According to Group-IB expert evaluations, almost 99% of all cybercrimes in the world now involve money theft. Don’t be surprised by such a high figure: computer-related crime seeks to maximize monetization and minimize risks. Therefore, it is much more interesting for professional cybercriminals to attack a bank than to hack, let’s say, a defense plant.
Targeted attacks currently pose the biggest hazard for banks: last year, losses suffered by financial institutions as a result of targeted attacks increased by almost 300%. One of these attacks cost a Russian bank RUB 140 million, while the total amount of stolen money increased to RUB 2.5 billion, according to our estimates. So why are targeted attacks so successful and what can banks do to counter them?
Remote theft
In July 2016, a masked man approached a First Bank ATM on the outskirts of Taipei. He phoned someone, and within several minutes the ATM gave out all the cash that it contained. The same thing happened at four dozen other First Bank ATMs: the criminals withdrew almost $2.2 million and disappeared.
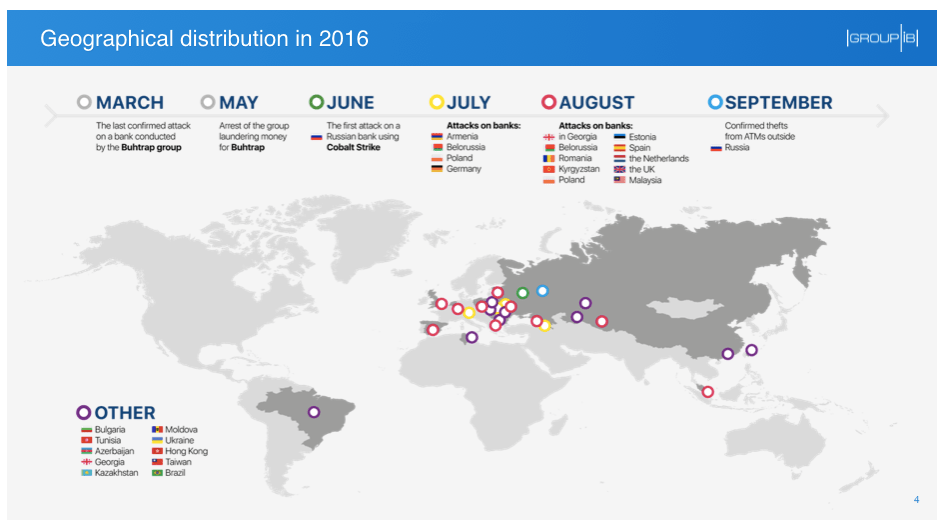
The local police encountered such a case for the first time: The criminals did not physically damage the ATMs, nor did they use skimmers or bank cards. So what happened? It was the final stage of a “logical” or “contactless” attack on ATMs organized, according to our sources, by a criminal group called Cobalt. Currently it is one of the most active groups: they have attacked banks in 14 countries of Europe and Asia.
Contactless attacks on ATMs represent just one type of targeted attacks on banks. In addition to ATM control systems, cybercriminals try to gain access to SWIFT systems, payment gateways and card processing systems.
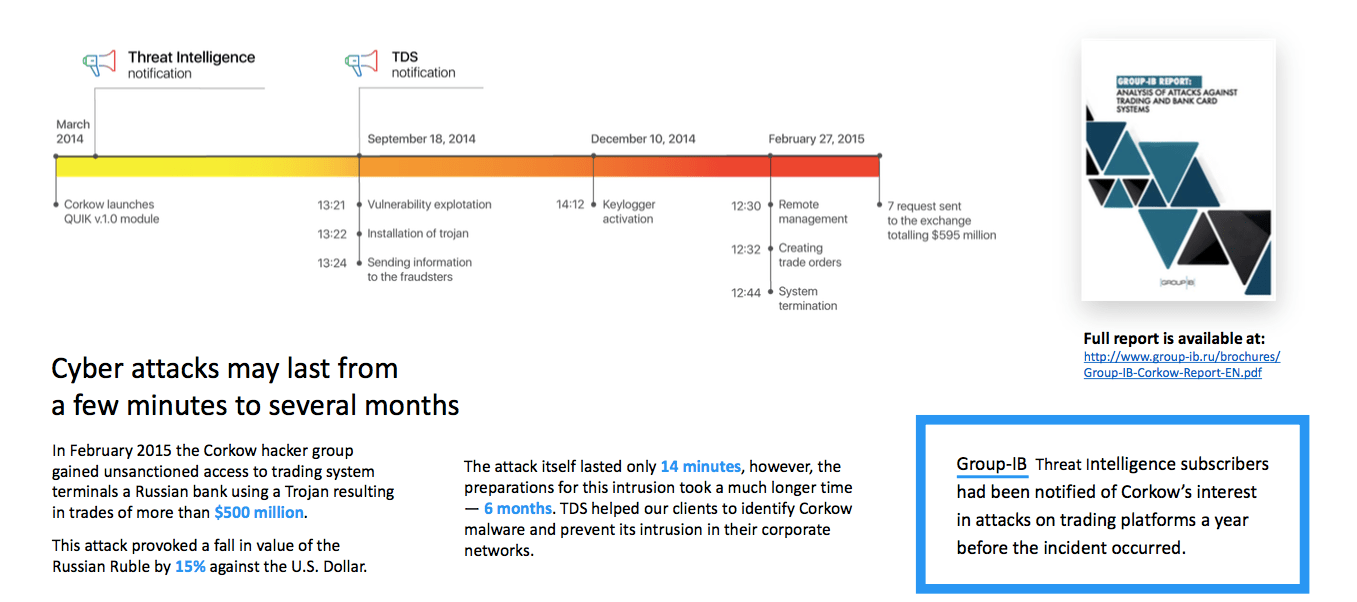
In February 2015, for the first time ever, a Trojan dubbed Corkow (Metel) gained control of a stock exchange trading terminal and placed orders worth a total of several hundred million dollars. In just 14 minutes attackers created abnormal volatility, which made it possible to buy dollars for 55 rubles and sell them for 62 rubles. As a result of the incident, a Russian bank suffered huge losses, although it was random traders rather than the hackers themselves that profited from it.
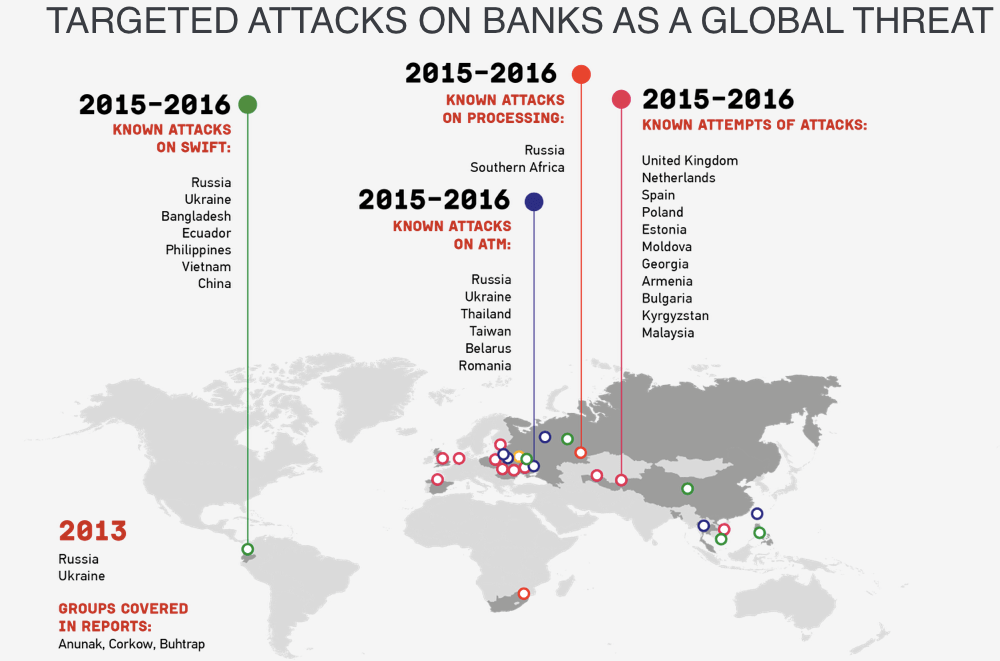
Group-IB tracked first large-scale targeted attacks on Russian banks as early as 2013. In 2014, there were only two known hacker groups, Anunak and Corkow, which conducted targeted attacks, whereas in 2015 there were three (Anunak, Corkow and Andromeda), and in 2016 four of them (Buhtrap, Lurk, Cobalt and MoneyTaker). The explanation is very simple: groups that used to attack companies that are banks’ clients are now shifting their focus to banks themselves. More money, less risk.
The majority of targeted attacks originated from Russia: hackers first tested all their new viruses, software and patterns of attacks on Russian banks and then went on to attack international financial institutions.
In February 2016, hackers tried to steal $951 million from the Central Bank of Bangladesh via the SWIFT system. Due to a mistake in a payment document they managed to steal only $81 million. According to investigation results, the attack was organized by Lazarus, a North Korean hacker group. For many years, it has been known for their actions against ideological opponents of North Korea, which involved DDoS attacks and hacking into resources of government, military and aerospace institutions in South Korea and the USA. However, apparently last year the North Korean hackers ran out of money, so they attacked dozens of financial institutions worldwide.
Group-IB specialists also observed hackers from another group trying to find experts in SWIFT and international money transfers on Internet forums. A forum user claimed that his bot network included computers that formed part the networks of German banks and had access to SWIFT. A recent successful attack on a Russian bank via the ARM CBR (Automated Work Station Client of the Russian Central Bank) payment system has provided evidence that intruders have a tool for automatic substitution of payments in the SWIFT system. After certain adaptation, it can be used for attacks on SWIFT throughout the world.
Financial infrastructure is attractive not only for cybercriminals. When the Shadow Brokers group (for more details about their attacks, see the Forbes material) shared data from a leak from the Equation Group – hackers associated with the US National Security Agency, it became clear that the secret service probably had access to SWIFT and controlled various financial transfers between banks in the Middle East and Latin America. Experts do not rule out the possibility that the NSA not only monitored but also purportedly intervened in financial transactions conducted by terrorist groups.
And there is one more danger caused by targeted attacks. The pattern of a successful attack on a bank may be used for spying and cyberterrorism – for instance, to hack into networks of industrial facilities and power plants or to gain access to control systems of critical infrastructure facilities. Last year, a similar scenario was used by the Black Energy group to attack the Boryspil International Airport in Kiev and Ukrainian power grids. Let us examine the mechanics of targeted attacks.
Mechanics of targeted attacks
Essentially, targeted attacks do not require special experience nor unique software. Hackers employ ready-to-use tools bought on underground hacking forums or free legal software, which is widely available.
Intrusion and infection
The key infection vector used to attack bank networks is sending phishing emails with malicious attachments (Trojans) disguised as a legitimate document or a password-protected archive to bank employees.
Criminals use various tricks to make bank clerks open these attachments. In 2015, employees of a Russian bank received emails about vacancies in the Central Bank sent to their corporate addresses. In 2016, Cobalt sent phishing emails acting as the European Central Bank (“The rules for European banks.doc”) or an ATM manufacturer Wincor Nixdorf. Malicious attachments with exploits can be developed with the use of ready-made virus creation kits, while to send executable files, one does not need any special tools, just an ordinary email client.
Remote access
Infection of one computer in a corporate network opens a door into a protected bank system. With freeware employed (such as TeamViewer, Ammy Admin, VNC, Light Manager), intruders gain remote access to a bank network. Then they extract credentials from the RAM of an infected computer. For instance, a source code of such a tool, Mimikatz, has been posted on a website and is currently available for everyone.
Search for targets
After obtaining domain admin privileges, hackers examine a bank’s internal network; they may be targeting SWIFT systems, instant transfer systems for individuals, ATM control networks, payment gateways or card processing systems. When hackers find their target, they start to track the actions of bank operators by taking picture or recording video on controlled computers. They need that in order to repeat their steps later and transfer money to controlled accounts. More advanced groups use ready-made tools to modify payment documents: simple scripts and executable files functioning as scripts are employed to automate fraudulent payments.
Conversion into cash
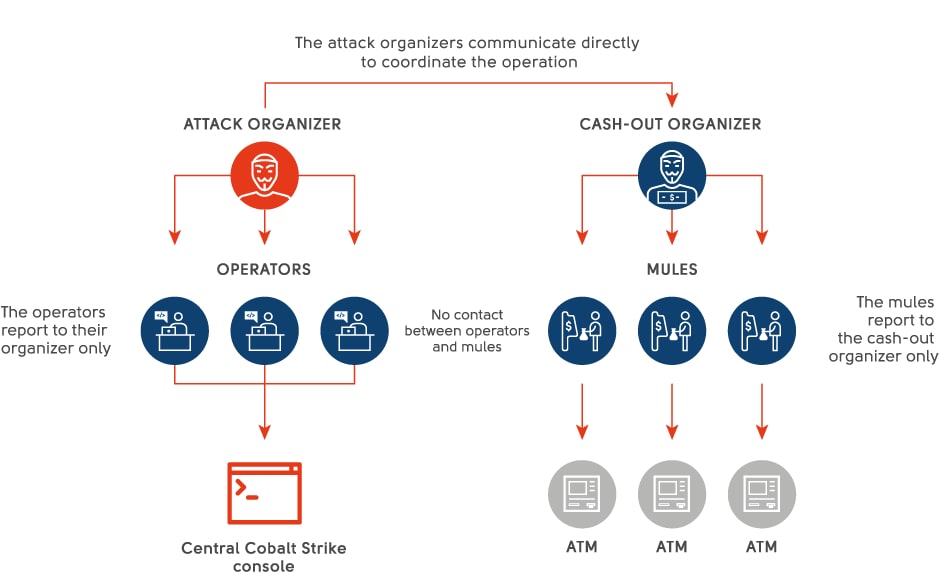
This stage is performed by special professional teams charging about 50% of stolen money as a fee for their services. Cash is withdrawn by “money mules” — the lower echelon of the criminal hierarchy. They can be brought to any city in order to pick up the money. While operating abroad, they most often pose as “tourists” and leave the country after the operation has been completed.
Staying ahead of the curve
Why are targeted attacks so successful? The main reason is that banks have little knowledge of the patterns and tactics of targeted attacks on the financial sector. They do not understand how these attacks are conducted, and therefore, they cannot develop adequate countermeasures.
The number of targeted attacks on banks will continuously grow. Following successful attacks on Russian and Ukrainian banks, hackers will turn to other regions of the world. We observe that criminals search persistently for insiders in banks in order to collect information and perform initial infection. Therefore, it is critical that banks be more careful in selecting their employees and arrange regular personnel trainings, which should include not only training sessions on issues related to targeted attacks, phishing and social engineering, but also “combat training”: banks should simulate targeted attacks or phishing emails from time to time.
The second reason for the success of targeted attacks is that companies rely too much on standard security features such as licensed and updated antivirus software, the latest versions of OS, firewalls or DLP and believe that they would stop intruders at some stage of their attack. But they are wrong.
Investigations of incidents show that infected computers almost always had antivirus software from popular antivirus providers and infrastructure was quite well protected with intruder detection systems and other hardware and software.
When a file is being sent by mail, an antivirus program can conduct a quick scan, but this does not make it possible to understand whether the file is malicious or not. In order to understand that, it is better to use “sandboxes” – systems for proactive protection against targeted attacks and hacking attempts. Delivery of emails may be less quick, but they will be checked more thoroughly; it will be possible to understand whether the file is malicious or not. We can recommend products provided by FireEye and Dr.Web Katana (Group-IB, the author’s company, also provides a sandbox system called TDS Polygon — Forbes).

Ilya Sachkov presents TDS – Group-IB’s unique solution allowing to detect threats in real time
There is no 100% guarantee of protection against targeted attacks on banks, but it is possible to mitigate risks and improve the efficiency of banks’ protection. The best way of doing that is Threat Intelligence: a system for collection, monitoring and analysis of information about actual threats, criminal groups, their tactics and tools. The services of intelligence companies are sought-after by foreign and – lately – Russian banks.
For instance, one large English bank has eight (!) suppliers of Threat Intelligence data. Some intelligence companies focus on zero-day vulnerabilities, while others focus on cyberterrorism or on Chinese hackers. If information about threats is confirmed by two sources, it is more reliable, and if there are three of them, it is even better. Data from various sources are combined and analyzed by TIPs (threat intelligence platforms). Subscribers of threat intelligence services can learn about the tactics and mechanics of attacks in advance, which will allow them to stop attackers, clear the network and block the access for intruders. To sum up, in order to keep your money, you need to stay ahead of the curve.
Any question about our products and services, or pricing?
Just fill out the form, and our representative will contact you soon.