On 24th October in Russia and Ukraine a largescale cyber attack took place using a new cryptolocker – BadRabbit. Amongst victims, this affected computers and servers of the Kiev metro, the Ministry of Infrastructure and Odessa International Airport, as well as a number of state organisations in the Russian Federation. Victims in the Russian Federation included Federal news sites and commercial organisations. Infections have also been reported in Bulgaria, Japan, Turkey and Germany.
Infection took place after visiting compromised legitimate sites. Group-IB identified that Bad Rabbit was spread via web traffic from compromised media sites, amongst them were:
- http://www.fontanka.ru/
- http://argumenti.ru
- http://argumentiru.com
The user was displayed a window with a suggestion to update FlashPlayer. If the user agreed to this update, a malicious file named install_flash_player.exe is downloaded: (FBBDC39AF1139AEBBA4DA004475E8839 – MD5 hash), and infects the host.
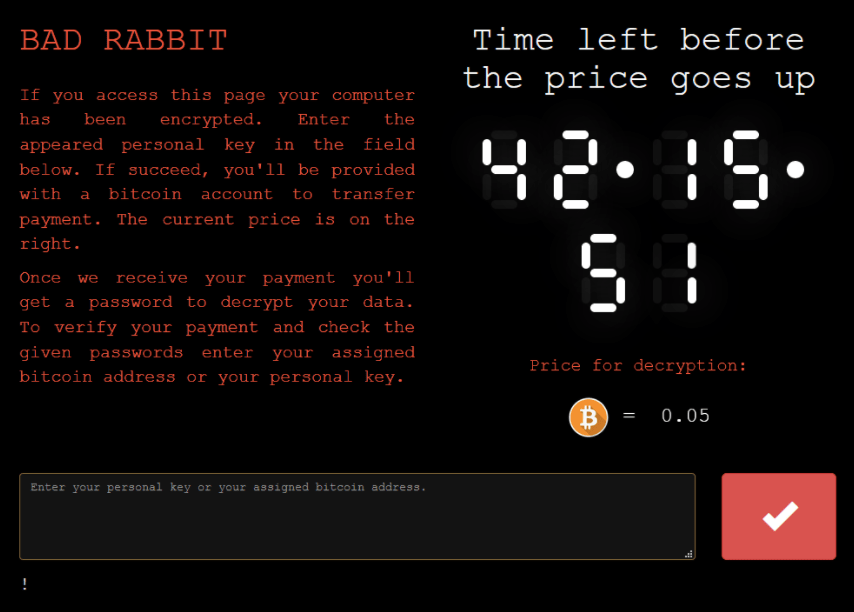
For decryption the attacks requested 0,05 bitcoin (at current exchange rates this is around 283 USD). After infection the malware raised privileges on the local machine for spreading. On local network this took place by SMB, using extraction of LSASS passwords from the compromised computer, or an internal password library.
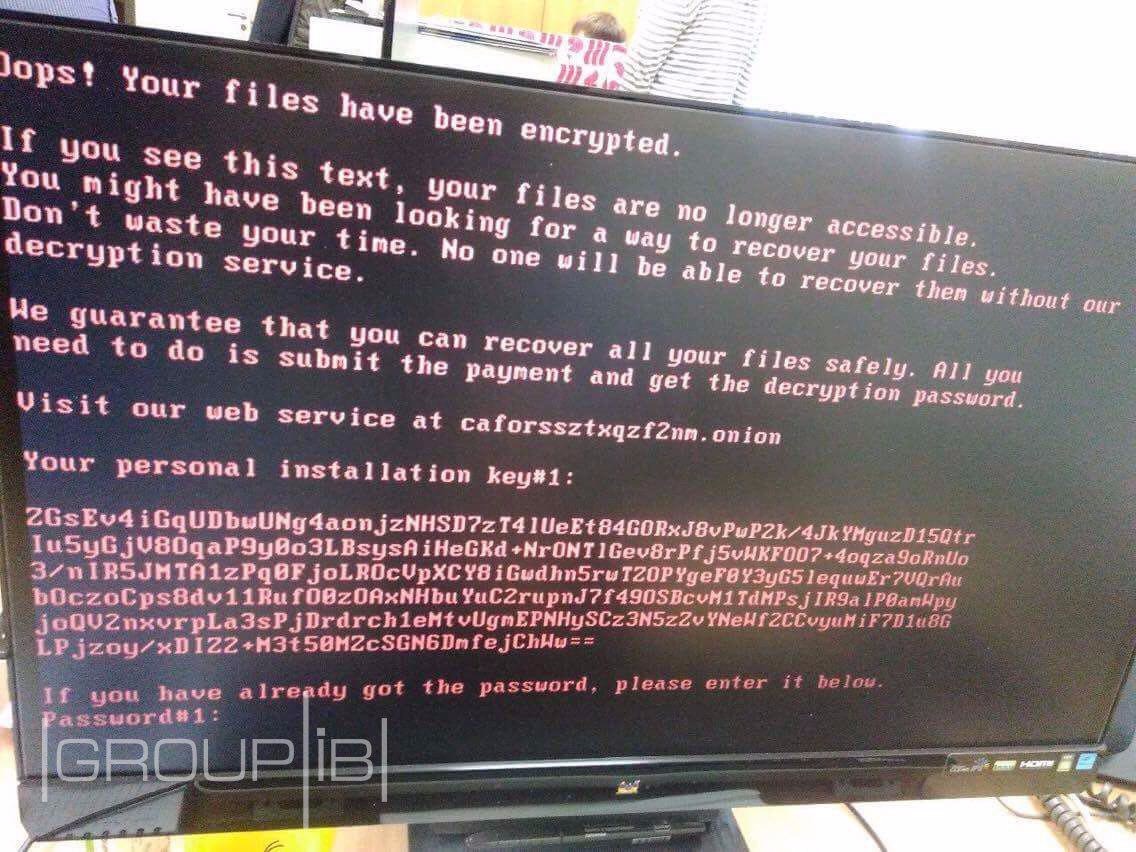
After infection, the victim sees the following window:
It contains an individual code and an address for a torrent site: caforssztxqzf2nm.onion, which lists an automatic timer. On the site, victims are required to enter their personal code, after which a bitcoin wallet appears. The attackers then demand 0,05 bitcoin in order to unlock the victim computer. Additionally, on the site there is a countdown timer until the cost increases.
Bitcoin wallets of attackers:
1GxXGMoz7HAVwRDZd7ezkKipY4DHLUqzmM
17GhezAiRhgB8DGArZXBkrZBFTGCC9SQ2Z.
The attack was prepared for a several days, on the site: http:// caforssztxqzf2nm.onion/ — there are two js scripts. Judging by information from the server, one of them was updated on 19th October – 5 days ago.
Eset detected that the malicious JS script send part of the information to server 185.149.120.3. On this server, since yesterday was installed a Apache Tomcat/Coyote JSP engine 1.1, for which there were prepared exploits which allowed remote code to be used on the server. The server belong to the company Jetmail, which engages in email marketing. At the current time their site is unavailable.
If a visitor pressed “download” then the malicious file was downloaded from 1dnscontrol.com. This domain name 1dnscontrol.com has IP 5.61.37.209.
The attack at a first glance appears to be financially motivated in general principle. For hosting, they used Inferno bullet proof hosting. The domain name 1dnscontrol.com was registered on 22 March 2016 and is currently prolonged. There are a number of malicious domains associated with this site, which relate back to 2011. It is possible that these domains have also been compromised or are used for analogous attacks. Amongst them it is worth noting:
- webcheck01.net
- webdefense1.net
- secure-check.host
- firewebmail.com
- secureinbox.email
- secure-dns1.net
Technical Analysis
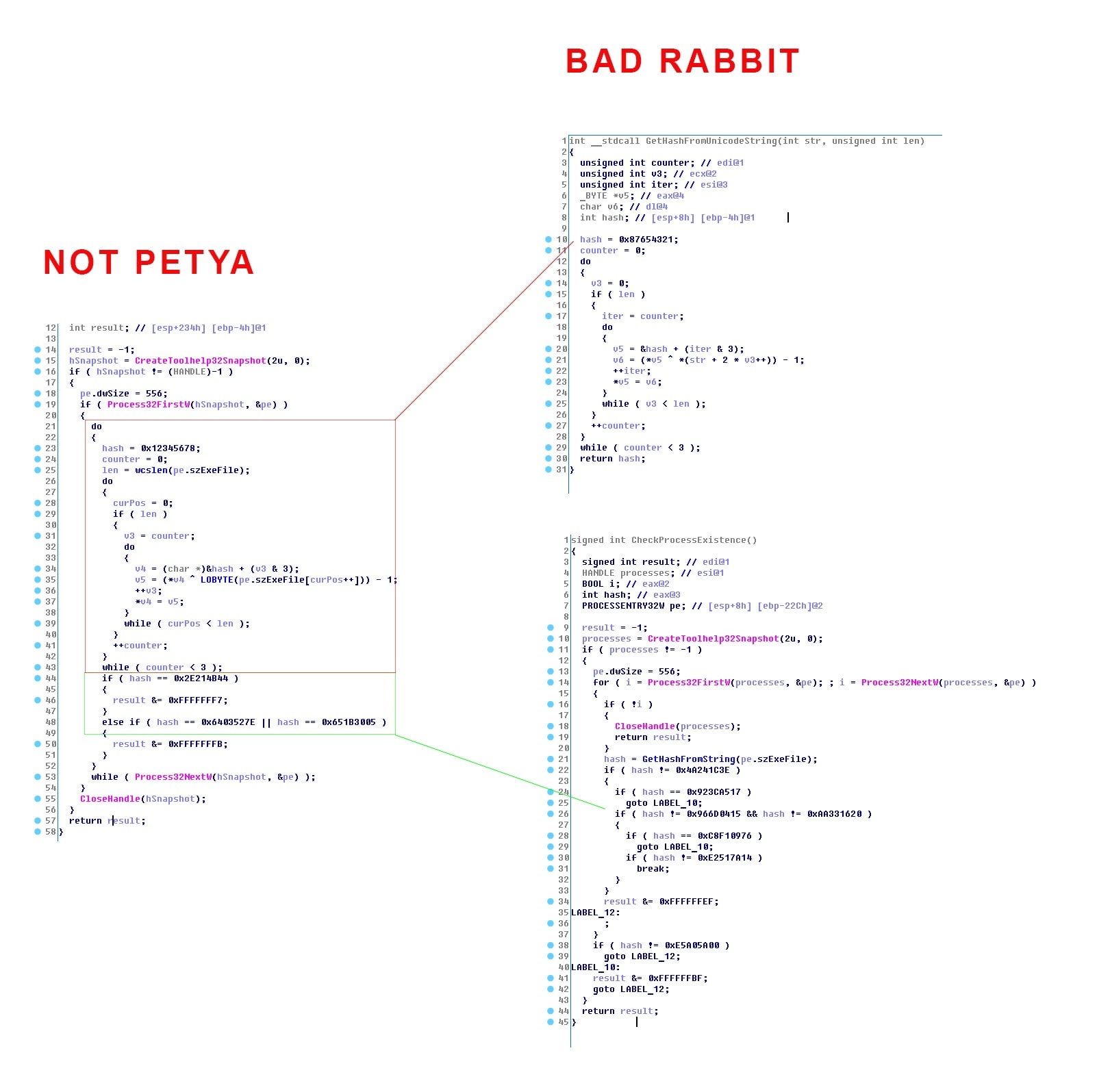
During analysis, it became clear that Bad Rabbit is a modified version of NotPetya, with changes to the encryption algorithm and in parts entirely mirrors that of NotPetya:
As you can see, in the NotPettya attack there is the same algorthm for processing the hashsum from run processes, with the same difference, that the first initialisation vector in Petya is 0x12345678, where in Bad Rabbit it is 0x87654321. Also, in the current attack the number of searched processes and the function for processing hash sum was compiled into a seperate function by the compiler (inlined in NotPetya case).
These similarities suggest a link between Bad Rabbit and Black Energy campaigns.
It was also detected that Bad Rabbit has a module for spreading via SMB protocol. After gaining access to the victim’s computer Bad Rabbit scans the local network for the following open SMB directories:
admin
atsvc
browser
eventlog
lsarpc
netlogon
ntsvcs
spoolss
samr
srvsvc
scerpc
svcctl
wkssvc
As identified, it users Mimikatz to collect logins and passwords on the infected machine and also uses credentials libraries to gain admin rights.
Hi-Tech Crime Trends 2017
Group-IB forecasted these attacks just in our annual research – get full version for more trends and forecasts
Recommendations
Kill Switch: to create read-only file C:\windows\infpub.dat. In case of infection files won’t be encrypted
- Restrict Scheduled Tasks: viserion_, rhaegal, drogon
- Make backup of important data
- Update operation systems and security systems
- Isolate infected PCs
- Block IP-addresses and domain names from Indicators list
- Block popup windows
- Use up-to-date security IDS systems and sandboxe for files analysis Group-IB
TDS Polygon notified users about infection attempts.