Authorized Push Payment (APP) fraud is one of the most damaging forms of digital deception.
The pattern repeats itself thousands of times each year: an email from the bank’s security team warning of suspicious activity. A phone call that follows immediately. The caller ID matches. The “fraud prevention officer” knows details about recent transactions. Within minutes, the victim authorizes a transfer to “protect” their savings — often tens of thousands of pounds. The realization comes too late. The money is already gone.
This is Authorised Push Payment (APP) fraud — a crime where the victim themselves, under manipulation, authorizes the transfer. Unlike unauthorized fraud where criminals break into accounts, APP fraud weaponizes human psychology. The victim willingly — though unknowingly — hands over their money.
This is achieved through sophisticated social engineering tactics, where criminals impersonate trusted organizations or build relationships with victims to manipulate them. Common examples include purchase scams, romance scams, and investment scams.
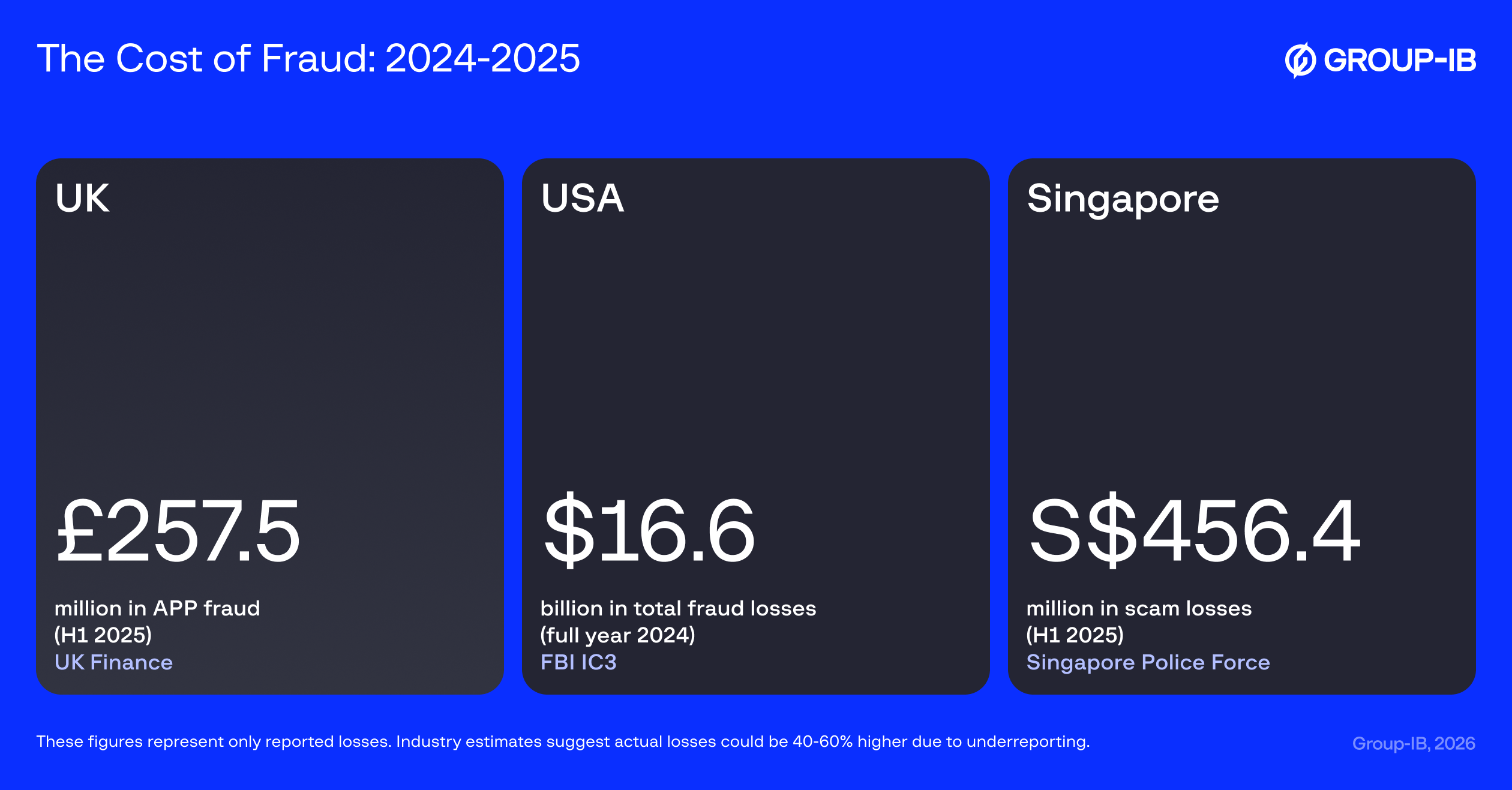
The Global Scale of the Problem: A Snapshot
The numbers behind APP fraud tell a story of a crisis that’s accelerating across every major economy. While exact figures vary by reporting methodology and definitions, the trend is unmistakably upward — and the true scale is likely far larger than reported, as many victims never come forward due to embarrassment or uncertainty about whether they’ve been defrauded.
The significant financial damage caused by APP fraud is a critical issue across all major economies, with national authorities reporting substantial and growing losses.
Real-Time Payments vs. Delayed Reporting
Understanding why APP fraud has become so devastating requires examining the fundamental mismatch between modern payment infrastructure and human response time.
The global shift to real-time payments has created a critical time asymmetry that fraudsters masterfully exploit. Domestic and international payment systems are engineered for speed:
- Europe’s SEPA Instant Credit Transfer (SCT Inst) can settle transactions in under 10 seconds.
- The UK’s Faster Payments Service (FPS) operates in near real-time.
- Brazil’s Pix payment system averages 40 seconds per transaction.
These payments are typically final and irrevocable. But here’s the critical asymmetry: while money moves in seconds, human awareness moves in days or weeks. Research from industry bodies indicates that victims often take a long time to realize they have been scammed, with some reports suggesting that only a fraction of fraud cases are reported within the first few hours. This delay creates a golden window for criminals to receive and launder funds long before the victim or their bank is even aware of the crime.
Consider the typical timeline: A victim realizes something is wrong on Tuesday afternoon. They call their bank Wednesday morning. The bank’s fraud team investigates Wednesday and Thursday, confirms the fraud Friday, and reports it through official channels the following Monday. Meanwhile, the criminal has had five days to:
- Move funds through a network of mule accounts across multiple institutions
- Convert to cryptocurrency via peer-to-peer exchanges
- Transfer to jurisdictions with weak AML controls
- Cash out through ATMs or complicit money service businesses
- Integrate the funds into seemingly legitimate businesses
Each of these steps takes hours, not days. By the time the official fraud report circulates through traditional channels, the money has passed through so many hands and forms that tracing it becomes virtually impossible.
Fraudsters use this time gap to execute the “layering” phase of money laundering with incredible speed. The stolen funds are not left sitting in the initial mule account. Within minutes, the money is often:
- Moved internationally through payment networks like SWIFT GPI, which has reduced cross-border payment times from days to, in many cases, minutes.
- Converted into cryptocurrency (such as Tether or Bitcoin) and transferred across borders almost instantaneously, bypassing traditional banking controls entirely. Blockchain analysis firms report that crypto mixers and illicit exchanges can obscure the trail of funds in a matter of hours.
Once the funds are moved offshore, particularly to jurisdictions with weak anti-money laundering (AML) controls or a lack of international cooperation, the chances of recovery plummet. The United Nations Office on Drugs and Crime (UNODC) and the World Bank’s Stolen Asset Recovery (StAR) Initiative have estimated that less than 1% of global illicit financial flows are ever seized and recovered.
This creates the core challenge of modern fraud prevention: by the time most fraud is reported, the money has already been moved, laundered, and is effectively unrecoverable. Prevention and real-time intervention are the only viable strategies.
The Limits of Siloed Defenses
The regulatory response to this crisis has been swift and global. Yet regulations alone cannot solve a problem rooted in technological fragmentation. Authorities worldwide recognize that without secure mechanisms for real-time intelligence sharing, even the strongest mandates remain aspirational.
Authorized Push Payment (APP) fraud is a coordinated crime that leverages the structural separation between financial institutions. A single institution’s view is limited to its own customers, making it blind to the risk profile of a recipient account at another bank. This lack of shared visibility is a key vulnerability that criminals exploit to move and launder funds through mule accounts.
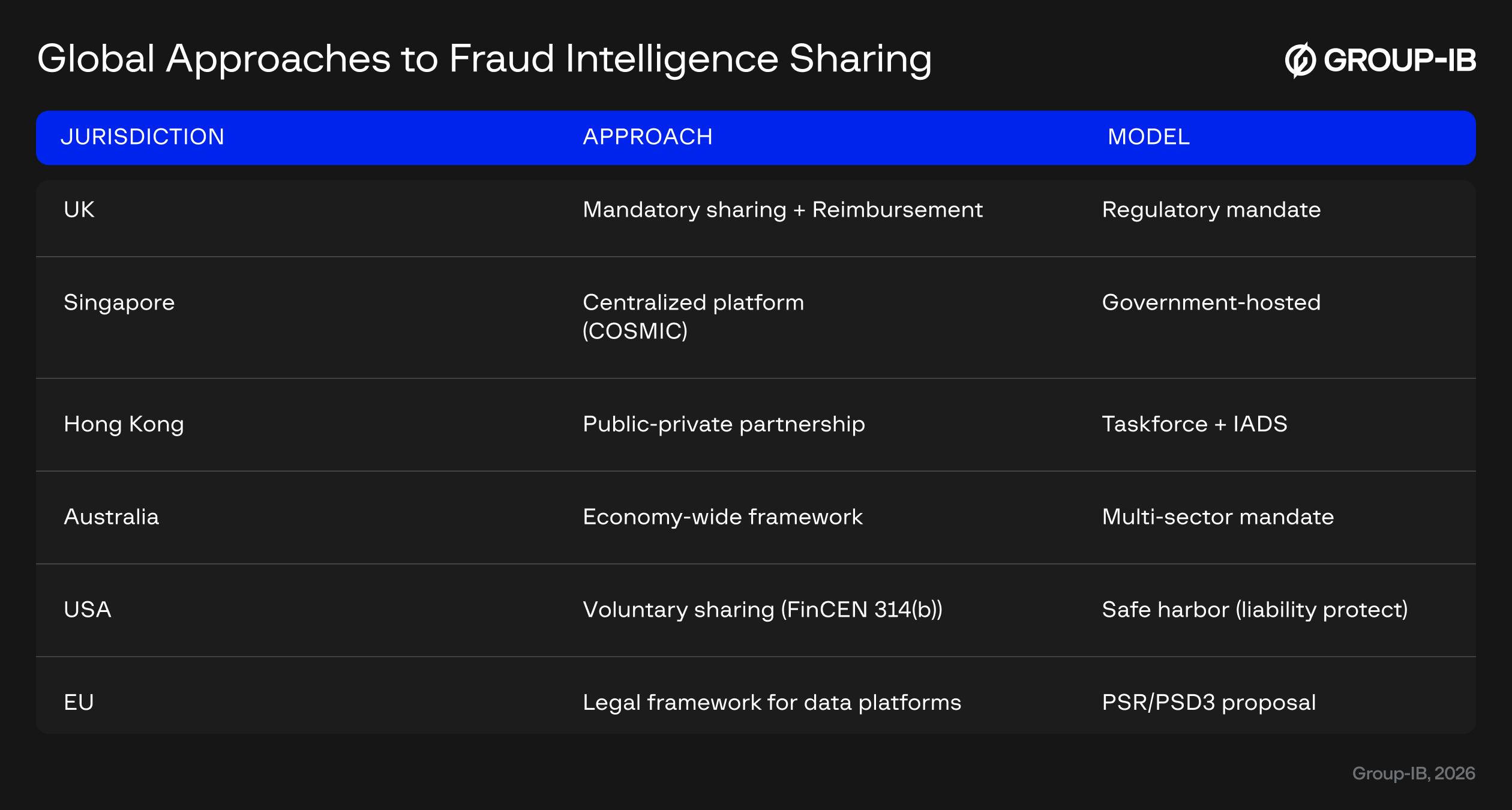
Mandatory Sharing Frameworks
Several jurisdictions have moved beyond encouraging information sharing to mandating it:
The UK Payment Systems Regulator (PSR) has taken perhaps the boldest step, requiring payment firms not only to reimburse APP fraud victims (Specific Direction 20) but also to participate in enhanced data sharing among providers. The Financial Conduct Authority (FCA) reinforces this through mandatory fraud event notifications (FCA Handbook – SUP 15.3).
Australia is implementing a comprehensive Scams Prevention Framework that will impose obligations on banks, telecoms, and digital platforms to prevent, detect, and disrupt scams, with strong penalties for non-compliance. This represents one of the most sweeping mandatory frameworks globally (Scams Prevention Framework – Protecting Australians from scams, Consultation Paper).
Infrastructure for Secure Sharing
Other jurisdictions have focused on building the technical infrastructure for safe collaboration:
Singapore’s Monetary Authority (MAS) developed COSMIC, a centralized platform enabling financial institutions to securely share customer information for AML and counter-terrorism financing purposes. This represents a government-hosted custodial model (MAS Overview and official announcement of the COSMIC Platform).
Hong Kong’s HKMA operates two complementary systems: the Fraud and Money Laundering Intelligence Taskforce (FMLIT) for direct fraud intelligence sharing, and the Interbank Account Data Sharing (IADS) initiative for broader fintech innovation (HKMA Publication on AML Regtech and HKMA Fintech – Interbank Account Data Sharing).
Canada’s FINTRAC has enabled voluntary private-to-private information sharing through recent legislative amendments, creating a legal safe harbor for institutions that collaborate to detect financial crime
(FINTRAC – Modernization and upcoming changes).
Global Standards and Cross-Sector Frameworks
The European Commission, as part of its new Payment Services Regulation (PSR) and third Payment Services Directive (PSD3) proposal, is introducing a legal framework to enable payment service providers to share fraud-related information and establish collaborative data-sharing platforms, seeing this as a key tool to prevent scams (Payment services package, June 2023 Proposal).
The Financial Action Task Force (FATF) sets global standards and encourages jurisdictions to establish legal frameworks that remove barriers to public-private and private-private information sharing to effectively combat financial crime (FATF Guidance on Private Sector Information Sharing).
The European Union’s Digital Operational Resilience Act (DORA) requires financial entities to put in place arrangements to share cyber threat information and intelligence, which is critical for preventing fraud originating from cyber attacks (Official Text of Regulation (EU) 2022/2554 – DORA).
In the United States, the Financial Crimes Enforcement Network (FinCEN) Section 314(b) program provides a safe harbor for financial institutions to voluntarily share information with one another to better identify and report activities that may involve money laundering or terrorist financing (FinCEN Section 314(b) Program Overview).
Yet despite this regulatory momentum, a critical challenge remains: how can institutions share intelligence about suspicious activity in real time while respecting stringent data privacy requirements? This is where technology must bridge the gap between regulatory intent and operational reality.
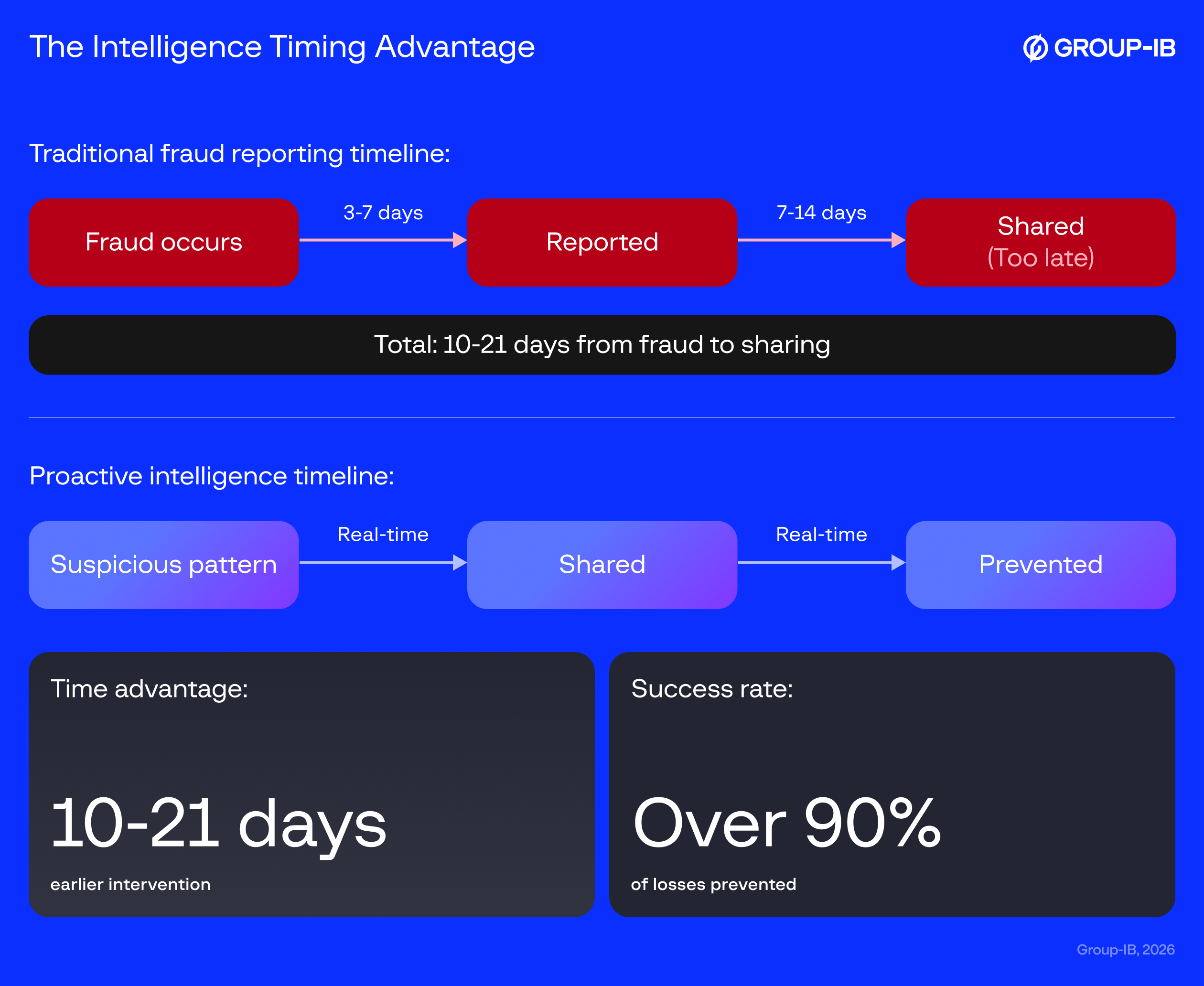
The Intelligence Gap: Confirmed Fraud vs. Proactive Prevention
The functional difference between sharing historical data on confirmed fraud and sharing real-time intelligence on suspicious activity is the difference between reactive reporting and proactive prevention. Global authorities and industry bodies have affirmed that a focus on suspicious, in-flight activity is critical to meaningful fraud reduction.
The Wolfsberg Group, an association of leading global banks focused on financial crime risk management, has advocated for measuring AML/CTF program effectiveness based on outcomes rather than process. In their framework on demonstrating effectiveness, the group emphasizes that financial institutions should focus on ‘providing highly useful information to relevant government agencies in defined priority areas’ — moving beyond compliance-focused reporting to intelligence that genuinely helps law enforcement prevent and detect financial crime. This outcome-based approach highlights the limitations of purely retrospective, compliance-driven reporting.
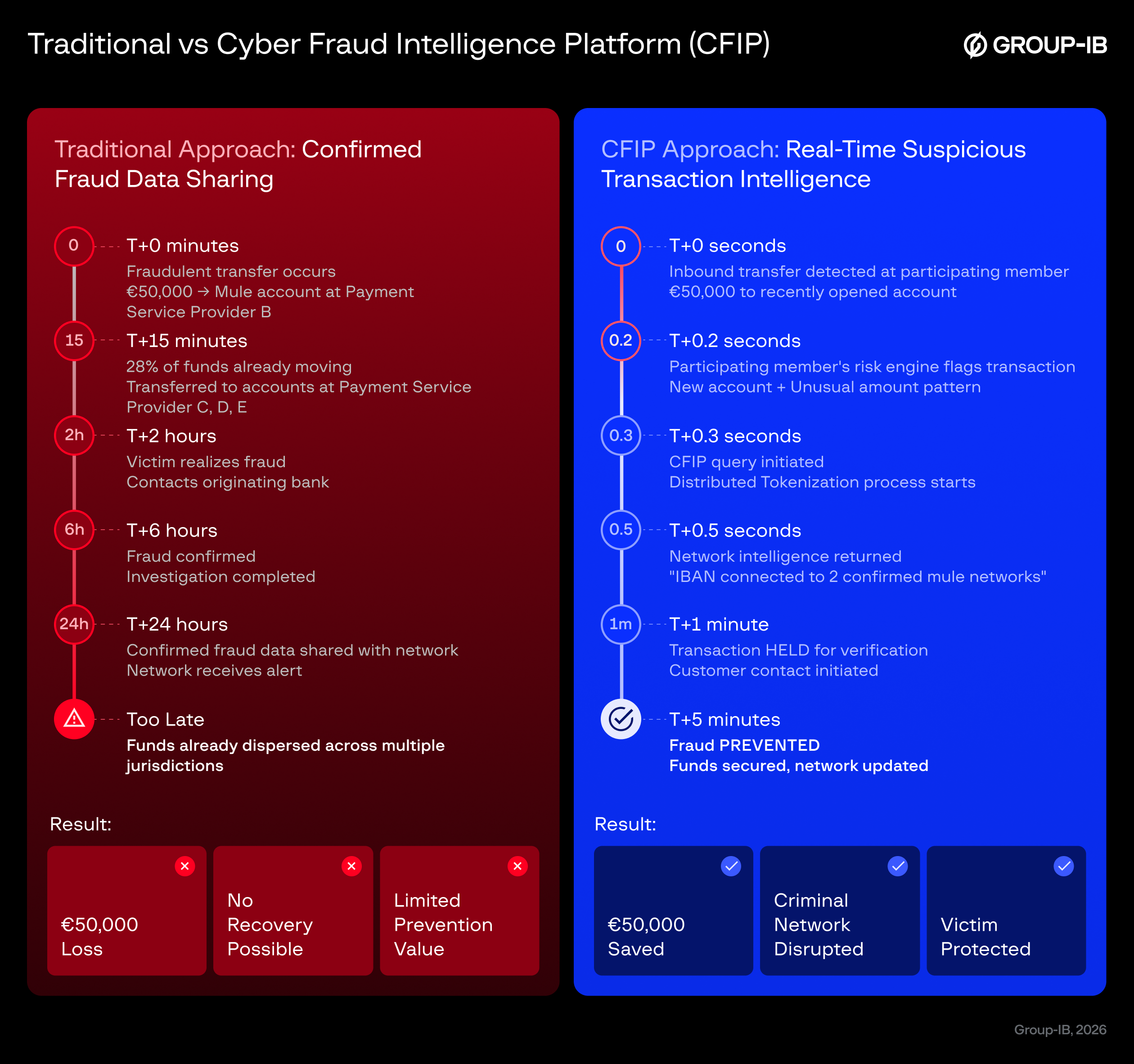
To understand why this distinction matters, consider two scenarios:
Scenario 1: Confirmed Fraud Sharing (Current Reality)
- Monday: Victim reports fraud to Bank A
- Tuesday: Bank A confirms fraud after investigation
- Wednesday: Bank A adds account to shared blacklist
- Result: The mule account has been actively receiving funds for 4-8 weeks. The blacklist will prevent future fraud to that specific account, but the criminal network simply opens new mule accounts.
Scenario 2: Suspicious Activity Sharing (Proactive Intelligence)
- Week 1: Bank A notices unusual account behavior during warm-up period
- Week 1: Bank A flags as suspicious, checks collaborative network
- Week 1: Banks B and C also flagged same account indicators
- Week 2: Network identifies high-probability mule account BEFORE deployment
- Result: Account is monitored or blocked before ANY victims lose money. The criminal network must restart the expensive warm-up process.
The difference is measuring prevention in millions of dollars versus documenting losses in millions of dollars.
Europol, through the European Cybercrime Centre (EC3), stresses the importance of rapid intervention. In its 2023 IOCTA (Internet Organised Crime Threat Assessment) report, it notes that criminal networks involved in fraud “usually launder their criminal funds very quickly after the fraud has taken place; this means that by the time the victim realises the scam, the money is already split through accounts based in multiple countries and laundered.” The clear implication is that intelligence must be available in real-time to law enforcement and financial institutions to have any chance of intercepting funds, reinforcing the need for systems that can flag suspicious transactions as they occur.
The U.S. Financial Crimes Enforcement Network (FinCEN) Section 314(b) program facilitates voluntary information sharing among financial institutions regarding activities that may involve money laundering or terrorist financing. The program permits financial institutions to share information with one another under a liability safe harbor ‘in order to better identify and report activities that may involve money laundering or terrorist activities.’ This framework enables institutions to build a more comprehensive picture of suspicious activity across multiple institutions, alert others to customers they may not have known about, and file more comprehensive Suspicious Activity Reports — helping identify criminal networks before they can cause further harm.
These bodies confirm that while reporting confirmed fraud is a necessary function, the key to preventing fraud lies in the ability to securely share actionable intelligence on suspicious activities in real-time. It is precisely this proactive capability that presents both the greatest challenge and the greatest opportunity for the financial industry.
A Technical Solution for Privacy-Preserving Collaboration
The challenge of sharing fraud intelligence while protecting privacy has stymied the industry for years. Standard encryption and hashing methods fail because they’re vulnerable to what’s known as a “dictionary attack.”
To address this challenge, a new technological approach is needed that permits proactive intelligence sharing while ensuring data privacy. Standard pseudonymization techniques like SHA256 hashing are not sufficient for this task, as they are vulnerable to re-identification if an interested party already possesses a list of potential account identifiers to test against the shared data.
Here’s why standard hashing fails in practice: Imagine Bank A wants to check if account number X123456 is suspicious. It hashes the number and checks Bank B’s database. But Bank B could create a “dictionary” of hashed values for every possible account number it processes. When it receives Bank A’s hashed query, it simply looks up which of its customers matches that hash. The “anonymization” is reversed, and Bank B now knows Bank A is investigating one of its customers — a clear privacy violation.
This is not a theoretical concern. The more standardized payment data becomes — particularly under ISO 20022, which creates uniform data fields across institutions — the easier such attacks become. If everyone uses the same format, the dictionaries become universal.
Group-IB’s Cyber Fraud Intelligence Platform (CFIP) is a privacy-first collaborative intelligence platform that enables financial institutions to share both confirmed fraud data and suspicious activity signals in real-time — addressing the critical gap between regulatory mandates and operational capability. Operating as a governed network, Cyber Fraud Intelligence Platform functions as an intelligence layer that integrates with each institution’s existing fraud prevention systems, enriching their risk engines with collective intelligence without replacing current infrastructure. Early deployments have demonstrated measurable results: in one pilot with 46 participating banks and payment providers, institutions conducting real-time checks prevented an estimated $10–15 million in fraud annually, with projections reaching $100–300 million at full network participation. The platform’s technical foundation — Distributed Tokenization — ensures this collaboration happens while maintaining full GDPR compliance.
The technical foundation that makes this possible is Distributed Tokenization (DT), Group-IB’s patented technology that overcomes the dictionary attack vulnerability. Unlike standard hashing, this process breaks a sensitive identifier into several parts, which are then sent to different participating entities for tokenization. This ensures that sensitive raw identifiers are never shared between entities. The result is a consistent and anonymous token; the same sensitive identifier will always generate the identical CFIP token across the network, allowing for effective pattern recognition and risk scoring. However, it is designed so that no single participant can reverse-engineer the token to reveal the original data.
The platform’s privacy-centric architecture is based on the principle of “Data Protection by Design”, a core tenet of GDPR. Bureau Veritas Cybersecurity has independently assessed the credibility of this approach. In a statement dated September 26, 2025, the organization concluded that “Group-IB is following the principles of GDPR as per the information available by September 2025”. The assessment also notes that in the context of CFIP, “Group-IB confirms that it does not act as Data Controller or Data Processor in the meaning of the General Data Protection Regulation”.
This validation matters because it provides institutions with regulatory air cover. Privacy regulators across jurisdictions have made it clear that intent is not enough — institutions must demonstrate, through independent technical assessment, that their data sharing mechanisms cannot be subverted to expose customer information. The Bureau Veritas assessment provides this documented proof, enabling institutions to confidently participate in collaborative fraud prevention without fear of privacy violations.
From Framework to Action: Building the Collaborative Defense
The technical and regulatory foundations are now in place for a fundamental shift in fraud prevention strategy. But infrastructure alone doesn’t stop fraud — participation does. The effectiveness of collaborative intelligence grows with the volume and diversity of signals being shared: each suspicious account flagged, each unusual transaction pattern reported, and each mule account identified during the warm-up phase adds to the collective intelligence. When Bank A checks a suspicious account against the network, its value lies in knowing whether any other participating institutions have seen similar patterns across their customers. The more institutions actively contribute and check, the richer the pattern recognition becomes, and the earlier mule networks can be identified.
The industry now faces a choice. Continue operating in silos, sharing only confirmed fraud data days after losses occur, and watch APP fraud losses continue their upward trajectory. Or embrace proactive collaboration, sharing suspicious activity signals in real time, and shift from damage control to genuine prevention.
The fraudsters have already made their choice. They collaborate globally, share tools and tactics freely, and operate as coordinated networks. The only effective counter is an equally coordinated defense — one that can match their speed, crosses institutional boundaries as easily as criminals do, and turns the criminal’s own tactics against them by identifying their mule networks before deployment.
The technology exists. The regulatory framework supports it. The business case is clear. What’s needed now is collective action.
Learn how your institution can join the collaborative fraud prevention network. Contact Group-IB to explore how the Cyber Fraud Intelligence Platform can integrate with your existing fraud prevention infrastructure and connect you to real-time intelligence from institutions worldwide.