting against dropper (mule) accounts–false accounts created by fraudsters based on stolen credentials specifically targeted to receive and transfer stolen funds or could be used for other purposes. Banks could bind legitimate accounts to specific devices and flag transfers that don’t originate from the bound device. This served as a deterrent as dropper accounts are often accessed from multiple devices and handed off between fraudsters. ATO attacks became harder as attackers now couldn’t transfer funds without the original device, even with valid credentials of the account holder.
This is where cloud phone technology has started becoming a serious threat. Imagine this, if you are able to sell a virtual cloud phone to someone else, why not sell a cloud phone with already-verified credentials in it? This is the main motive behind new fraud schemes involving cloud devices. Group-IB researchers have started noticing sale offers for real, working bank cards and virtual wallets from different banks on various portals. Darknet markets now list pre-warmed dropper accounts with clean device telemetry for Revolut and Wise priced at $50–200 each for high-fraud utility. Concerning Central Asia, there are whole channels and groups on platforms like Telegram where people can buy bank cards from any bank in Uzbekistan:
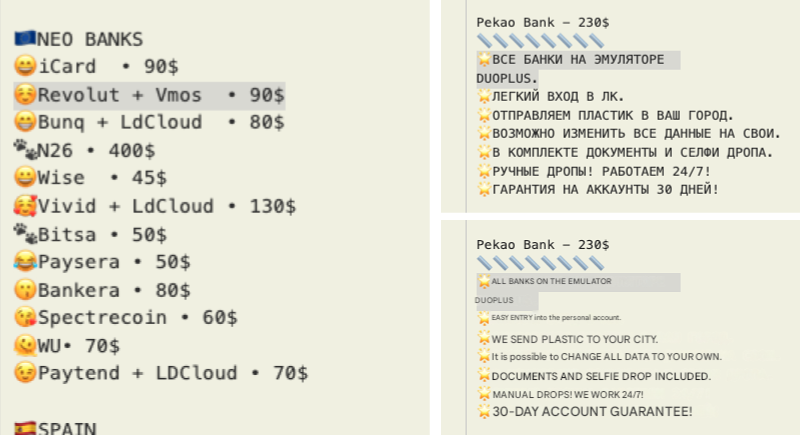
Figure 5. Cloud phones with pre-registered virtual wallets and bank cards on sale on darknet markets.
The buyer of such services receives both a bank account AND access to the same cloud phone instance where the account was authenticated. To the bank’s fraud detection system, it will appear to be the same device accessing the account that has always accessed it–same hardware fingerprint, same telemetry, same behavioral patterns. No device change flags are triggered, no step-up authentication is required, and funds can be transferred without additional verification.
How does this scheme work?
The victims of this type of fraud can range from teenagers with little understanding of the consequences of their actions to adults who fall prey to social engineering. Innocent victims of the scheme are tricked into providing their personal banking credentials to fraudsters impersonating bank workers or government officials in order to complete the verification process on the fraudsters’ cloud phone. Fraudsters are also known to target ordinary people, often those who are less educated residing in small towns or rural areas, bulk-purchasing their bank accounts without informing them how their data would be used.
These cloud phone devices with configured bank cards and accounts are later sold to third parties and other criminals, often becoming the receiving end of Authorized Push Payment (APP) scams as they are the critical missing link in many APP fraud cases where victims are socially engineered into transferring money to what appears to be a legitimate account, which is then quickly emptied.
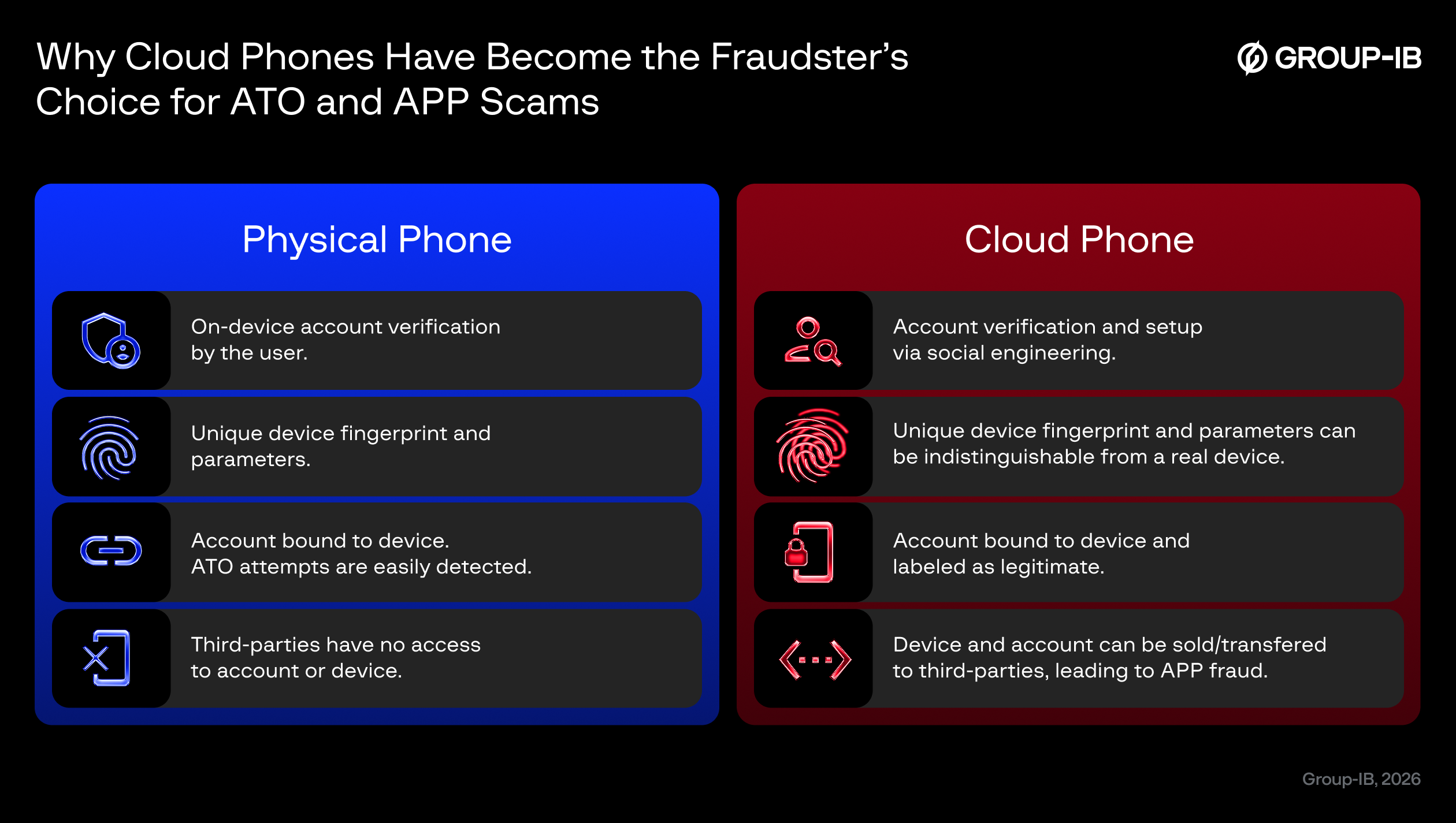
Figure 6: Why cloud phones have become the fraudster’s choice for ATO and APP scams.
APP fraud continues to lead industry losses. According to the UK Finance Annual Fraud Report 2023, APP fraud losses reached £485.2 million in 2023, with the dropper account fraud identified as the single most contributing incident of all. In Central Asia, for Uzbekistan alone, Group-IB analysts estimate an accumulated loss of $150,000 based on the number of active cloud phones detected by Group-IB’s Fraud Protection platform. The problem continues to grow and spread in other regions.
The UK’s Payment Systems Regulator (PSR) has been at the forefront of addressing APP fraud through regulatory intervention that fundamentally changes bank economics. In October 2024, new regulations took effect that required banks to reimburse victims of APP fraud up to £415,000, a dramatic increase from the previous £85,000 cap. The regulations mandate that liability be shared between the sending and receiving banks with a 50/50 split in most cases, giving banks a strong financial incentive to detect receiving dropper accounts early while cloud-phone-farmed droppers make that detection significantly harder.
Why is This a Big Problem?
The main reason fraudulent activities carried out by cloud phones are flagged as problematic stems from the difficulties associated with their detection. Unlike emulators, each cloud phone instance has an independent system, independent IP address, and hardware parameters while the equipment environment is also controllable and can be disguised. The fixed parameters of the real phone such as Screen Resolution, CPU Model, GPU Model, IMEI/GAID/Android ID can be readjusted / regenerated or batch cloned in cloud phones. Classic Android emulators by now have become an easy source of detection as they leak obvious artifacts – x86 CPU, missing sensor data, emulator specific files, unnatural timings. Cloud phones, on the other hand, can be cloned, snapshotted, reset, geo-assigned, and automated via APIs. They often present consistent hardware identifiers, plausible sensor data, stable OS versions, and valid app integrity signals making their technical characteristics hard to rely on for detection. Their abuse patterns emerge only on higher telemetry layers — behavioral timing, network locality mismatches, account graph correlations, or telecom-side signals — rather than the device-fingerprint layer where emulators were easiest to catch.
| Technical Characteristics | Emulator | Cloud Phone |
| CPU architecture | Runs on PC chips x86_x64 and must be translated from ARM code | Runs directly on ARM/ARM64-based server chips (same as real phones) |
| GPU hardware | Desktop GPU. Runs on a PC, uses host machine resources | Mobile GPU. Real Android devices, accessible via the Internet |
| MAC addresses | Virtual adapter patterns | Device manufacturer ranges |
| System build properties | Emulator signatures. Limited: often no camera, GPS, or Bluetooth support | Real device values. Complete, including SIM card, network, etc. |
| IMEI/Hardware IDs | Fake or follow known generator patterns | Unique and authentic manufacturer-assigned IDs from real device parts |
| Network settings | Depends on the host, difficult to emulate a mobile network | Real IP addresses of mobile operators |
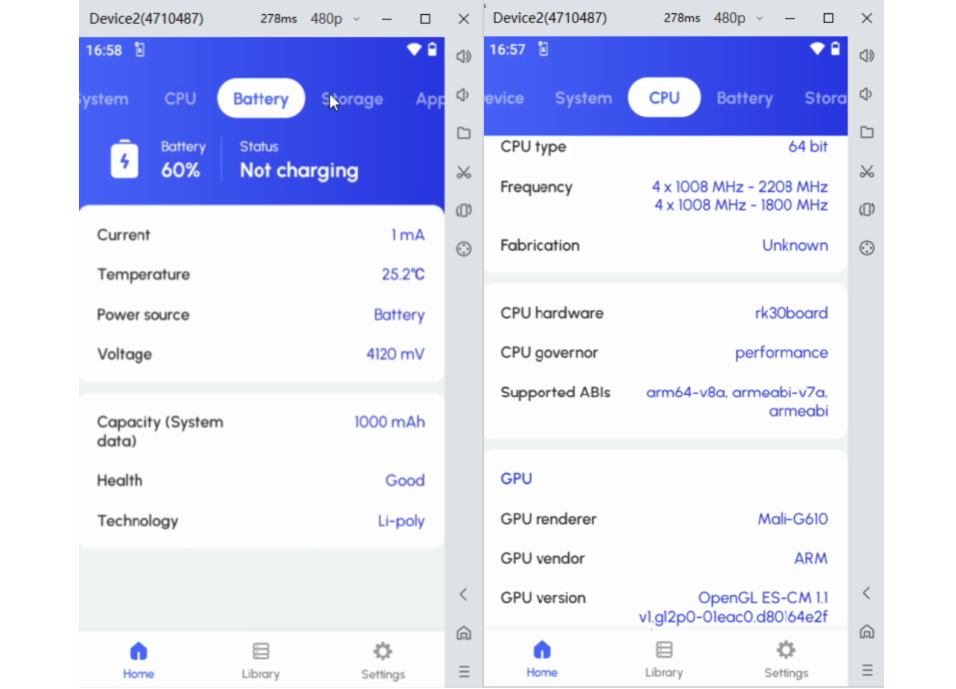
Figure 7: Cloud phones often run on platforms with very low power and specifications.
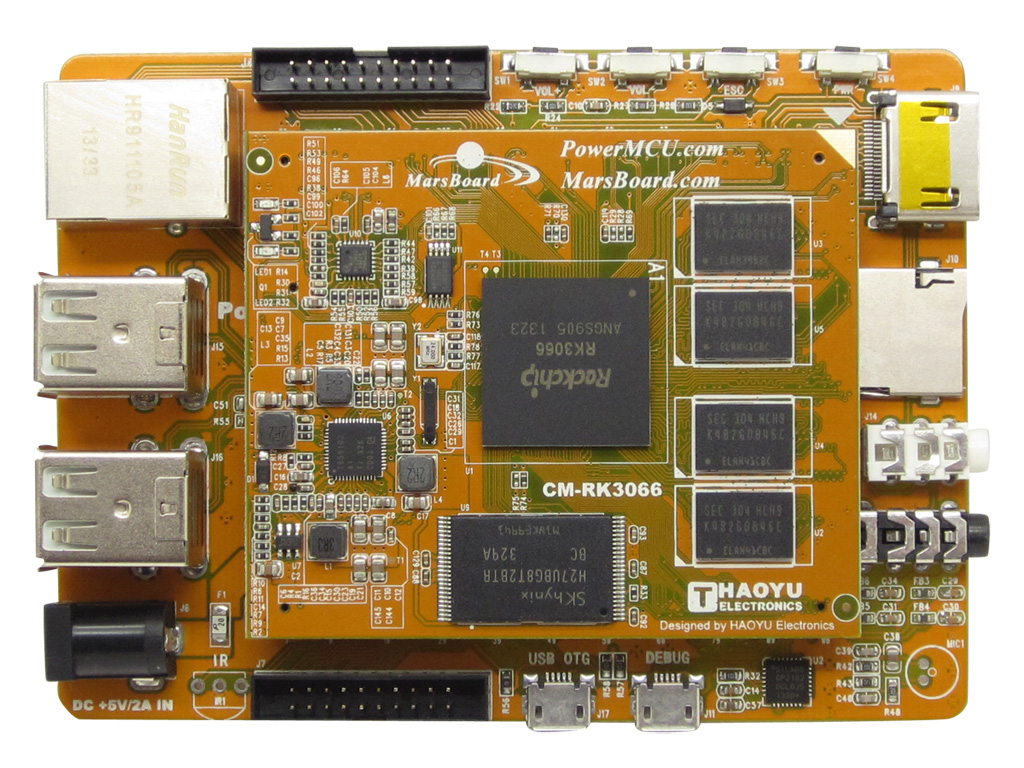
Figure 8: Sample cloud phone motherboard similar to those used in children’s toys and TV set-top boxes.
Detection via Anonymization and Installed Applications
By checking installed applications on the device, our team has also determined that by default, many normal applications are absent in cloud devices, sometimes, even those that are usually pre-installed in real devices. Fraudsters using cloud phones first install certain anonymization tools such as VPNs, or proxy applications or a single cloud device can have suspiciously high numbers of banking or financial applications. In other cases, there are special system management applications specific for vendors which cannot be found on official sources such as Google Play or AppStore. These applications allow users to download other applications, enable root privileges, change geolocation and phone model.
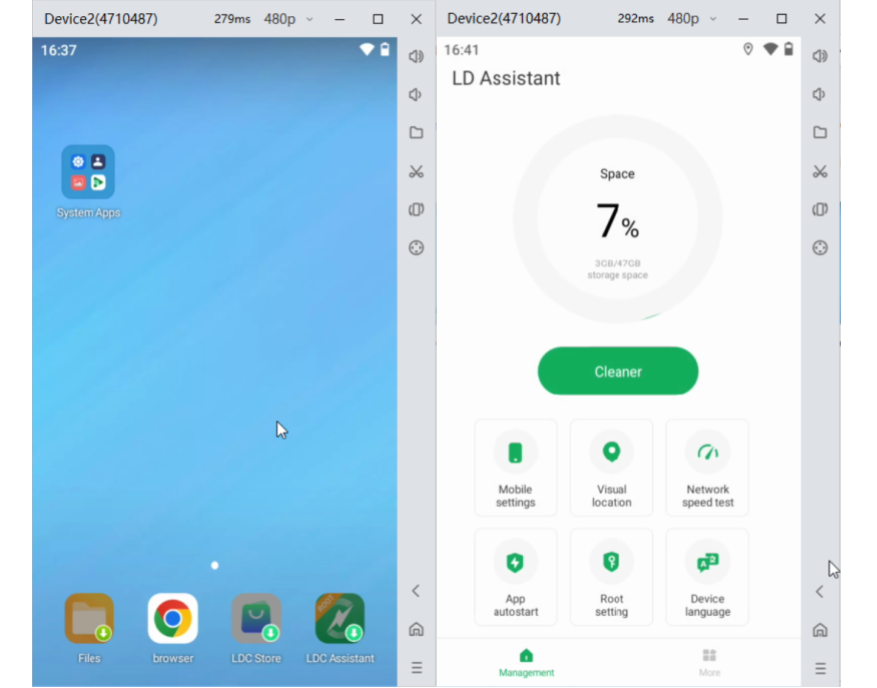
Figure 9: Installed applications list and presence of anonymizers often point to cloud phone setups.
Behavioral patterns
Certain anomalies in behavioral patterns can also be used for identifying cloud phones. Even though data from sensors of cloud phones cannot always be reliable for detection as they are usually simulated, a subtle mismatch in device IP address, time zone, and its location and recent appearance of the device in the detection system could indicate atypical behavior than a real device and could be a decent indicator. Lack of device-environment correlation, such as battery levels that are always 100% or devices that never show motion during active use sessions, creates suspicious scenarios that real devices wouldn’t signal.
Current status
Combining above detection metrics under a single logic, Group-IB’s Fraud Protection solution was able to come up with a new rule for better detection of cloud devices based on their technical parameters. Since the launch of this new detection technology, there has been a drastic decrease in the average number of daily unique logins or Group-IB customers in Central Asia.
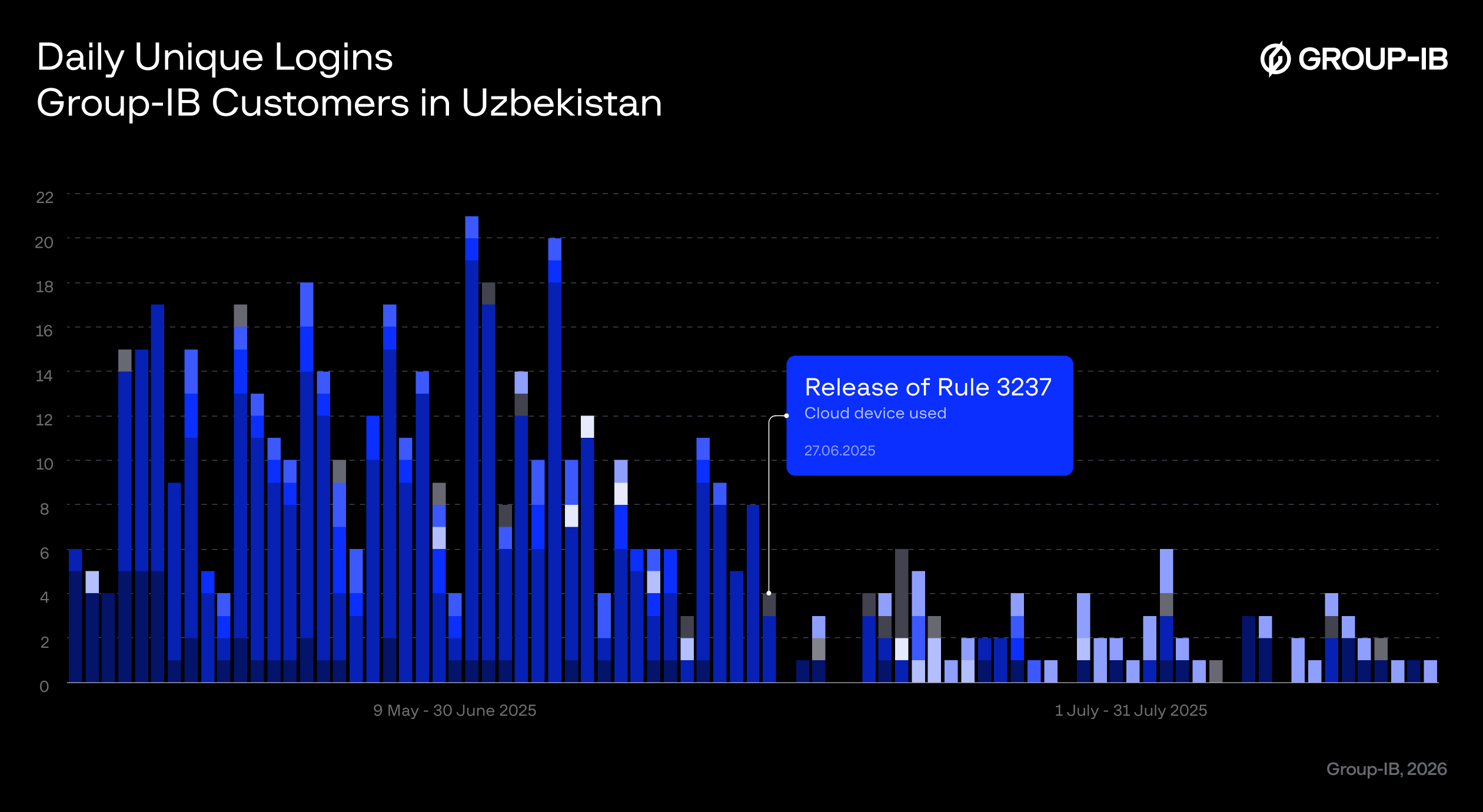
Figure 10: Based on new cloud phone detection metrics, daily unique logins have drastically decreased among Group-IB customers.
Conclusion
Cloud phones solve the fraudster’s fundamental problem: how to conduct fraud at scale while presenting authentic device signals that defeat most modern detection systems. The threat is real, growing, and causing measurable losses today. Banks are losing millions to cloud phone-enabled dropper accounts operating beneath their detection systems. Device binding, once a powerful defense against account takeover and mule account reuse, is weakened when device environments themselves become rentable and transferable assets. The broader lesson is not that device fingerprinting has failed, it is that fraud detection must move beyond static device authenticity checks to multi-layered intelligence: device-environment correlation, infrastructure-level visibility, behavioral modeling, and graph-based analytics.
Recommendations
To protect against fraud, we recommend that end users and financial organizations follow these risk mitigation recommendations.
For Financial Organizations:
- Adopt multi-layer device intelligence by combining device fingerprinting with network intelligence, and cross-session behavioral modeling such as Group-IB’s Fraud Protection platform rather than relying solely on static hardware identifiers.
- Use graph-based risk modeling to identify clusters of accounts sharing infrastructure-level similarities, rather than evaluating each device in isolation.
- Pay particular attention to new accounts created from environments exhibiting low app diversity, high financial app density, or anonymization tooling patterns.
- Cloud infrastructure evolves quickly. Fraud detection logic must be updated continuously to keep pace with changes in VMI providers and cloud phone platforms.
For End-users:
- Never complete account verification processes under third-party instruction. Keep in mind that banks and government institutions will not ask customers to authenticate accounts through unfamiliar apps or remote environments.
- Enable device-based security features. Use official mobile banking apps, biometric authentication, and strong device-level security settings.
- Be cautious of “easy income” schemes involving bank accounts. Fake job offers requiring you to “verify” bank accounts, government officials requesting account verification, bank representatives asking you to move money to “safe” accounts.
- If you suspect that you have been targeted, contact your bank immediately. Update passwords and enable multi-factor authentication on all accounts.
Frequently Asked Questions (FAQ)
What is a cloud phone?
A cloud phone is an internet-based virtual phone system that enables users to send and receive voice calls, messages and access features just like a physical device. Modern cloud phones can fully virtualize the Android smartphone experience and run apps as well.
What are phone farms?
Typically, phone farms can be a physical or virtual machine setup comprising multiple Android smartphones – from hundreds to thousands of devices depending on the scale of operation – used to automate tasks such as the manipulation of social media engagement, fake app reviews and installs, in-game economy or other metrics. Phone farms have also become an industry to itself, where cloud phone instances can be rented out in a SaaS model to anyone.
How is cloud phone technology abused for financial fraud?
Threat actors are able to buy, sell, and move cloud phones with pre-loaded e-wallets and pre-verified bank cards and accounts, ready to be used in Account TakeOver (ATO) and Authorized Push Payment (APP) scams.
Why are cloud phones so difficult to detect?
Modern cloud phones are so advanced, they can perfectly mimic real devices, with independent systems, IP addresses, hardware parameters and equipment environments. Attackers make use of this technology to bypass traditional fraud protection systems as cloud phone activity is often indistinguishable from a legitimate device.
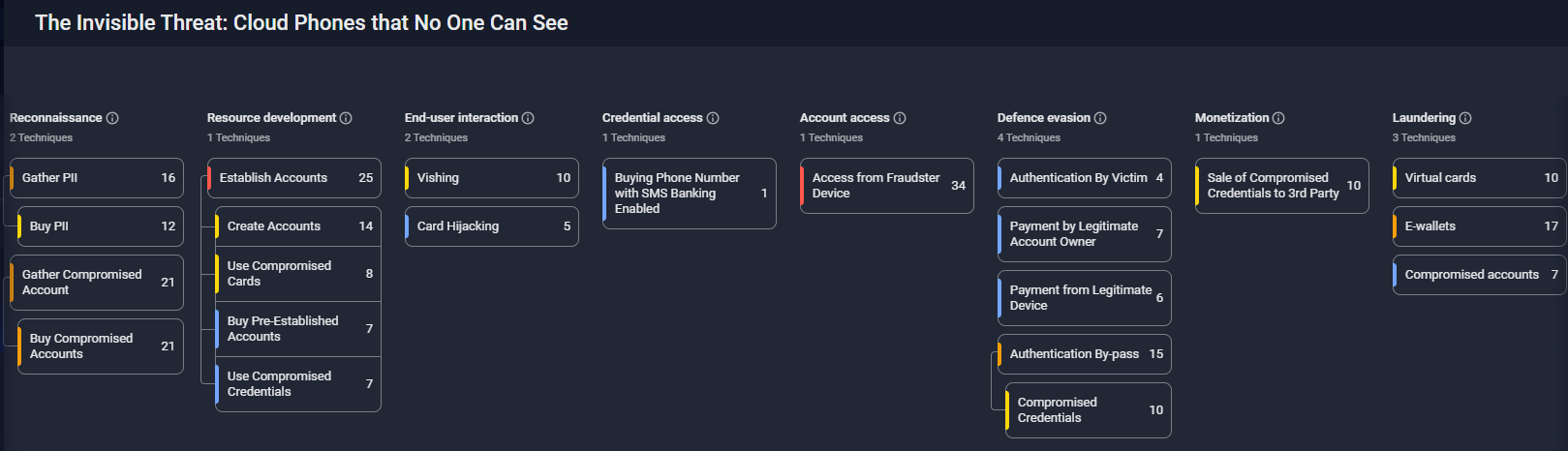
Group-IB Fraud Matrix
| Tactic | ID | Technique | Procedure |
| Reconnaissance | T2105.003 | Buy Compromised Accounts | Fraudsters obtain compromised accounts already set up on Cloud Phones through illicit channels such as dark web marketplaces and hacking forums |
| T2036 | Gather PII | Fraudsters employ various techniques to gather Personally Identifiable Information (PII), including phishing, data breaches, mass purchasing and social engineering and use PII to set up legitimate accounts on Cloud Phones. | |
| Resource development | T2023 | Establish Accounts | Fraudsters leverage cloud phones by opening accounts using false identities or stolen personal information, they gain access to financial services and resources that can be exploited for illicit purposes. By rotating through hundreds of cloud phone devices, fraudsters can open accounts across multiple financial institutions simultaneously while each account maintains a “clean” device history with no cross-contamination or multi-accounting flags. |
| T2023.004 | Use Compromised Credentials | Cloud phones enable fraudsters to safely use compromised credentials during account establishment which involves inputting stolen or leaked login information to gain unauthorized access to systems or services. | |
| T2023.007 | Use Compromised Cards | Adversaries may use compromised credit cards during account creation or modification. Fraudsters use cloud phones to add stolen credit cards to mobile wallets during account setup. | |
| T2023.005 | Create Accounts | Fraudsters create accounts by providing false or stolen information to deceive systems into believing they are legitimate users. This technique often involves using fake identities or compromised data to bypass verification processes and gain unauthorized access. | |
| End-user interaction | T2066 | Card Hijacking | Fraudsters engage in card hijacking by unlawfully acquiring sensitive payment card details, such as card numbers, expiration dates, and security codes, through various illicit means like skimming devices or data breaches. Fraudsters use cloud phone farms to test harvested card details. Successful cards are then sold on dark web marketplaces, often with the cloud phone device credentials included so buyers can continue using the card with the same “trusted device” fingerprint. |
| T2084 | Vishing | Vishing, or voice phishing, is a technique where scammers use phone calls to deceive victims into providing sensitive information or taking certain actions. These calls often impersonate trusted entities, such as banks, government agencies, or tech support, and employ various manipulation techniques to create a sense of urgency or fear. By exploiting the victim’s trust and urgency, fraudsters aim to extract personal information, financial details, or even remote access to devices, which can lead to identity theft, financial fraud, or unauthorized account access. All personal information extracted via Vishing is used in-parallel for account setup on a Cloud Phone. | |
| Credential access | T2141 | Buying Phone Number with SMS Banking Enabled | Fraudsters purchase phone numbers associated with cloud phone instances that have SMS banking already configured through various illicit channels, such as underground markets or illegal data brokers. Once in possession of such a phone number, fraudsters can exploit the SMS banking feature to intercept authentication codes and other sensitive information sent by financial institutions to the victim’s mobile device. |
| Account access | T2069 | Access from Fraudster Device | Fraudsters gain unauthorized access to victim accounts and carry out illicit activities from their own cloud phones. |
| Defence evasion | T2157 | Authentication By-pass | Fraudsters use Authentication Bypass techniques to circumvent login or access controls, granting them unauthorized entry into systems or accounts. Cloud phones bypass authentication controls by presenting legitimate device attestation. By creating accounts on cloud phones and maintaining access via those same devices indefinitely, fraudsters ensure every login appears to come from the account’s original, trusted device. |
| T2178 | Compromised Credentials | Fraudsters utilize Authentication Bypass through Compromised Credentials by exploiting stolen or leaked login credentials to gain unauthorized access to systems or accounts. When using compromised credentials, fraudsters leverage cloud phones to establish new device associations that appear legitimate. | |
| T2054 | Authentication By Victim | Fraudsters leverage Authentication by Victim for Defense evasion by convincing a victim to start and complete the authentication process. This technique enables fraudsters to bypass security controls making it difficult for fraud protection teams to distinguish between legitimate and fraudulent actions. A fraudster logs into the victim’s account from a cloud phone and through social engineering (posing as bank security), the fraudster convinces the victim to approve the login. The cloud phone then gains authenticated access with a legitimate device fingerprint. | |
| T2072 | Payment from Legitimate Device | Fraudsters leverage the Payment from a Legitimate Device by convincing a victim to make transactions from a legitimate/victim or trusted device. By doing so, they mask their fraudulent activity as legitimate transactions, making it difficult for detection systems to flag the transactions as suspicious. | |
| T2115 | Payment by Legitimate Account Owner | Fraudsters use cloud phones to initiate transactions that pass all device reputation checks. The payment appears to come from a recognized device with consistent fingerprints, proper OS configuration, and no emulator artifacts. This technique allows them to bypass security measures and evade detection by exploiting the trust associated with the legitimate account. | |
| Monetization | T2162 | Sale of Compromised Credentials to 3rd Party | Fraudsters monetize compromised credentials by selling them to third parties on underground forums or dark web marketplaces. When selling compromised accounts on dark web marketplaces, fraudsters include the associated cloud phone device access as a premium feature. The seller transfers the cloud phone instance credentials to the buyer, who can then access the account indefinitely while maintaining the original device fingerprint. This creates a liquid secondary market for “device-locked” accounts that were previously difficult to transfer. |
| Laundering | T2110 | E-wallets | Fraudsters use cloud phones to create and operate e-wallet accounts (PayPal, Venmo, Cash App, Revolut) that serve as laundering nodes. They then transfer funds into e-wallet accounts. Illicit funds flow through multiple cloud phone-hosted e-wallets, with each transfer appearing to originate from a legitimate mobile device. |
| T2181 | Compromised accounts | After taking over victim accounts, fraudsters use cloud phones to maintain access and perform laundering operations. The cloud phone is configured to match the victim’s device characteristics, ensuring continued access without triggering security alerts. Fraudsters exploit compromised accounts for laundering by using them as intermediaries to obscure the source and destination of illicit funds. | |
| T2087 | Virtual cards | Fraudsters use virtual cards for money laundering because they provide anonymity, flexibility, and ease of use in online transactions. Virtual cards are often obtained with less stringent identity verification, making it easier to conceal illicit financial activities. Fraudsters use cloud phones to create and manage virtual payment cards for layering illicit funds. Each cloud phone instance hosts a separate virtual card account, created with stolen or synthetic identities. |
DISCLAIMER: All technical information, including malware analysis, indicators of compromise and infrastructure details provided in this publication, is shared solely for defensive cybersecurity and research purposes. Group-IB does not endorse or permit any unauthorized or offensive use of the information contained herein. The data and conclusions represent Group-IB’s analytical assessment based on available evidence and are intended to help organizations detect, prevent, and respond to cyber threats.
Group-IB expressly disclaims liability for any misuse of the information provided. Organizations and readers are encouraged to apply this intelligence responsibly and in compliance with all applicable laws and regulations.
This blog may reference legitimate third-party services such as Telegram and others, solely to illustrate cases where threat actors have abused or misused these platforms.
This material is provided for informational purposes, prepared by Group-IB as part of its own analytical investigation, and reflects recently identified threat activity.
All trademarks referenced herein are the property of their respective owners and are used solely for informational purposes, without any implication of affiliation or sponsorship.